Exclusive – A Close Look at the Largest Credential Harvesting Campaign Via an IoT Botnet
Exclusive: MalwareMustDie discovered a criminal gang that is using SSH TCP direct forward attack technique in a large-scale operation.
The popular researcher MalwareMustDie published his first analysis of 2017, and his report is astonishing. The expert has uncovered a large-scale cybercrime gang that is harvesting credentials and credit card numbers from major websites all around the world leveraging on an IoT botnet.
MMD has published a detailed analysis of the harvesting technique used by cyber criminals that hit thousands of major web services and web servers across the world.

Become a certified reverse engineer!
The researcher has monitored the activity of the group and has determined the model of attack devised by the crooks that operated on a large-scale by powering both automated and manual attacks.
"A legitimate user who is having authentication privilege of an existing SSH connection can forward TCP protocol in the proxying mechanism. It is an almost common practice nowadays in a nutshell, especially to the services that are meant to be viewed from a local networking area." wrote MMD.
"This threat's definition is The abuse of SSH TCP forward legitimate usage, by performing automatic or manual attack to weak SSH accounts of remote devices (either servers and IoT), with brute-forcing account's credential or passwords, to perform malicious set of TCP attacks via TCP Direct Forward technique on SSH Forwarding functionality utilizing this "force-accessed" SSH connection to targeted remote services."
The attack method
To understand the importance of the criminal operation let us see how the attackers have operated.
The hackers have used an IoT botnet to launch a large-scale "data harvesting" campaign focused on the login credentials, email addresses a credit card data from target websites.
Once gathered the information, attackers used it to log into payment websites such as PayPal. They do not target the front-end of the web services instead they try to exploit APIs to access them.
The same set of credentials is then used in other attacks against gaming platforms and social networks.

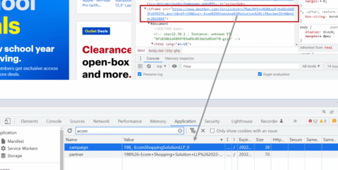
Figure 1 - Attacker Strategy published by MMD
The hackers try to maximize their efforts by trying to compromise SSH accounts to many mail servers worldwide.
Often such kind accounts are less protected and easy to exploit for hackers. The hackers powered brute-forcing attacks through their botnets; they used to send specific TCP packets to vulnerable servers to hack them.
"The attacker is grabbing credentials from the hackable targets from their infrastructure," continues the MalwareMustDie blog. "They manually perform the attack or daemonized the SSH connectivity to be TCP forwarded through some layers of hackable SSH accounts to perform the attack. The infrastructure of compromised SSH services and IoT devices are used as front-end cushion for the attack. They aimed for credential launched through several TCP attacks (HTTP/HTTPS or SMTP)."
"we have a recycle-like process for ultimate credential harvesting directed by hackers." reads MMD.
The hackers launched both automated and manual attacks with different characteristics in the way of making connections and performing attack sessions.
"Some typical characteristic in its logged activities have suggested a human's direct interactive during a session of attacks, supporting facts of the establishment for the connection used to conduct TCP forwarding that was manually set." wrote MMD.
Attackers can launch various forms of attacks mostly aiming HTTP (protocol) with and without SSL.
Malware Must Die have uncovered the following forms of attacks:
- Sending malformed HTTP requests to a targeted web server to exploit the service.
- Sending invalid HTTP method requests for mod-ssl vulnerabilities with the same purpose as above.
- Sending HTTP requests to force (brute) authentication in legitimate sites for user(s) and password(s).
- Sending HTTP requests to compromised sites to allegedly confirm suspicious activities.
- Sending SMTP requests to several email servers (Here forth is called as "MTA").
The analysis published by MalwareMustDie includes PoC codes in multiple attack scenarios; it includes screenshots of most seen abuses against major websites such as PayPal, LinkedIn, Facebook, Gmail, Royal Bank, AT&T, PlayStation Store, PlayStation Network, eBay, Ubisoft, Sony Entertainment Network, and many others.
The expert also shared reversed code and traffic analysis, along with mitigation measures.
According to MMD, the hackers harvested a huge quantity of email from major online email services, including Gmail, Yahoo, AOL, Microsoft (Live Mail & Hotmail), Mail.ru, Yandex, etc.

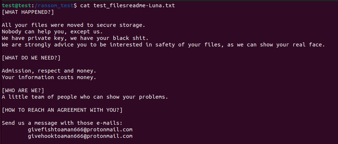
Figure 2- Harvested credentials
Focus on Italian websites under attack
MMD, with the support of the popular cyber security expert Odisseus, allowed me to prepare and share a list of the Italian websites targeted by the criminal gang.
We publish on exclusive the list of targeted Italian websites, the overall number of targets is 140, that includes many mail servers.
The complete and detailed list has been shared with Italian authorities to allow further investigations.
Among the victims there are:
- Alma Mater Studiorum Universita di Bologna
- Siae
- Ansaldo S.p.A. WAN
- Telecom Italia S.p.A.
- Universita degli Studi di Milano
- FAO Food and Agriculture Organization of the United Nations
- Bankadati Servizi Informatici Soc. Cons. p. A.
- Intesa Sanpaolo Group Services S.c.p.A.
- Cedecra Informatica Bancaria SRL
- DADAnet Italia
- BANCA CARIGE S.p.A.
- Italiaonline S.p.A.
- Tiscali SpA
- Fincantieri Cantieri Navali Italiani
- Server Plan S.r.l.
- Banca Popolare di Milano
- Telecom Italia S.p.A.
- FastWeb's Main Location
Security Affairs and Odisseus alerted the "Team Digitale" of the Italian Government that confirmed it is already working on the case.
Q&A with Malware Must Die
I have spoken with Malware Must Die asking for further details on the crime group and its TTPs (Techniques, Tactics, and Procedures).
Below the Q&A with MMD
Can we classify this harvesting campaign as one of the largest data breaches in term of the number of targeted organizations? Can you better explain in simple words for non-tech-savvy people how crooks are stealing information?
This is a mass credential harvesting process. The bad actors are exploiting weak sites, which are having the flaw in their web system and gather all usernames and passwords, along with the email addresses. Adult websites and live camera sites are a privileged target due to the lack of security.
They then also targeted finance payment portal sites like PayPal, but not targeting the front-end security on the website directly, but using the API on URI that allows some mobile device to access these payment sites. The attackers are "pumping" the gathered email addresses of these sites to get more financial data of users...see if they can be logged in with the same passwords.
The process is not stopping in here; they continue to hack using specific URLs to access other sites (i.e. Game sites like battlefield, PlayStation, Mojang, etc.) and check if they can log in with the same credentials. The crooks are going further attempting to access social network platforms like LinkedIn, Google accounts, Yahoo, Facebook, and many international portals too like Yandex, Rambler, or Mail. RU... at this point they also aim the access to several email addresses to see the data inside (if possible).
Lastly, they access some sites of Banking, online sell, in each specific country using specific email addresses from that country, like in Canada they hit Lowlaw.CA (the wholesale store online portal) and aiming RoyalBank (Canadian bank) to get the credential that can be used to hack further financial data.
At this point, comes the interesting part of the attack.
The hackers check the email servers in each related country of the email addresses previously collected, and first they scan where the servers are, then they check whether the email servers has IMAP or POP protocol.
For IMAP servers they try to hack with the credential collected via HTTP attack again, for the POP they try to access directly to the POP protocol and SMTP protocol in the attempt to get the direct access to the mailbox.
This happens to the overall email address data collected around the world,
In Japan for SMTP attack, we have like 220+ attack in Japan and 74 positive hack attempt, you have like 400 attacks in Italy and have like 140+/- positive hack attempts to the email servers, Germany has like 340+ positive hack attempts, and the USA suffers a lot bigger numbers.
This means that we are facing with a large-scale operation for mass stealing credential, I believe that main goal is to steal credit card data.
Which is the risk for LinkedIn, Gmail, Facebook Users?
Gmail, Facebook, or LinkedIn are sites with good security, but they are providing access to a mobile application which is often "less secure" and leverage on simplest authentication scheme with the URI and parameters sent through it (encrypted or not) when users access from his web browser.
The attackers are studying which format of URI is possible to exploit to bypass to exploit vulnerabilities in the target servers.
They are hackers so that they will try as much as possible attack patterns. And in this scheme, they automated a script program to make a DAEMON (a process , like a server, that ready to execute several tasks), which tunneling via SSH through hacked layers under the attacker infrastructure, and pushing the hack command to the targets RAPIDLY, and using as many pattern to test the AUTH scheme of the portals mentioned above.
However, mostly, the accounts that they already grabbed that have valid credentials can be logged in into such services. I checked for Gmail, Yahoo, Hotmail credentials with the only purpose to see if this hacking scheme works, and it did work.
The attack scheme starts with getting the raw materials (emails and passwords from weak sites such as gaming sites, adult sites, and so on). Recycle stolen data trying to attack the email servers or to Social Network Sites. Then they also tried to use the stolen data aiming banking sites, online payment sites, or sites like eBay and LobLaw.
Interestingly, adult sites are all having credit card database for payment scheme, and mostly weak in security.
Do you believe that it is a group of crooks? Why not state-sponsored action?
It was my first thought. This is a large-scale operation; it is the work of professionals. Continuing the investigation on the collector and working on the bad actors database we have collected over the years; we have compared the hacking scheme of this group with the ones of other threat actors. We have found a positive match for a group of crooks that we thought many of them have been arrested, but the recent harvesting campaign suggests some of them are not. Some members of the gang are still out there.
They are selling credit cards on their special website, and this is why they can have so many credit cards to sell on their website. Realizing, the actors behind these carding websites are the same that launched the harvesting campaign. We contacted the law enforcement providing it this information; the police are investigating the case.
The crooks are skilled professionals that can avoid being arrested. I think law enforcement has a hard task to track them.
Conclusions
This is a very complex operation currently under investigation by experts and law enforcement.
The report shared by MMD is full of interesting data, including geographical distribution of the victims (mostly in the US) and the overall list of targeted IP addresses, including the Italian ones.

Figure 3 - GeoIP Map for victim's network (MMD Report)
Below the information shared by Malware Must Die:
- Overall list of victims
- Positive targeted list
- List contains attackers origin and hacked IoT/ dialup SSH service (which are victims too)
MMD also provided suggestions to the sysadmin to detect ongoing attacks.
The best way to spot the attack is to analyze connections to their servers; admins can seek for the longest ESTABLISHED session in the SSH from the network that is unrelated to their activities as suspicious.
"Pick one process that linked to a connection, and you can elaborate the data based on the connection aimed (as the root of course), a set command like ps, ptrace+ *debuggers and list of files are useful to be used for detection," wrote MMD.
"Blocking for the threat is simple. For the Linux sysadmin iptables is good, for BSD users you can use ipfw, pf, or ipf, or as an option you can use the TCP wrapper compiled web application or services to be blocked by hosts.allow which will work just fine."
Below some samples to block the threat with both iptables and ipfw:
// iptables (linux)
sudo iptables -A INPUT -s 5.45.72.0/22 -j DROP
sudo iptables -A INPUT -s 5.45.84.0/22 -j DROP
sudo iptables -A INPUT -s 5.45.76.0/22 -j DROP
sudo iptables -A INPUT -s 5.45.64.0/21 -j DROP
// ipfw (freebsd)
ipfw add deny from 5.45.72.0/22 to any
ipfw add deny from 5.45.84.0/22 to any
ipfw add deny from 5.45.76.0/22 to any
ipfw add deny from 5.45.64.0/21 to any
Special Thanks to Odisseus who supported me in the analysis of the events.
References
http://blog.malwaremustdie.org/2017/02/mmd-0062-2017-ssh-direct-tcp-forward-attack.html

Become a certified reverse engineer!
http://securityaffairs.co/wordpress/56864/cyber-crime/ssh-tcp-direct-forward.html