ADMX: 1.0.1: VulnHub CTF Walkthrough
This capture the flag (CTF) is easy to medium, and it is built for OSCP aspirants. The target of this CTF is to get to the root of the machine and read flags. Download the CTF here:
https://download.vulnhub.com/admx/AdmX_new.7z
You can download the machine and run it on VirtualBox.
Please note: for all these machines, I have used Oracle VirtualBox to run the downloaded machine. I am using Kali Linux as an attacker machine for solving this CTF. The techniques used are solely for educational purposes, and I am not responsible if the listed techniques are used against any other targets.
Steps
The summary of the steps required in solving this CTF is given below:
- Getting the IP address with the Netdiscover utility
- Port scanning through Nmap
- Enumerating web application
So, now we have all the information that we need. Let us get started with the challenge.

Learn Container Security
The walkthrough
Step 1
The first step is to run the Netdiscover command to identify the target machine's IP address. In the screenshot given below, we can see that we have run the Netdiscover command, giving us the list of all the available IP addresses. [CLICK IMAGES TO ENLARGE]
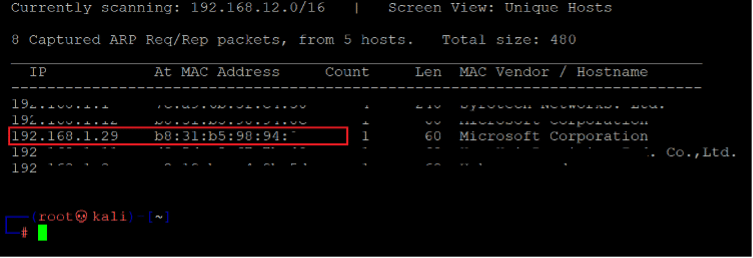
Command Used: << netdiscover >>
In the above screenshot, we have identified the IP address of all the devices connected to our router. Still, due to security reasons, we have hidden the MAC address of my personal connected devices. Our target machine IP address that we will be working on throughout this challenge is 192.168.1.29 (the target machine IP address). We will be using 192.168.1.28 as the attacker’s IP address.
Note: The target machine IP address may differ in your case, as the network DHCP is assigning it.
Step 2
The second step is to run a port scan to identify the open ports and services on the target machine. We will use the “Nmap” tool for port scanning as it works accurately and is available on Kali Linux by default.
In the highlighted area of the following screenshot, we can see the Nmap command, which we used to scan the ports on our target machine. The identified open ports can also be seen in the screenshot given below.
Command Used: << namp 192.168.1.29 -p- -sV >>
The output of the Nmap shows that only one open port has been identified Open. Here, we used the ‘-sV’ option for version enumeration and ‘-p-‘ for full port scan, which means we are telling Nmap to conduct the scan in all 65535 ports. By default, Nmap performs the scan only known 1024 ports. So, it is crucial to complete the full port scan during the Pentest or solving the CTF. However, in our case, we have found only one port in which is running the HTTP service.
Step 3
Let us start the CTF by exploring the HTTP port. We opened the target machine IP address on the browser.
As can be seen in the above screenshot, the Ubuntu default page is visible on the browser. In this case, where we do not know anything about our target, the best idea is to run a Dirb scanner to identify hidden directories.
Command Used: << http://192.168.1.29/ >>
The output of the Dirb shows a large output on the terminal, where we can see the identified files and directories. We closely analyzed it and identified two directories tools and WordPress. So, let's open these directories one by one.
First, we open the WordPress directory into the browser, which can be seen in the following screenshot.
The output shows that the WordPress website is running. As we know, WordPress is one of the most popular content management systems (CMS) for developing websites and the most vulnerable if not updated regularly. So, we ran a WordPress vulnerability scanner on this website. The command and output can be seen in the following screenshot.
Command Used: << wpscan --url http://192.168.1.29/wordpress/ >>
The above screenshot shows that the WordPress scanner has completed, but it does not show any vulnerability that could help exploitation. We also checked other folders which were identified by the Dirb but didn’t get any useful information. In the next step, we will launch the brute force attack on the login page.
Step 4: Launching Brute force with WPScanner
There are multiple ways to do the brute force on the WordPress login page. but we will be using WPScanner as it is simple to run as follows:
Command Used:
<< wpscan --url http://192.168.1.29/wordpress/ --password-attack xmlrpc -U admin -P /usr/share/wordlists/rockyou.txt >>
In the highlighted area of the above screenshot, we can see that WPScanner has identified valid admin login credentials. Now, we can use the Metasploit file upload module to take the reverse shell of this system, which we will be doing in the next step.
Step 5 Getting the Reverse shell with Metasploit
We started the Metasploit by running the msfconsole command on the terminal, which can be seen in the following screenshot.
Command Used: << msfconsole >>
The Metasploit has started with a friendly CLI interface, and it also gives knowledge about the available exploits and other modules. So, let’s search the wp_admin_shell_upload module in the Metasploit framework. It can be seen in the below screenshot.
Command Used: << search wp_admin_shell_upload >>
The output of the search command shows an exploit name with the path details. We know the exploit name, so we used the “use” command to enable this module. After that, we used the “show option” command, which shows all the required parameter details which need to be added in the exploit to run as follows:
Command Used:
- << set RHOSTS 192.168.1.29 >>
- << set USERNAME admin >>
- << set PASSWORD adam14 >>
- << set TARGETURI /wordpress >>
- << show options >>
The command which we used in the above screenshot are explained below:
- We used the set RHOSTS command to set up the target machine IP address. It can be changed in each case depending on the network configuration.
- Set USERNAME is used to configure the username. So, we added admin as a username.
- Set password is used to configure the password. In our case, the password is adam12.
- Set TARGETURI is used to configure the folder name from where the application is running. In our case, the application is running from the WordPress directory.
- After setting up all the required details, we verify it with the show options command, showing all the needed details.
Now, our exploit is ready to run. We run the exploit command, which executed our exploit and gave us the reverse shell connection.
Command Used: << exploit >>
As shown in the above screenshot, we got a Meterpreter shell configured by default by the Metasploit Framework. We tried to run the id command it does not sometimes work. After that, we ran the shell command, which opens another command shell where we run id command. The output of the id command shows that we got the access of www-data user, which is not the root. In the next step, we will try to get root access.
Step 6: getting the root access and reading flag
Until now, we have a limited access shell on the machine. But our target was to get the root access. So, we ran some more commands to enumerate the running operating system and kernel version, which can be seen in the following screenshot.
Command Used:
- << python3 -c ‘import pty;pty.spawn(“/bin/bash”)’ >>
- << uname -a >>
- << cat /etc/issue >>
As can be understood in the above screenshot, first we used the python command, which returns us the stable command shell. Then we used uname -a and /etc/issue command, which provides us the information about the running operating system and the kernel version. We explored the local exploits online for this version but didn’t get any working exploit for it. After spending some time, we noticed local.txt file in the /home/wpadmin, which can be seen in the below screenshot.
Command Used:
- << su wpadmin >>
- << cat local.txt >>
We attempted to access the local.txt file, but we were not able to read the file due to insufficient permission. As we previously know one password, we used that password for the wpadmin user, which works, and we got the access of wpadmin user. Then we used the cat command to read the first flag file.
Therefore, we have user access. However, our objective was to get root access. So, we did some more enumeration and got to know this user can run MySQL command as a root user, which can be seen in the following screenshot.
Command Used: << sudo -l >>
We highlighted the MySQL command in green color. Thus, we ran this command which gives us the MySQL access as follows:
Command Used: << sudo /usr/bin/mysql -u root -D wordpress -p >>
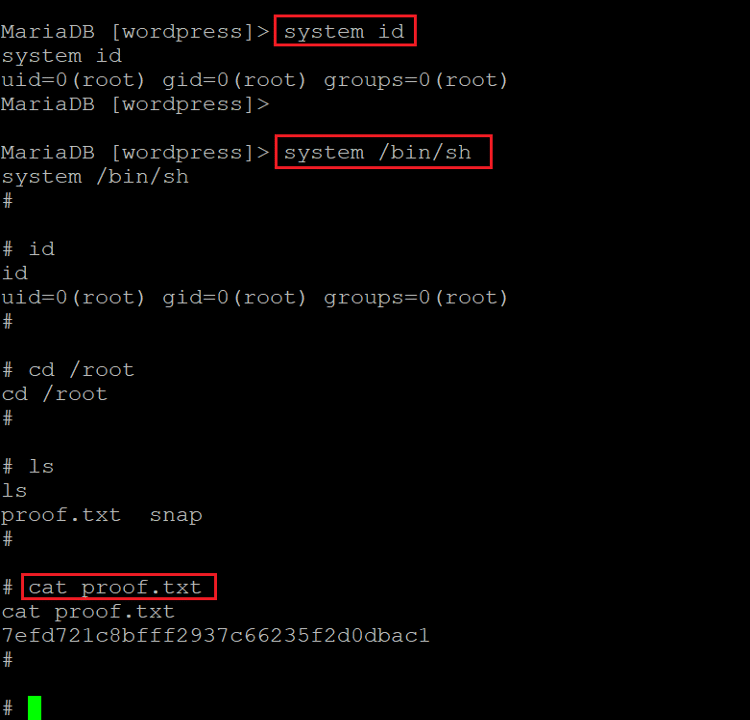
Now the MySQL is running with root. So, if we run any system command so it will be run as the root user. First, we run the id command, confirming that we can run any command as a root user. After that, we /bin/sh command which gives us the root shell as follows:
Command Used:
- << system id >>
- << system /bin/sh >>
- << cat /root/proof.txt >>
Now we have root access to the target machine. Hence, we changed the current directory to the root folder and read the flag file with the cat command.

Learn Threat Modeling
I hope you enjoyed completing this challenge with us. Stay tuned for many more CTF solutions to come.
Sources:
- AdmX, VulnHub https://download.vulnhub.com/admx/AdmX_new.7z
- AdmX, VulnHub https://download.vulnhub.com/admx/AdmX_new.7z.torrent