Phishing techniques: Contest winner scam
Introduction: Phishing is evolving via bogus online ads and webmail
Phishing scams are among the most serious and pervasive frauds operating today. One of the most used tactics is a scheme that has been around for years now: the “contest winner” fraud.
In this article, I will provide details of these scams. Contest winner scams have been adopted by phishers all over the world and can truly pose a threat if users aren’t cautious.

Learn Vulnerability Assessments
Strategies used in this phishing attack
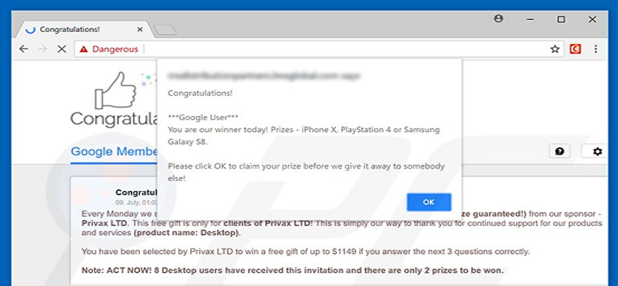
How this phishing attack unfolds: A user is browsing around the internet looking for information and lands on a legitimate site. Suddenly a pop-up appears saying something like “Congratulations User …” or “You are the chosen …” or “You are the winner of our Promotional Contest”. Many people are wise to this scam, but many more are tempted to click on the banner or pop-up.
Most of the time, good sense prevails and the user realizes this is nothing but the usual online scam, knowing that legitimate ad networks do not operate in this way. However, a less-savvy user or a child might not recognize the danger until it is too late. Those who take the bait and click on the pop-up are usually redirected to fraudulent websites and become victims of scripts that take over the user’s system and possibly download malware.
The phishing attempt can also come in the shape of mass emails. This email might, for example, link to an online form asking for sensitive information; the email seems genuine but is connected to a spoof website.
Figure 1. "Congratulations You Are Todays Winner” Source: PCrisk.com
The “Congratulations You Are Today’s Winner” message that is so tempting for the user is part of what is also known as the “todayswinner.club phishing scam.” It’s the perfect way for phishers to lure users into their net. The attacker can then take over the victim’s system with potentially unwanted applications (PUAs) and/or elicit information about them.
Scammers have the tendency to ask for a physical mailing address in delivering the prize, in addition to payment details (for alleged shipping costs) and may even request a person’s Social Security Number. This makes the alleged winner think the collected data is needed to prove their identity. Or they may be asked to create an account, providing an opportunity for the phisher to reel in their victim.
Another line of attack comes from web users’ habit of using the same password for multiple accounts, enabling any savvy phisher to gain access by automated guessing. Those who become the victim of a hacked account can be certain their information can be gathered easily online. For the unaware user, it’s a short leap from the happiness of being a lucky winner to the desperation of losing money or being the victim of identity theft.
How can users defend themselves?
"You Are Our Winner Today!" Sounds tempting to click, right? Not if you’re aware that these schemes are common and part of the daily life of internet surfers.
How do you defend yourself? On the technical side, much can be done by activating basic defenses that are present in every web browser — from pop-ups and banner blockers to malware and scripts stoppers.
The first and most important approach is to think before you click. Rather than falling prey of the enthusiasm of being today’s sweepstake winner and dreaming of the new iPhone they just became owners of, for example, users will need to remember that "if it seems too good to be true, it probably is."
First of all, if they don’t remember entering a contest, they are probably not a winner. Secondly, if a legitimate website does have a contest or a daily recognition program, it will be highly unlikely that they will advertise through a pop-up and would have definitely asked the user whether he or she opted into the contest.
Another red flag is the immediate request for personal information in order to collect the winnings from a sweepstakes, and the pressure to claim a prize before it’s offered to someone else.
Beware of entities asking for money in relation to a win. “Here’s one way to think about it: if you have to pay, it’s not a prize,” the Federal Trade Commission (FTC) says. At best, the scammer will take the money and fail to deliver the promised prize; in the worst-case scenario, credit card info and bank accounts could be compromised.
Consider running anti-phishing utilities for countermeasures. This ultimately helps to identify suspicious websites and either blocks them altogether or alerts the user to exercise caution. Major web browsers have their own type of phishing filters already in place, but other security software and hardware can help.
Awareness, however, is always the best line of defense when users and their actions are the target. In a company, implementing a phishing training program is ideal. For this undertaking, you can use a phishing simulator that assesses staff’s ability to identify and mitigate phishing, while doing so points out possible areas of improvement and helps to assess someone’s training needs.
What if you do fall victim to a scam?
If you do fall victim of this type of scam, make sure to report it. One way is to contact the FTC: you can file a complaint online or opt to send complaints to Fraud.org (which are also transmitted to the FTC). Specific information is also available at www.consumer.gov/idtheft or 1-877-ID-THEFT. Visit IdentityTheft.gov to find specific information on how to handle a compromised bank account number, Social Security Number, credit card information and so on.
You might also want to consider contacting national credit bureaus to request fraud alerts and credit freezes, so as to have it available if any of your accounts (especially financial accounts) is compromised or fraudulently used. This ensures that no new accounts can be opened in your name or any of your existing accounts be changed without you being contacted first.
If you believe your mailing address could have been compromised, then it is also a good idea to ensure the postal service has not received any recent address change requests.
There are a number of actions you can take also on your computer or mobile device. Immediately run security checks through security software. If it is a PC, you might want to consider a full format of the hard drive; on a mobile device, you can determine whether an antivirus, anti-spyware or anti-malware should be installed. Also make sure to change the access credentials to the most important accounts you have (bank, e-mails, Apple ID and so on).
Conclusion
Any correspondence that indicates "You have won!" is, for the most part, a scam. This is especially true if found in web-based email or a webpage. So if you have any doubts that the win could actually be a fraud, make sure not to respond.
It's always best to be cautious. Contact the supposed sender directly, requesting further information. The names of legitimate businesses are often fraudulently used, so contacting the company or vendor directly using trusted methods of a given phone number or website could spare yourself and potentially others from being victimized by those impersonating as a trustworthy third party. This will also alert those genuine companies of the possible harm to their online reputation.
Avoid online scams in the form of display ads, pop-up ads and emails. Most importantly, DO NOT provide any of your personal details in response to these messages. Otherwise, you may end up paying far more than the contest is worth, if you get a prize at all.

Intro to x86 Disassembly
Sources
- Congratulations You Are Todays Winner Phishing Scam, PCrisk.com
- How to Recognize and Avoid Phishing Scams, FTC.gov
- How to Avoid Phishing Scams When Entering Sweepstakes, The Balance Everyday
- 12 Warning Signs of Sweepstakes Scams, The Balance Everyday
- Sweepstakes Fraud Prevention, PrizeGrab.com
- Prizes and sweepstakes scams, Fraud.org
- Prize Scams, FTC.gov