Abusing email rules
Introduction
For the average email user, setting up rules like automatic email forwarding is a harmless exercise. But for the individual whose role it is to prevent security breaches and achieve compliance, email rules and forms can turn into a nightmare situation in seconds.
Hackers can break into a person’s email client and create rules to forward incoming emails to their server, delete certain messages (such as legitimate warnings) and even format the victim’s hard drive to cover up any evidence if needed. Any rich email client (such as Outlook and Mozilla Thunderbird) allowing users to set up rules can be abused to perform malicious actions.

Learn Python for Pentesting
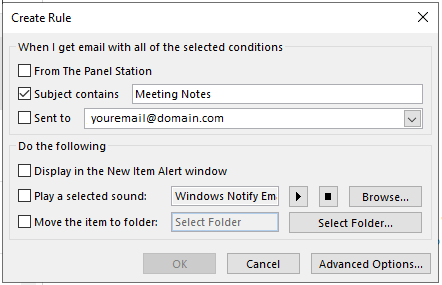
With Outlook, for instance, you can instruct the client to display an item alert, play a sound or move an item to a specific folder if the email subject line contains a certain set of keywords.
What’s eye-opening about these rogue email rules is that the data lives on the email client’s server. This means potential targets cannot prevent hackers from executing malicious programs by simply changing computers, updating their passwords or erasing their hard disk. Unless they check the email client, the rules will live through all types of software updates and bug fixes.
Examples of email rule attacks
One of the most recent cases of an email rule attack was uncovered by the co-founder and chief visionary of TRIBU & CROFTi.
One of CROFTi’s clients asked the company for assistance in getting to the root of suspicious wire transfers. They were almost about to lose a million dollars, and only realized that they’d been scammed at the last minute. Fortunately, they were able to get in touch with their bank and cancel the transfer.
CROFTi launched an investigation on their behalf and found that some of the company staff’s Office365 accounts had recently been compromised. Cybercriminals gained access to these accounts and created rules for all incoming emails to be forwarded to their own Gmail accounts. The forwarded messages were then deleted on the original email accounts, leaving the victims unaware of the attack.
The hackers only needed to monitor the emails to find out when any funds were going to be transferred. Needless to say, they jumped at the opportunity when they found out about a million-dollar investment that was going to take place. They set up a new rule to target any emails regarding the wire transfer and, again, deleted all the original evidence.
They went on to forge responses that seemed legit and ultimately put in a last-minute request for the banking details to be changed. Though this seemed out of place, the client still proceeded to make the transfer.
Even though there was no financial damage, the client still suffered a loss due to the following reasons:
- They had to hire experts to identify where the threat came from and how to stop future attacks
- The company experienced downtime as employees helped with the investigation
- Their reputation was damaged when customers became aware that their information had been compromised
Another instance of an email rule attack was reported by Motherboard. The source revealed that the email metadata of Outlook users was compromised in a bid to steal their cryptocurrency.
One Microsoft user named Jevon Ritmeester revealed that the hackers gained access to his inbox, which enabled them to reset his Karken.com password and withdraw his bitcoin. The victim also provided Motherboard with a screenshot of an email forwarding rule the adversaries set up.
The rule instructed the email client to forward any email containing the name “Kraken” to a Gmail address owned by the hackers. This would include messages such as bitcoin withdrawal requests and password resets. Ritmeester only came to know someone had asked for both of these things after checking the trash folder of his Outlook account. He lost 1 bitcoin as a result of this breach.
Both of these examples indicate how damaging malicious email rules can be. Anti-malware and log alert systems don’t check for them, which makes it easier for hackers to stay hidden and capitalize on incoming/outgoing emails.
How to protect yourself from rogue emails
The best protection measures are knowledge and awareness. If your email client is acting weird, manually examine the email rules to ensure you don’t have any unexpected modifications or add-ins. Check the rule description for suspicious actions that launch an application or refer to a .ZIP or .EXE file. You can also leverage Microsoft’s script that will help you identify the various rules for specific email clients.
If you’re using an event monitoring system, see if the vendor has any plans to release a feature that helps detect what events are created when a new email client is used. If yes, the system should be able to notify users about events that include potential threats.
Conclusion
There’s no silver bullet solution for identifying malicious rules, but with a little knowledge and frequent checks, email users can help ensure incoming/outgoing emails are functioning like they’re supposed to be. If, at any point, you detect a suspicious rule, report it to the email client’s support team and reach out to important contacts alerting them of malicious messages that may have been delivered from your account.

Learn Vulnerability Assessments