Shamoon Reloaded: the Mysterious Return of the Dreaded Wiper
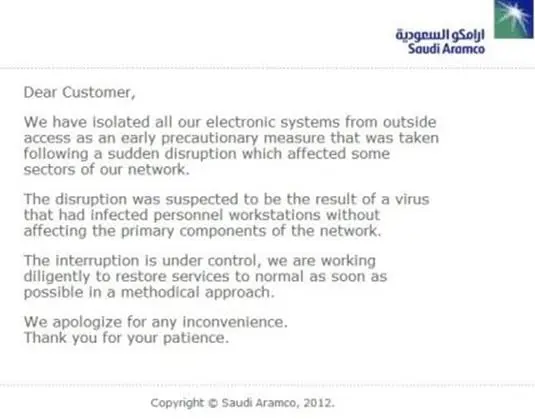
August 2012 – Saudi Aramco hit by a cyber attack
On August 15th, 2012, the Saudi Arabia's oil company, Saudi Aramco announced that its systems and its internal network were victims of a cyber-attack. According to the company, malware infected more than 30,000 workstations; it was the Shamoon malware, also known as Disttrack.
All the servers have been cleaned and restored, and all the activities are back to normal in a few days. Fortunately, the production environment has not been affected by the attack because it uses a totally isolated network.

Learn Vulnerability Assessments
Saudi Aramco confirmed that other companies in the energy industry suffered similar attacks, the company CEO Khalid A. Al-Falih announced further measures to improve the security of the IT infrastructure.
"Saudi Aramco is not the only company that became a target for such attempts, and this was not the first nor will it be the last illegal attempt to intrude into our systems, and we will ensure that we will further reinforce our systems with all available means to protect against a recurrence of this type of cyber-attack," said Khalid A. Al-Fali.
Figure 1 - Saudi Aramco announcement
At the time of the attack, several groups claimed responsibility for the cyber-attacks, the "Cutting Sword of Justice" and the "Arab Youth Group" are among them. The Cutting Sword of Justice announced on Pastebin to have infected and destroyed more than 30,000 computers of the company. The attack is the retaliation against the company responsible for supporting "crimes and atrocities" against citizens in Syria, Egypt, Lebanon and other countries in the area.
According to Jeffrey Carr, CEO of Taia Global, the Arab Youth Group, used terms like "evil Al-Saud" and "Al-Saud traitors" and specifically refers to Lebanon and the Forqan War (aka Operation Cast Lead 12/2008-1/2009) which at least one Iranian hacker crew – the Ashiyane Security Group – participated in.
The second group, the Cutting Sword of Justice, posted several messages containing proof of the attack such as the list of compromised IP addresses of the servers. Analyzing the way, they wrote the messages it is possible to note that they have not made religious proclamations and that the attackers focused the statements on political concepts like "tyranny."
According to Jeffrey Carr, the Hezbollah, a Shi'a militant group based in Lebanon, is close to Iran and received financial and political support from the government of Teheran. Hezbollah includes in its ranks hackers that may have been recruited to launch cyber-attacks like the one that hit Saudi Aramco.
Up to 70 Aramco employees, including Lebanese Shi'a, were investigated for the cyber-attack.
They hackers shared information linked to strings found in the code of the Shamoon malware, the malicious code used to destroy the target machine.
The malware can exfiltrate data from the infected machine before destroying it.
It was first spotted by Kaspersky Lab that analyzed some instances of the malware that included a "wiper" component.
Shamoon can destroy files on the victim's PC and overwrite the master boot record of its disks making the machine unusable. The malware can infect Windows machines, including Windows 95, Windows 98, Windows XP, Windows 200, Windows Vista, Windows NT, Windows ME, Windows 7, Windows Server 2003 and Windows Server 2008.
The researchers at Seculert who analyzed the malware discovered that it gathers data from the victim's PC, the malicious code takes data from the 'Users', 'Documents and Settings', 'System32/Drivers,' and 'System32/Config' folders on Windows computers, and send them to another infected PC on the same internal network.
"The attacker took control of an internal machine connected directly to the internet and used that machine as a proxy to the external Command-and-Control (C2) server. Through the proxy, the attacker infected the other internal machines, which were probably not connected directly to the internet," explained Seculert CTO Aviv Raff.
"Threats with such destructive payloads are unusual and are not typical of targeted attacks," reads the analysis published by Symantec on Shamoon attacks.
Many experts believe Shamoon is a nation-state malware used in cyber-espionage campaigns; it includes a wiper component to hide any track of its activity on the infected system.
The real reason behind the attack appears to be the dispute between Iran and Saudi Aramco over Oil Embargo placed upon Iran by the U.S. and the European Union on July 1st, 2012.
Teheran menaced to close the Strait of Hormuz to respond to the embargo, but many experts speculated that Iran was financing cyber-attacks to destroy companies such as Saudi Aramco that were sustaining the penalties against the country.
Figure 2 - Oil routes
Due to the reasons exposed, it is reasonable to assume that Iran is one of the main suspects in the attack on the oil company.
"While both the Arab Youth Group and the Cutting Sword of Justice involvement gives it the appearance of a mere hacktivist attack, I think that a careful analysis of the known facts points to a state-sponsored attack by Iran that was crafted to look like the work of hacktivists." stated Carr.
December 2016 – Shamoon is back
In December 2016, security experts observed a new wave of attacks leveraging on the Shamoon malware. The malware experts from Palo Alto Networks and Symantec both reported an attack on a single Saudi company.
The new variant of Shamoon, so-called Shamoon 2, can rewrite the MBR on affected computers with an image of a three-year-old Syrian boy named Alan Kurdi that lay dead on a Turkish beach.
"Why Shamoon has suddenly returned again after four years is unknown. However, with its highly destructive payload, it is clear that the attackers want their targets to sit up and take notice," reported Symantec.
"Last week, Unit 42 came across new Disttrack samples that appear to have been used in an updated attack campaign. The attack targeted at least one organization in Saudi Arabia, which aligns with the targeting of the initial Shamoon attacks. It appears the purpose of the new Disttrack samples were solely focused on destruction, as the samples were configured with a non-operational C2 server to report to and were set to begin wiping data exactly on 2016/11/17 20:45. In another similarity to Shamoon, this is the end of the work week in Saudi Arabia (their work week is from Sunday to Thursdays), so the malware had potentially the entire weekend to spread. The Shamoon attacks took place on Lailat al Qadr, the holiest night of the year for Muslims; another time the attackers could be reasonably certain employees would not be at work." reads an analysis published by Palo Alto Networks.
Experts from Symantec have no doubts; the cyber-attack is the result of a carefully planned operation. The malware comes with passwords that appear to have been stolen from the targeted organizations. The availability of the credentials allowed the threat to spread across the targeted network rapidly. It is still unclear how the attackers obtained the credentials.
The analysis of the Shamoon 2 default configuration shows that the threat was programmed to start the disk-wiping component at 8:45pm local time on Thursday, November 17. The attack was planned to start on Laylat al Qadr (Night of Decree) that is a Muslim holiday.
Considering that in Saudi Arabia the working week runs from Sunday to Thursday, the attackers tried to hit the organization during the suspension of working activities to maximize the effects of the attack.
"The malware had a default configuration that triggered the disk-wiping payload at 8:45pm local time on Thursday, November 17. The Saudi Arabian working week runs from Sunday to Thursday. It would appear that the attack was timed to occur after most staff had gone home for the weekend in the hope of reducing the chance of discovery before maximum damage could be caused." wrote Symantec.

Figure 3 - Shamoon 2 Attack
The analysis of the malware revealed that it was almost identical to the one used in the 2012 attacks.
The Shamoon 2 malware is composed of three components, a dropper, a wiper, and a module for communications that was developed to control the malware remotely.
Experts noticed that in the recent attack, the component for the remote communications was configured with the IP 1.1.1.1, that didn't host the Shamoon C&C server. This circumstance suggests that attackers plan did not include the possibility of updating the threat once launched the attack.
According to PaloAlto Networks, from a functionality standpoint, the wiper is powered by EldoS RawDisk driver utility that can overwrite files on the system without any interaction with the OS.
Malware researchers believe that the group behind the Shamoon 2 variant are the same that launched the 2012 attack against the company Saudi Aramco. For example, the expert noticed that the EldoS RawDisk driver altered the infected host's system time to August 2012, just a day before the expiration date of the driver's temporary license. The license was the same used in the 2012 attacks.
"The current attack campaign has several TTP overlaps with the original Shamoon campaign, especially from a targeting and timing perspective. Also, Disttrack malware used in the recent attacks is very similar to the variant used in the 2012 attacks, which uses the exact same RawDisk device driver as well (down to the same, temporary license key). The main purpose of the Disttrack malware is to overwrite files and storage partitions in an attempt to destroy data and render the system unusable. To maximize its destruction, the Disttrack tool attempts to spread to other systems on the network using stolen administrator credentials, which suggests that the threat actors had previous access to the network or carried out successful phishing attacks prior to the attack using Disttrack." states PaloAlto Networks.
January 2017 - a second variant of the Shamoon 2 targets virtualization products
In January, researchers at Palo Alto Networks discovered a new strain of the Shamoon 2 malware that was targeting virtualization products.
The previous instance of the Shamoon 2 malware was used at least in a targeted attack against a single Saudi organization, the Saudi Arabia's General Authority of Civil Aviation (GACA).
Now the second variant of the threat had been configured to start wiping infected systems at 1:30 AM (Saudi Arabia time) on November 29, when the employees of the targeted organization' were likely at home.
The first variant of Shamoon 2 analyzed by the experts presented a default configuration that allowed the execution of the disk-wiping component at 8:45 pm local time on Thursday, November 17.
The two payloads present many similarities, but the analysis of the experts revealed some differences.
The second Shamoon 2 variant included credentials for virtualization products from Huawei; it was developed to target virtual desktop infrastructure (VDI) products such as FusionCloud.
This circumstance suggests that attackers were aware that the target organization used this specific virtualization product. The hackers attempted to breach the target networks using the default credentials reported in the product official documentation; this means they were hoping that the targeted organizations had not changed them.
According to the experts, threat actors may have had access to appliances hosting the infrastructure.
"VDI solutions can provide some protection against a destructive malware like Disttrack through the ability to load snapshots of wiped systems. Also, since FusionCloud systems run a Linux operating system, which would not be susceptible to wiping by the Windows-only Disttrack malware, this could be seen as a reasonable countermeasure against attacks like Shamoon," reads the blog post published by Palo Alto Networks.
"However, if the attacker was able to log into the VDI management interfaces using the account credentials they could manually carry out destructive activities against the VDI deployment, as well as any snapshot."
Researchers observed that communications module used by the threat was configured without a C&C, the module completely lacks any IP address or domain name for a C2 server within its configuration.
Symantec speculates the credentials used by the attackers may have been provided by another cyber espionage group called Greenbug.
Greenbug hackers used the Ismdoor remote access Trojan (RAT) and other tools in attacks against organizations in the Middle East.
The Ismdoor malware allows to establish a backdoor on the target machine and leverages PowerShell for command and control (C&C).
The group targeted organizations in multiple industries, including aviation, investment, government and education organizations in several countries (i.e. Saudi Arabia, Iran, Iraq, Bahrain, Qatar, Kuwait and Turkey, and a Saudi company in Australia).
"Greenbug was discovered targeting a range of organizations in the Middle East including companies in the aviation, energy, government, investment, and education sectors. The group uses a custom information-stealing remote access Trojan (RAT) known as Trojan.Ismdoor as well as a selection of hacking tools to steal sensitive credentials from compromised organizations." states the Symantec report on Greenbug.
"Although there is no definitive link between Greenbug and Shamoon, the group compromised at least one administrator computer within a Shamoon-targeted organization's network prior to W32.Disttrack.B being deployed on November 17, 2016."
The Greenbug group launched spear phishing attacks against its victims to trick users into downloading the malicious code onto their systems. The email messages are fake business proposals that delivered an RAR archive that stored a clean PDF and a compiled HTML help file (.chm) that contained the Ismdoor Trojan.
The Greenbug hackers exploited the alternate data streams (ADS) to avoid detection.
"Windows Alternate Data Streams (ADS) is a feature of NTFS which is used to store details about a file. The information stored in ADS is hidden to the user, which makes it an attractive feature for attackers. ADS is sometimes abused by attackers to hide malware or other hacking tools on a compromised computer." continues the analysis.
Researchers at Symantec speculate that Greenbug may have supplied credentials for the Shamoon 2 attacks. The experts detecting the Ismdoor malware on an administrator computer belonging to one of the organizations targeted with Shamoon 2.
It is important to highlight that there is no technical evidence that Greenbug and Shamoon 2 attackers are linked, but it is interesting to note that Greenbug seems to have vanished one day before the November 17 attacks.
"The presence of Greenbug within an organization prior to the destructive attack involving W32.Disttrack.B provides only a tentative connection to Shamoon. Greenbug's choice of targets and the fact that Ismdoor and associated tools downloaded by the threat appear to have gone quiet a day prior to the November 17, 2016, Shamoon attack is, however, suspicious." reads the report.
Shamoon 2 … it's alarming
A few days ago, On Monday, the Saudi Arabian labor ministry confirmed it had suffered a cyber-attack such as another chemical firm that reported a network disruption.
A state news agency confirmed the attack against the labor ministry but excluded any impact on the data.
The Reuters agency also added that the telecoms authority is inviting all parties to be vigilant for the spreading of a new version of the Shamoon 2.
According to security experts, the threat actor behind the Shamoon attacks was likely working on behalf of the Iranian government in 2012.
"The Shamoon hackers were likely working on behalf of the Iranian government in the 2012 campaign, and the more-recent attacks" Adam Meyers, vice president with cyber security firm CrowdStrike reported to Reuters. "It's likely they will continue."
The State-controlled Al Ekhbariya TV confirmed that the dreaded malware targeted multiple Saudi organizations
The Sadara Chemical Co, a joint venture firm owned by Saudi Aramco and Dow Chemical, confirmed it had suffered a network disruption last week, the oil company had stopped all services related to the network.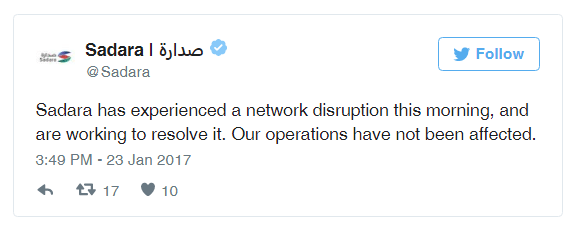
Figure 4 - Sadare Tweet that confirmed the cyber attack
As part of the incident response, the company had stopped all services related to the network.
Reuters said that other companies in the petrochemicals Jubail hub also experienced network disruptions.
"Those companies sought to protect themselves from the virus by shutting down their networks, said the sources, who declined to identify specific firms." states Reuters.
Saudi Arabia Computer Emergency Response Team (CERT)'s Abdulrahman al-Friah confirmed to Al Arabiya that at least 22 institutions were affected by the wave of Shamoon attacks.
"We cannot definitely determine the financial costs of such breaches yet as it depends on each institutions platform. Websites which sell and buy will obviously be affected the most," Friah said.
Who is behind the attack?
Researchers believe the attacks were launched by Iranian state-sponsored hackers targeting Saudi Arabian infrastructure in retaliation for cyber-attacks against Iranian petrochemical facilities.
Iranian facilities suffered a string of cyber-attacks last year between July and September, a fire at the Bou Ali Sina Petrochemical Complex in Iran caused $67m in damage.
The first incident occurred on July 6, in the Bou Ali petrochemical plant on the Persian Gulf coast, a couple of days after the fire was put out, a liquefied gas pipeline exploded in the Marun Oil and Gas Production Company. On July 29, another fire occurred at the Bisotoon petrochemical plant.
The incidents were originally blamed on human error, but after another explosion of a gas pipeline near Gonaveh the Iranian Petroleum Ministry started an investigation to understand the real cause of the anomalous string of incidents.
"The Iranian Petroleum Ministry, in charge of all of the affected sites denied the plants were sabotaged and the Iranian oil minister Bijan Namdar Zanganeh said the fires and explosions were due to technical faults and human error," reported Time.com. "However when an explosion in a gas pipeline near Gonaveh, which killed a worker, and another fire in the Imam Khomeini petrochemical plant, occurred within hours of each other on Aug. 6, the ministry refused to comment until after investigations. "
Mr. Abolhassan Firouzabadi, the secretary of Iran's Supreme National Cyberspace Council, confirmed that a team of investigators were working on the case trying to understand if the incidents are linked and if they were caused by a cyber-attack.
"The viruses had contaminated petrochemical complexes," Brig. Gen. Gholam Reza Jalali told the IRNA news agency. "Irregular commands by a virus may cause danger."
In this scenario, we can imagine an ongoing cyber dispute between Iran and Saudi Arabia.
There is also another speculation about possible culprits, in a second scenario a third nation-state actor that could have spread the Shamoon 2 variant in the wild to feed political tension in the Middle East.
As usual, when dealing with cyber-attacks, the attribution is a difficult activity, and a foreign government could benefit from a crisis in the area.
References
http://securityaffairs.co/wordpress/55634/cyber-crime/shamoon-2-greenbug.html
http://securityaffairs.co/wordpress/55643/cyber-crime/shamoon-2-saudi-arabia.html
http://www.symantec.com/connect/blogs/shamoon-attacks
http://securityaffairs.co/wordpress/55703/cyber-warfare-2/shamoon-resurrection.html
https://www.symantec.com/connect/blogs/shamoon-back-dead-and-destructive-ever
http://securityaffairs.co/wordpress/55235/malware/shamoon-2-virtualizations.html

Get your free course catalog