Phishing: Denial of Service (DoS) Implications
A denial of service attack can be bewildering to victims. It’s like an ambush of boy scouts by a team of fully armed United States Marines. Incidents of these malicious cyber-attacks are increasingly in the news and have far-reaching implications for small businesses and large corporations that we’ll address in this article, but first let’s set the scene by taking a look at what DoS and DDoS attacks are, why attackers do it, and how. There is, incidentally, no profile for the typical DoS or DDoS victim; everyone is at risk, which we’ll illustrate with a few examples from headline-making news stories.

Implementing HIPAA Controls
The theme of this article is that much more needs to be done by businesses to defend against these attacks. To go back to the simile of the boy scouts and the marines: It’s not enough to wail about the unjustness of it, digital business boy scouts need to arm up. Denial of service is as much a threat to a mom-and-pop outfit from a rival who hires cyber-criminals to launch an attack on their online cookie biscuit business, as it is to a multi-national financial institution that faces the loss of potentially millions of dollars if their site is down, vulnerability to extortion, data losses, threats of lawsuits and reputation damage.
As we’ll see, there’s a reason denial of service attacks are referred to in military terms: To lay people reading the technology section of their local newspapers, it sounds like an Internet war, and the bad guys are winning.
What Are DoS and DDoS Attacks?
- A Denial of Service (DoS) attack attempts to make a machine, network resource, or website unavailable to users usually by flooding (overloading) it with more requests than it can handle and/ or impairing it in some way, e.g., weakening it enough in order to breach some other security vulnerability or limitation. In other words, sometimes it is used as a smokescreen. During the attack, regular traffic will be either slowed down or completely suspended. A DoS attack typically uses one computer and one internet connection to flood the target.
- A Distributed Denial of Service (DDoS) attack uses multiple computers and Internet connections to flood a targeted resource. An attack is usually generated using thousands of unsuspecting zombie machines, collectively known as botnets. DDoS attacks are arguably the biggest cyber-security threat to web-based businesses today. To give you an idea of the significance of the threat, according to Akamai’s 2016 State of the Internet Security report, the total number of DDoS attacks recorded over its content delivery network increased by 125.36% year-on-year from the same period in 2015.
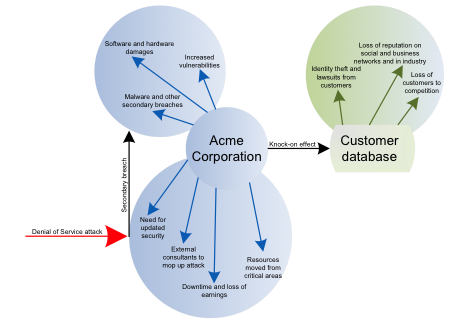
In both cases, it’s a case of "closed for business," as the network is bottlenecked and the company’s servers attempt to secure the perimeter, fight the fires already started, and at the same time reassure customers and try to secure their data. The consequence is that security in areas other than those initially targeted is weakened and open to attack by other malicious techniques. For cyber-criminals, attack is a multi-pronged approach and for businesses it is becoming increasingly difficult, or at least expensive, to protect themselves on all flanks.
Who Gets Attacked?
DoS and DDoS attacks are a deadly new weapon for political activists, cyber-thieves, internet bullies, unscrupulous Internet businesses, and extortionists. They are launched with military precision, often anonymously, and with widely different motives for the attacks. The short answer to the question of who gets attacked is anyone, as the fallout is often felt by thousands of users who become victims indirectly. For instance, an attack on a financial institution to extort money from them could lead to the identify theft of the institution’s customers.
However, certain industries have been identified as prime targets. According to security experts Kapersky, finance, telco, and IT sectors were the most common targets for DDoS attacks in 2015. But Computerworld notes that smaller companies' websites are increasingly at risk due to the rising popularity of DDoS-for-hire services. These services may be likened to hiring a hit man to break your competitor’s legs before a big race.
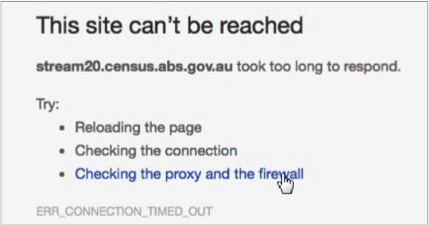
Any site that cannot handle the number of visits it receives is at risk; i.e., where, in a nutshell, demand (traffic) exceeds supply (bandwidth). Gaming, gambling, media, entertainment, political, and even non-profit websites have all been victims. An interesting question that arose recently after a purported attack on the Australian Bureau of Standards websites, is: Was this a DoS attack or did the system simply fail internally? Interesting, because this could provide alleged victims with a reason for poor security measures.
What Strategies Do DoS and DDoS Attacks Use?
- Disable a service, network or computer(s).
- Infiltrate multiple devices, like cell phones, printers, alarms and mobile devices via company networks.
- Compromise system resources like bandwidth, databases, processors and software processes.
- Illegally install and execute
- Exploit known system vulnerabilities including those in security software and hardware, browsers and popular internet applications, e.g., Facebook and free email services, as well as custom applications.
- Take advantage of loopholes in software that is old or that has not been kept updated (although not a DoS attack, this was how the Panama Papers debacle came about).
- Attack unrelentingly, often from more than one angle, resulting in a system’s shutdown.
Why Do Attackers Do It?
- Blackmail or extortion: Extort money from companies that rely on their websites being accessible 24/7. Financial institutions are prime targets but gambling websites and IT security companies are favored victims too, often having to deal with ransom demands to keep their sites up and running.
- Business rivalry and/or turf wars: Cripple business rivals by shutting down their businesses. Unscrupulous businesses have been known to pay for their rivals to be constantly attacked, ultimately hindering day-to-day operations and encouraging customers to find alternative providers. This motive has led to an increase in the demand for DDoS-for-hire services, as mentioned above, a new and profitable service provided by cyber-criminals to attack businesses’ competitors, for a price. The past few years have seen a rapid increase in these cheap, web-based services, called booters or stressers.
- Financial motives: DoS and DDoS attacks may hide another, more insidious, attack on a company, where attackers first break down a company’s security defenses and then perform other breaches with a view to stealing from it. Alternatively, it may use attacks to disrupt normal routines and take the opportunity to phish users by luring them to imitations of the websites whose operations have been temporarily suspended so that they can attack them and steal their identities.
- Revenge, expressions of anger, punishment and protest: Fight personal or group wars, protest against political policies, voice social or community grievances or demonstrate solidarity with illegal or unpopular groups.
- Training for hackers and phishers: DoS and DDoS attacks offer phishers and hackers an opportunity to train members of phishing groups.
- Pure maliciousness: For the cyber-psychopath, DoS and DDoS attacks are what more mundane hobbies, like reading, camping and football, to the rest of us.
Examples of Some Attack Motivations
Nobody is immune to DoS or DDoS attacks and anybody with the means can perpetrate them.
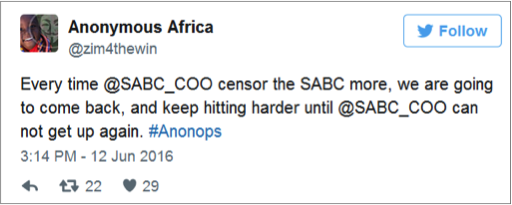
- Protest: In June this year, the hackivist group Anonymous Africa (AA) launched two DDoS attacks on South Africa’s national television broadcasting corporation (the SABC) in protest against the suspension by the broadcaster of journalists who disagreed with changes in reporting policies that amounted to widely creeping censorship. The same month saw a number of other DoS attacks on South Africa websites, including one by AA on the Economic Freedom Front (EFF) website.
- Extortion: The following month, July, saw a near record-breaking 470 gigabits per second (Gbps) DDoS attack on a Chinese gambling website. Described as one of the largest ever staged, the assault pummeled the gambling servers for more than four hours. To put this attack into perspective, an attack of 1 Gbps can create disruptions for a website business; 470 Gbps is practically overkill. Gambling companies are attractive game for DDoS attacks with the intention by the attackers of getting the companies to pay ransoms to stop the attacks.
- Training: Again in July, the Bank of Finland was attacked: "It was a traditional denial-of-service attack that involved directing too much traffic to the site,” said the Bank of Finland’s IT expert Petteri Vuolasto.
- Grievance: Online gamers were targeted in August when Hackers took down Overwatch and other Blizzard games, apparently in retaliation for the company’s banning of alleged cheaters, although other sources claim the attack was simply a “prank.” If the latter, let’s file this one under "malicious"; it’s not nice to spoil other people’s fun for your own amusement.
We Don’t Like to Blame the Victims, but ....
The danger from these attacks cannot be blamed only on seemingly technologically super-knowledgeable, incredibly sophisticated cyber-criminals, but also on inadequate security measures taken by victims. Interestingly, not all DoS and DDoS attacks are especially clever attacks; in some instances, the failure by victims properly to secure servers has arguably given hackers more opportunities than they should have.
- Inadequate firewalls: Some of the U.S. Library of Congress's websites were inaccessible as the result of a denial-of-service attack, the Library reported in July. The attack also caused other websites hosted by the LOC, including the U.S. Copyright Office, to go down. According to the Fedscoop website, “In June 2015, the Government Accountability Office published a limited-distribution report — undisclosed publicly though it was sourced in a 2015 GAO testimony to the Committee on House Administration — highlighting digital security deficiencies apparent at the Library of Congress, including poor software patch management and firewall protections.”
- Inadequate load testing: In August, The Australian Bureau of Standards (ABS) census website crashed, causing chaos on Australia’s census day. Experts immediately diagnosed a DDoS; apparently the site had been tested to 150% of the day’s expected usage and it really shouldn’t have crashed. However, according to Theconversation, “(The claim that the website would be able to handle 1 million form submissions every hour) sounds impressive but it actually equates to only 277 a second. When nearly 11 million people are accessing the site at roughly the same time, this would actually be a very small number.” The worst of it was that the ABS had spent an inordinate amount of time before the big day to convince a skeptical Australian public their data was safe. Later reports suggested that the website was simply unprepared for the volume of traffic it had received.
Business impacts
A 2012 Ponemon Institute study identified DoS and DDoS attacks as the highest cyber-security threats according to risk mitigation priorities and these threats are increasing. How does this impact a company’s bottom line?
- Loss of intellectual property/trade secrets/data theft: The motivation for and techniques used in DoS attacks have changed. Initially the attacks were primarily about revenge and ransom but, according to Andy Shoemaker, who runs Nimbus DDoS, increasingly attackers are using denial of service as a way to distract IT administrators from the real attack, which is trying to steal data.
- Damage to reputation and brand: Often customers will decide to switch to a rival business because they believe their current provider can’t guarantee security and privacy, and because they can’t afford to pay for a service that isn’t available 24/7.
- Cost of downtime and decline in productivity: A denial of service attack means that resources have to be channeled from other areas which may then struggle to perform their own tasks efficiently, leaving other areas in the company at risk of attack.
- Infiltration of spyware and installation of malware: A DoS or DDoS attack, as we have seen, may only be the first attack wave. Undetected malware on the network could cause further disruptions down the line.
- Lost revenue: Commonly reported during the tidal wave of DDoS attacks that targeted Yahoo and Amazon in 2000 was the estimated cost of over $1.2 billion in damages. Clearly, avoiding attacks is more cost-effective than paying the costs of repairing the stable door. A 2014 Incapsula report estimated the hourly cost of a successful DDoS attack at $40,000.
- Damaged equipment and cost of replacement or repair: This may include the cost of updating software or installing new software.
- Cost of external consultants or expert advice: Lawyers, risk management consultants, corporate image consultants, auditors, and IT security consultants may all have to be outsourced to combat an attack or mop up after one.
- Increased vulnerability to new attacks: The battering by DoS attacks on a company’s security infrastructure may prevent the logging of other security events and even force the network, simply because there are no resources to scan it, to allow all data through, even malicious data, unchecked. The calculated strategy by attackers to ensure there is enough bandwidth available for new attacks to assault a weakened network enable multiple attacks on the same company and with each attack the offensive position is strengthened.
- Regulatory actions or lawsuits: If customers' reputations have been damaged, their data compromised or their money lost, they may sue.
- Loss of staff morale: Employees may blame their employee for sub-standard security and feel their personal information is also at risk.
Types of Attacks
There are three main types of attacks.
Volumetric attacks: In these attacks, the goal is to flood the server with responses. Example: User datagram protocol (UDP) is a session-less working protocol. In a UDP flood attack, random ports on the target machine are flooded with packets that cause it to keep listening for, and trying to respond to, non-existent applications on those ports.
Application layer attacks: These attacks target specific applications on a server, e.g., WordPress or email applications. They target web application packets in order to disrupt the transmission of data between hosts. Example: an HTTP flood attack uses multiple infected machines to force a target to expend an excessive amount of resources when responding to a HTTP request.
State-exhaustion attacks: These attacks target the connection state tables in firewalls, web application servers, and other infrastructure components. Example: In buffer overflow attacks, the attacker sends more traffic to a network address than the network’s data buffers can handle. Often the attacker may be aware that the target system has a weakness that can be exploited. Techniques used include:
- Sending e-mail messages that have attachments with 256-character file names to mail programs.
- Sending oversized internet control message protocol (ICMP) packets to the server. This technique is known as the packet internet or inter-network groper (PING) of death.
Conclusion
Cyber-crime has one primary feature that can be counted on: It is in a permanent state of change. Criminals constantly take advantage of new technologies and trends. 2016 has seen an increase in denial of service attacks and if businesses don’t secure their servers now and educate themselves instead of leaving the problem to security experts, they’ll have increasing difficult warding off future threats and security will the biggest bill they face in the coming years. One of the most pertinent lessons that can be learned from the past is that denial of service attacks have a knock-on effect and are often precursors to other forms of attack.
Head DoS attacks off at the pass. Infosec Institute offers a number of free anti-DoS attacking tools here: https://resources.infosecinstitute.com/dos-attacks-free-dos-attacking-tools/.
Sources consulted
http://www.security-faqs.com/dos-vs-ddos-what-is-the-difference.html
http://searchsoftwarequality.techtarget.com/definition/denial-of-service
http://memeburn.com/2016/06/sabc-suffers-weekend-cyber-attack-anonymous-africa/
http://mybroadband.co.za/news/security/168353-anonymous-takes-down-eff-website.html
http://www.theregister.co.uk/2016/06/27/world_of_the_dark_ddos/
https://arc.applause.com/2016/06/21/akamai-ddos-attacks/
http://thevine.com.au/news/census-website-crashed-malicious-attack/

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
https://www.rivalhost.com/12-types-of-ddos-attacks-used-by-hackers/