Emotet returns in summer 2020 with new improvements
Introduction
Emotet is a self-propagating and modular Trojan first discovered in 2014 and a popular cyberthreat out in the world. It was initially developed as a banking Trojan but was reinvented as a distributor of other malware such as Trickbot and Ryuk, used to explore several and different scenarios after compromising a computer. This article will address the new changes to bypass antivirus engines used by TA542 — the threat actor that distributes this malware in-the-wild.
According to the US Department of Homeland Security's Cybersecurity and Infrastructure Security Agency (CISA), Emotet is seen as "one of the most prevalent ongoing threats", as it impacts state and local governments. In general, Emotet uses multiple methods for maintaining persistence and evasion techniques to avoid detection. It spreads via phishing spam emails containing malicious attachments or URLs.

Cybersecurity interview guide
Emotet’s wave in summer 2020
The malicious group (TA542) that operates the Emotet malware around the globe decreased Emotet’s activity during 2020. That five-month absence stretched from February 7th to July 17th, 2020. In fact, this was seen as the longest known holiday in the Emotet timeline since 2014.
However, Emotet continues to be a dangerous and severe threat and is often updated to avoid early detections. The break between February and July was a moment to improve the Emotet’s packer/loaders by crooks, as stated by Proofpoint.
The significant new changes and innovations include:
- The dissemination of the Qbot module as the primary payload instead of the well-known Trickbot
- A modification in the mail module that is now attaching benign attachments along with malicious ones
Proofpoint research pointed out small changes, including:
- The volume of target countries observed is significant. In this way, threat actors continue to use generic template emails such as COVID-19 to lure victims
- New improvements on the layouts of maldocs (Word attachments) with malicious macros embedded, PDF attachments with sensitive data and URLs to Word files available on the internet
- The threat actor continues to target a set of countries including Germany, Austria, Switzerland, the United States, the United Kingdom and Canada. It now also targets Indonesia, the Philippines, Sweden, India and Spain
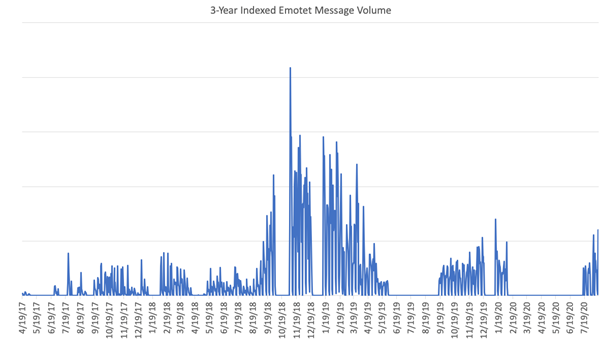
Figure 1 presents the volume of the Emotet messages in the last three years (from April 19, 2017, to August 18, 2020) from a visual perspective.
Figure 1: The volume of Emotet messages in the last three years
One of the most recently impacted countries is Spain, as mentioned above. Industry in Spain has been affected by this threat in large numbers — this piece of malware impacted 16.8% of Spanish companies in September of this year, which represents 2% over the global average.
Digging into the Emotet packer changes
During summer 2020, a new wave of Emotet was observed attacking several countries, with fresh improvements to avoid detection. The significant increase in Emotet loader downloads is associated with a change in the Emotet’s packer causing low detection by AV engines. This change makes Emotet detections hard and affects the blocking of the malicious URLs used to download the next stages from the internet.
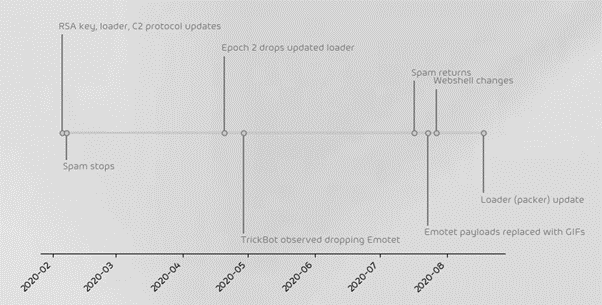
According to Hornetsecurity, on August 18th, 2020, changes on the Emotet’s loader were observed. The Emotet spam returns and the loader is now protected with a different and more sophisticated packer.
Figure 2: Emotet changes timeline from February to July 2020
As previously detailed, the Emotet packer led to a lower detection rate of the Emotet loader by AV engines. With this new trick, the threat can affect and bypass several security restrictions, increasing its impact. The unpacked loader has also received several updates making Emotet a real cyber weapon. Because of this, the volume of the Emotet loader downloads increased in contrast to the last months where a buffer overflow problem exploited as a vaccine called Emocrash almost stopped the threat.
Fresh Emotet templates
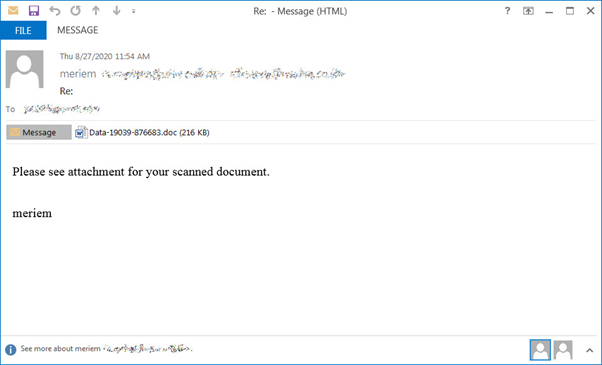
The Emotet dissemination schema is very popular. The threat is shared via a maldoc attachment (Word file) with a malicious email template inside or via URLs that download the target Word document from the Internet (often a compromised website).
Figure 3: Emotet malicious email template — September 2020
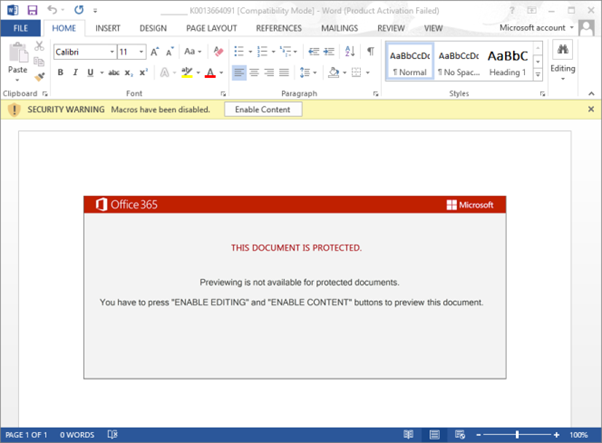
When the doc file is opened, a message will prompt the victim to “Enable Content” so that malicious macros will run to install the Emotet malware on the infected computer. To lure victims to enable macros, Emotet has been using a document template informing that it cannot be opened as it was created on the iOS system (a trap).
Figure 4: Doc file with malicious macro inside that executes the next stage (Emotet’s loader)
According to Hornetsecurity analysis, the share of download URLs pointing to the Emotet loader has increased in number (20% on 2020-08-19). This is due to the fact that Emotet doc files (Word docs) now use six or seven malicious URLS hardcoded instead of five to download the next stage, as seen in Figure 5.
Figure 5: Emotet loader URLs — September 2020
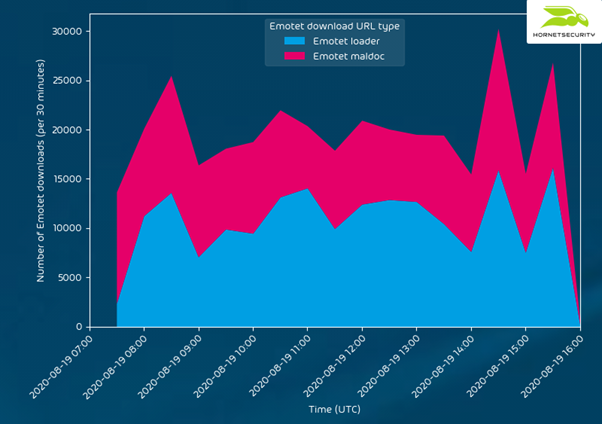
In addition, two days after the packer update on August 19th, 2020, the Emotet download statistics indicate that the loader was downloaded at a rate of around 25.000 times per hour on average, a 1000% increase. The next graphic shows the relation between the Emotet loader and Emotet maldoc downloads as well as their volume — results from August 19th, 2020.
Figure 6: Relation between the Emotet loader and Emotet maldoc downloads — August 2020 (Hornetsecurity)
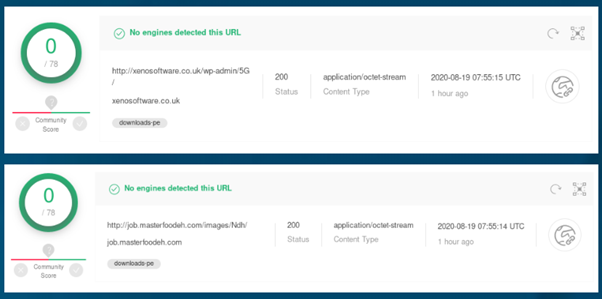
The increase is related to the recent changes in the Emotet packer. This fresh improvement is not detected by AV engines very well. As a result, Figure 7 below shows that the URLs hardcoded inside the analyzed Emotet loader are not listed on VirusTotal and the Emotet first stage is not blocked when executed on the victim’s computers.
Figure 7: Emotet URLs not detected after packer modification — August 2020
With this new trick, criminals can abuse this global threat to infect a large number of computers and organizations, and using Emotet to deliver additional payloads such as Trickbot and Ryuk in later stages.
Finally, it’s interesting to understand that Emotet’s success is the result of a set of well-defined and known steps, namely:
- It can spread via nearby Wi-Fi networks
- Emotet uses a polymorphic skeleton to change its characteristics, making it hard to detect
- Fileless approach such as PowerShell scripts makes post-infections difficult to analyze and detect
- Emotet take advantage of worm-like features that steal admin passwords and use them to spread throughout a network — thus infecting new users and machines
- It performs email hijacking to reach other victims
Prevention measures
Some prevention measures are presented in order to contain potential infections. They are not focused on Emotet threat, but at all kinds of threats that affect internet users in general:
- Do not download suspicious attachments or click on suspicious URLs. Detecting potential malicious emails and social engineering schemas is the most important thing to fight this war. In this sense, awareness programs are shown as the best way to promote internet users’ education
- Instruct users to create strong and complex passwords. Using MFA should be adopted as a mandatory rule of thumb to prevent unauthorized accesses
- Create a cybersecurity program that includes multilayered protection with business products to detect and block Emotet infections in real-time is needed
- And last but not least, keep the software, antimalware products and OS updated

Learn Web Server Protection
Conclusion
Emotet is operating with the same intensity registered at the beginning of this year. After a period of absence, the threat was once again a concern for several entities around the world. This piece of malware is considered the most widely spread malware targeting internet users today and operating since 2014. Emotet is a critical threat, as it is used to disseminate other dangerous malware such as Trickbot, QBot and Ryuk onto the victims’ computers. With this modus operadi in place, Emotet can perform different malicious activities: stealing stored passwords, cookies and banking information, and even executing ransomware attacks.
As Emotet is a wild threat that spreads via email, recognizing the used malicious templates is seen as an initial and important task to avoid malicious infections.
Sources
Emotet malware's new 'Red Dawn' attachment is just as dangerous, Bleeping Computer
Emotet, MITRE
Emotet Update increases Downloads, Hornetsecurity
Emotet alarm in Spain, more than 16% of businesses affected in September, Morning Tick
A Comprehensive Look at Emotet’s Summer 2020 Return, Proofpoint
Threat Report: Emotet Triple Chain Analysis 2019 – Portugal, Segurança Informática