HermeticWiper malware used against Ukraine
Data-wiping malware dubbed HermeticWiper has impacted hundreds of machines and networks geolocated in Ukraine. It is malware used not just to infect machines but also to destroy them.

Learn Python for Cybersecurity
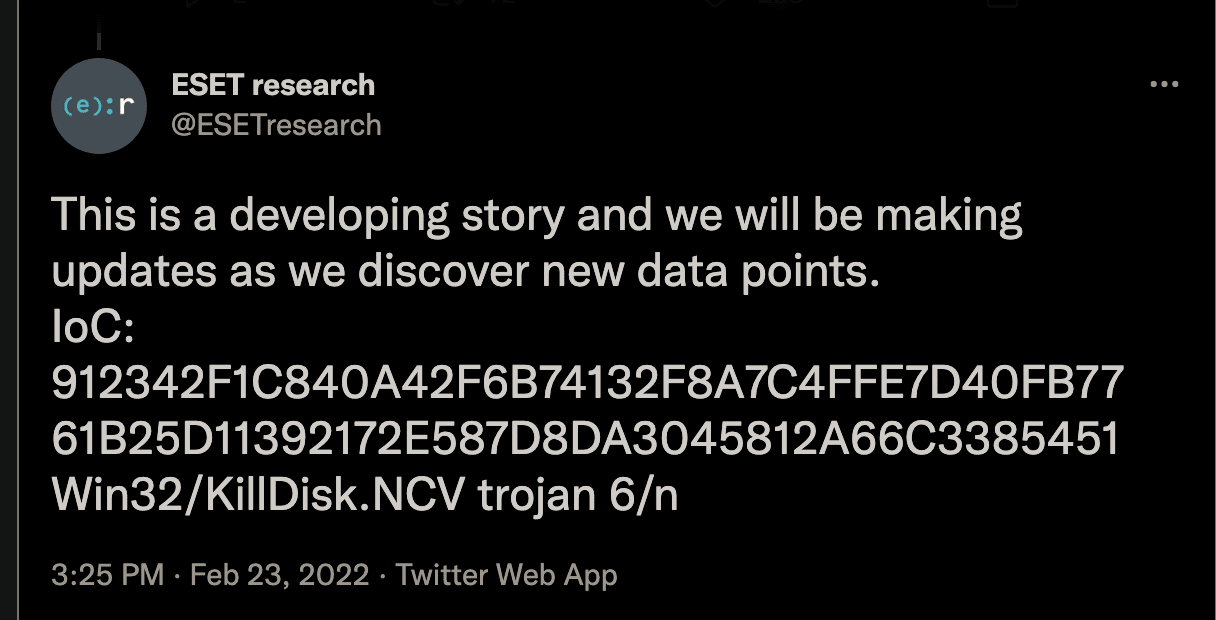
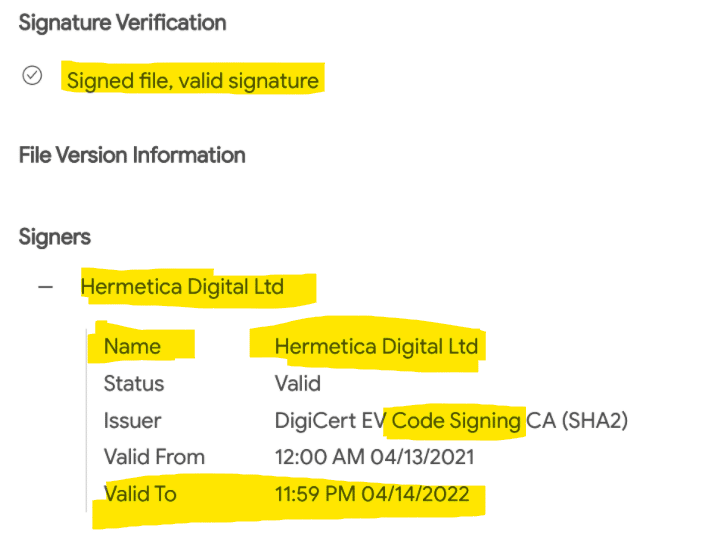
HermeticWiper has been active since Feb. 23, 2022, and has impacted machines and Ukraine networks. The name attributed to this malware, "HermeticWiper," is based on a stolen digital certificate stolen from a company called Hermetica Digital Ltd. With a lot of features introduced by its authors, HermeticWiper can bypass Windows security features and gain write permissions to many low-level data structures on disk. One of the destructive procedures implemented by its developers is the capacity to re-write fragments on the disc to make the recovery process impossible. [CLICK IMAGES TO ENLARGE]
Figure 1: Tweet by ESET reporting the malicious IoCs related to the HermeticWiper (source).
This malware tries to bypass some security features by using a legitimate certificate by Hermetica Digital Ltd. The name of the malware is directly related to this finding.
Figure 2: Code signing certificate by Hermetica Digital Ltd used by HermeticWipe malware.
Digging into the details
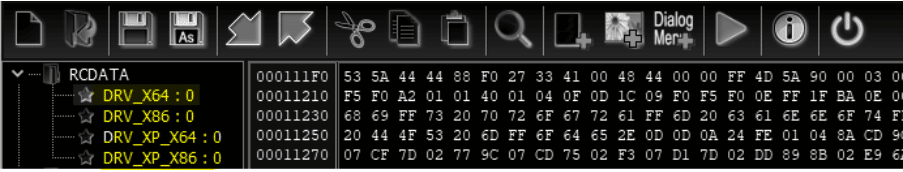
HermeticWiper is a simple PE File with only 114 KBs in size but four binaries on the RCDATA section. Observing the files' names (x86 e x64) will be extracted and executed according to the target machine architecture. The files are decoded in runtime by using the LZMA algorithm.
Figure 3: Aditional binaries present in the RCDATA section.
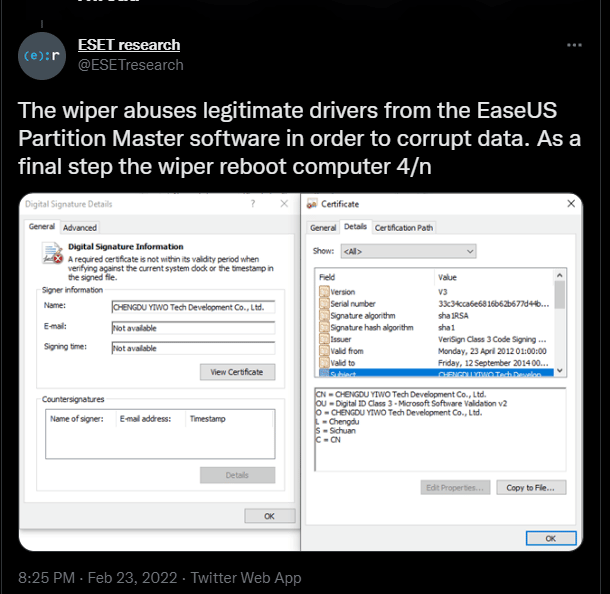
In detail, the four files are drivers that will be installed on the target machine and found and reported by ESET on Twitter.
Figure 4: Drivers dropped by HermeticWiper and addressed by ESET on Twitter.
According to the Sentinel Labs analysis, "the benign EaseUS driver is abused to do a fair share of the heavy-lifting when it comes to accessing Physical Drives directly and getting partition information. This adds to the difficulty of analyzing HermeticWiper, as a lot of functionality is deferred to DeviceIoControl calls with specific IOCTLs".
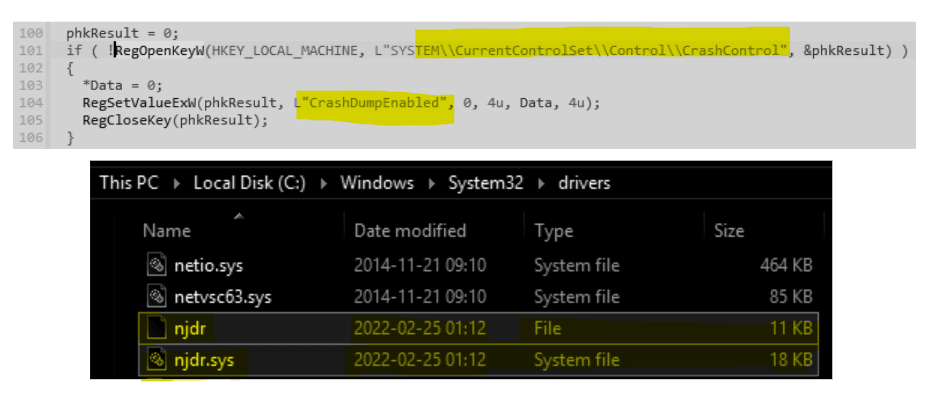
Before installing and dropping the drive on the disk, the crash dumps are disabled.
Figure 5: Drivers dropped, and crash dumps disabled (source).
After this point, the driver is added to the system service, initiating the infection data-wiping process.
Features of HermeticWiper
Several features are activated during the malware execution, as some do not follow a logical structure. The process is the following:
- Disabling shadow copies — to make data recovery impossible
- Performing data fragmentation — to damage all the data and difficult the file carving process
- Corrupting Master Boot Record (MBR)
- Executing data collection approach by scanning NTFS directories
- Executing last stage: data overwriting
At first glance, this malware has one purpose: damaging all the data.
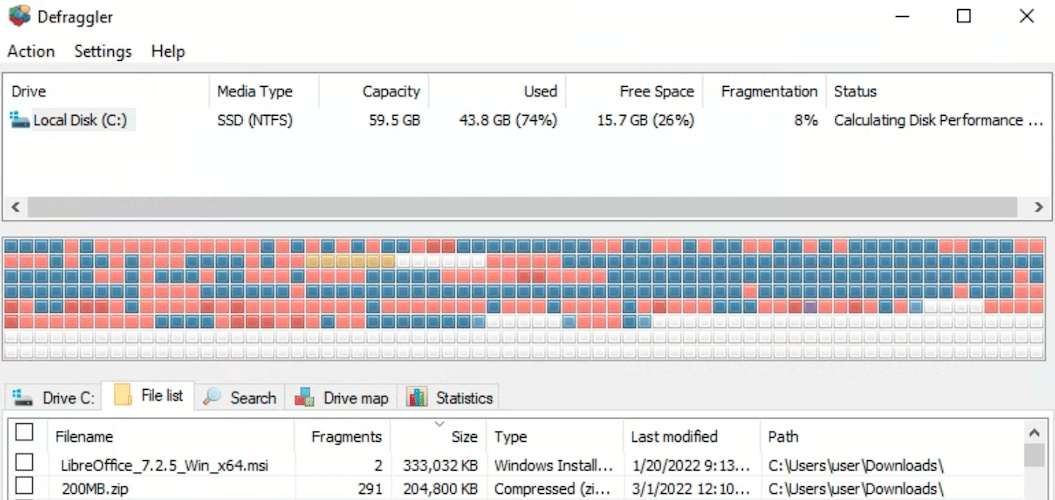
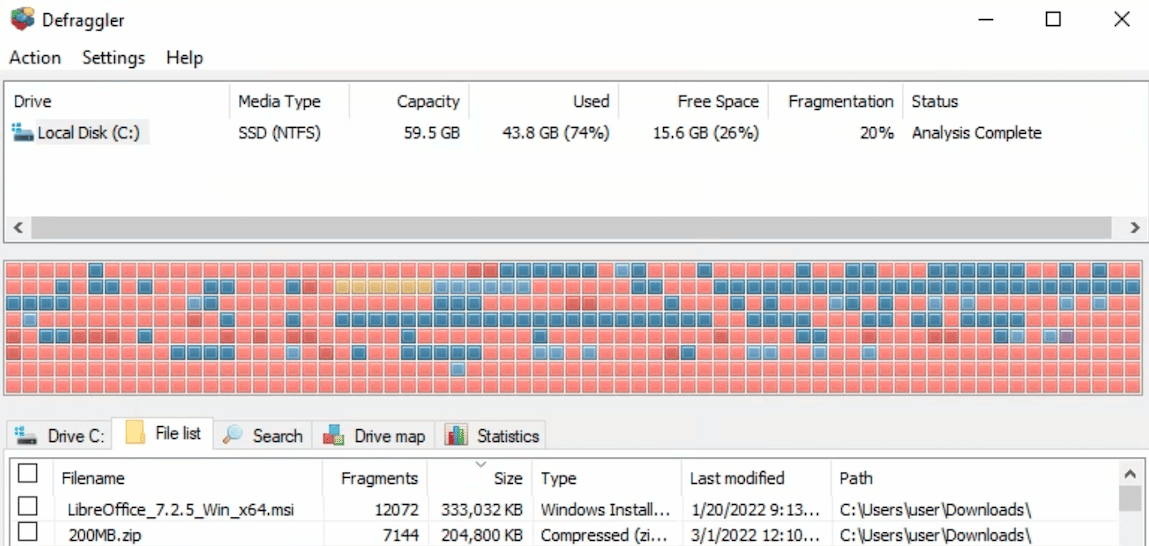
The next image shows the status of the disk data fragmentation before and after the malware execution.
Figure 6: Disk before the malware execution (source).
Figure 7: Disk after the malware execution — all the data was overwritten (source).
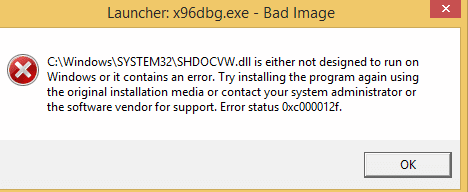
After the malware executes, the data is overwritten, making hard data recovery via forensics and file carving techniques. Even system DLLs are corrupted, causing the system to no longer start.
Figure 8: System DLLs damaged during the malware executing and "Missing operating system" after rebooting the system (sources).

Cybersecurity interview guide
The malware wiping data in Ukraine
HermeticWiper is seen as a critical and dangerous malware as its only intent is to damage data and make it impossible to recover. It takes advantage of a code signing certificate to bypass its detection, and its attack scope is theWindows ring 0 (kernel space).
The malware initially fragments the files and overwrites those blocks to difficult the forensics process. According to security experts, "even without the last step (indiscriminate disk trashing), the combination of fragmentation and wiping of required structures (like $MFT) would be enough to make a recovery almost impossible."
In a publication by US-CERT here, some recommendations and measures can be taken to mitigate the impact of threats of this nature.
Sources:
- Hermetic-Wiper Ukraine under attack, SentinelOne
- Hermetic-Wiper analysis, MalwareBytes
- Hermetic-Wiper Alert, US-CERT
- Data-wiping malware hits Ukraine, Welivesecurity