Phishing Attacks on the Retail Industry
Phishing Attacks in the Retail Industry
Phishing Targets by Industry:
- Financial Phishing
- Government and Military Phishing
- Healthcare Phishing
- Retail Phishing
- Phishing Individuals
What is the Origin of Phishing and Retail?
The 1995 surge in popularity of the Internet service provider America Online (AOL) changed so much about how we live, work, communicate, and do business—and how criminals operate against us, as well.

Get your free course catalog
AOL brought paying consumers, and, significantly, their financial information, to the Web as never before. It’s no surprise, then, that the outlaw practice known as “phishing”—that is, directly obtaining protected data from users through fraudulent offers, claims, and other misrepresentations—is largely traced back to a mid-’90s hacking device known as AOHell, which specifically targeted AOL customers.
The Internet has evolved immeasurably past those early AOL days, of course. So, too, have the opportunities for individuals and companies alike to buy and sell online. Unfortunately, phishing has kept pace with our changing times and technologies. Nowhere is that more evident than in the history of such attacks against the retail industry.
How Did Phishers Dupe Retail Victims Early On?
In recent years, commercial giants such as Amazon, Costco, Home Depot, Target, Toys-R-Us, Walgreens, Walmart, and China’s mammoth online shopping outpost Alibaba have fallen prey to phishing onslaughts. Fortunately, Chicago’s InfoSec Institute and other combatants against such criminality have been able to outpace the outlaws, time and again. Still, phishing attacks on retailers pose an ongoing challenge in keeping with the practice’s tremendously compelling back story.
Throughout the second half of the 1990s, phishers focused largely on small-scale acquisitions. They’d send out phony emails or Instant Messenger communications and reap what they could from duped victims, often using bots to multiply the size and scale of their nefarious operations.
Why Did Phishers Escalate from Individuals to Whole Businesses?
With the early 21st-century boom of sites such as eBay and PayPal, phishing took to targeting businesses' online transaction systems. Buyers and sellers among the public grew accustomed to utilizing the Internet as just another series of stores, boasted by unprecedented speed, efficiency, and convenience. Alas, these advantages came loaded with unprecedented dangers, as well.
The very success of retailers using Internet and online credit card technology is what makes them such ripe prizes for phishers. After all, when a consumer orders items regularly from Amazon or has successfully purchased clothing from Old Navy or groceries from Peapod online, he simply comes to trust the overall practice.
How Has Phishing Adapted to a Growing Cashless Economy?
That same risky consumer trust holds true as the transactional economy moves away from cash even in physical locations, with credit and debit cards quickly becoming the norm. Again, as data thefts are relatively rare compared to how frequently a consumer pays with plastic, an inherent sense of “this is just how things work” takes hold.
In addition, the more we shop online, the more we get used to regularly receiving email messages from retailers. As a result, it’s easy to see the name of an outlet you’ve frequented or from where you’re even anticipating a delivery and to not think twice about clicking on a message with a subject like “Order Status” or “Important updates to your account.”
Phishers, of course, count on exactly that mindset, dating back to the ascension of online commerce nearly two decades ago. One crucial difference now is that, in times past, a phishing message might grant a crook access to just your personal information, whereas today, phishers have been able to penetrate retailers using the email accounts of employees and even customers.
What Are Phishing’s Most Effective Tools and Techniques?
One early case in point: An attempted June 2001 phishing raid on the digital currency site E-Gold incorporated used intentionally confusing domain names, email worms, “spoofed” messages, and malware on a newly extensive scale. This incident failed to cause as much damage as was intended, but it established the basics of how phishers would operate going forward and still do, in large part, today. The aforementioned online juggernauts eBay and PayPal, in particular, were forced to fight off attacks of this sort regularly by 2004.
For nearly a decade, phishing posed a serious problem for retailers large and small. Costs and complications inflated exponentially as attackers ramped up to take on “big box” entities such as Best Buy, Meijer, OfficeMax, and PetSmart.
How Large-Scale Was the 2008 Heartland Payment Systems Phishing Crisis?
The first phishing assault to be perceived as one of crisis proportions occurred in 2008. That’s when cybercrooks breached Heartland Payment Systems, a Princeton, New Jersey-based payment processor and tech provider, and stole the credit and debit card information of up to 130 million individual accounts.
As massive as that haul proved to be, it only inspired phishers to aim higher—specifically in the direction of multinational big box retailers, where the volume of customers’ financial information—potentially available from both online shopping systems and in-store credit card readers—could easily dwarf what was hauled off from Heartland Payment Systems.
What Happened with the Massive 2013-14 Target Corp Phishing Breach?
That road led to the most (in)famous phishing attack to date: the late-2013 data raid against Target Corporation, wherein 110 million customers of the company’s physical retail outlets fell victim to financial information theft, just in time for the mammoth holiday shopping season.
The Target scam went undetected for two disastrous weeks, and eventually proved to be so vast that it was estimated that up to 50% of all United States shoppers might have had their financial data compromised in the process. The staggering financial cost to Target is reported to have run as high as $1 billion.
How Did Target Get Phished?
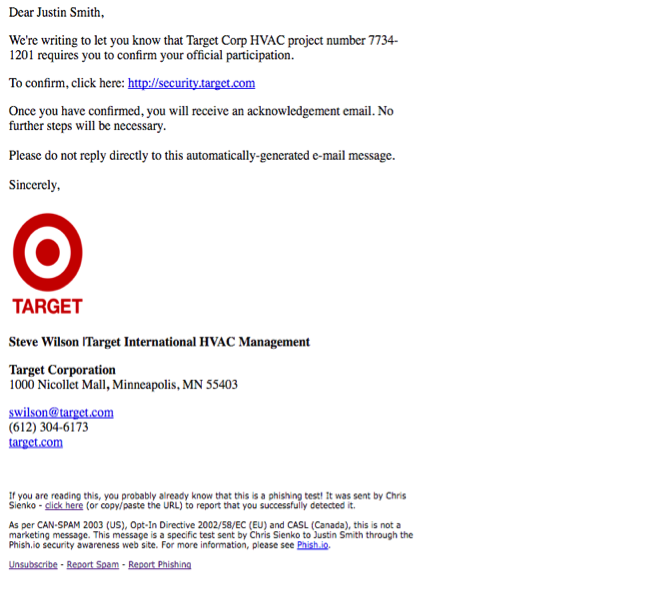
That historic Target phishing breach was masterminded by a cybercriminal operating out of the Ukraine. Reports indicate that the scammer first used a simple email to infiltrate Fazio Mechanical Services, a third-party contractor that worked on heating, ventilation, and air-conditioning (HVAC) systems at numerous Target locations.
Research suggests that a Fazio Mechanical Services employee got duped into clicking on a bogus email message that appeared, very much, to have come from a trusted source. This specific technique has come to be known as “spear-phishing,” and this basic ruse is believed to have set off the most famous retail data compromise to date.
How Was One Phishing Email Able to Set Up the Target Breach?
Using a typically sophisticated and intricate spear-phishing email, the message that fooled the Fazio Mechanical Services may have come from an account marked “Target International” or some other very close variation, with the victim’s own supervisor’s name listed as the sender, and a subject line directly addressing a project he was working on. Spear-phishers are frighteningly accurate when employing such familiar details.
[cta id="1470255016597" post="35467"]
After gaining access to Fazio Mechanical’s system, the attacker is theorized to have used Target’s online portal for contractors. The thief is then thought to have compromised a Windows file server and used it to track down and violate the stores’ point-of-sales (POS) systems, installing a Trojan program that acquired clear-text copies of credit card magnetic stripe data. The data was then transported back to the compromised Windows server, where it was exfiltrated to multiple FTP servers regularly over the course of the two-week breach.
What Did Phishers Do After the Target Attack?
While the Target disaster made headlines worldwide, it only seemed to further inflame phishers to try even harder. Retail phishing scams increased from 2014 to 2015, with the FBI reporting at year’s end an alarming 270% rise in losses connected to business email compromise (BEC) situations with dollar figures well into the billions. In basic terms, that’s the cost of getting phished.
All this operational chaos and financial wreckage can arise—and has, in the case of Target, arisen—from a simple phishing setup. Of course, the information extraction, once an attacker gets into a system, grows ever more complex, but so, too, does the back-end defense against such malignant maneuvers.
How Vulnerable Are You to Phishing?
It’s been said that, as of right now, there are only retailers who have been the victims of phishing—and those that don’t yet know they’ve been the victims of phishing. That observation stresses the crucial importance of online defense operations on the high order of InfoSec Institute.
The cutting-edge level of information security research, technology, and techniques developed and taught by InfoSec Institute surges ahead at the forefront of what’s possible in the realms of keeping your company and your customers safe not only from phishing attacks, but from all manner of potential breaches. Be it in the form of small-time Trojan viruses or global-scaled spear-phishing, InfoSec Institute provides an ever-growing stronghold against high-tech criminals.
How Can You Protect Yourself from Phishing?
Get smart and get safe. Learn how to defend yourself and your business from phishers and other information thieves. It’s just as crucial to empower your associates and employees with the same knowledge and techniques.
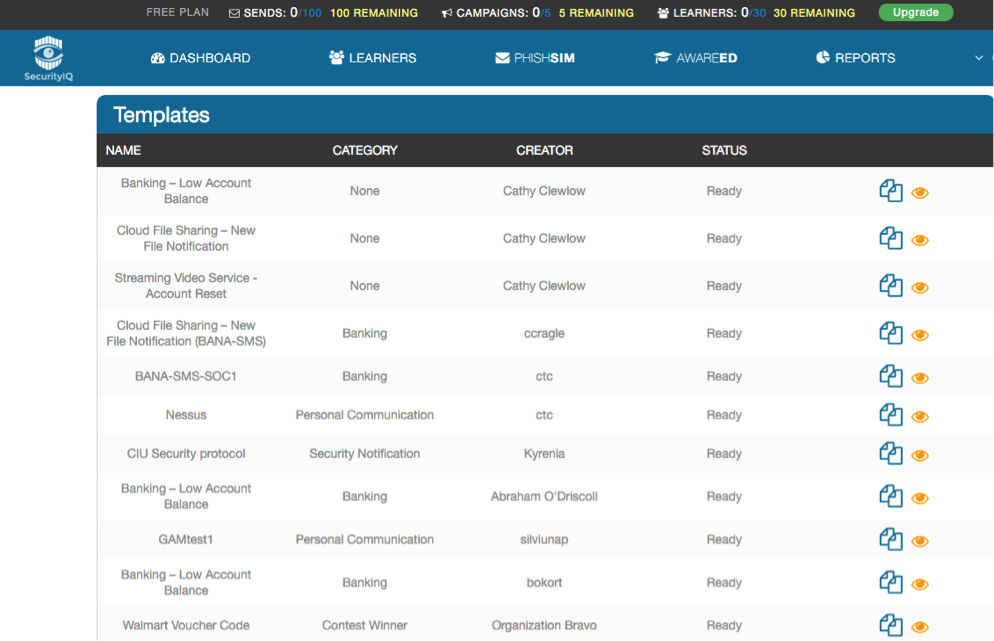
After 15 award-winning years on the cutting edge of information defense, InfoSec’s SecurityIQ provides an all-encompassing system for protecting yourself, your family, and your livelihood from phishing breaches and all other related violations.
What Is SecurityIQ?
InfoSec Institute’s SecurityIQ program has successfully trained both individuals and numerous Fortune 50 companies in information security, along with large-scale government agencies, including a vast array of military entities.
SecurityIQ provides on-site corporate, military, and security training in the form of 20-hour course customization work by a highly experienced, certified senior instructor. Multiple awards and confirmed testimonials for leaders in industry, government, and military alike attest to the power of the program.
What Makes SecurityIQ So Effective?
InfoSec Institute’s security awareness training program directly, and in great detail, addresses the information protection and compliance requirements of finance, retail, manufacturing, logistics, and consulting corporations, US civilian departments and agencies, state and local governments, and educational institutions.
Utilizing the most personable, experienced, and thoroughly qualified instructors, InfoSec’s security awareness training program employs a series of short lectures followed by realistic, hands-on exercises has been proven to enhance learner retention to engage clients in completion and interest in the program—and, more important, to implement what they learn going forward.
Core learning modules include lessons and exercises on phishing, malware, password security, and safe browsing, while optional modules address FISMA, Sarbanes-Oxley, and many more topics.
SecurityIQ can be particularly effective for any organization seeking to meet the formal security awareness program requirements of payment card industry data security standards (PCI-DSS). Completing such a program is mandatory for retailers to do business using payment card technology, and SecurityIQ excels in every aspect of such instruction and implementation.
As culture and technology has grown, SecurityIQ has expanded and evolved along with it. The safety and security of the program’s users provide all the proof of its effectiveness, as well as the InfoSec Institute’s commitment to keeping ahead of phishers and other bad guys.
As an exclusive offer to readers of this article, you can sign up for SecurityIQ and check out the PhishSim templates page to utilize a free email template in the style of the Target management email that fooled the HVAC employee. Just look for the template titled “Target Security protocol for HVAC employees.”

Learn Python for Pentesting