Open source threat intelligence tools & techniques
The Internet, the network or networks is huge and has the most significant data you can ever think about; it is not limited to search the people or company information only, but it has the potential to predict the future happenings. The said prediction is based on data, that you need to process for the information, the job of an OSINT professional is to connect the data points and draw a meaningful conclusion:
Yes, data is everywhere, and you can do wonders with it. Let's discuss the role of open source intelligence in threat management.
Open source threat intelligence
Threat is anything that can potentially harm the business operation or continuity; threat depends on three core factors:
- Intention: A desire or objective
- Capability: Resources that support the intention
- Opportunity: Right timing, technique, procedure, and tools
Often organizations fail to identify the threat, and they usually spend too much on fixing the vulnerabilities & investigating the issues after the attack, rather fixing it before it appears.

Learn Network Forensics
Threat intelligence, as Gartner defines: "evidence-based knowledge, including context, mechanisms, indicators, implications and actionable advice, about an existing or emerging menace or hazard to assets that can be used to inform decisions regarding the subject's response to that menace or hazard."
It is an act to predict (based on the data) the upcoming attacks against an organization. Whereas, open source threat intelligence refers the process of using publicly available sources to predict the actor or potential action (threat). Cyber threat intelligence helps you to make better decisions about your defense and other benefits along:
- Adopt a proactive approach instead of reactive; you can create the plan to fight against the current and future threats.
- Organize the security alert mechanism, know before they attack you.
- Always provide the better response to the security incidents
- Use the cyber intelligence feeds to provide your security technologies up-to-date information to block the emerging threats
- Of course a better investment regarding risk and benefit analysis.
What to look for:
- Malicious IP addresses
- Domains / Websites
- File hashes (malware analysis)
- Victim industries / countries
Open source threat intelligence framework
OTX - Open Threat Exchange: AlienVault Open Threat Exchange (OTX) provides open access to a global community of threat researchers and security professionals. It delivers community-generated threat data, enables collaborative research, and automates the process of updating your security infrastructure with threat data from any source.

Open source threat intelligence gives actionable advice to follow, learn from the attacks and patch it before they hack you.
Let's compare the two situations below:
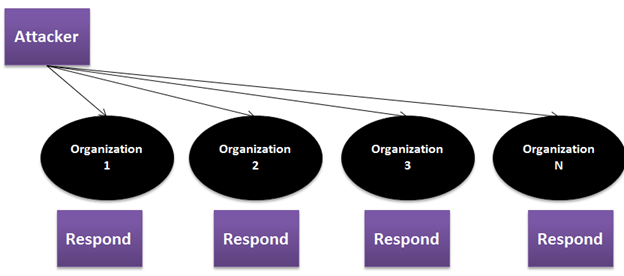
Traditional Approach
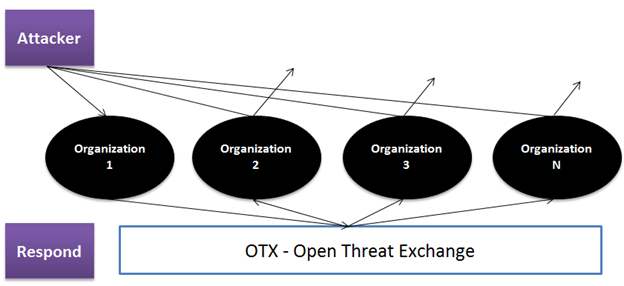
OTX Approach
The process is very straightforward, keep an eye on the emerging threats, define the rules and strengthen your policies that block those threats; this proactive approach saves your infrastructure and reputation as well. An attack not only destroys the technology infrastructure or steals data, but it also hurts the brand reputation, customer trust, and future sales as well. So responding to an attack can't retrieve what's being stolen before, the smart strategy is to block the attack before it happens to you. It also helps to:
Threat indicators
Threat indicator is an entity that indicates the possibility of an attack or compromise of some kind. The most common types are file hashes (signatures), and reputation data on domains and IP addresses that have been associated with attacks.
The hash file is a unique identifier of a worm, Trojan, keylogger and another type of malicious program. MD-5 or SHA-1 generates a unique fingerprint of the program during the compilation process; the malicious file can be identified using its unique text string. Similarly, websites, IPs, and even specific URL propagate malware; an affected user puts the entire network at risk. Track the malicious websites, blacklisted IPs, identify the malicious files using the hash string and block them accessing your technology infrastructure. The associated risk with the malicious websites/IPs:
- Spam and phishing pages
- Malware and spyware
- Anonymous proxy tools and P2P networking
- Darknet IP address (using TOR)
- C&C server that manages botnets
Use the public and private feeds to gather the information, analyze them and block the access.
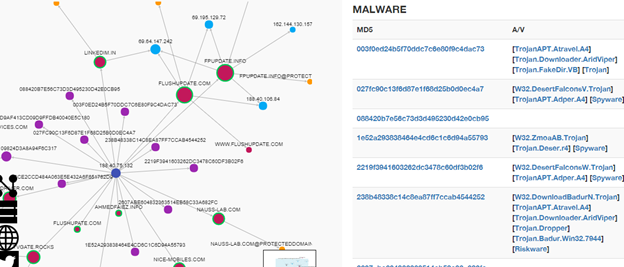
Threatcrowd, a search engine for threats allows the user to search and investigate the threats associated with the IPs, websites or organization. It also provides the API and with the ThreatCrowd API you can search for:
- Domains
- IP Addresses
- E-mail addresses
- File hashes
- Antivirus detections
It fetches the information from Virustotal and malwr.com; it also provides MALTEGO transform to analyze and linked the data:
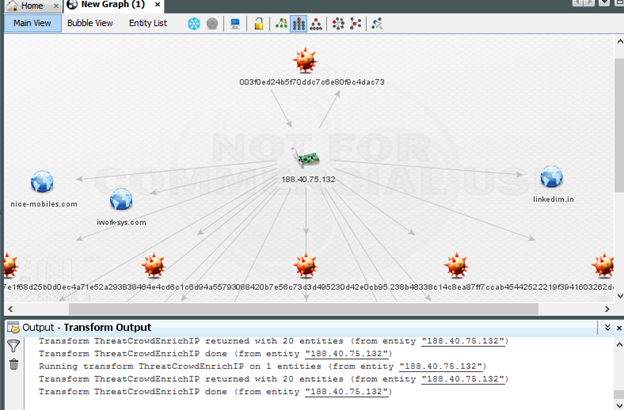
It shows the analysis of an MD-5 hash; the information reveals its source IP, domains, and the other associated hashes. These signatures represent the malicious file that should not run on your technology infrastructure.
Detail information of the Trojan can be seen on the threatcrowd website.
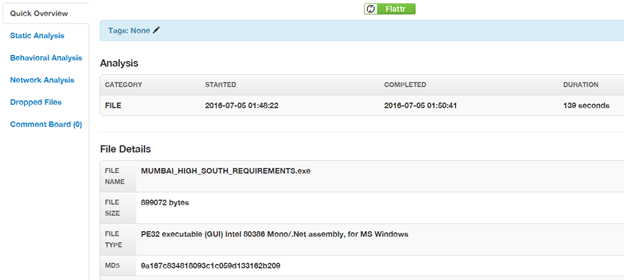
Use malwr.com for detailed analysis:
- Static analysis
- Behavioral analysis
- Network analysis
- Screenshots
- Domain and IPs
- Registry keys
- And much more.
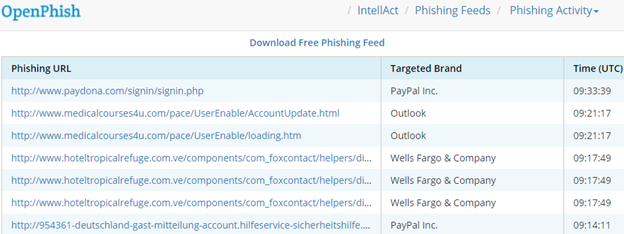
The rising phishing threat has already shaken the world of cyber security; training and security awareness is not the only solution. You can stop the phishing attacks by using actionable intelligence, the following services track and publish the phishing pages:
- openphish.com
- phishtank.com
Don't let your employee or user fall for fake pages like:
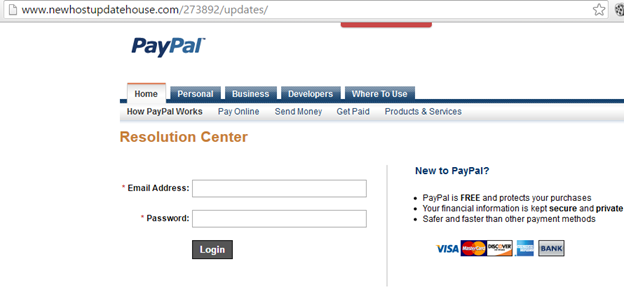
Openphish identifies the zero-day phishing pages and provides comprehensive, actionable, real-time threat intelligence.

Cybersecurity interview guide
All the discussed and important data are available publicly for free to everybody, it requires effort to gather and analyze these data. Using Maltego transform and open threat exchange program, you can access the data easily. It is also important to participate in these programs to enhance them before it is the matter of collective threat intelligence management.







