Phishing Attacks in the Shipping Industry
Introduction
The good old email is still the cybercriminals’ most preferred avenue for unauthorized access to your technological (and other) assets. As many as 9 out of 10 cyberattacks start with a phishing email. According to a 2016 study by PhishMe, there was an astounding 789 % increase (6.3 million) in the phishing emails in the first quarter of 2016 compared to the same figure in the last quarter of 2015.

Learn Vulnerability Assessments
Typically, a phishing attack is “activated” when a recipient of a phishing email downloads an attached file containing malware or visits a corrupt web page by clicking on a link appearing in the email. In the latter case, he could also be asked to submit sensitive information under whatever pretext upon landing on the corrupt web page.
Phishing attacks are the initial phase of every cyberattack that consists of multiple steps – for instance, theft, ransomware, or spying – through which criminals gain a foothold into a victim’s computer system. The Internet elevated the identity theft to a new heights, heights that stretch beyond most people’s imagination. Cybercrooks could steal usernames and passwords so that they can order goods or use services to send spam emails to unsuspecting customers. The results of a year-long investigation by Google into Gmail account hijacking showed that phishing attacks entail greater dangers to users compared to data breaches, because of the additional information cybercriminals collect and the opportunity for account hijacking.
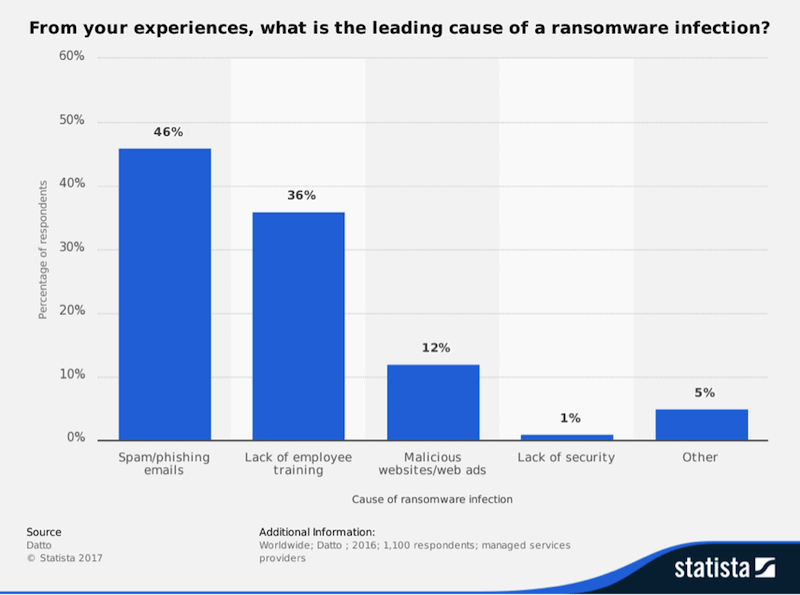
Stolen credit cards and identity theft, however, take more work to monetize, whereas ransomware deliver quicker results by definition; also, ransomware is more or less an “automated” cybercrime and criminals do not need to do much other than sit back and watch the money flow in. Perhaps that is why 93% of all phishing emails in the first three months of 2016 contained encryption ransomware (PhishMe).
This is an article about both phishing attacks that target shipping businesses (e.g., FedEx, UPS, maritime companies, etc.) and phishing attacks directed at customers, purporting to be from legitimate shipping businesses.
A report by KnowBe4 reveals that the five most common email subjects contributing to phishing incidents are:
- Security Alert – 21%
- Revised Vacation & Sick Time Policy – 14%
- UPS Label Delivery 1ZBE312TNY00015011 – 10%
- BREAKING: United Airlines Passenger Dies from Brain Hemorrhage – VIDEO – 10%
- A Delivery Attempt was made – 10%
As you can see, two of them shipping-related.
Why and How are Shipping Companies Phished?
The Business Perspective
Criminals persistently target shipping agents to worm out information. As stated in a report by the marine insurance company Skuld, emails claiming to be from the Suez Canal Authority solicited vessels for detailed and confidential information in 2016. This probe further included a request for the settlement of invoices.
One of the aspects that predisposes shipping companies to cyber attacks in general is the growing complexity of systems of transportation at hand of the shipping industry and their connectivity to services provided by other partners’ networks. As a rule of thumb, stand-alone systems will be less vulnerable to information threats.
Skuld report is eloquent when it comes to information security weak points in the shipping industry:
“As shipowners are under pressure to win new business, many have disregarded due diligence when dealing with new business partners. As both the greater reliance on IT and electronic trading platforms and documents increases, so does the need to stay ahead of the game played by the fraudsters.”
As Skuld warned, phishing scams, even the most innocuous ones, can lead to problems of considerable magnitude, ranging from monetary fraud to theft (ransomware) or hijacking of vessels or crew members. In 2014, the major fuel supplier World Fuel Services (WFS) fell victim to a spear-phishing attack that ultimately cost an estimated $18 million.
Bunkering frauds, cargo and document frauds, chartering frauds and port related frauds are some scams examined in detail, and blackmail frauds, cyber fraud, fake job averts and information phishing are also briefly described in the report.
(Tip: To determine the authenticity of trade documents, shipowners can turn to ICC International Maritime Bureau (IMB))
Moreover, online shipment-tracking tools available to customers can be used by malicious parties as a stepping stone to a cargo management system. 18 of the world’s largest 20 container carriers seems to be vulnerable to “clickjacking” – i.e. setting up a fake version of a legitimate business’s website.
Lars Jensen, CyberKeel chief executive: “There’s not a tool you can put in place to stop people clicking the wrong links.“ The Loadstar
Of course these links leading to the fake version of the carrier’s website arrive into a shipper’s inbox via a phishing mail. Once he enters his username and password (which are surreptitiously recorded), the visitor is redirected to the genuine website where he goes on with activities oblivious to the theft that has just happened.
Israeli cybersecurity and intelligence company Clearsky Cyber Security – a partner of CyberKeel — uncovered a massive phishing campaign designed to impersonate shipping and banking websites, which hit a New Zealand shipping company.
What do cybercriminals do with the freshly obtained user credentials? They use them to gain access the carrier’s valuable assets. Mr Jensen sheds some light on that matter: “Unauthorised access can, at worst, be used to steal detailed shipment information, arrange transportation for illicit cargo, make fraudulent amendments to freight documents and steal the cargo itself.”
IRS scam – The following phishing scheme is executed to steal employees’ tax related information that will, in turn, facilitate identity theft and tax fraud:
This fraudulent activity targets not only shipping companies, but also healthcare organizations, school districts, restaurants, and temporary staffing agencies.
Ransomware – Initially originated from Ukraine, Petya ransomware spread as fast as a plague outbreak around the world via tax and accounting software packages that come with pre-installed malware. One of the first of its high-profile victims was Maersk. Supposedly, Petya went into the local system of the Danish transport & logistic conglomerate through a security vulnerability that was not ‘patched’. Being a worm, this malware has the ability to self-propagate. Maersk reported that the security breach could cost it as much as $300 million in profits. FexEx was another shipping company affected by Petya.
Let us see how the shipping-related phishing looks like from a consumer point of view.
Nowadays people buy more and more goods online, especially during holidays. Unfortunately, email notifications and shipment tracking systems provided by virtually all shipping companies as convenient delivery services to their clients are conveniently repurposed to serve mala fide causes.
Criminals impersonate shipping companies – Bad guys seems to be getting better and better at mimicking logos, trade marks, and the coloring through which shipping companies are known in public, as the Comodo Threat Research Labs team noted.
Shipping notifications, and any other invoice, tax, or e-fax notifications, may be used in phishing emails in order to lure recipients into clicking a link or downloading a file to find out what is the notification about. “USPS Delivery Failure Notification” is an example of such a phishing scam. UPS and FedEx suffer the same fate.
Photo by Luc Legay / CC BY-SA 2.0
Kaspersky Lab detected one scam message in which the user was asked to fill in and sign a delivery form to receive a shipment. Nothing was mentioned, however, about the fact that the attached DOC file contained the exploit Exploit.MSWord.Agent.gg, which allow the email sender to gain remote access to the infected computer, among other things.
In another scam fraudsters inform potential victims that their shipment is already at a given DHL office, but the courier is unable to deliver it due to an “unclear” delivery address. The recipient is offered one quick fix – to follow a link within 48 hours and submit the shipment number on the tracking page; otherwise, the shipment will be returned to the sender /See Tip №6 at the end of this writing/.
None of the links of course led to the original DHL website. Users who follow them are taken to a bogus DHL website, and prompted to enter their login credentials in order to access the shipment tracking system.
Beware of Vishing – USPS staff received phone calls from unknown entities presenting themselves as USPS employees to inquire about customers’ birth data and Social Security number so that they can “confirm a package delivery”.
Steps for Preventing Shipping Phishing
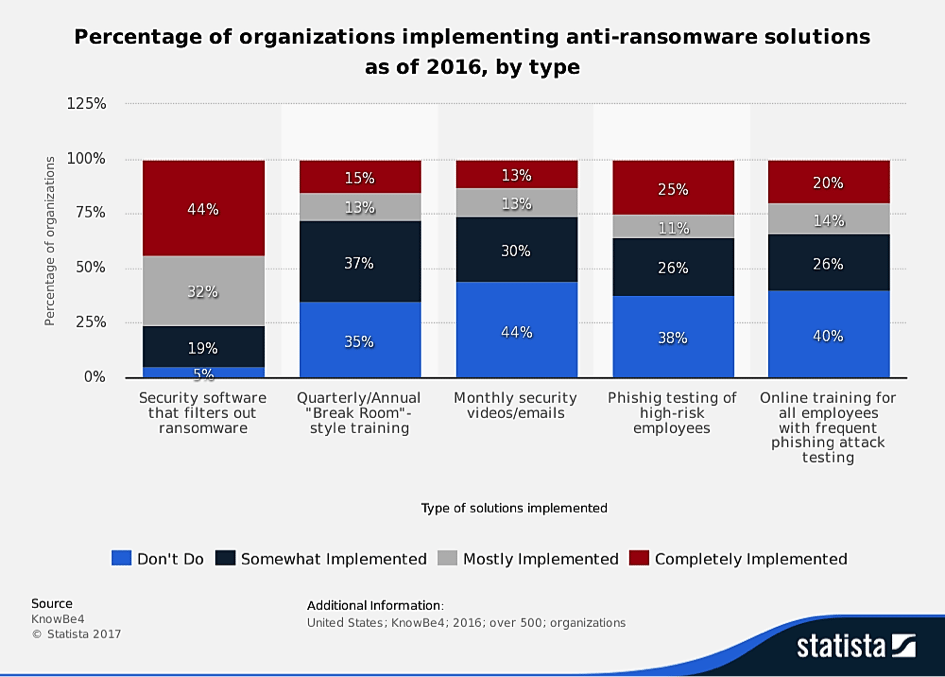
A security expert at the Barracudablog adviced companies to adopt a multi-layered security approach to minimize the threats entailed by phishing and other cyberattacks. It consists of three layers:
1) Sandboxing – the goal is to block any malware before it ever reaches corporate mail servers.
2) Anti-phishing protection – advanced phishing engines block links to compromised websites.
3) Employee training and awareness – regular training is a conditio sine qua non in terms of information security awareness and success rate of averting phishing attempts.
Prevention
Advice for the HR department – ask applicants to submit CVs and resumes through a job board instead of the corporate email. In that way, the submitted documents will be fully viewable through the third party’s platform without needing to download them.
Other measures include blocking executable files and keeping macros disabled by default because innocuous looking Word documents may in fact be executable files.
Tech Solutions
Technology-wise one of the best options to secure your system against phishing campaigns are advanced security solutions. They have the ability to monitor and categorize all ongoing processes and anticipate any malicious behavior in real time.
A router with a subscription service for small businesses and a web security gateway and management products for mid/large business can stop many phishing attacks at the network perimeter by filtering spam emails and bad URLs.
Intrusion Prevention Systems (IPSs) can prevent some forms of phishing, such as “someone trying to intercept a DNS request so that they can impersonate a legitimate site,” explains the network director for 5Nines Data, Anton Kapela. He is also a proponent of the layered security approach.
Jody Cleworth, who is a CEO of Marine Transport International, adduced arguments in favour of the implementation of blockchain technology in the shipping industry:
“The blockchain has proven to be an excellent way of connecting the different parties involved in any supply chain environment due to the transparency and security-by-design of the technology [which are leading principles in the EU General Data Protection Regulation and are among the FTC’s recommended practices for cybersecurity and privacy].”
Training
Why phishing attacks are so dangerous? Simply put because they prey on the human factor, thereby circumventing otherwise expensive hardware/software protective mechanisms. The so-called “Human Element” is obviously still the weakest link in every corporate firewall.
With respect to proper training methods, Gartner’s analysts propose in their report Innovative Insight for Anti-Phishing Behavior Management the following ideas:
“Anti-phishing behavior management solutions are not a tool for initiating cultural change. Assess your organizational culture first, and deploy anti-phishing as part of a comprehensive program of security behavior management and education.”
As far as staff training is concerned, however, simulated phishing campaigns seem to deliver the best results in order to determine which employees need more training. Such extra training could include trackable training modules tied to a learning management system (LMS) and more interactive content like videos, games and tests.
Click the fake UPS email to see examples of Infose IQ's extensive phishing template library
SOFTimpact, a maritime IT service provider, delivers the world’s first dedicated Maritime Phishing Simulator. According to their stats gained through simulations across many companies in the shipping sector, 70% of users opened and 45 % clicked on links or provided credentials. It is a disastrous statistic that illustrates the lack of anti-phishing training among the employees in these companies.
See How Security Awareness Can Prevent a Ransomware Situation
***
FedEx position on the matter of unsolicited emails that prompt users for information is clear: "FedEx does not send unsolicited emails to customers requesting information regarding packages, invoices, account numbers, passwords or personal information.”
***
10 Tips to Avoid Phishing Scams
- Have an antivirus program in place.
- Keep your software up to date.
- Browse only through secure websites (i.e. the ones starting with ‘https://’).
- Be suspicious of every entity asking you to provide personally identifiable information (PII), financial information, account information (such as passwords), IDs, copies of invoices irrespective of whether it is through email, standard mail, or phone.
- Security policies and procedures should govern comprehensively the handling of PII, including strict rules under which is to be sent. Some measure that could ensure information safety are encryption of PII and making a confirmation phone call to a person in charge prior to hitting the ‘Send’ button.
- Be careful when the email tries to create a sense of urgency – it may be a tactic to panic and confuse you even more.
- Do not click a link in a shipping notification. Instead copy/paste the tracking number directly into the shipping company’s website or type URLs directly in your browser address bar instead.
- Check the formatting and contents – the footer of real emails contains an address and privacy policy information. Does the spelling look fine? Is the written delivered in a vague fashion?
- As Mr Jensen advised with regard to clickjacking prevention, frame breaking functionality, among other slight technical changes in the genuine website setup, could potentially prevent fraudsters from framing the said website.
- Repeat unexpected simulated phishing attacks regularly to keep your team vigilant.
Reference List
Cisco. What Is Phishing? Accessed at https://www.cisco.com/c/en/us/products/security/email-security/what-is-phishing.html (19/11/2017)
Cidon, A. (2017). Threat Spotlight: The airline phishing attack. Accessed at https://blog.barracuda.com/2017/03/30/threat-spotlight-the-airline-phishing-attack/ (19/11/2017)
Channelnewsasia (2017). Beware of phishing emails from fake courier companies: SingCERT. Accessed at http://www.channelnewsasia.com/news/singapore/beware-of-phishing-emails-from-fake-courier-companies-singcert-8975302 (19/11/2017)
Green, E. (2017). Phishing Scam Targets Human Resources and Payroll Departments. Accessed at https://www.lexology.com/library/detail.aspx?g=bd94ab2d-a964-458f-86e3-27b27090ede9 (19/11/2017)
ICC Commercial Crime Services. Report warns shipping of phishing scams. Accessed at https://www.icc-ccs.org/news/931-report-warns-shipping-of-phishing-scams (19/11/2017)
Kaspersky Lab (2016). Spear phishing attack hits industrial companies. Accessed at https://ics-cert.kaspersky.com/alerts/2016/12/16/spear-phishing-attack-hits-industrial-companies/ (19/11/2017)
Kostin, A. (2015). Tis the season for shipping and phishing. Accessed at https://securelist.com/tis-the-season-for-shipping-and-phishing/73174/ (19/11/2017)
Korolov, M. (2016). 93% of phishing emails are now ransomware. Accessed at https://www.csoonline.com/article/3077434/security/93-of-phishing-emails-are-now-ransomware.html (19/11/2017)
MarEx (2016).Shipping Industry's Own Cyber Security Guidelines Released. Accessed at https://www.maritime-executive.com/article/shipping-industrys-own-cyber-security-guidelines-released (19/11/2017)
Networks Asia staff (2017). Phishing attacks against shipping and cloud storage companies rose in H1 2017. Accessed at https://www.networksasia.net/article/phishing-attacks-against-shipping-and-cloud-storage-companies-rose-h1-2017.1508814675 (19/11/2017)
PandaSecurity, (2017). Top 10 Email Subjects for Company Phishing Attacks. Accessed at https://www.pandasecurity.com/mediacenter/security/top-10-email-subjects-phishing-attacks/ (19/11/2017)
Palmetto Technology Group (2017). Four Types of Phishing Emails Targeting Businesses. Accessed at http://blog.goptg.com/four-types-of-phishing-emails-targeting-businesses (19/11/2017)
Pickard-Whitehead, G. (2017). 10 Phishing Examples in 2017 that Targeted Small Business. Accessed at https://smallbiztrends.com/2017/08/phishing-examples-small-business.html (19/11/2017)
Prakash, R. (2017). Phishing In All Its Forms Is a Menace to Small Businesses. Accessed at https://www.entrepreneur.com/article/295793 (19/11/2017)
Sadler, A. (2016). Warning: Fake package notification could be dangerous malware. Accessed at http://clark.com/scams-rip-offs/warning-about-fake-package-delivery-email-scam/ (19/11/2017)

Learn Python for Pentesting
SCmagazine (2016). New phishing scam targets FedEx customers. Accessed at https://www.scmagazine.com/new-phishing-scam-targets-fedex-customers/article/529027/ (19/11/2017)