Sharkfest 2013

The sharkfest challenge was organized by Wireshark University. There are seven challenges related to the trace files analysis. In each challenge, there are some questions we have to answer by analyzing the captured trace files. The sharkfest challenge trace files can be downloaded from the reference links. In this part of the article we will solve the first three challenges, and the other four challenges we will continue in the second part of the article.

Earn your CISSP, guaranteed!
CHALLENGE #1: WHAT THE HECK?
TRACE FILE: challengescan.pcapng
BACKGROUND: This captured file was taken from a very large and well-established network that had been considered very stable and unchanging. The network administrator has given you this file that contains what he considers "suspicious" behavior and has asked you to evaluate it.
QUESTIONS:
1. What is the IP address of the scanning host?
Analysis - We will open the trace file and see what's going on. As can be seen below, the ICMP echo request is coming through 192.168.1.141.
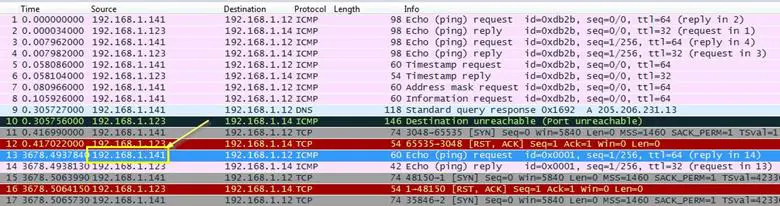
Whenever a network scanner scans its target, it first sends a ping request to the target for checking if the host is alive or not.
Answer: 192.168.1.141
2. What is the IP address of the target host?
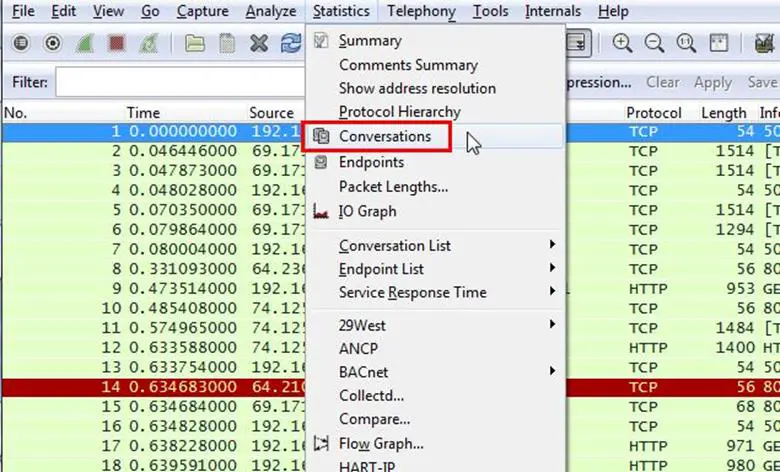
Analysis - So we know the attacker's IP and we have to find the target's IP. In Wireshark, there is a feature to view all networks' communication. We will see first how many IP addresses are in this trace file. So select Statistics >Conversations
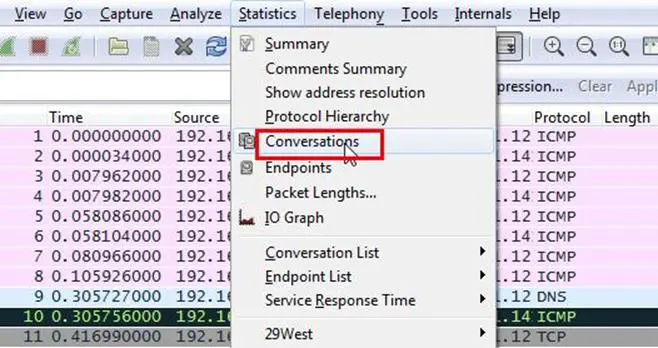
As can be seen below in the IPV4 tab, only one conversation is going on between 192.168.1.123 and 192.168.1.141.
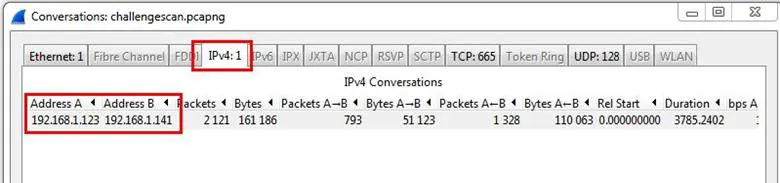
It's pretty much obvious that if the IP address 192.168.1.141 is the attacker's IP, then 192.168.1.123 is the victim.
Answer: 192.168.1.123
3. Which TCP port opens on the target?
Analysis: Now we know the target's address and we have to find the open port on it. So it is asking for TCP port, so first of all we will apply a filter as TCP only to make the task easier. As can be seen below, we can now see the TCP packets only.

Now how we will find the open port of the target? First we need to know how the scanner works and how it detects the open port. The basic understanding is that if a port is open in the network, then it will respond with a SYN/ACK flag. If you get a SYN/ACK for a SYN packet, that most certainly means that the port is open, so we have to find the SYN/ACK flag packet where we can find the source port of the target.
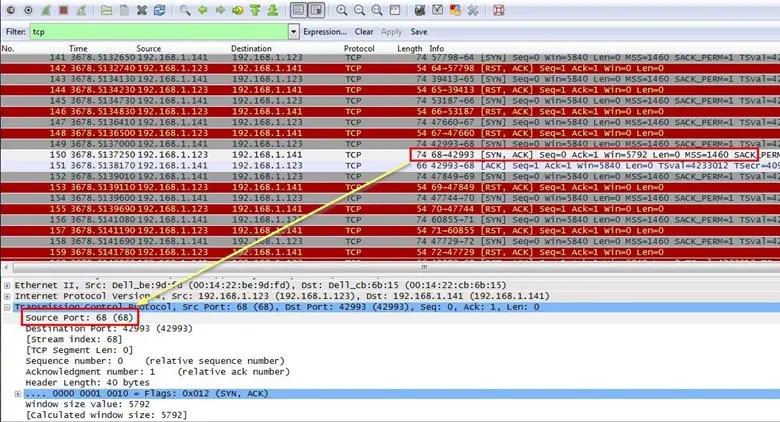
Answer: port 68
4. Which ICMP packets contain non-standard Type/Code numbers?
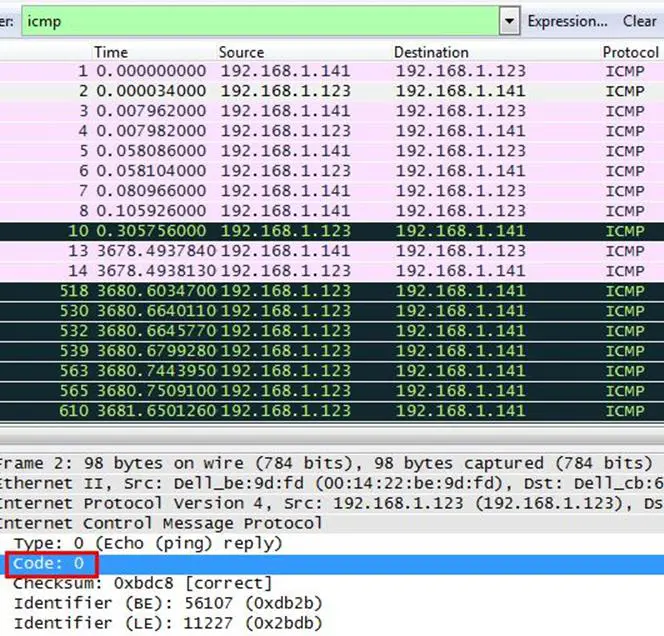
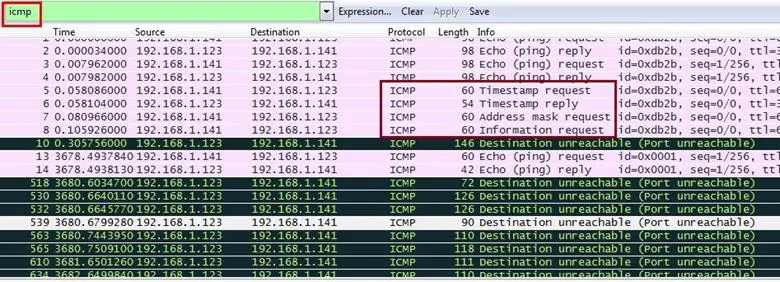
Analysis: First we will apply a filter for ICMP packets. As can be seen below, all ICMP packets are sorted out.
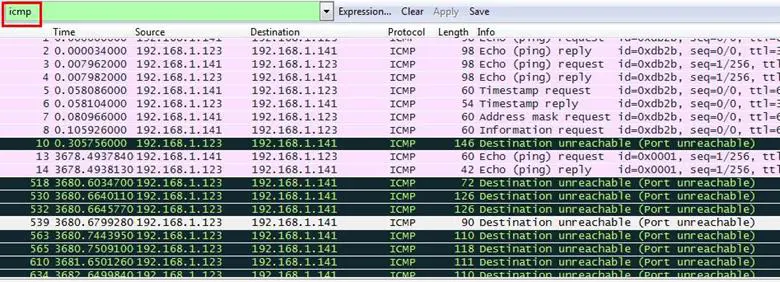
We have to find the non-standard code for ICMP packets. We did a Google search for standard code types for ICMP packets and we got a list of codes here: http://www.nthelp.com/icmp.html and now it easier to find the non-standard one. We selected a random packet and expanded the Internet Control Message Protocol section, and we can see the code value is 0, but this is a standard one according to that list.
By using the same method, we checked each and every packet and we found a code 123 which is not mentioned in the code list. As can be seen below, we applied a filter for code type 123. Right click on the code and Select>Apply As Filter>and selected
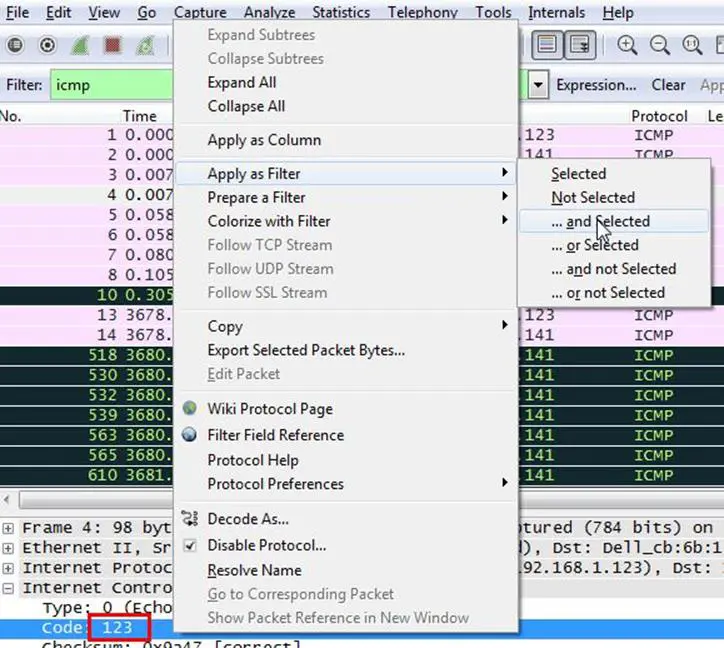
The filter sorted the ICMP packets with code 123, and as can be seen below, there are only four packets which contain code 123.
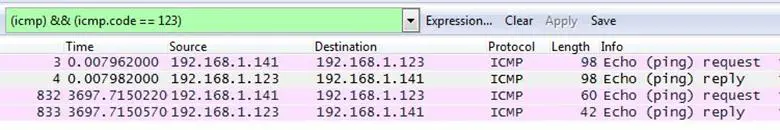
Answer: 123
5. What software is used to scan the target?
Analysis: Now it is not an easy task to figure out which scanner is being used for scanning the host because there are lots of network scanners available. We started to look deeply in the traffic and noticed that there are three common packets going on TCP, ICMP and UDP. As we know, these packets can be used by a scanner so we started to search on Google for all famous scanners like Nmap, Nessus, Amap, UnicornScan, etc. for its scanning signature, and apparently we found a presentation of DefCon on the Xprobe scanner.
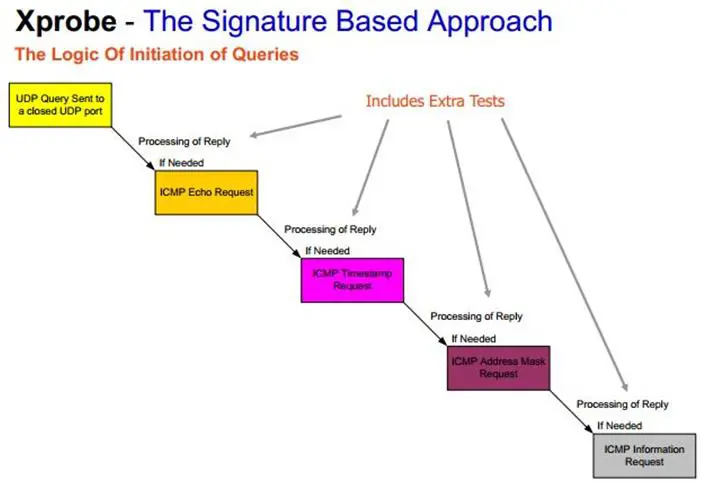
As can be seen in the above diagram, it is an ICMP based scan and the first request is an ICMP echo request; after that it sends the ICMP timestamp request, then it sends the ICMP address mask request, and at last it sends the ICMP information request. The same pattern is also available in the trace file where we applied the filter for ICMP packets.
Answer: Xprobe
CHALLENGE #2: CURSED
TRACE FILE: challengewhatsup.pcapng
BACKGROUND: Sure, Scott is one of the best friends at the company, but he's always asking for computer help. No amount of training seems to work. Today he sent you a text message to complain that his computer hard drive light is always blinking on - even though he's not touching the keyword. With a promise of decent drinks after work, you remotely connected to his machine and started capturing traffic. Sure enough - loads of packets were flying around. Just then, Scott arrived in your office.
Hmmm… Scott is here but his computer seems to have a lot of network activity going on. You stopped the trace to see what happened in the background on his system.
QUESTIONS:
1. How many different IP hosts is Scott's machine communicating with?
Analysis - We already did this thing in the previous challenge, we just have to check the communication. Select Statistics>Conversations
Then in the IPV4 tab we can see the count is 152, which means there are 142 IPs communicating with Scott's machine.
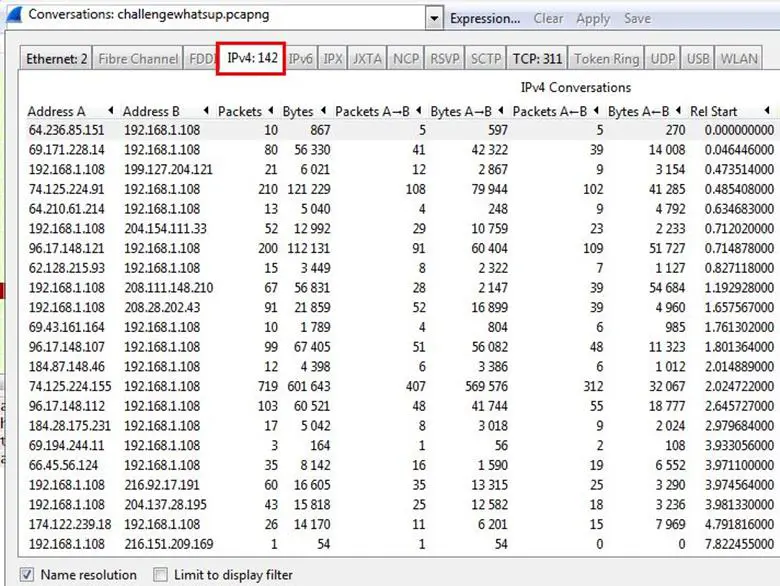
Answer: 142
2. What is the average packets per second rate seen in this trace file?
Analysis - We can check out the packets rate per second from the summary options. Select > Statistics> Summary
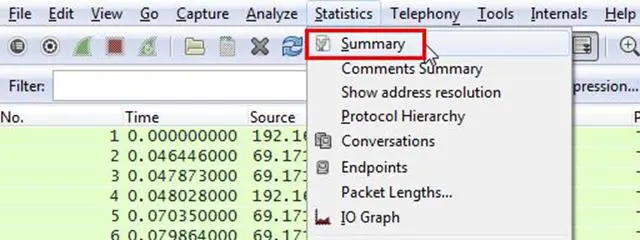
And as shown below, we can see the average packets rate per second.
Answer: 30.589
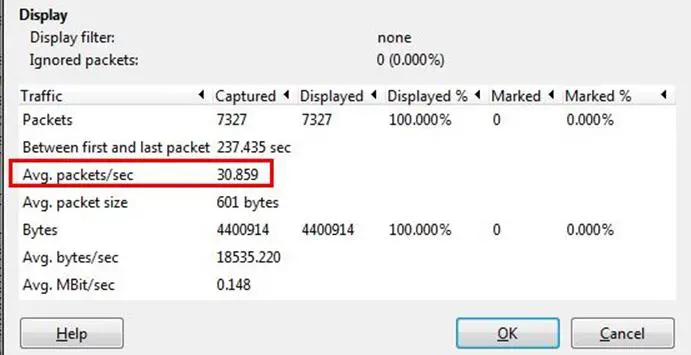
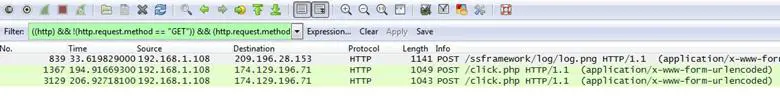
3. How many HTTP POST requests did Scott's machine send?
Analysis - For this task we need only the POST request, so we will first remove the GET request. We apply a filter for removing the GET request. As can be seen below, just right click on the request method GET and select Apply as Filter > and not selected
Now we can see one POST request and we need only this type of request, so again we did a filter. Same process: Right click on the Request Method POST and select Apply as Filter > and Selected
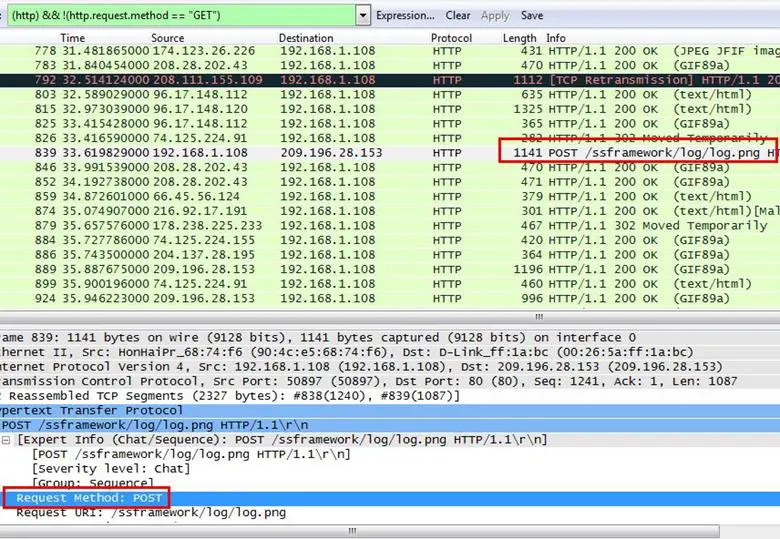
Now we can see only POST requests and there are only three.
4. What location information is contained in the POST to scanscout.com?
Analysis - Well this is not hard. Our first hint is to find the POST request, and there are only three of them, and next we have to find which request header contains the scanscout.com. We checked out all three requests and found one of the request headers is for scanscout.com.
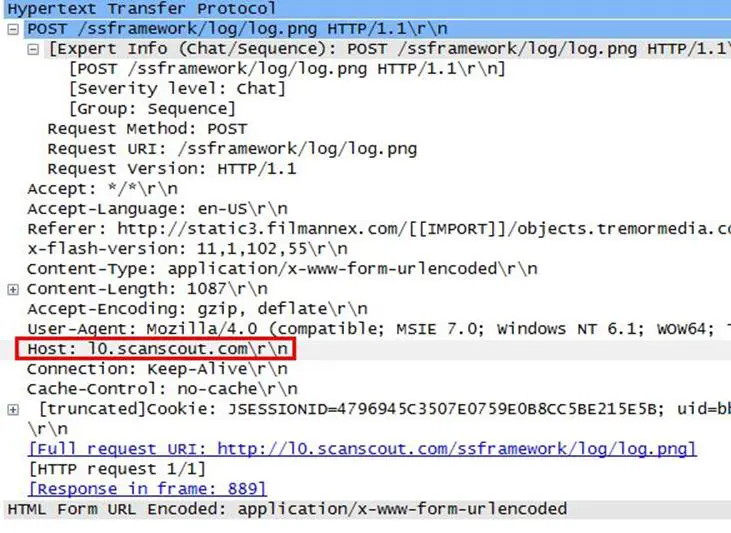
Now we have to find the location, so just right click on the POST request and select Follows TCP Stream.
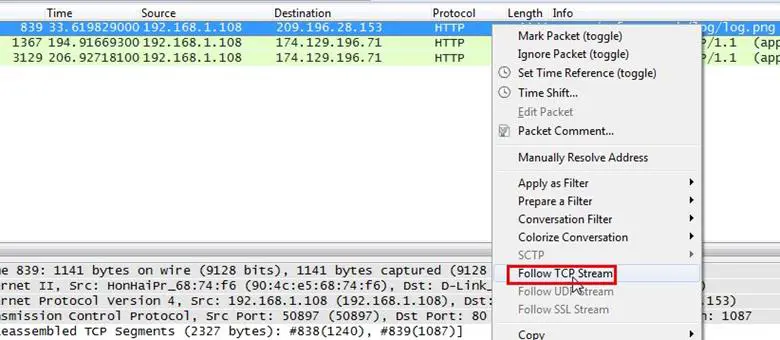
As can be seen below we can now see the whole POST data of that request. It contains a lot of parameters and its value and its URL are encoded, so we are not able to read them clearly.
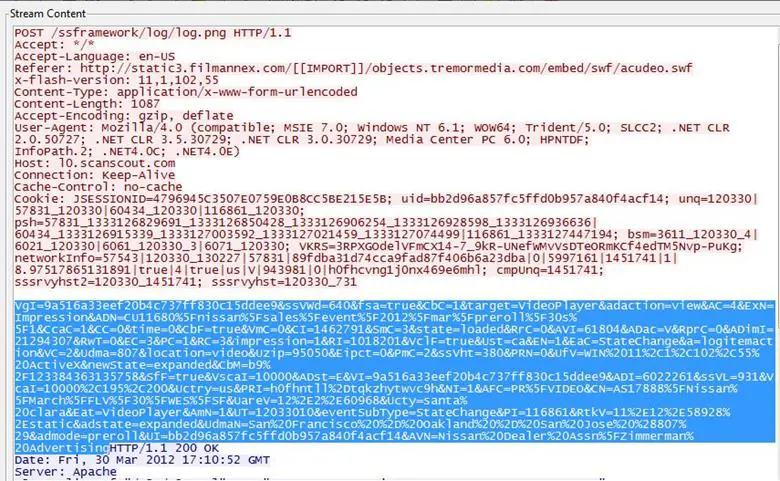
We copied the whole data and decoded it and now we can see in the below figure that the parameter UdamN has its value San Francisco - Oakland - San Jose.
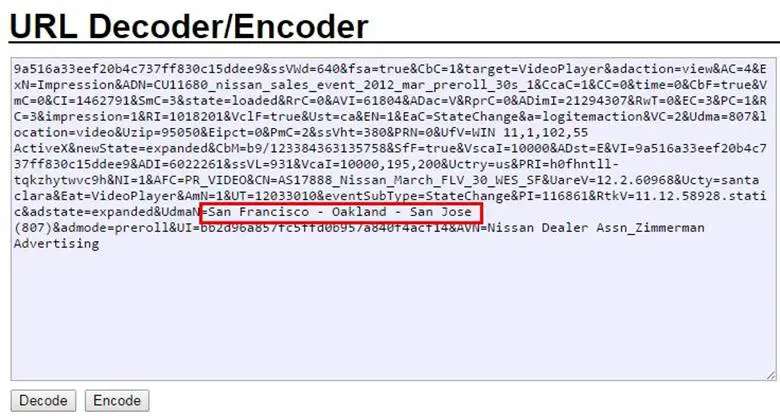
Answer: San Francisco - Oakland - San Jose
5. What application appears to be generating these GET/POST requests?
Analysis - Pretty much an easy answer, it's obviously a browser, but we have to find which one. It can be done by analyzing the User-Agent string of any GET/POST request.
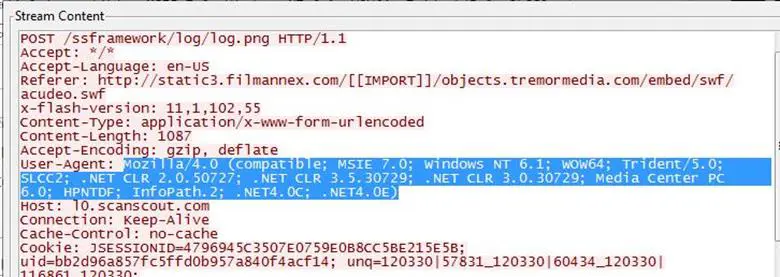
We just copied the user-agent string and did a Google search on a user-agent string detector, and we found one and the browser was Internet Explorer 7.0.
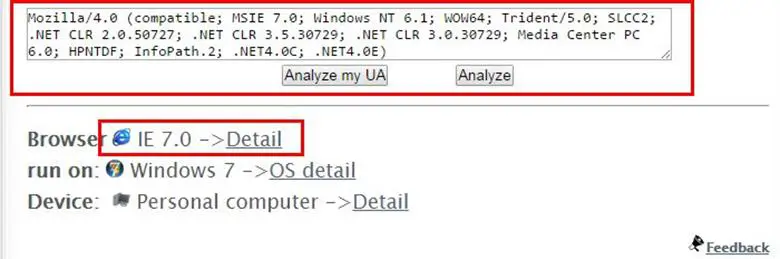
Answer: Internet Explorer 7.0
6. Find, export and reassemble load_small.png. What shape is in the image?
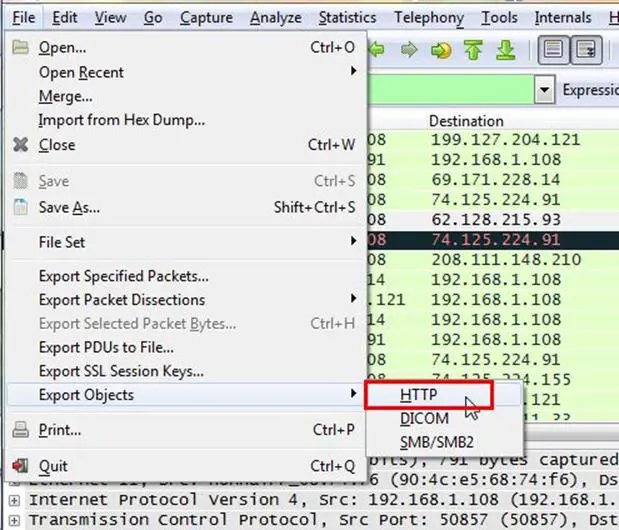
Analysis - Hmm... We have to find a .png image in this. All packets can't check every request manually and look for this image, so we will extract all the HTTP objects from this trace file. Go to File and select Export Objects > HTTP
Next it will ask to save objects for hostnames. In this case we don't know where this load_small.png file is located in which hostname, so that's why we will save all.
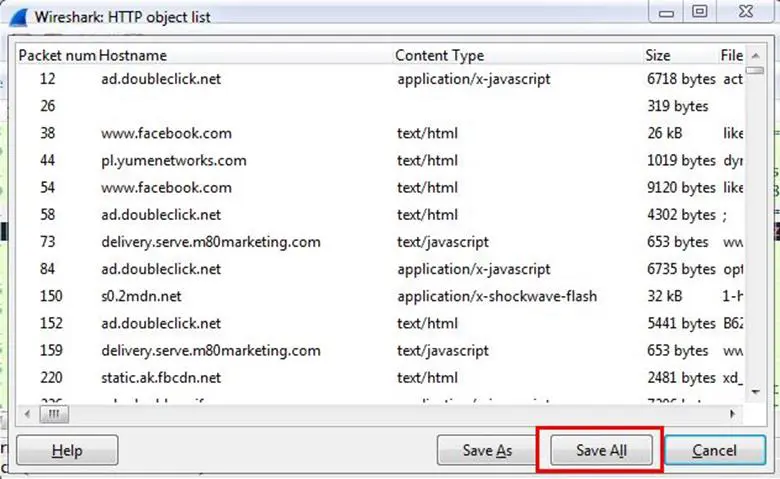
We saved all files in a directory and searched for the load_small.png file and we found that file.
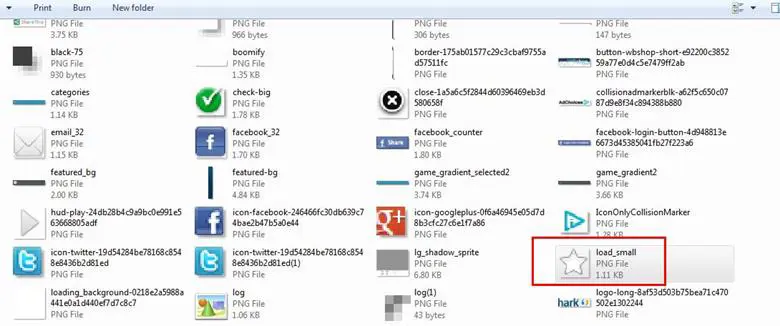
Answer: Star
CHALLENGE #3: FTPS ANALYSIS
TRACE FILES: challengeftp1.pcapng challengeftp2.pcapng
BACKGROUND: A customer needed a secure file transfer application put in place. These two trace files illustrate the separate options they have tested - implicit FTPS and explicit FTPS.
QUESTIONS:
1. What is the IP address of the server?
Analysis - As we did in the previous challenges for checking the communication of the IP addresses, we selected the Conversation options and it can be seen below that 192.168.1.1 is the request sender and 64.65.53.234 is the receiver, and it must be the FTP server.
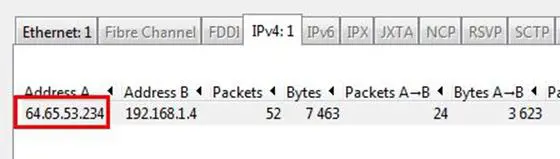
Answer: 64.65.53.234
2. Which trace illustrates implicit FTPS?
Analysis - First of all we need to understand what are implicit and explicit FTPS. After Googling it, we found a common difference in both, that implicit FTPS is a secure connection and it runs on port 990 and the explicit runs on port 21.

Now we opened both trace files for finding the port number from which we can identify the explicit/implicit ones. We found that challnegftp1.pcapng file has port number 990 and is the implicit one.
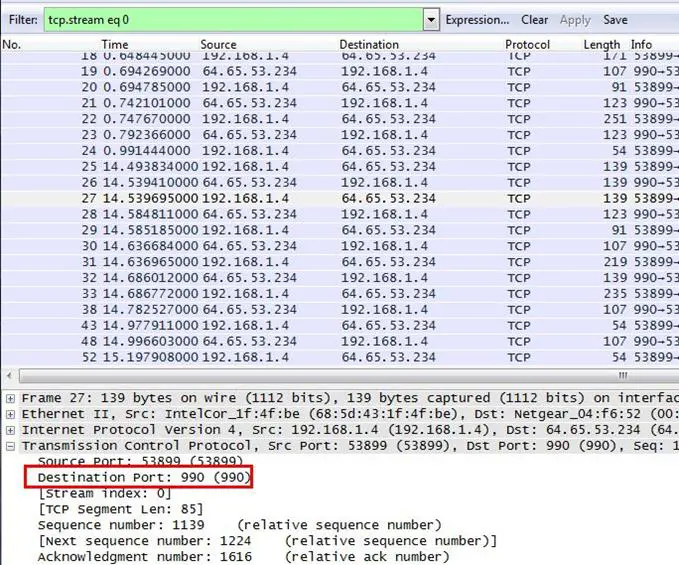
Answer: challengeftp1.pcapng
2. Which trace illustrates explicit FTPS?
Analysis - This answer is obvious and needs no explanation.
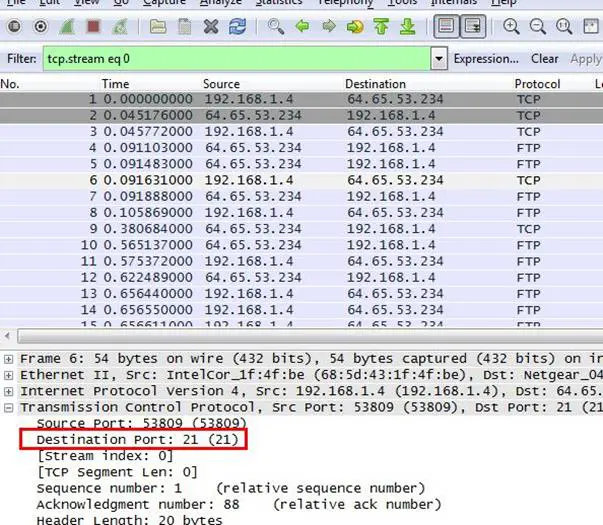
Answer: challengeftp2.pcapng
4. What IP address initiated the data connections in the trace file?
Analysis - We already found the FTP server IP in the first question and the host which is initiated by the connection with the FTP server.
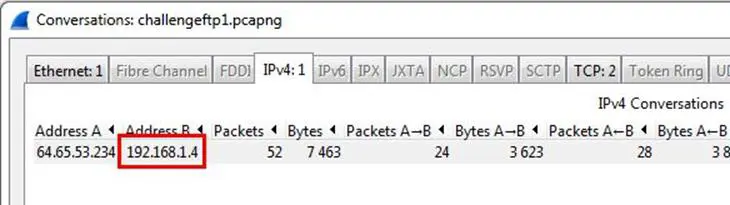
Answer: 192.168.1.4
5. What port numbers are used for the data connection in each trace file?
Analysis - We opened the first trace file and now we have to find out on which ports data the transfer took place. Go to Statistics and select Conversations. As can be seen below, in the TCP tab we can see two connections initiated: the first connection is with the FTP port on 990 and the other connection is with 10007, where data transfer is done.
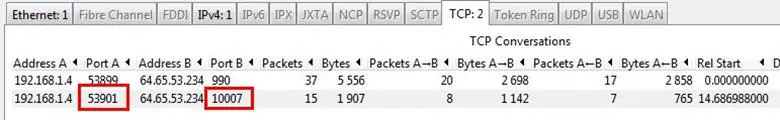
Answer: 53901-10007
By following the same process, we found the ports on the second trace file also.
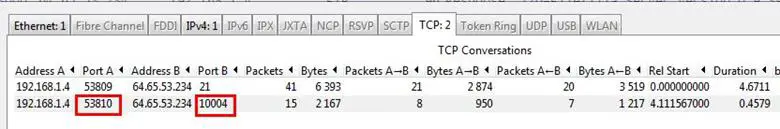
Answer: 53810 - 10004
Stay tuned for the next part....
References:
http://www.wiresharktraining.com/sharkfest2013challenge.html
http://www.defcon.org/images/defcon-10/dc-10-presentations/dc10-arkin-xprobe.pdf

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
http://help.globalscape.com/help/secureserver3/Explicit_versus_Implicit_SSL.htm