Russia and Ukraine: Information Warfare
The Current Situation
The fighting in Ukraine has escalated sharply since the elections on May 25th. President-elect Petro Poroshenko, backed by the European Union and US, ordered the national army to strengthen its eastern border with Russia and stop an influx of fighters.
The Ukraine offensive came after pro-Russian rebels had launched several assaults on Ukrainian forces, such as in the battle for control of Donetsk's international airport. Ukrainian troops attacked the rebels by launching a major assault on separatist positions in their stronghold of Slovyansk.

Learn Network Forensics
The United States and Europe accuse Russia of fomenting the separatist group's unrest in eastern Ukraine after Moscow annexed the Crimea in March.
NATO's senior military leader declared that the Russian Government is planning to withdraw the majority of up to 40,000 troops it had deployed close the Ukraine borders, but several large formations will remain in the area.
General Philip Breedlove reported that the Government of Moscow is actively acting to destabilize the eastern part of Ukraine by promoting "very well-led, very well-financed, very well-organized clashes with Ukrainian forces."
"It is very clear that the Russian influence is a part of this … Russian irregular forces, Russian-backed forces and Russian finances are very active in eastern Ukraine," Breedlove said.

Figure - Pro-Russian rebels inspect the offices of an Ukrainian border troops military unit in Luhansk. Photo: AP
Russian Information Warfare Capabilities
Ambassador Extraordinary and Plenipotentiary of the Republic of Latvia to the United States Andris Razans commented recently on the decision of the Russian government to pull back significant ground forces from the Ukrainian border, stating that the government of Moscow in reality is continuing Information Warfare against the adversaries.
"Sometimes we might be characterized as alarmists, troublemakers, etc., but I think we are realists … You might be moving your troops away … but on the other hand if you continues to support activities that … keep the situation unstable, I think we stand very far away from 'backing off,'" explained Razans, referring to the massive use of cyber and information warfare capabilities of the Russian government.
Security experts are aware of the powerful Russian Army, composed of highly skilled hackers able to hit any government with covert operations and to design sophisticated cyber weapons for cyber espionage and sabotage.
"Russia is much more powerful and more skillful in the cyber arena than we know here in the western world … While their campaign against Ukraine has kept a lower profile than the so-called 'cyber war' against Estonia (Latvia's neighbor) in 2007, they've been 'much more active' than most people realize," said Jarno Limnell, a former Finnish military officer who's now director of cybersecurity for Intel Security.
In March, the BAE System revealed a cyber espionage campaign on a large scale that targeted systems all over the world, mainly the Ukrainian government ones.
The report issued by BAE demonstrated the existence of a powerful spyware know as Turla, which compromised Ukraine systems more than any other country. Despite that there is no evidence to prove the malware was developed by the Russians, security experts believe that the government of Moscow is the responsible for the diffusion of the malicious code that curiously hasn't hit any Russian system.
According to Limnell, the malware is dated at least 2008, considering that it was active since 2010, and that for its development, skilled professionals had worked a couple of years.
"It's been called the most sophisticated spying malware that's ever created … it's five to six years old … This is estimation and speculation, I have to emphasize that," he said — that Russian malware is "sleeping" in all sorts of Ukrainian critical infrastructure, ready to wake up on command and wreak havoc with the electrical grid, financial system, and so on. "I believe preparations for these kinds of strategic cyber attacks are being made," Limnell said.
If Russia has developed such sophisticated malware 6 years ago, let's try to image its cyber capabilities today.
"When we think about cyber in the western countries, we usually think about DDOS attacks or cyber attacks on our critical infrastructure … Cybersecurity is too often treated only as a technological problem…. but from the Russian point of view cyber is primarily the information sphere — what the Soviets would have called propaganda," Limnell added.
The Russian government can also count on a dense network of patriotic hackers that systematically hit foreign government networks, and Ukraine is probably within the principal targets of these groups. But Russia has also used online propaganda to destabilize its adversaries. Social media are new battlefield. In this period, many accounts on the principal social media were spreading news and videos related to the situation in critical areas of the Ukraine.
Psychological operations are an essential instrument of modern warfare, and the intense activities of the principal media are focused on the incitement to fight on both sides. The BuzzFeed website recently reported that the Russian government is recruiting and training a new army of online trolls to change global sentiment on its invasion of Ukraine.
The cadre of trolls is spreading comments and driving discussions on the principal western online media outlets, including Fox News, Huffington Post, The Blaze, Politico, and WorldNetDaily.
The revelation is based on the disclosure of plans attached to emails leaked by a mysterious Russian hacker collective, which shows IT managers reporting on a new ideological front against the West in the comments sections of media agencies.
The group which disclosed the emails, which calls itself Anonymous International, is apparently not linked to the popular collective Anonymous.
The group has also posted online the internal Kremlin files related to plans for the Crimean independence referendum and the list of pro-Kremlin journalists whom Putin gave awards for their Crimea coverage.
"None of the group's leaks have been proven false."
The documents report detailed instructions provided to the commenters that describe the workload expected of their activities.
"On an average working day, the Russians are to post on news articles 50 times. Each blogger is to maintain six Facebook accounts publishing at least three posts a day and discussing the news in groups at least twice a day. By the end of the first month, they are expected to have won 500 subscribers and get at least five posts on each item a day. On Twitter, the bloggers are expected to manage 10 accounts with up to 2,000 followers and tweet 50 times a day.
They are to post messages along themes called "American Dream" and "I Love Russia." The archetypes for the accounts are called Handkerchief, Gay Turtle, The Ghost of Marius the Giraffe, Left Breast, Black Breast, and Ass, for reasons that are not immediately clear," states BuzzFeed.
The psyop seems to have started in April and is led by a firm called the Internet Research Agency based in Saint Petersburg. The project leaders mentioned in the documents denied any involvement in the propaganda, and the Kremlin declined to comment on the event.
Some of the leaked documents detail an extensive effort to create hundreds of fake accounts on principal media like the Huffington Post, and to recruit hundreds of freelance bloggers to comment on Russian-language sites.
Pro-Russian forces have been accused to have arranged a large-scale PSYOP through social media since the Ukraine's political crisis started. The media reported a campaign dubbed "Polite People", which was orchestrated to promote the invasion of the Crimean Peninsula.
"This is similar to media dynamics we observed in the Syrian civil war … Russian news channels broke stories that seemed tailor-made to reinforce pro-Assad narratives, and then Syrian social media authors pushed them," commented Matt Kodama, an analyst at the web intelligence firm Recorded Future.
The Kremlin reserves a great interest in the surveillance of social media in the country. The Russian government is aware of the destabilizing power of psyop operations through blogs and social networks. In late 2012, the government of Moscow announced the deployment of one of the most sophisticated surveillance systems. Events such as the Arab Spring and the concomitant growth of political activism have alerted the Russian government to the risks related to the manipulation of information on social media. The imperative is to be able to monitor everything to avoid surprises, to keep Western eyes far from "internal questions".
"New technologies are used by Western secret services to create and maintain a level of continual tension in society with serious intentions extending even to regime change…. Our elections, especially the presidential election and the situation in the preceding period, revealed the potential of the blogosphere," declared the First Deputy Director of the FSB, Sergei Smirnov.
Smirnov stated that it was essential to develop ways of reacting adequately to the use of such technologies and confessed openly that "this has not yet happened."
A Russian law approved in August 2012 also forces bloggers with more than 3,000 followers to register its activity to a government register.
"The internet has become the main threat — a sphere that isn't controlled by the Kremlin," said Pavel Chikov, a member of Russia's presidential human rights council. "That's why they're going after it. Its very existence as we know it is being undermined by these measures."
The Snake Platform
The Snake is a hacking platform adopted in a large-scale cyber espionage campaign that targeted highly confidential systems in governments and military industries all over the world. Experts at BAE Systems Applied Intelligence, who discovered the Snake campaign, have found evidence of a link between of the Uroburos rootkit, a malware used for espionage campaigns and discovered by the German firm G Data, and the Snake platform.
Malware experts at BAE also detected another piece of malware named Turla. According to their investigation, this malicious code was developed by a Russian cyber specialist, and there is the concrete possibility that Turla and Uroburos have been developed by the same group of experts, which according to BAE could be part of a cyber weapon program of the Russian government.
According to the investigation conducted by malware experts, the Snake cyber espionage campaign remained undetected for a long time, at least for eight years. Researchers have also found a link to older pieces of malware, such as Agent.btz, a worm which infected US military networks and nearly 13,800 systems across 100 countries in 2013.
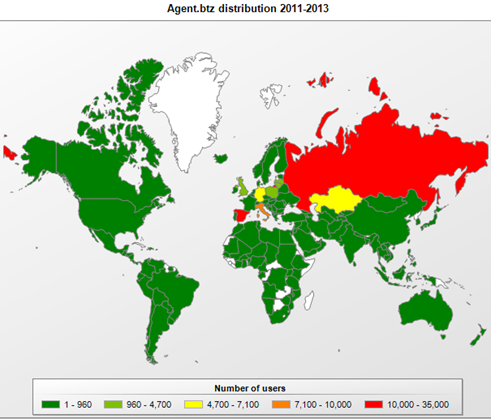
Figure - Agent.btz infection distribution
Exactly like the predecessors Agent.btz and malware used for the Red October cyber espionage campaign, Turla seems to have been designed by Russian-speaking malware authors. Turla uses the same XOR key and log file names as Agent.btz, but we have to consider that it could be a diversionary strategy of the malware authors.
The details of the Agent.btz agent have been known publicly for a long time. Many reports provide information regarding the name of the files used, including the specific log file names and even the XOR key.
"The connection between Turla and Agent.btz is more direct, although not sufficiently so to conclude that the two programs have the same origin. Turla uses the same file names as Agent.btz – 'mswmpdat.tlb', 'winview.ocx', and 'wmcache.nld' for its log files stored on infected systems," saidAleks Gostev, Chief Security Expert at Kaspersky Lab.
Turla and Agent.btz have files with identical names, but the surprise is the presence of a file called "thumb.dd" present in both Turla and Red October malware.
"We cannot make such a conclusion based only on the listed facts … All the information used by developers was publicly known – at least by the time of Red October and Gauss/Flame creation. First of all, it wasn't a secret that Agent.btz used 'thumb.dd' as a container file to collect information about infected systems … Secondly, the XOR key used by developers of Turla and Agent.btz to encrypt their log files was also published in 2008. It's unknown since when this key was first used in Turla, but we see it for sure in the latest samples of the malware (created in 2013-2014). At the same time, there are some data that Turla's development started in 2006 – before any known sample of Agent.btz. Which leaves the question open," wrote Gostev.
Probably the malware used for the campaign was designed to scan for the "thumb.dd" file on the victim machine to steal the data contained in the file.
Gostev remarked that there also are some similarities between the Flame, Gauss and the Agent.btz, but this circumstance could be a consequence of the fact that the authors of Flame and Gauss have had access to the analysis of Agent.btz.
"Summarizing all the above, it is possible to regard Agent.btz as a certain starting point in the chain of creation of several different cyber-espionage projects. The well-publicized story of how US military networks were infected could have served as the model for new espionage programs having similar objectives, while its technologies were clearly studied in great detail by all interested parties. Were the people behind all these programs all the same? It's possible, but the facts can't prove it," Gostev reported in the analysis he conducted.
Let's take a look at the distribution of the Snake malware samples. It's a significant number of malicious code which targeted mainly the Ukraine and the Lithuania.
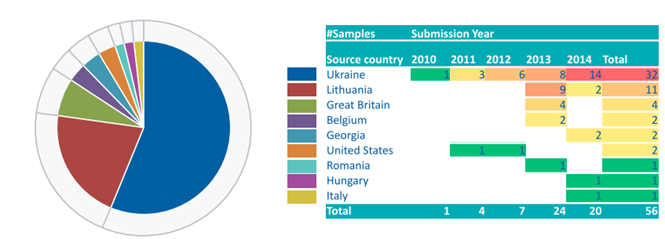
Figure - Snake Samples
Analyzing the day of the week and hour of the day in which the malware samples were compiled, the experts have noticed a pattern already discovered in other state-sponsored cyber espionage campaigns: malware developers operate a working week in working time. The working time has been adjusted to UTC+4 to show a possible fit to the operators' local time.
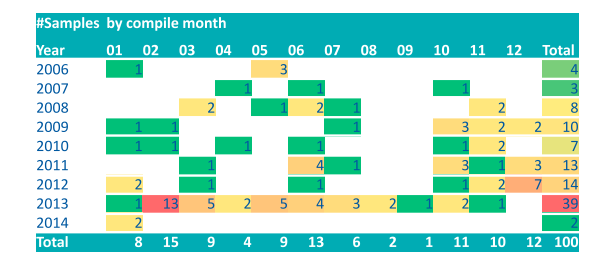
Figure - Snake sample by compile month
The Snake platform is probably one of the most sophisticated platforms for cyber espionage since 2007. It seems that malware authors behind the operation are Russian and have operated mainly in working time during working days. The last coincidence is that Russian malware mainly hit recently Ukraine systems.
The Cyber Dispute during the Geopolitical Tension between Russia and Ukraine
One of the most interesting analyses proposed since the Ukraine political crisis was proposed by experts at FireEye. The analysts have focused their investigation on the increased number of cyber attacks between the two countries.
Groups of hackers on both sides may be actively engaged in online campaigns. During the last weeks, security experts at FireEye have observed the rise of DDoS attacks and malware-based cyber attacks, according to its own data.
Security analysts at FireEye have collected evidence of the intense activity in cyberspace between Russia and Ukraine. The analysts have focused the investigation on malware "callbacks", malware communications seeking instructions from an infected machine to the command and control servers, over the past 16 months.
"One of the most reliable ways to discover computer network operations is to look for malware "callbacks" – the communications initiated from compromised computers to an attacker's first-stage command-and-control (C2) server. At FireEye, we detect and analyze millions of such callbacks every year." "As we track the evolution of callbacks during this period, we see a likely correlation between the overall number of callbacks both to Russia and to Ukraine, and the intensification of the crisis between the two nations," wrote FireEye senior global threat analyst, Kenneth Geers.
In the following table is proposed the list of nations by number of malware callbacks. Concurrently with geopolitical tensions, Ukraine has jumped from #12 to #9. Russia has passed from an average #7 to #5.
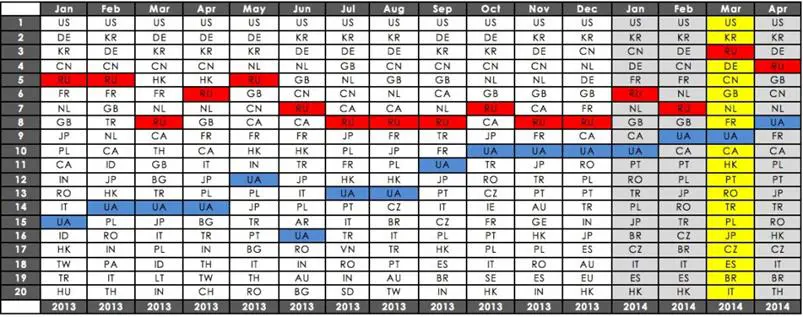
Figure - List of nations by number of malware callbacks
The data proposed in the table demonstrate that Russia was among the countries with the greatest number of callbacks, but analyzing the number of malicious calls, security researchers noticed an intensification of the activities in concomitants of the Ukrainian crisis.
The greatest jump in the malware callback data occurred in March 2014, exactly in the same period the Russian government authorized the use of military force in the Crimea. Many experts have found many similarities with tactic adopted by cyber units against Georgia in 2008.
"The rise in callbacks to Russia and Ukraine (or to any other country or region of the world) during high levels of geopolitical tension suggests strongly that computer network operations are being used as one way to gain competitive advantage in the conflict," states the post.
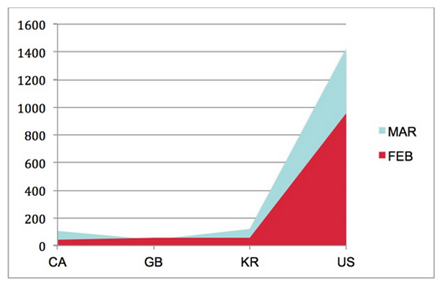
Figure - Rise in malware callbacks to Russia from three of the top four source countries in February: Canada, South Korea, and the U.S
Below is a list of events that occurred in March:
- Russia's parliament authorized the use of military force in Ukraine;
- Vladimir Putin signed a bill incorporating the Crimean peninsula into the Russian Federation;
- The U.S. and EU imposed travel banned and froze assets on some senior Russian officials;
- Russian military forces massed along the Ukrainian border; and
- Russian energy giant Gazprom threatened to cut off Ukraine's supply of gas.
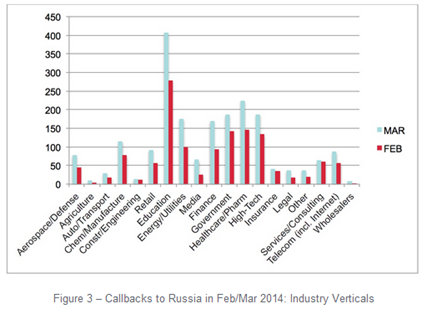
Figure - Callbacks per industries
FireEye observed malicious traffic from any country of the globe. Malware callbacks to Russia came from compromised computers in a range of countries, including the US, Italy, South Korea and Japan.
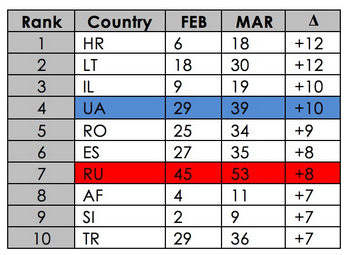
Figure - Callbacks in 2014: Number of Source Countries
"It is important to note that nearly half of the world's country experienced a decrease in callbacks during this same time frame," reports the blog post on data in the above table.
Who is behind the cyber operations?
The expert highlighted that it isn't his intention to suggest that Russia and/or Ukraine are the sole threat actors within the data set proposed, and he doesn't speculate on the precise motives of the attackers behind all of these malware callbacks.
"Within such a large volume of malware activity, there are likely to be lone hackers, 'patriotic hackers', cyber criminals, Russian and Ukrainian government operations, and cyber operations initiated by other nations," Geers said.
Personally, I have no doubts that the rise in malware callbacks in Russia and Ukraine is superior to the increment observed in any other area and is for sure related to the geopolitical tension between the two states.
Another interesting presentation conducted on the cyber attacks observed during the Ukrainian crisis is titled "Cyber attacks in the Ukraine - Quantitative Analysis December 2013 –March 2014". Its author, Glib Pakharenko, described the growth of cyber attacks in the period from December 2013 - April 2014, focusing on the offensives that hit Ukrainian assets. The majority of attacks were DDoS and targeted mainly media, which have supported the Eurorevolution and government entities. The expert also referred to numerous incidents that occurred to the mobile infrastructure. The presentation evaluated more than 35 incidents within public and private sources.
When conflict tension raised, numerous "anonymous" groups emerged, including the "CyberBerkut" in support of the Russia and "Cyber100" in support of Ukraine. At the same time, the Non-Governmental Organization "Ukrainian Information Security Group" launched a campaign to mobilize volunteers among IT security specialists to improve defense of Ukraine from the potential cyber attacks originated by the Russian cyber army.
As explained by Glib Pakharenko, the ISACA Kyiv Chapter started a dialog with Russian security experts to promote initiatives to guarantee peace between the two countries.
The majority of cyber attacks against Ukraine aimed to block the audience of media portals to reach them. Several inefficiencies were observed in the banking industry, such as bank clients could not perform payments through the Internet.
The majority of attacks were not complex in nature. There is no evidence that any APT group was involved, nor that Russia has started an information war against the Ukraine to support military operations in the Crimea. The cyber attacks were originated by botnets, the flood attacks were using spoofed IP addresses, and the packets were coming from all BGP peers.
DDoS attacks were the principal offensives against Ukrainian assets, but as I have described in a past article, there were also numerous physical attacks against infrastructure, including cables cut over, building assault, and server expropriation by the police. The physical attacks were the offensive with the largest impact on the adversaries, while DDoS attacks were observed all the time in recent years. Physical attacks were mainly related to the fights between Ukrainian forces and pro-Russia dissidents.
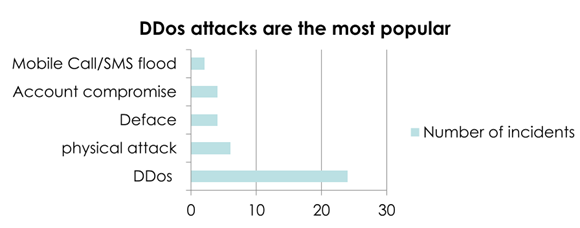
Figure - Cyber attacks against Ukraine - Glib Pakharenko
Most attacks affect resources managed from Kyiv and Crimea, in concomitance with the Yanukovitch fall.
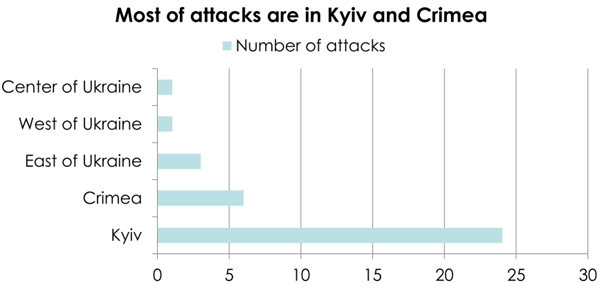
Figure - Attack against Kyiv and Crimea
Side Effects
Security experts are sure that the recent cyber attacks against the Belgian foreign ministry are related to the dispute between Russia and Ukraine. In May, unknown hackers stole data related to the Ukraine crisis from the ministry. The cyber attack has caused the crackdown of targeted servers, which has left diplomats without Internet service. Email services were also impacted by the attacks.
Belgian Foreign Minister Didier Reynders confirmed to the Belga news agency that "everyone (on the European level) notes at this moment a very powerful pickup in hacking activity probably coming from the east and in any case having to do with Ukraine."
According to the local press, the attackers used the malicious code Snake described in this post, probably the same that caused the disruption in Brussels.
Hackers used the code to infiltrate Belgian foreign ministry networks and steal documents related to the situation in Ukraine. It seems that they were interested in any document containing information on the crisis in East Europe and targeted the Belgium entity because its access to sensitive information was managed by countries in the European Union.
"It was malware which copied documents specifically related to the Ukraine crisis … We saw that data was stolen about the crisis in Ukraine but we do not yet know who stole it," reported a spokesman for the Belgian foreign ministry.
The spokesman avoided providing further details on the stolen documents and their level of confidence. He also confirmed that the network has been completely shut down and all the services were interrupted. Fortunately, the ministry's internal networks weren't compromised.
Another important effect noted by cyber experts is the significant increase in the number of corporate data breaches in every industry.
Recently, American Express reported that unknown hackers accessed data related to customers' credit card data. AmEx revealed that nearly 76,000 cardholders in California would be notified of a breach on their accounts after a data breach was verified by the company.
A group of hacktivists belonging to Anonymous Ukraine claimed responsibility for the attack and published cardholders' account numbers, card expiration dates, the dates the cards became effective, and the four digit codes printed on the front of the cards.
Unfortunately, this is just a small subset of the overall 668,000 total AmEx numbers that were part of the 7 million records released by Anonymous Ukraine in March. The group Anonymous Ukraine published data related to MasterCard (1.7 million) and Visa (3.2 million). The overall amount of information also includes 362 records related to Discover cards.
"Some of the non-AmEx data released included name, address, SSN, birth date, and even PINs."
Most likely, much of the data was not from a new breach, but from older breaches, as many of the cards had already expired.
The episode appears very suspicious. The security community speculates that the "real" Anonymous Ukraine group was not involved with the release of the information. Anonymous official social media accounts haven't claimed the responsibility for the hack. Another particular to consider is that the original discussion regarding the stolen credit card data was posted on Russian language forums, a circumstance that suggests that behind the hack there is a Russian criminal gang.
For further information about the evolution of the cyber dispute between Russia and Ukraine, stay tuned.
(Security Affairs – Russia and Ukraine, malware callbacks)
References
http://securityaffairs.co/wordpress/25369/intelligence/russia-and-ukraine-cyber-tension.html
http://securityaffairs.co/wordpress/24912/cyber-crime/belgian-foreign-ministry-hacked.html
http://securityaffairs.co/wordpress/23012/intelligence/agent-btz-malware-link-snake-red-october.html
http://securityaffairs.co/wordpress/22875/intelligence/snake-cyber-espionage-campaign.html
http://www.buzzfeed.com/maxseddon/documents-show-how-russias-troll-army-hit-america
http://www.baesystems.com/article/BAES_165734/the-snake-campaign
http://www.buzzfeed.com/maxseddon/documents-show-how-russias-troll-army-hit-america
http://info.baesystemsdetica.com/rs/baesystems/images/snake_whitepaper.pdf
http://kavkazcenter.com/eng/content/2014/06/03/19247.shtml

Cybersecurity interview guide








