BlackEnergy Used as a Cyber Weapon Against Ukrainian Critical Infrastructure
Introduction
Recently the researchers at ESET firm spotted a new wave of malware-based attacks that are targeting media outlets and energy companies in Ukraine. The threat actors rely on the BlackEnergy Trojan that is able to wipe hard drives of the infected machines.
The BlackEnergy is a DDoS Trojan that gained notoriety in 2008 when nations-state hackers used it during the Russia-Georgia conflict, when hackers launched cyber-attacks against the infrastructure of the Georgia.

Learn Incident Response
The experts have no doubts, the BlackEnergy Trojan was developed by a Russian hacker and originally used for DDoS attacks, bank frauds and spam distribution. Later a number of improved variants were used in targeted attacks on government entities and private companies across a range of industries.
According to the report proposed by experts at ESET in 2014, the malware targeted more than 100 government and industry organizations in Poland and the Ukraine, the security firm F-Secure reported other attacks based on BlackEnergy, which hit a target in Brussels.
F-Secure security advisor Sean Sullivan speculated that BlackEnergy detected in Brussels has been used in a targeted attack on the European Parliament or European Commission.
"A large number of state organizations and businesses from various industry fields in the Ukraine and Poland have been targeted in recent attacks. What would otherwise be a mundane scenario in today's world of cybercrime is spiced up by the fact that the malware-spreading campaigns have leveraged the tense current geopolitical situation in Eastern Ukraine and the use of a malware family with a rich history. The most recent campaigns are dated August 2014." states the blog post on VirusBulletin.
Malware researchers from ESET uncovered a hacking campaign that targeted hundreds of victims mainly located in Eastern Europe.
"We have observed more than 100 individual victims of these campaigns during our monitoring of the botnets," Lipovsky said. "Approximately half of these victims are situated in Ukraine and half in Poland, and include several state organisations, various businesses, as well as targets which we were unable to identify."
The experts noticed that counties infected with the BlackEnergy malware were already targeted by another cyber espionage campaign documented by F-Secure, dubbed CosmicDuke.
Further researches allowed the experts to collect evidence of the link between the CosmicDuke, Miniduke and OnioDuke Advanced Persistent Threat campaigns.
Who is behind the cyber espionage campaigns?
The experts speculated that CosmicDuke, MiniDuke and OnionDuke are the products of Russian state-sponsored hackers because the campaigns targeted governments with an interest in Russian affairs. The fact that CosmicDuke operations targeted users of illegal substances may also indicate the involvement of law enforcement agencies of the Russian Government.
The Ukraine blackout
Security believe malware represent a serious threat for ICS e SCADA systems in the critical infrastructure worldwide.
In the past other malware has targeted these critical components, the most popular one is Stuxnet that is considered the first cyber weapon in the history. Stuxnet has been used in a joint effort of the US and Israeli Governments to destroy the Iranian nuclear program in the nuclear plant in Natanz.
Other malware was later designed to target systems managed by the company in the energy industry, Havex, Shamoon and BlackEnergy are some examples of this malware.
Recently, the Ukrainian media TSN reported a prolonged blackout interested the Ivano-Frankivsk region of Ukraine on December 23th, the media speculated that the power outage was caused by a malware that disconnected electrical substations.
The hackers used a highly destructive variant of the BlackEnergy malware to compromise the systems at three regional power authorities in Ukraine that disconnected electrical substations in the country. It seems that a cyber-attack disrupted the local energy provider Prykarpattyaoblenergo and caused a major power outage that left half population in the region without electricity.
The Ukraine energy ministry confirmed blackouts and revealed that the Government is investigating on the causes.
A statement on the Security Service of Ukraine (SBU) website reported the discovery of malware on the networks of regional power companies. According to the SBU, the cyberattack was accompanied by a barrage of phone calls to their technical support, a circumstance that suggests a diversionary action leveraging on the resulting denial of service (DoS) attack.
"Security Service of Ukraine has warned Russian special services try to hit the computer network of the energy complex of Ukraine. Employees of the Security Service of Ukraine found malicious software in the networks of individual regional power companies. Virus attack was accompanied by continuous calls (telephone "flood") to numbers technical support supply. Malware localized. Continued urgent operational-investigative actions." states the SBU.
The attribution of the attack is not simple, we are only aware that the BlackEnergy malware has a Russian origin and that Russian has a political dispute with the Ukraine that had repercussion also on the cyberspace.
The KillDisk component
Experts at ESET discovered a new component in the BlackEnergy Trojan, the KillDisk, which is capable of destroying some 4000 different file types and rendering machines unbootable.
The KillDisk component characterized the instances of the malware used to compromise the energy companies in Ukraine, according to the experts it is slightly different from other versions. Below the list of new features observed by the experts:
Now it accepts a command line argument, to set a specific time delay when the destructive payload should activate.
It also deletes Windows Event Logs: Application, Security, Setup, System.
It is less focused on deleting documents. Only 35 file extensions are targeted.
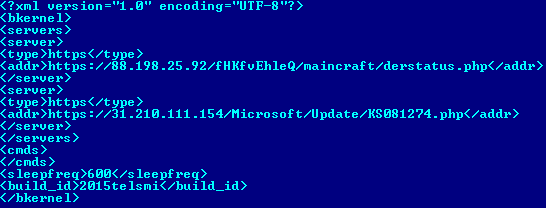
Figure 1 - The BlackEnergy configuration example used in 2015 (ESET)
The strain of malware detected by ESET in 2015 also uses a previously unknown SSH backdoor to access the infected systems, in addition to BlackEnergy backdoor.
"ESET has recently discovered that the BlackEnergy Trojan was recently used as a backdoor to deliver a destructive KillDisk component in attacks against Ukrainian news media companies and against the electrical power industry." states the blog post published by ESET.
The researchers at ESET highlighted the presence of Build IS numbers in the BlackEnergy code, these data could provide information useful for the attribution of the malicious code. In the specific case the build identity numbers suggest the possible involvement of Russian hackers, but ESET avoids confirming it.
"Apart from a list of C&C servers, the BlackEnergy config contains a value called build_id. This value is a unique text string used to identify individual infections or infection attempts by the BlackEnergy malware operators. The combinations of letters and numbers used can sometimes reveal information about the campaign and targets." states the post "We can speculate that some of them have a special meaning. For example, 2015telsmi could contain the Russian acronym SMI – Sredstva Massovoj Informacii, 2015en could mean Energy, and there's also the obvious "Kiev"."
According to Symantec, one of the most interesting features observed in the destructive BlackEnergy variant used in the attacks is that the malware attempts to stop and delete a service named "sec_service". This service belongs to 'Serial to Ethernet Connector' software developed by Eltima and allows access to remote serial ports over network connections. The circumstance suggests that hackers specifically designed the malware to hit SCADA and have a deep knowledge of legacy SCADA systems. Many SCADA architectures still use serial ports for RTU (Remote Terminal Unit or Remote Telemetry Unit) communications, the operators use them for communicating remotely with control systems and monitor device failure.
Interfering with the sec_service the attacker can block remote communications increasing the potential for damage for the targeted system.
It is possible to cause a prolonged power outage with a malware?
On this point there are different opinions, some experts argue that infecting critical components of a process can lead to the paralysis of activities, including those of a power plant. Malware theoretically can lock processes critical for the critical infrastructure.
The popular security expert Brian Honan, explained that there is no publicly acknowledged evidence that the infection observed in the Ukraine are linked to the power outage.
"I am still trying to piece this together," says Dublin-based information security consultant Brian Honan, who is a cybersecurity adviser to the association of European police agencies known as Europol. "We have reports of a power outage and reports of systems being infected with a computer virus, but no connection - at least a publicly acknowledged one - that the two are related. In other words, how would a wiper-type virus stop the station from producing power?"
Michael Assante, formerly a CSO at NERC, speculates that attackers have used much more than malware to trigger the blackout.
"A file-wiper function can certainly disrupt the SCADA system, but that alone does not account for the outage," he says. "We suspect an attacker manually interacted with an infected machine, like an HMI - human-machine interface - to command breakers to open," although adding that this is still just a theory. "The wiper function could then have been used to extend the outage by denying the SCADA system, but the impacted Ukrainian utility was still capable of resorting to manual operations to re-close breakers and energize their system." Assante said in a Jan 5 SANS Institute newsletter.
He also highlighted that the cellular telephone network denial-of-service attack observed in concomitance with the power outages may be part of a strategy implemented by the attackers that aimed to prevent energy operators from remotely controlling the affected systems.
"The Ukraine has had power grid reliability problems in the past, so that probably means they were dependent on remote access," said the industrial control system cybersecurity expert Joe Weiss "noting that such remote access may be provided just not via the Internet, but also via cellular networks."
The SandWorm APT
According to a report published by the iSIGHT Partners, the cyber-attack against a Ukraine power station has been managed by a Russian group called Sandworm.
The researchers at iSIGHT's linked the KillDisk to the BlackEnergy 3 used by Sandworm in the past.
"Last week iSIGHT's sources provided us with the same KillDisk malware published by Rob Lee of SANS and Dragos Security. As ESET has, we place this malware within the greater context of activity tied to BlackEnergy 3, which we believe is Sandworm Team. We believe this KillDisk malware is related to the destructive malware leveraged during Ukrainian elections in October. At the time, CERT-UA connected that incident to BlackEnergy 3. Symantec has since verified those claims. Furthermore, iSIGHT's own sources indicate that BlackEnergy 3 malware was deployed on at least one of the Ukrainian power systems affected by KillDisk." wrote John Hultquist, director of cyberespionage analysis at iSight Partners.
The threat actors launched a spear-phishing campaign across the Ukrainian power authorities to spread the destructive variant to the BlackEnergy leveraging on Microsoft Office documents.
At the beginning of March 2015, the experts spotted a cyber-attacks using BlackEnergy2 / 3 malware against broadcasting companies of Ukraine. The phishing emails included malicious documents (.xls and .pps) containing macros and JAR-file, respectively, which in turn launched a PE-file.
The attackers used subjects and documents naming referring the crisis in the area and a mobilization of the revolutionary events. Below an example of one these messages.
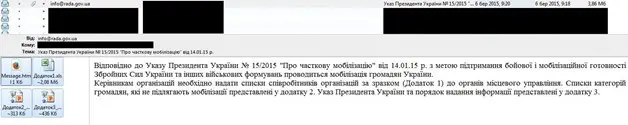
Figure 2 - Spear Phishing Email
The attribution of the attack is not simple, we are only aware that the BlackEnergy malware has a Russian origin and that Russian has a political dispute with the Ukraine that had repercussion also on the cyberspace.
According to a previous report published by iSIGHT on the Sandworm, the APT has been active since at least 2009. In 2014, the Russian group targeted a Polish energy firm, a Western European government agency and also a French telecommunications firm.
The experts began the investigation in late 2013 when the NATO alliance was targeted by the SandWorm group with various exploit kits. The experts spotted SandWorm APT using a critical zero-day exploit in August 2104, when the hackers targeted the Ukrainian government, in the lead-up to the NATO summit in Wales.
"In late August, while tracking the Sandworm Team, iSIGHT discovered a spear-phishing campaign targeting the Ukrainian government and at least one United States organization. Notably, these spear-phishing attacks coincided with the NATO summit on Ukraine held in Wales." states the report published by iSIGHT.
Security experts speculated that the intensification of the cyber dispute between Russian and Ukraine could have increased the likelihood to discover operations that went under the radar for so long.
Figure 3 - Sandworm SPT report (iSight)
Below chronological details provided by the researchers on the Sandworm activity:
- The NATO alliance was targeted as early as December 2013 with exploits other than the zero-day
- GlobSec attendees were targeted in May of 2014 with exploits other than the zero-day
- June 2014
- Broad targeting against a specific Western European government
- Targeting of a Polish energy firm using CVE-2013-3906
- Targeting of a French telecommunications firm using a BlackEnergy variant configured with a Base64-encoded reference to the firm
The SandWorm hacking team sent spear-phishing emails with malicious attachments to compromise the victim's machine, the threat actors mentioned a global security forum on Russia and a purported list of Russian terrorists.
Another element that suggests Russia is responsible for the cyber espionage campaign are codes discovered on the C&C server, located in Germany, that had not been properly secured and that contains Russian-language computer files that had been uploaded by the hackers.
"They could have closed it off, and they didn't," he said of the server. "It was poor operational security."
The Ukraine's CERT already reported numerous attacks against Ukrainian media leveraging the BlackEnergy malware, the offensive was intensified in concomitance the local elections.
"Recently, a number of Ukrainian media in the days of local elections was attacked by unknown hackers." states the UA-CERT "In general, I would like to note that the threat has the character of a well-planned order to show the ability of abnormal function compromised corporate media networks by using a tool such hackers as Black Energy (Win32 / Rootkit.BlackEnergy, Backdoor.Win64.Blakken), which is used to conducting APT-attacks."
Conclusion
The outage is considered by Information warfare and security experts a milestone in the history of cyber-attack. It is the first time that a power outage has been caused by hackers using a malware.
The Intelligence experts of many countries are already working with operators in critical infrastructures to avoid that similar techniques could in the future to target other power operators around the world.
"What is now true is that a coordinated cyber-attack consisting of multiple elements is one of the expected hazards (electric utilities) may face," said SANS ICS Director Michael Assante.
"We need to learn and prepare ourselves to detect, respond, and restore from such events in the future."
References
http://securityaffairs.co/wordpress/43281/malware/blackenergy-targets-ukraine.html
http://securityaffairs.co/wordpress/43321/hacking/ukraine-attack-caused-power-outage.html
http://securityaffairs.co/wordpress/28582/cyber-crime/blackenergy-lite-targeting-eu.html
http://securityaffairs.co/wordpress/32071/cyber-warfare-2/miniduke-cosmicduke-onionduke.html
http://securityaffairs.co/wordpress/43413/malware/sandworm-apt-ukrainian-power-outage.html
https://cys-centrum.com/ru/news/black_energy_2_3
http://www.dpstele.com/scada/introduction-fundamentals-implementation1.2_c.php?
http://www.sbu.gov.ua/sbu/control/uk/publish/article?art_id=170951&cat_id=39574

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
http://www.databreachtoday.com/ukrainian-power-grid-hack-9-questions-a-8781