How to hack a phone charger
Introduction
We live in an era where malware is targeting smartphones and other devices from the Internet of the Things (IoT) world. This is not a desirable situation, but unfortunately, it happens more frequently and in a destructive way.
Of course, criminals look for other ways to exploit attacks, choosing different pathways and landscapes. Most recently, this is focused on chargers which can attack a smartphone until it melts or burns.
Intro to x86 Disassembly
Introduction to the “bad power” attack
Security researchers were recently able to compromise a great variety of chargers with malicious code to deliver more voltage than the connected device could handle. With this approach in place, the overload caused the components inside the affected electronics to spark, sizzle and melt.
The attack is known as bad power. It works by altering the default parameters in the fast charger firmware.
Figure 1: Common fast chargers potentially vulnerable to this attack.
Let’s understand a little bit how fast chargers work. It may look like a regular charger, but they are built with special firmware. The charger firmware can speak with the connected device in order to establish a charging speed based on the device’s capabilities — remember that each device has its features and power speed.
In this sense, if the target device doesn’t support a fast charging feature, the fast charger delivers the standard power — 5V. On the other hand, if it accepts bigger inputs of charging, the charger can use 12V, 20V or even faster charging speeds. This is the crucial point where the bad power attack can be exploited.
Coming to the stage, the bad power attack corrupts the charger firmware. The exploit changes the default charging parameters in the firmware and tampers with it to push a higher voltage than the charging device can handle. This abnormal behavior damages and degrades the receiving device’s components — leading it, in dramatic scenarios, to completely burn.
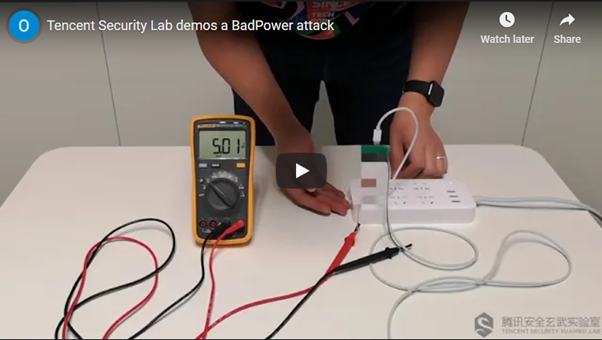
The following video is a proof of concept from Tencent Security Lab in order to demonstrate the bad power attack.
See the full video here.
Bad power attack by numbers
The Tencent research team tested the bad power attack on 35 fast chargers from 234 models available on the market. According to the article, 18 models from 8 different vendors were vulnerable to this flaw.
The worst scenario happens in some chargers of specific vendors. The bad power vulnerability can be fixed in common chargers by updated the device’s firmware, but researchers said that 18 chip vendors were not built with a firmware updated option. In this case, there is no way to fix the vulnerability in those devices.
From this perspective, this flaw is considered a critical problem and without a fast and efficient solution. Many people have three or four chargers in their homes and they are probably vulnerable now.
Be careful with your device
One of the particularities of this attack is that anyone can make it deadly and silently. It’s a single simple step to destroy any device: connect it to the right fast charger. In the worst-case scenario, the attack can damage the device in a few seconds.
Figure 2: Device damaged when connected to the “malicious” fast charger.
According to the researchers, “with some fast chargers, the attackers don’t even need hardware. They can load the attack code to modify the firmware on the target smartphone or laptop. When a victim connects their infected smartphone or laptop to a fast charger, the device could go up in flames”.
Learn Python for Pentesting
Final thoughts
The exploitation of physical and hardware flaws should be taken into account as a common and serious problem these days. Although bad power can be a beast if the target device is connected to the right charger, the damage caused by this attack would vary, depending on the fast charger model and on the mobile device and protection against malicious code.
The researchers didn’t share the name of the vulnerable products, but the specific vendors were contacted. China’s National Vulnerability Database was also contacted about the potential problem.
In order to mitigate and reduce the risks of this attack, it’s suggested that manufacturers add additional fuses to devices that support lower-voltage fast charging. Another suggestion is to include hardening firmware to prevent unauthorized modifications, also deploying overload protection to charged devices.
For users, they need to be warned about the problems of using third-party chargers or power banks — for example, in cyber-spaces, airport, shopping and so on.
Sources
BadPower Vulnerability In Fast Chargers Might Make Phones Halt And Catch Fire, Hackaday