PoS Malware is More Effective and Dangerous
Introduction to POS malware
In September 2014, experts at Trustwave firm published an interesting report on the evolution of the point-of-sale (PoS) malware in recent months. The attention of the media on PoS malware was raised after the numerous data breaches suffered by retail giants Target, Home Depot and Neiman Marcus. Experts at Trustwave investigated a number of incidents involving payment card data, and researchers examined a large amount of malicious code used by criminal crews to target point-of-sale devices. PoS malware is specifically designed to steal sensitive information stored in the magnetic stripe of a payment card, yet techniques implemented by the malware authors are different and are becoming even more sophisticated. Point-of-sale malware are able to steal data by scraping the memory of the machine or accessing its disk. Since 2013, POS malware is rapidly evolving, and numerous actors in the underground have offered customization for malicious codes widely used worldwide.
The most interesting evolutions for PoS malware are related to evasion techniques and exfiltration methods. Cyber criminals are exploiting new solutions to avoid detection of defensive software.
Malware authors are also looking with great interest to PoS malware botnets that rely on command and control (C&C) servers hidden in the TOR networks.
"We also saw evidence of more authors automating the installation and control of their malware in 2013. While Trustwave discovered a number of new POS malware families exhibiting botnet-like tendencies, a number of well-known, older families also made an appearance," states the post published by Trustwave.
Which are the most popular PoS malware?
Experts at Trustwave revealed that the Alina (19,1) malware family was the most prevalent malware used by threat actors behind the cases investigated by Trustwave. Other malware detected by the investigators were Baggage (16,5%) and Triforce (11,2%), meanwhile the popular BlackPos malware, Dexter and ChewBacca were used in a limited number of attacks, despite that they are considered very sophisticated.
A detailed look to several PoS malware revealed that the Dexter malware is appreciated for the memory dumping ability it implements. Dexter implements process-injection mechanisms and logs keystrokes. Chewbacca is another powerful malware characterized by a sophisticated exfiltration mechanism that relays over the TOR network to host C&C servers.
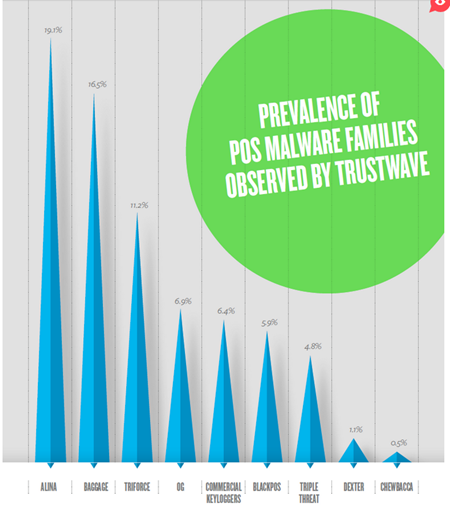
Figure 1 - Trustwave PoS malware families
"Debuting in late 2012, Alina surprised many, because it was one of a small number of POS malware families that included a C&C structure, encrypted the data it exfiltrated, blacklisted common Windows processes and installed itself to a randomly chosen name."
In many cases, criminal crews also used commercial keyloggers to infect the POS systems. A common characteristic for all the malware detected since 2014 is the lack of encryption for exfiltrated data. The "exclusive OR" (XOR) operation is the encryption technique most used by the malware authors (32%), followed by Blowfish (3.7%).
Analyzing the exfiltration methods used by point-of-sale malware, the experts discovered that in the majority of cases (41%) the attackers don't adopt a botnet infrastructure with a classic C&C infrastructure, instead they prefer to leave the stolen data on disk to be extracted manually later. HTTP is the second exfiltration technique (29%), followed by SMTP (22%).
By analyzing the POS malware persistence mechanisms, the experts noticed that they did not change significantly from the past years. The point-of-sale malware use maintained persistence in one of the following ways:
- Run Registry Modification (53.2%)
- Installed as a Service (30.9%)
- AppInitDLLs Registry Modification (0.5%)
- None (14.9%)
The evolution of point-of sale malware – what's new?
The authors of point-of-sale malware are improving their code. Let's analyze together the most interesting code discovered since the report published by Trustwave in 2014.
- Sophisticated method to find card data.
- Self-update ability to execute new code.
- Effective measures to protect its code from analysis.
- The malware belongs to the "scrapers" family.
- Implementation of the Luhn formula to verify card validity.
- Uses a keylogger module.
- Efficient memory scraping process.
- Custom packer and new anti-debugging mechanisms.
- Implements ability to harvest user input.
- To obtain persistence it uses registry entry with the name "Java. Update Manager".
- Disables the warning messages used by the OS.
- Implementation of the Luhn formula to verify card validity.
- Infects Mass Transit Systems.
- Allows remote control of victims.
- Implements functionalities of RAM scrapping and keylogging features.
- Allows loading of additional payloads through "File Upload" option for lateral movement inside the local network.
The PoSeidon malware
Recently, experts at Cisco have discovered a new strain of PoS malware dubbed PoSeidon. The new variant of malware presents many similarities with the popular Zeus trojan and implements sophisticated methods to find card data on the infected machine with respect to other PoS malicious code like BlackPoS, which is the malware that was used to steal data from the US giant retailers Target and Home Depot.
"PoSeidon was professionally written to be quick and evasive with new capabilities not seen in other PoS malware," states the blog post from Cisco's Security Solutions team. "It can communicate directly with C&C servers, self-update to execute new code and has self-protection mechanisms guarding against reverse engineering."
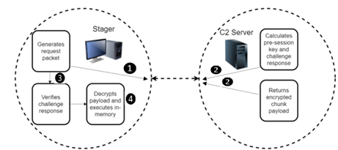
The following image shows the architecture of the PoSeidon malware used by criminal crews to steal credit/debit card data from PoS systems.
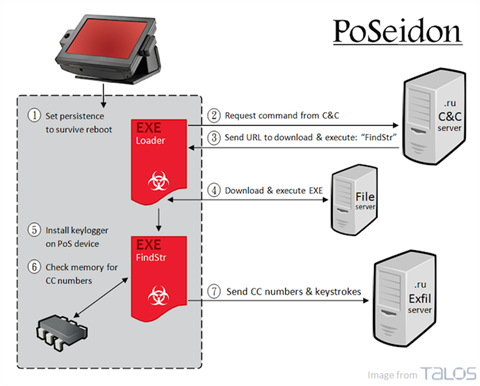
Figure 2 - Poseidon Point of Sale malware (Cisco)
The malicious code belongs to the family of malicious code dubbed "scrapers", which are malware that "scrape" the memory of point-of-sale systems searching for card numbers of principal card issuers (i.e. Visa, MasterCard, AMEX and Discover). PoSeidon has the ability to verify the validity of card numbers by using the Luhn formula.
Once in execution, PoSeidon starts with a loader binary that operates to ensure the persistence on the infected PoS machine, then it receives other components from the C&C servers. Among the binaries downloaded by the loader, there is also a keylogger component used to steal passwords and could have been the initial infection vector, Cisco said.
"The Loader then contacts a command and control server, retrieving a URL which contains another binary to download and execute. The downloaded binary, FindStr, installs a keylogger and scans the memory of the PoS device for number sequences that could be credit card numbers. Upon verifying that the numbers are in fact credit card numbers, keystrokes and credit card numbers are encoded and sent to an exfiltration server," continues Cisco.
The loader contacts one of the hardcoded servers in the following list provided by CISCO experts, the majority of them belonging to Russian domains:
- linturefa.com
- xablopefgr.com
- tabidzuwek.com
- lacdileftre.ru
- tabidzuwek.com
- xablopefgr.com
- lacdileftre.ru
- weksrubaz.ru
- linturefa.ru
- mifastubiv.ru
- xablopefgr.ru
- tabidzuwek.ru
PoSeidon protects exfiltrated data with encryption. The data stolen from the memory of the machine and collected by the keylogger are sent to the C&C in XOR and base64 encoding. The majority of command and control servers identified by the experts are currently hosted on ".ru" domains.
PoSeidon demonstrates the great interest in the criminal underground in PoS systems. Criminal crews are developing sophisticated techniques to compromise these systems.
"Attackers will continue to target PoS systems and employ various obfuscation techniques in an attempt to avoid detection. As long as PoS attacks continue to provide returns, attackers will continue to invest in innovation and development of new malware families. Network administrators will need to remain vigilant and adhere to industry best practices to ensure coverage and protection against advancing malware threats," explained Cisco's Security Solutions team.
NewPosThings malware
Another insidious point-of-sale malware recently improved is NewPosThings. Researchers at Trend Micro in fact have detected a new strain of the malicious code. The new variant of NewPosThings, also known as NewPosThings 3.0, is a 64-bit version of the known agent discovered in 2014 by the experts at Arbor Networks. The researchers at Trend Micro confirmed that the malware had been in development since October 2013, and since then many variants were detected in the wild, including the last version that was specifically designed to compromise 64-bit architectures.
The NewPosThings PoS malware implements an efficient memory scraping process to steal payment card data directly from the memory of the PoS machine. Malware authors implemented a custom packer and new anti-debugging mechanisms and a module to harvest user input.
The NewPosThings variant, coded as TSPY_POSNEWT. SM, installs itself on the victim's machine using different names that appear familiar to the users, including javaj.exe, vchost.exe, dwm.exe, ism.exe and isasss.exe.
As explained by malware experts from Trend Micro, the choice of the name is not casual, but it is the result of an algorithm that calculates based on information related to the infected machine like its name and the volume serial number. NewPosThings uses a registry entry with the name "Java Update Manager" to obtain persistence on the PoS machine.
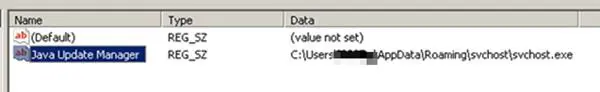
Figure 3 -NewPosThings uses a registry entry with the name "Java Update Manager" to obtain persistence on the PoS machine.
Once it has infected the target, NewPosThings starts gathering sensitive data, including passwords for virtual network computing (VNC) software such as UltraVNC, RealVNC, WinVNC, and TightVNC. Then the malware disables the warning messages used by the OS for certain file extensions, including .exe,.bat,.reg and .vbs. .exe,.bat,.reg and .vbs.
"Disabling the Open File Security Warning of Microsoft Windows reduces the overall security posture of the Microsoft Windows host operating system. This is because the system no longer prompts the user for validation when opening up files that could have been downloaded from malicious sources," states the blog post published by Trend Micro.
NewPosThings checks the presence of financial software on the target machine, and when it recognizes the associated process it searches for patterns that could be associated with credit/debit card numbers, and like other malware, uses the Luhn algorithm to validate the data.
The same algorithm was used for card number validation by recently discovered PoSeidon and Soraya malicious codes. NewPosThings transfers data to the command and control (C&C) server every 10 minutes. The collected data is sent to the server via HTTP.
Among the C&C servers used by the malware authors there are also IP addresses associated with two US airports.
"While analyzing the C&C servers used by the PoS Trojan, experts identified IP addresses associated with two airports in the United States. Trend Micro PoS Trojan, experts identified IP addresses associated with two airports in the United States. Trend Micro warned
that travelers will be increasingly targeted and that airports are a target-rich environment."
Security Experts at Voidsec security firm published an interesting analysis of the malware and its command and control infrastructure.
The experts used data provided by Arbor Networks to locate the Command & Control servers that are still up and running. The experts exploited some vulnerabilities in the C&C servers to analyze their contents.
By analyzing the server, experts from Voidsec discovered the following vulnerabilities:
- Ability to run bruteforce attacks on administrative credentials.
- Presence of the phpMyAdmin application implementing web login.
- Authentication bypass, which gives the attacker the ability to view a protected page on the C2 server without being logged.
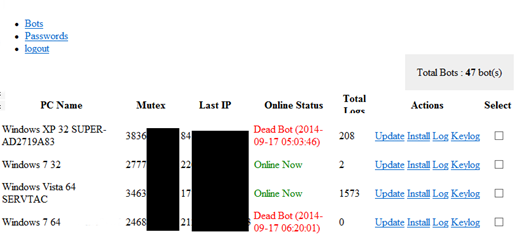
Figure 4 – NewPosThings Command and Control Interface
By accessing data hosted on the compromised Command & Control servers, the researcher profiled the botnet used by the criminal crews:
- The two servers C&C servers analyzed managed a total of 80 bots.
- At the moment the experts logged C2 servers, there were 50 bots active, 10 did not have a status, and 20 bots were "dead."
- The total number of archived log is 5240, an average of 65.5 log / bot.
- 79% of the bots were based on 32-bit architecture, the remaining on 64-bit architecture.
- The majority of compromised bots (57%) were XP machines, followed by Windows 7 (34%).
-
The greatest number of infections was observed in Canada (29%), Australia (21%) and UK (13%).
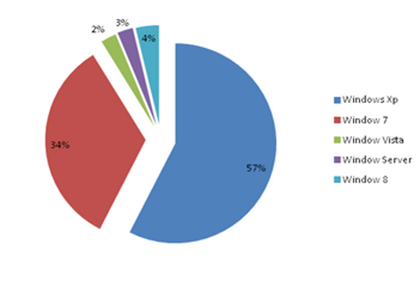
Figure 5 - PoS machine OS (Analysis Voidsec)
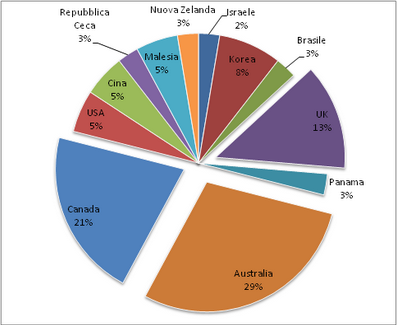
Figure 6 - PoS machine by Country (Analysis Voidsec)
The "d4re|dev1|" PoS malware
The last case I want to discuss is a PoS malware that was detected by security experts at the IntelCrawler cyber threat intelligence firm at the end of 2014. Researchers detected a new point-of-Sale malware called "d4re|dev1|" (read dareldevil), which was used by criminal crews to infect ticket vending machines and electronic kiosks.
In this case, the malware was used to infect Mass Transit Systems. The malicious code appeared as a sophisticated backdoor, which allows remote control of victims. d4re|dev1| implements RAM scraping and keylogging features exactly like any other PoS malware. The experts at IntelCrawler explained that d4re|dev1| is able to steal data from several PoS systems, including QuickBooks Point of Sale Multi-Store, OSIPOS Retail Management System, Harmony WinPOS and Figure Gemini POS.
IntelCrawler discovered that cyber criminals managing the d4re|dev1| botnet also compromised ticket vending machines used by mass transportation systems and electronic kiosks installed in public areas. One of the infected ticket vending machines was identified in August 2014 in Sardinia, Italy, and attackers obtained the access exploiting credentials for a VNC (Virtual Network Computing).
"These kiosks and ticket machines don't usually house large daily lots of money like ATMs, but many have insecure methods of remote administration allowing for infectious payloads and the exfiltration of payment data in an ongoing and undetected scheme," states IntelCrawler.
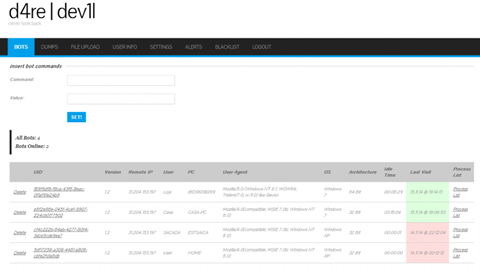
Figure 7 - d4re|dev1| Control panel
In a classic attack scenario, threat actors used to compromise the targeted PoS by discovering the remote administrative credentials, for example through a brute force attack.
Researchers at IntelCrawler believe that attackers use this tactic to compromise the POS systems. Anyway, the d4re|dev1| malware also allows operators to remotely upload files to the victim's machine, and in this way the attacker can provide updates to code or to serve additional payloads for lateral movement inside the local network.
"The malware has a "File Upload" option, which can be used for remote payload updating. The process of malware was masked under "PGTerm.exe" or "hkcmd.exe", as well as legitimate names of software such as Google Chrome. Adversaries use this option for the installation of additional backdoors and tools, which allows them to avoid infrastructure limitations and security policies designed for detection," said InterCrawler.
The "upload feature" is particularly important for cyber criminals. Experts speculate that attackers are interested to compromise systems inside enterprise wide networks to capitalize their efforts with multiple activities inside the targeted infrastructure (i.e. data stealing, botnet recruiting).
"Serious cybercriminals are not interested in just one particular Point-of-Sale terminal—they are looking for enterprise wide network environments, having tens of connected devices accepting payments and returning larger sets of spoils to their C2 [command-and-control] servers," states the blog post published by IntelCrawler.
Conclusions
The number of data breaches is growing at a fast pace, and the retail industry is among the most affected sectors. Security experts sustain that measures to prevent cyber attacks against systems in the retail industry are not adequate, and PoS systems are a privileged target of cyber criminals that are developing new malicious code that presents sophisticated techniques.
In this post, we have analyzed three of the most effective samples of PoS malware recently detected by security firms. They implement a similar feature that makes these malicious codes perfect hacking weapons that in some cases are used to breach the overall infrastructure of the victims.
The experts highlight that the employees of breached companies commonly violated security policies, for example, it is very common that they used the terminals to navigate on the web, check their email, to access social network accounts and play online games. This dangerous behavior must be banned, and it is necessary to instruct personnel on the principal threats and the techniques, tactics, and procedures of the attackers.
It is recommended to use a secure connection for administrative activities and limit the software environment for operators "by using proper access control lists and updated security polices".
References
http://securityaffairs.co/wordpress/28160/malware/point-of-sale-malware.html
https://gsr.trustwave.com/topics/placeholder-topic/point-of-sale-malware/
http://securityaffairs.co/wordpress/35181/cyber-crime/poseidon-pos-malware.html
http://www.arbornetworks.com/asert/2014/09/lets-talk-about-newposthings/
http://securityaffairs.co/wordpress/30570/cyber-crime/pos-malware-dareldevil.html
http://blog.trendmicro.com/trendlabs-security-intelligence/newposthings-has-new-pos-things/
http://voidsec.com/newposthings-hacked-exposed/#server
http://securityaffairs.co/wordpress/30570/cyber-crime/pos-malware-dareldevil.html
https://www.intelcrawler.com/news-24
http://securityaffairs.co/wordpress/30570/cyber-crime/pos-malware-dareldevil.html