Static malware analysis
Starting here, I would like to share the results of my recent research into malware analysis. We will begin with some basics and proceed to advanced levels. In this first installment, we will discuss the techniques involved in static analysis of malware. I will also include some files for illustrative purposes in this document.
Before we directly move onto the analysis part, let us set up context with some definitions.

Learn ICS/SCADA Security Fundamentals
What is malware?
Malware is any software that does something that causes detriment to the user, computer, or network—such as viruses, trojan horses, worms, rootkits, scareware, and spyware.
Malware static analysis
Basic static analysis consists of examining the executable file without viewing the actual instructions. Basic static analysis can confirm whether a file is malicious, provide information about its functionality, and sometimes provide information that will allow you to produce simple network signatures. Basic static analysis is straightforward and can be quick, but it's largely ineffective against sophisticated malware, and it can miss important behaviors.
Enough with definitions -- let's get down to Malware Static Analysis Techniques.
Malware static analysis techniques
Uploading the results to VirusTotal
The very first technique in static analysis is to upload the suspicious executable to VirusTotal, which runs the executable against several AV solutions and gives the result. For example, the below file states that the detection ratio is 17 out of 57.
Finding strings
Searching through the strings can be a simple way to get hints about the functionality of a program. For example, if the program accesses a URL, then you will see the URL accessed stored as a string in the program.
Microsoft has a utility called "Strings". When Strings searches an executable for ASCII and Unicode strings, it ignores context and formatting, so that it can analyse any file type and detect strings across an entire file (though this also means that it may identify bytes of characters as strings when they are not). Strings searches for a three-letter or greater sequence of ASCII and Unicode characters, followed by a string termination character.
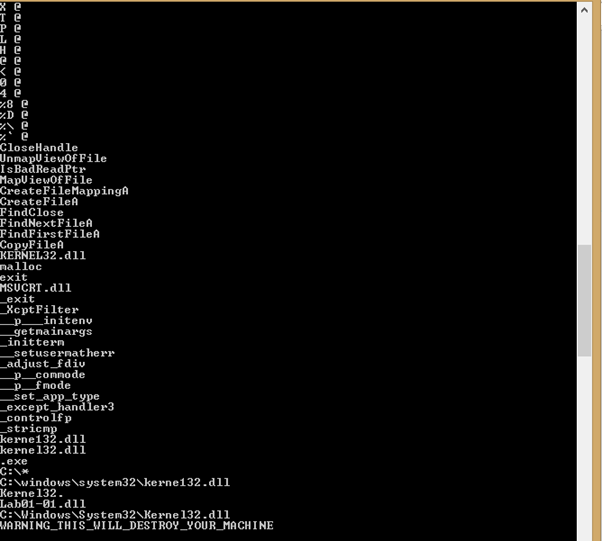
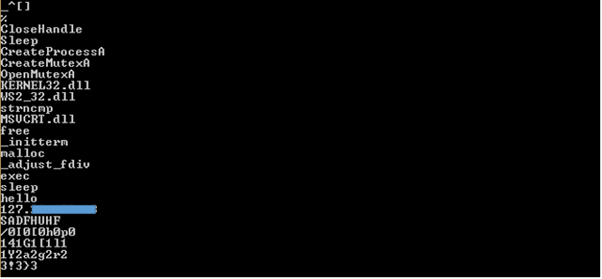
Below are some examples of strings from which important information can be revealed. Using the Strings utility, files can be searched with following command at the cmd: Strings <filename>
Example 1: Below is a string extraction of keywords from a malicious executable. As we can see, it gives us good information that functions like "FindNextFileA" and "FindFirstFileA", which shows that this executable will search for a file, and then combining that with "CopyFileA" means that it will find a file and replace it with another file. Another important point to note that is about "Kerne132.dll". This is a misleading text and should not be confused with "Kernel32.dll".
Example 2: Below is another extraction from a string utility. It shows us that usage of "CreateProcessA" will create a process. Commands like "Exec" and "sleep" are used to control a remote file. It can be a bot as well, and then an IP field, which can be the IP of a controlling server.
Example 3: Below is another example of an extraction using Strings. Interesting fields are "InternetOpenURLA" which states that it will connect with some external server to download something, and then we have a http:// file also, which even clarifies the server address from which it will connect and download.
How to check if a malware code is obfuscated or not?
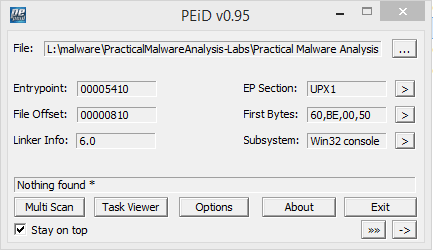
Often malware writers obfuscate their codes so that the files are hard to read. When a packed program runs, a wrapper program also runs around to unpack it. With static analysis, it is really hard to predict which files are packed unless it is clearly evident that they are. For example, tools like PEid sometimes are able to tell that the files are packed. In the below figure, it is clearly evident that files are packed with UPX.
Files which are UPX packed can be unpacked by the following command:
- upx –o <newfilename> -d <packedfilename>
PE file sections
Information gathering from Portable Executable (PE) file format
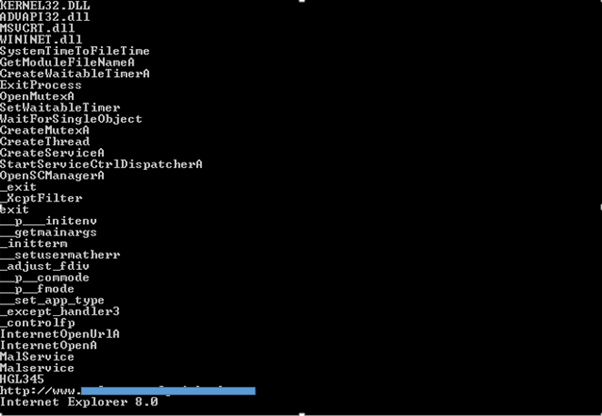
PE file format is used by Windows executables, DDLs etc. It contains the necessary information for Windows OS loader to run the code. While examining the PE files, we can analyse which functions have been imported, exported and what type of linking is there i.e. runtime, static or dynamic.
PE file sections
A PE file contains a header and some more important sections. Under these sections there is some useful information. Let's understand these sections as well.
- .text: This contains the executable code.
- .rdata: This sections holds read only globally accessible data.
- .data: Stores global data accessed through the program.
- .rsrc: This sections stores resources needed by the executable.
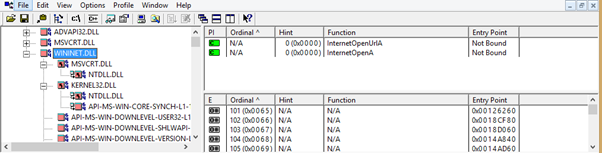
- Most often malware writers use dynamic linking in their code. For example, with the use of the tool Dependency Walker, we can see in the below screenshot that under WININET.dll are functions like "InternetOpenUrlA", which states that this malware will make a connection with some external server. Note: Wininet.dll contains higher level networking functions that implement protocols such as FTP, HTTP and NTP.
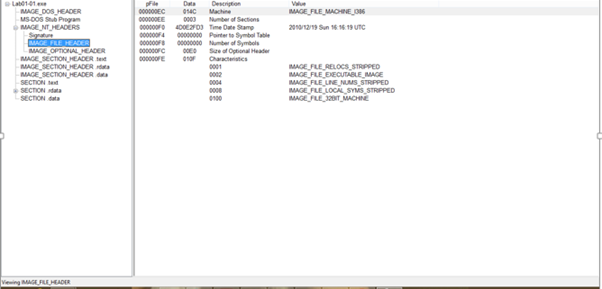
- Under the header, there is a subsection named "IMAGE_FILE_HEADER", which contains the timestamp field. This timestamp shows the compile time of the executable. This is very important information, since if the time is old, then there may a case that AV solutions might have a signature around it. However, this field is not reliable, since the compile can be changed easily by the malware writer.
- Suppose from static analysis, an analyst predicts that the executable will create a process and then suppose the following exec and sleep command is found, but there is no information found about the respective DLL, which has a function to connect with another server. In that case, the resource is hidden with the executable. Open the .rsrc section of PE file with a tool like Resource Hacker to gain more information regarding the malware.
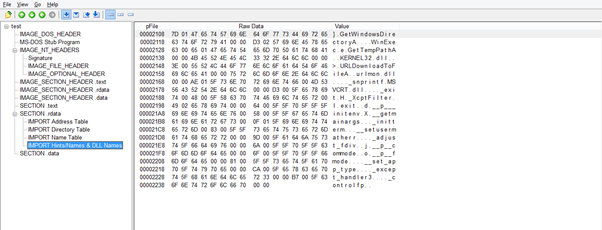
Below is the analysing of the above resource using PEview.

Get your free course catalog
As we have learnt with static analysis, there is very little information that can be gathered, but it is very useful too. In a coming article, I will bring in dynamic analysis though basic to the rescue.







