Malware analysis

Malware analysis
Learn more about the popular and dangerous AsyncRAT malware.

January 10, 2023
Pedro Tavares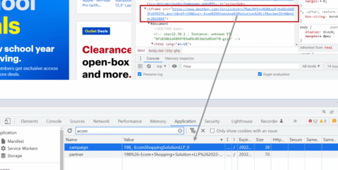
Malware analysis
Learn how Chrome extensions are being used for nefarious purposes.

October 19, 2022
Pedro Tavares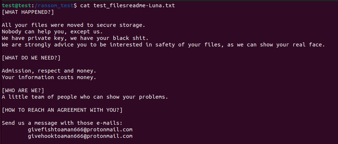
Malware analysis
Criminals use the Rust and Goland programming languages to develop new threats.

September 28, 2022
Pedro Tavares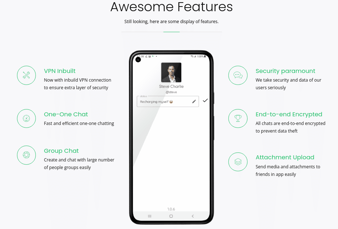
Malware analysis
Learn all about the Bahamut malware that is once again infecting devices.

September 21, 2022
Pedro Tavares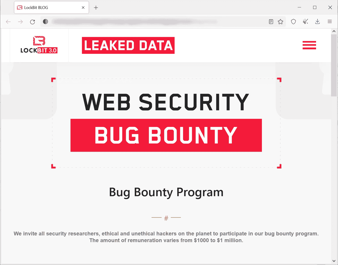
Malware analysis
Hospitals and health systems are susceptible to the LockBit ransomware.

September 14, 2022
Pedro Tavares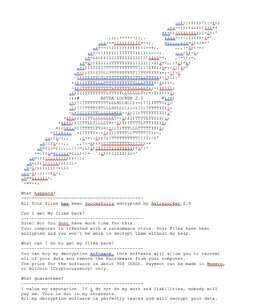
Malware analysis
Astralocker is a piece of ransomware first identified in 2021. It is probably a fork from the well-known Babuk and other ransomware like Rook. Version 2.0 of

September 7, 2022
Pedro Tavares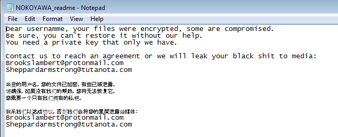
Malware analysis
Ransomware is an ongoing threat. New variants are constantly detected, and existing threats keep adding new features and techniques for performing malicious

August 31, 2022
Pedro Tavares
Malware analysis
Goodwill ransomware uses three different socially-driven and philanthropic activities to be able to download the decryption key.

August 29, 2022
Pedro Tavares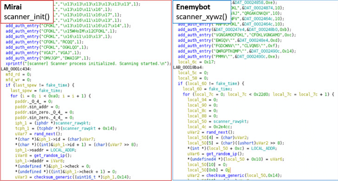
Malware analysis
EnemyBot is a dangerous IoT botnet that was designed to attack web servers, Android devices and CMS servers. Learn more in this article.

August 24, 2022
Pedro Tavares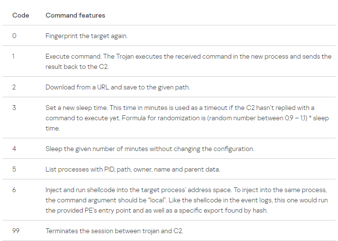
Malware analysis
Learn about a fileless malware that is “taking advantage of Windows event logs to stash chunks of shellcode for the first time in the wild.”

August 3, 2022
Pedro TavaresLearn IoT Security
Build your IoT security skills and become a Certified IoT Security Practitioner. What you'll learn:
- Securing IoT networks
- Software and firmware risks
- Controlling access to IoT
- Ensuring privacy
- And more
In this series
- How AsyncRAT is escaping security defenses
- Chrome extensions used to steal users' secrets
- Luna ransomware encrypts Windows, Linux and ESXi systems
- Bahamut Android malware and its new features
- LockBit 3.0 ransomware analysis
- AstraLocker releases the ransomware decryptors
- Analysis of Nokoyawa ransomware
- Goodwill ransomware group is propagating unusual demands to get the decryption key
- Dangerous IoT EnemyBot botnet is now attacking other targets
- Fileless malware uses event logger to hide malware
- Nerbian RAT Using COVID-19 templates
- Popular evasion techniques in the malware landscape
- Sunnyday ransomware analysis
- 9 online tools for malware analysis
- Blackguard malware analysis
- Behind Conti: Leaks reveal inner workings of ransomware group
- ZLoader: What it is, how it works and how to prevent it | Malware spotlight [2022 update]
- WhisperGate: A destructive malware to destroy Ukraine computer systems
- Electron Bot Malware is disseminated via Microsoft's Official Store and is capable of controlling social media apps
- SockDetour: the backdoor impacting U.S. defense contractors
- HermeticWiper malware used against Ukraine
- MyloBot 2022: A botnet that only sends extortion emails
- Mars Stealer malware analysis
- How to remove ransomware: Best free decryption tools and resources
- Purple Fox rootkit and how it has been disseminated in the wild
- Deadbolt ransomware: The real weapon against IoT devices
- Log4j - the remote code execution vulnerability that stopped the world
- Rook ransomware analysis
- Modus operandi of BlackByte ransomware
- Emotet malware returns
- Mekotio banker trojan returns with new TTP
- Android malware BrazKing returns
- Malware instrumentation with Frida
- Malware analysis arsenal: Top 15 tools
- Redline stealer malware: Full analysis
- A full analysis of the BlackMatter ransomware
- A full analysis of Horus Eyes RAT
- REvil ransomware: Lessons learned from a major supply chain attack
- Pingback malware: How it works and how to prevent it
- Android malware worm auto-spreads via WhatsApp messages
- Malware analysis: Ragnarok ransomware
- Taidoor malware: what it is, how it works and how to prevent it | malware spotlight
- SUNBURST backdoor malware: What it is, how it works, and how to prevent it | Malware spotlight
- ZHtrap botnet: How it works and how to prevent it
- DearCry ransomware: How it works and how to prevent it
- How criminals are using Windows Background Intelligent Transfer Service
- How the Javali trojan weaponizes Avira antivirus
- HelloKitty: The ransomware affecting CD Projekt Red and Cyberpunk 2077
- DreamBus Botnet: An analysis
- Kobalos malware: A complex Linux threat
Phishing simulations & training
Unlock pricing and see how Infosec IQ can help you empower employees with 2,000+ security awareness resources to:
- Reduce security events
- Reinforce cyber secure behaviors
- Strengthen cybersecurity culture at your organization
