Hacking ATMs: The New Wave of Malware
Introduction
In recent weeks, security experts at Kaspersky Lab have observed several attacks on Automated Teller Machines (ATMs) which were infected by malware dubbed Tyupkin. Tyupkin is one of the most popular malwares used by criminals to compromise ATMs and force these machines to release cash on demand. Experts at Kaspersky Lab collected evidence that Tyupkin infected at least 50 ATMs, mainly in Eastern Europe.
Tyupkin is just one of the different strains of malware used in the cyber criminal ecosystem to hack ATMs. In May 2013, security experts spotted another ATM Trojan dubbed Padpin; meanwhile in October 2013, malware researchers isolated samples of another malware dubbed Ploutus that was circulated to compromise banking machines and steal cash from them.

Learn Vulnerability Management
In this post, we will try to analyze each of the above ATM malware, suggesting countermeasures to defend the Automated Teller Machines.
Hacking ATMs
Cyber criminals are adopting even more creative and sophisticated tactics to collect users' personal information. Banking is one of the industries most targeted by cyber criminals. Very interesting are the techniques adopted by criminals to steal money with malicious code or to capture users' PINs directly from the ATMs.
"It just blows you away how sophisticated these folks are in thinking this stuff up,"says Bryan Sartin, director of the team at Verizon Communications that investigates data breaches.
US Intelligence estimated annual losses from ATM skimming at more than $1 billion in 2008. In the past, cyber criminals used phony number pads and skimmers to steal debit card PIN data, a risky practice due to the necessity to deploy the sniffing equipment and then come back to remove it while avoiding surveillance.
For this reason, cyber criminals have evolved their attack schema to steal users' PINs directly from ATMs and remote locations like gas pumps. The hackers exploit banks' wireless Internet connections used by financial institution to monitor ATM cash flow and update software.
"Regulators at the Federal Financial Institutions Examination Council warned in April that the ATMs of small and midsize banks are preferred targets for criminals who hack bank Web pages to boost ATM withdrawal limits and then clean out people's accounts," reports Bloomberg Businessweek.
Criminals are able to capture PINs remotely, according to a Verizon report. Another common tactic is to get jobs with technical-support companies that give them access to ATMs, then installing malicious code that can steal and transmit PIN data back to the attackers via e-mail address or through a phone line.
Remote hacking of Web-connected ATMs is a serious problem that occurs very frequently. In March, the FBI identified 17 people involved in a card fraud that stretched from Bulgaria to Chicago.
The technology used in these attack schemas is available in the cyber criminal ecosystem. Criminals could easily acquire memory chips and transmitters that enable to assemble PIN hacking devices, thin and light enough to be hidden easily in ATM installed by banks.
In December 2013, security experts spotted a wave of attacks against ATMs. The criminals cut a piece from the chassis of the Automated Teller Machine to expose the USB port and plug in USB drives carrying their malicious code.
A detailed description of the technique was presented by two German researchers at the last Chaos Computing Congress in Hamburg, Germany. The technique was used against the ATMs of an unnamed European bank's cash dispenser.
The two researchers who presented the attack have requested to not divulge their identities. The event is dated back to July 2013 when a series of ATMs were being hacked despite the adoption of necessary and ordinary defensive measures. The attackers were able to steal the highest value banknotes to minimize the duration of the theft and the windows of exposure.
The results of the investigation revealed that cyber thieves were vandalizing the ATMs to infect them with USB sticks. After they compromised the cash machine, they patched the holes up, hiding any evidence of the attack. In these ways they targeted the device several times.
According to the investigators, the criminals have a "profound knowledge of the target ATMs." The malware itself appeared to be very complex and designed for the specific goal.
Forensic analysis of the infected machines revealed that the creation of the malicious code would have required a huge team of skilled developers. The experts believe it is not a prototype. Malware design requires a significant economic effort for a long time and the source appears sophisticated and perfectly written. The researchers also discovered that the software is the result of numerous improvements.
"For sure, they had to have a profound knowledge of ATMs … Most likely they actually had one to test. Either they stole one and reverse engineered the cash client, or most likely, they had someone on the inside," revealed one of the researchers.
Once it has infected the machine, the malware is triggered by an access code composed of 12 digits typed by cyber criminals, and the software launches a special interface. Instances of the malicious software were found on four targeted machines. The malware was able to display the amount of money available in each denomination of notes and presented a series of menu items to release them.
The investigators made an interesting discovery: the thieves, driven by mutual distrust, implemented an access mechanism to the money that requires the introduction of a double code, one for each component in the gang.
"But the crimes' masterminds appeared to be concerned that some of their gang might take the drives and go solo. To counter this risk the software required the thief to enter a second code in response to numbers shown on the ATM's screen before they could release the money," reported a post on the BBC.
The dual factor authentication process means the thief could only obtain the access code by phoning another gang member and telling them the numbers displayed. In case of failure, the ATMs would return to their normal state after three minutes.
The malware is also able to intercept information such as customer PIN numbers or account data, though its primary function is immediate extraction of cash.
Just for curiosity, the name of the key file was called hack.bat. The German researcher remarked that similar attacks could be observed soon elsewhere:
"I'm not sure this is the end attack, or the end game … We'll probably see this kind of malware on another bank, in another city, on another continent."
Tyupkin malware used to force ATM to dispense cash
In the majority of cases, criminals used to compromise ATMs by tampering them with card skimmers that are used to steal card data, but during the recent months, criminal organizations in Eastern Europe are demonstrating a great interest also in a different technique based on the hacking of the ATM machine with a malware.
The malicious code allows cyber criminals to compromise the ATM without using cloned credit cards and force it to release cash on demand. The Interpol conducted a joint investigation with researchers at Kaspersky Lab, which allowed them to discover that the Tyupkin malware that infected nearly 50 machines at banking institutions was from a particular manufacturer running a 32-bit version of Windows.
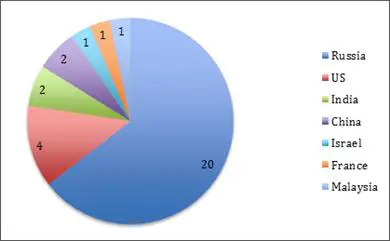
The investigators discovered that Tyupkin malware, which mainly hit banking institutions in Eastern Europe, may have spread to several other countries, including the US, India, and China.
Figure 1 - Tyupkin infection worldwide (Kaspersky)
The researchers had the opportunity to evaluate several variants of Tyupkin malware, so they were able to analyze improvements of the malicious code over the time. The latest variant, coded as .d, includes anti-debug and anti-emulation features, and the new variant is able to neutralize application security software from a particular vendor.
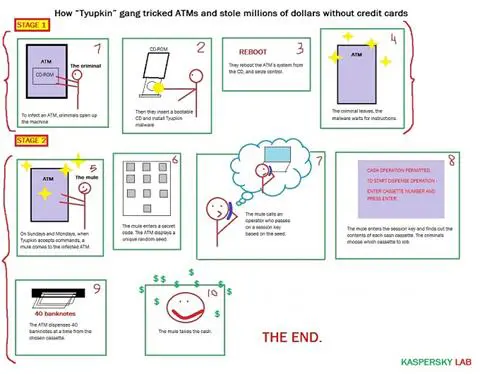
The cyber criminals target ATMs for which physical security measures were absent or limited, and running on outdated or not updated operating systems which could be easily compromised by the malware.
The attackers need to physically access the targeted ATMs and install the malware by uploading it from a bootable CD and copying a couple of files to the machine. One of the files is an executable and a debugging file, which is removed after a registry key is created to ensure persistence. The other one, once it has infected the ATM, allows the malware to wait for user input. To complicate the analysis of the investigators, the malware remains dormant during the week, except on Sunday and Monday nights, when it accepts requests from the criminals who have physical access to the ATM.
The choice to configure the malicious code to run only at specific times, together with the implementation of a challenge-response authentication mechanism, allows hackers to secure access to the infected ATM.
"When the key is entered correctly, the malware displays information on how much money is available in every cassette and allows an attacker with physical access to the ATM to withdraw 40 notes from the selected cassette," the researchers wrote.
ATM malware is designed to evade detection and to ensure the presence of only a single attacker on the banking system. Another precaution implemented by the developers of Tyupkin is the disabling of the local area network, a measure necessary to avoid any remote diagnostics which could detect malware and run countermeasures to neutralize it.
The basic command accepted by the malware via PIN PAD to the ATM are:
- XXXXXX – Shows the main window.
- XXXXXX – Self deletes with a batch file.
- XXXXXX – Increases the malware activity period.
- XXXXXX – Hides the main window.
As anticipated, the Tyupkin at this point requests a session key to prevent interaction with random users. If the user provides the above key it is possible to interact with the ATM. Once it has received the correct key, the malware shows the following message:
CASH OPERATION PERMITTED.
TO START DISPENSE OPERATION -
At this point, the criminal just needs to select the cassette number, and the ATM will dispense 40 banknotes from it. Be aware, because if the attacker fails to provide the correct key, the malware disables the local network and shows the message:
DISABLING LOCAL AREA NETWORK...
Another interesting element to consider is that the malware interacts with the ATM through the standard library MSXFS.dll – Extension for Financial Services (XFS). This library is a standard Microsoft library for which there is not public documentation, but that is anyway exploited by Tyupkin and other malicious codes.
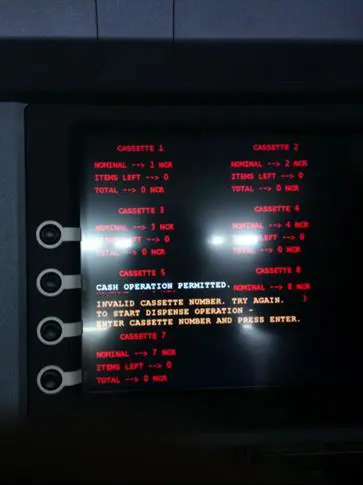
Figure 2 – Proof of Concept Image of the attack on the ATM
"The Tyupkin malware is an example of the attackers taking advantage of weaknesses in the ATM infrastructure," said Vicente Diaz, Principal Security Researcher at Kaspersky Lab's Global Research and Analysis Team. "We strongly advise banks to review the physical security of their ATMs and network infrastructure and consider investing in quality security solutions … The fact that many ATMs run on operating systems with known security weaknesses and the absence of security solutions is another problem that needs to be addressed urgently," Diaz added.
Figure 3 - Tyupkin attack (Kaspersky Lab)
Ploutus malware - How to rob ATMs with SMS messages
Tyupkin malware is just the most recent malicious code spotted by investigators. Experts at Symantec in March discovered a series of attacks against ATM machines based on Windows XP.
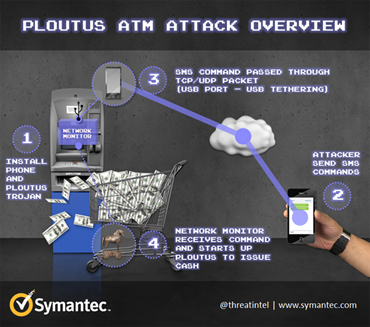
In March 2014, a team of researcher at Symantec detected a strain of malware dubbed Ploutus that is able to exploit a weakness in Windows XP based ATMs. The malware infected a few machines in Mexico, and according to the experts, the threat actors were able to steal cash just by sending text messages to the automated teller machine.
"The new variant was identified as Backdoor.Ploutus.B (referred to as Ploutus throughout this blog). What was interesting about this variant of Ploutus was that it allowed cybercriminals to simply send an SMS to the compromised ATM, then walk up and collect the dispensed cash. It may seem incredible, but this technique is being used in a number of places across the world at this time."
The experts at Symantec published an interesting analysis of the Ploutus malware, highlighting the level of sophistication of the attacks. As explained by the researchers, the attackers need to have physical access to the ATM in order to connect a mobile phone via USB tethering that allows them to share the network connection between the phone and the ATM.
Once the connection has been established, the attacker will start to send specific SMS commands to the phone attached or hardwired inside the ATM.
"Since the phone is connected to the ATM through the USB port, the phone also draws power from the connection, which charges the phone battery. As a result, the phone will remain powered up indefinitely."
The experts have detected several versions of the PLOUTOS malware. Most advanced instances are able to steal customer card data including the PIN, and the experts revealed the existence of a version that is also able to run a man-in-the-middle attack.
The attack scenario described by the experts at Symantec is composed of the following steps:
- The attacker physically accesses the ATM and connects a mobile handset with a USB cable, and then he injects the Ploutus Malware.
-
The attacker sends a couple of SMS messages with specific content to the mobile phone inside the ATM.
- The first SMS contains a valid activation ID, which is used by the attacker to activate the malicious code.
- The second SMS contains a valid dispense command that instructs the ATM to dispense the money.
- The mobile handset in the ATM receives the valid SMS messages and converts them into network packets that forward the ATM through the USB cable.
-
The malware is equipped with a Network packet monitor (NPM) component that sniffs all incoming traffic waiting for specific sequences representing the attacker's commands. When the NPM receives a valid TCP or UDP packet from the mobile phone, he will parse the packet and search for the number "5449610000583686" at a specific offset within the packet. In this way, the module is able to analyze the whole package of data, and once it has found a specific number, the NPM will read the next 16 digits and use them to construct a command line to run Ploutus. An example of such a command is shown below:
cmd.exe /c PLOUTOS.EXE 5449610000583686=2836957412536985
"In this version of Ploutus, the mule never sees the 16 digits, giving the master criminal added security and the ability to centrally control cash withdrawals. The code is active for 24 hours," reports Symantec.
- The amount for cash withdrawal is pre-configured inside the code of the malware.
- The attacker just needs to collect cash from the hacked ATM machine.
Ploutus was detected by security experts in different countries all over the world. Symantec explained that this type of attacks could benefit from the lack of security updates issued for operating systems no longer supported by vendors, like Windows XP.
The absence of proper defense measures such as hard-drive encryption represents a further element of concern, but the primary cause of such type of attacks is the lack of physical security for the computer inside ATMs. ATMs located in remote and isolated locations are usually more exposed to criminal activity.
The Padpin backdoor and the link to other ATM malware
We have analyzed a couple of the most popular malware used to compromise ATM machines, Tyupkin and Ploutus, but other malicious codes have hit banking systems in the past. In May 2013, researchers spotted another ATM Trojan, dubbed Padpin, which has something in common with malicious codes recently detected.
The development of malware capable of compromising an Automated Teller Machine needs a good knowledge of the architecture of these machines and of the devices they use. Security experts sustain that malware authors of the malicious codes recently spotted having had access to this kind of information.
A recently disclosed news report has created apprehension among malware researchers. The author of the malicious code used in the recent attacks has obtained information on the architecture of an ATM from a leaked programming manual for interacting with the physical components of Automated Teller Machines.

The manual might have helped malware authors to design the malicious application that was used to steal cash from ATMs.
Malware researchers at F-Secure firm have analyzed a few samples of the Padpin malware and discovered that its code is written to allow interaction with ATM components through the Extension for Financial Services DLL library(MSXFS.dll) that is specifically used by Automated Teller Machines. The library provides a special API for the communication with the ATM's PIN pad.
"Analyzing the code, we started wondering how the malware author knows which pin pad service name to provide to the API so that the program is able to interact with the pin pad device," the F-Secure researchers said in a blog post.
The researchers at F-Secure confirmed the circumstance that the DLL library used by malware authors is not officially documented by Microsoft, speculating on the fact that bad actors gain access to the information in a different way.
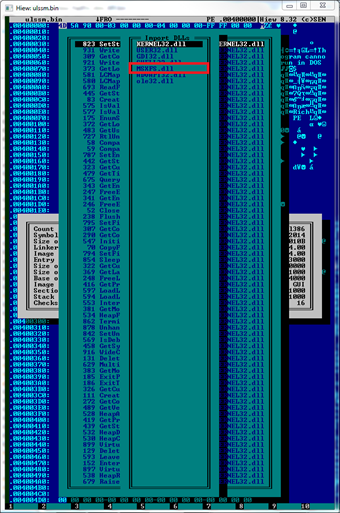
"It's a valid question because the pin pad service name used in the code is quite unique and it is very unlikely one can figure out the service name without documentation," added the expert.
Information on the Dll is available in a programmer's reference manual from NCR, which is a popular manufacturer of ATMs and point-of-sale devices. The document was posted on an eBook site owned by Chinese online search company Baidu.
According to the experts, it's not only malware programmers experienced in writing ATM applications who may have obtained precious information by reading the leaked manual, but also other coders.
"The documentation is helpful enough to give programmers some sample code as well," the researchers said.
While we are discussing … 18 ATMs were compromised in Malaysia
The use of malware to compromise ATMs is becoming a common practice of cybercrime. Latin American criminal gangs have recently hacked eighteen ATMs in Malaysia. The criminals have stolen nearly 3 million Malaysian Ringgit, or over US$900,000, from the banking machines according to the principal media agencies.
The media highlighted the fact that an RM100 chip, specific technical knowledge, and a free malware obtained over the Internet is all that is necessary to hack Automated Teller Machines (ATMs).
The revelation was made by a cybercrime expert, which released an exclusive interview to the FMT (freemalaysiatoday.com). According to the expert, the criminal gangs stole more than $1.2 million from ATMs of at least 17 bank branches belonging to United Overseas Bank, Affin Bank, Al Rajhi Bank and Bank of Islam. The closed-circuit television (CCTV) footage from the banks showed that 2-3 Latin American men entered and withdrew money from these targeted ATM machines.
"What you need is a mastermind, a RM100 computer chip and possibly a bank 'insider' to execute the attacks," he said.
This theft represents an element of concern for the banking industry that, according to the expert, is losing ground in the fight against cybercrime.
"Banks should look into their security seriously, and not just for the sake of compliance … This mentality has to be changed to build security in the DNA of the bank."
The investigator explained to the journalist that similar attacks could be organized just by knowing the architecture of the targeted ATM and don't require specific knowledge.
"He (the hacker) will know where the locks and connections are, the model of the machine, the level of security and the version of the operating system," explained the expert.
The expert also pointed out the roles of the guys captured by the surveillance cameras at the bank
"The guys caught on the CCTV are not the actual criminals … It's like the 'monkey see, monkey do' situation. They can be shown what is supposed to be done without the need for any technical knowledge. They probably do not even know what they are doing."
Compromising an ATM machine could be very easy using malware, and malicious code could be easily acquired on the underground market for a few thousand dollars. A security expert has no problem to wreak havoc on the actual banking system.
"It is a simple attack as there are many free malware available online. And it is definitely something that the bank has to seriously think about."
The expert highlighted the wrong approach of the banking industry in the protection of ATM machines. In many cases, ATMs run an outdated operating system, lack patch management, or they are poorly configured. According to the expert who ran several penetration test sessions and vulnerability assessments, the bank systems are in many cases vulnerable to external attack, and the attacks allowed the investigators to breach the banking systems.
"The bank I worked for was not happy that we breached the system after doing a hacking" he said. "It's either they wanted to ensure that we couldn't find anything, or, they will hire incompetent people who will not find anything."
"Banks have been taking things for granted because nothing like this has ever happened before," the expert added. "They depended heavily on the CCTV, and in some locations, they do not even have security guards."
The experts also claimed the lack of use of encryption technology emerged during the tests. The attacks could expose sensitive data to tampering advantaging the hack of these machines with a malware based attack.
"It is also because of the lack of encryption technology such as the Public Key Infrastructure (PKI) … If the PKI was implemented, it wouldn't have happened," he added.
Conclusion – How to protect the ATMs
The banking industry is working to improve security of modern ATMs to respond to the numerous cyber-attacks experts are observing. The new automated teller machines have enhanced security features such as hard-drive encryption enabled by default, which can prevent malware installations.
However, older ATMs still deployed worldwide are running on Windows XP and in many cases vulnerable to external cyber-attacks, and the problem is particularly challenging for those machines deployed in all sorts of remote locations. Another difficulty that needs to be addressed is the physical security of the computer inside the ATMs. While the ATM's money is locked inside a safe, the computer generally is not. Without adequate physical security for these older ATMs, the attacker has the upper hand.
Below is a list of mitigation measures that could be adopted to improve security of ATMs:
- Upgrade ATMs to a supported operating system (e.g. Windows 7 or newer versions).
- Use full disk encryption to help prevent disk tampering.
- Provide adequate physical protection.
- Install an efficient CCTV monitoring system to protect the ATMs and be sure that security alarms work. Be sure that the cameras are visible, which could work as a deterrent.
- Periodically review the state of physical and logical security status of the installed ATMs. Experts at Kaspersky Lab revealed that cyber criminals behind Tyupkin infected only those ATMs that had no security alarm installed.
- Regularly check the ATM for signs of manumissions (e.g. Deployment of skimmers).
- Change default upper pool lock and keys in all ATMs. Avoid using default master keys provided by the manufacturer.
- Lockdown the BIOS to prevent booting from unauthorized mobile media (e.g. CD ROMs or USB sticks).
- Install a system lockdown solution.
- The ATM should be securely fixed to the floor with an anti-lasso device.
- Be aware of possible social engineering attacks by criminals who try to collect information on the installed ATMs by pretending to be inspectors.
Let us close the post with the illustrious point of view of Sanjay Virmani, Director of the INTERPOL Digital Crime Centre, which is sure that criminals will explore new technologies to steal money from banking systems.
"Offenders are constantly identifying new ways to evolve their methodologies to commit crimes, and it is essential that we keep law enforcement in our member countries involved and informed about current trends and modus operandi," said Sanjay Virmani, Director of the INTERPOL Digital Crime Centre.
References
http://securityaffairs.co/wordpress/28920/cyber-crime/atm-hacking-rm100.html
http://securityaffairs.co/wordpress/28993/cyber-crime/tyupkin-malware-steal-atms.html
http://securityaffairs.co/wordpress/29094/cyber-crime/leaked-manual-behind-atms-malware.html
http://securityaffairs.co/wordpress/20844/cyber-crime/atms-infected-usb-malware.html
http://securityaffairs.co/wordpress/25616/hacking/2-14-year-old-hacked-atm.html
http://blogs.intralinks.com/collaborista/2014/10/cybercriminals-can-steal-money-malware-infected-atms/
https://securelist.com/blog/research/66988/tyupkin-manipulating-atm-machines-with-malware/
http://securityaffairs.co/wordpress/23421/cyber-crime/rob-atms-couple-sms-messages.html
http://securityaffairs.co/wordpress/25616/hacking/2-14-year-old-hacked-atm.html
http://www.businessweek.com/articles/2014-05-08/hackers-can-steal-atm-users-pins-wirelessly
http://www.symantec.com/connect/blogs/texting-atms-cash-shows-cybercriminals-increasing
http://securityaffairs.co/wordpress/28920/cyber-crime/atm-hacking-rm100.html
http://securityaffairs.co/wordpress/20844/cyber-crime/atms-infected-usb-malware.html
http://www.symantec.com/security_response/writeup.jsp?docid=2014-051213-0525-99&tabid=2
http://www.freemalaysiatoday.com/category/nation/2014/10/02/atm-hacking-made-easy-with-rm100/
http://www.symantec.com/security_response/writeup.jsp?docid=2013-102523-2331-99
http://www.freemalaysiatoday.com/category/nation/2014/10/02/atm-hacking-made-easy-with-rm100/

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
http://www.link.co.uk/AboutLINK/site-owners/Pages/Security-for-ATMs.aspx