Lampion malware: what it is, how it works and how to prevent it | Malware spotlight
Introduction
The Lampion malware is spread through emails containing a link that downloads a .zip file with malicious files in it. It’s a banking Trojan: criminals developed it to steal information related to banking portals from the victim’s devices or make fraudulent transactions.
This form of malware is a big challenge from the banking security team’s point-of-view, as the accesses are performed through the victim’s device — a trusted device.

Learn Threat Modeling
How Lampion spreads
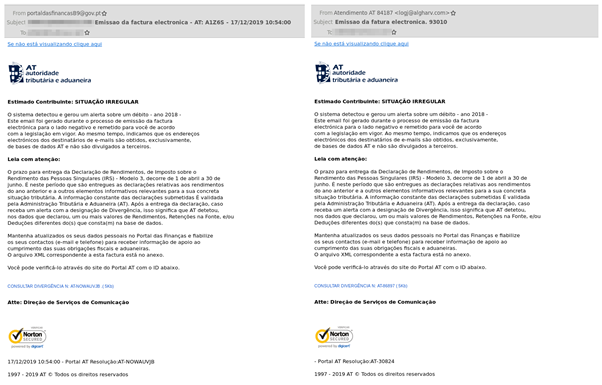
Lampion was identified by Segurança-Informática (SI) LAB in December 2019. This malware has spread via phishing campaigns using the Portuguese Government Finance & Tax’s email templates. It requires the recipients to click on a link within the email to avoid being misled by criminals. [CLICK IMAGES TO ENLARGE]
Figure 1: Lampion email templates
In the detail above, the email reports issues related to debt for the year 2018 and attaches a malicious file. When the victim clicks on the link available on the email, the malware gets downloaded from the online server generally hosted on AWS S3 buckets (a trusted repository).
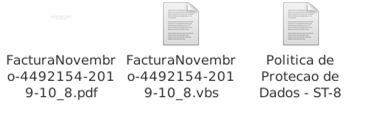
The downloaded file called “FacturaNovembro-4492154-2019-10_8.zip” has another three files inside: a PDF, VBS and a TXT file. The VBS file is responsible for starting the malicious chain when the victim manually executes the file.
How Lampion works
When the victim opens the VBS file, the infection chain starts. The script is a Trojan downloader that gets two files from the AWS buckets — a ZIP file called 0.zip and another file identified as a DLL (P-19-2.dll).
Figure 2: High-level overview of Lampion modus operandi
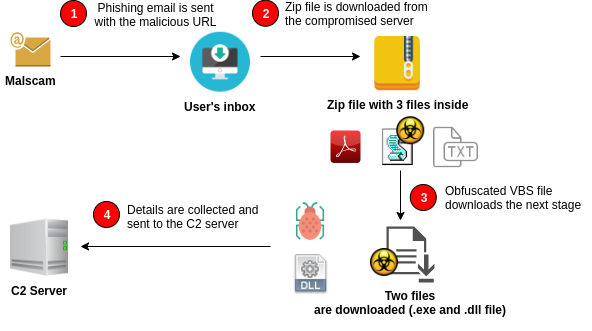
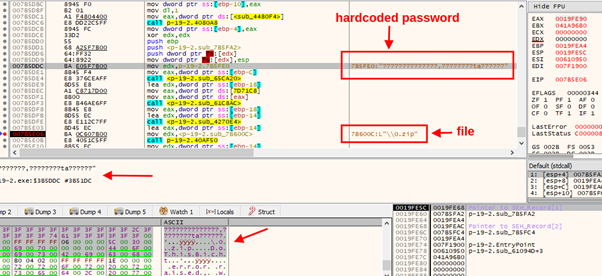
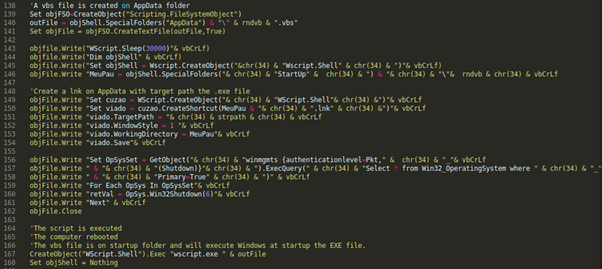
The VBS file is obfuscated to complicate its analysis and detection by antivirus engines. The downloaded files are the malware’s next stage, where the .dll file is the malware itself (in fact, it’s in the PE file) and the ZIP file, protected by a password, is a DLL that exports some of the crucial functions imported and executed by the first file (P-19-2.dll).
Figure 3: Password hardcoded inside the malware
As shown in Fig. 3, the password to unpack the ZIP file is hardcoded inside the P-19-2.dll file.
This file is renamed to an .exe extension and placed in the C:UsersuserAppDataRoaming directory. A .lnk file is also created in Windows StartUp Folder to execute the malware every time the operating system starts.
Figure 4: Part of the Lampion VBS script (the first stage)
Exfiltrated information to the C2 server
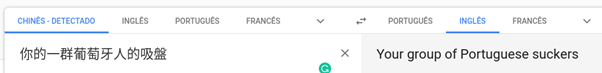
The Lampion Trojan is a malware developed to attack Portuguese citizens. The DLL file inside the 0.zip file initially downloaded has a name with a strong message for Portugal: “Your group of Portuguese suckers” (written in Chinese characters).
This is a threat that has only been observed attacking Portuguese citizens, with a landing page from Portuguese services such as “Autoridade Tributária e Aduaneira” (ATA) and “Energias de Portugal” (EDP).
When executed with success on the victim’s device with a Windows operating system installed, a lot of sensitive information is stolen and sent to the C2 server:
- Information about banking saved on cache and browser history
- Banking credentials saved on web browsers
- Sensitive information from other files (txt files)
The malware also has keylogger capabilities and dialog box spawning to get credentials typed by the victim.
Lampion capabilities include the following actions:
- Remote connection startup
- Network resources retrieval
- Network resources manipulations and redirect
- Folder path retrieval
- Messages communications
- Communications parameters changes
- Custom functions
- Dialog box spawning
- Code logic storage
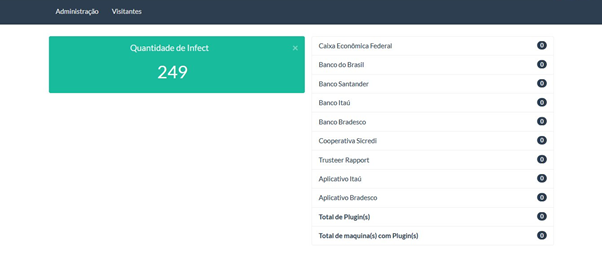
After getting details on the victim, the malware sends them to a C2 server available on the internet. Some details about the C2 portal available on an AWS EC2 server are presented below.
Through the C2 portal, malware operators can access all the exfiltrated information, the number of compromised victims grouped by bank organizations and some details about the victim’s device:
- Country
- Date and hour of access
- Operating system
- Computer name
- Installed antivirus engine
- Version
- Plugin
Conclusion: Prevention measures
This particular Trojan is being distributed through emails, via phishing and spearphishing waves. One of the first steps to mitigate this threat is never to download, open and execute an attachment received via email when the sender is unknown or the email subject raises any suspicion. In fact, this is a problem associated with the email protocol, as the final decision to open the email is always on the recipient side (even if the email is a part of a malspam campaign).

Learn Network Forensics
Nonetheless, some measures can be adopted in order to mitigate this malware in particular:
- Install antivirus/anti-malware Software: Maintain your device secure against emergent cyber-threats.
- Keep your antivirus software up to date: Don’t forget, updating your antivirus database is crucial to detect the most recent threats.
- Keep your operating system current: Install OS patches when they are available.
- Keep your personal information safe: Don’t keep your personal information on a text file on your desktop. The use of cryptographic vaults can help you to maintain your information secure.
- Think before you click: This is generally the major weakness leveraged by criminals to execute the malware on the victim’s devices.
Sources
- Targeting Portugal: A new trojan ‘Lampion’ has spread using template emails from the Portuguese Government Finance & Tax, Segurança Informática
- vbs.lampion, Malpedia