Amazon Phishing Template: Example and Preventing Attack
What to do if you’ve clicked on an Amazon Phishing Email
Amazon is the world's largest online retailer and a prominent cloud services provider. Despite being often maligned for its supposed inability to make money compared to tech giants like Google, it still made a $92 million profit in the first quarter of 2017. The company has approximately 66 million paying Prime members (and that excludes active accounts which are for customers who have made at least one purchase in the previous 12 months) and attracts millions more to its website every month. For cyber fraudsters, every day is the perfect day to go phishing because the Amazon phish tank is always full.

Learn Threat Modeling
What’s in a name?
Cyber criminals love to disguise themselves as Fortune 500 companies because people generally trust big name brands. Someone is far more likely to respond to or click on a link in an email purportedly from a company like Amazon than from a company called BigJHopLa09. Like all popular online brands, Amazon has had its share of scams, breaches and a phenomenal increase in scam sellers (where criminals hijack legitimate Amazon third party vendor accounts.)
Interestingly, the increase in scam sellers can be partially attributed to a previous Yahoo data breach. In August 2016, 200 million Yahoo users were hacked and stolen user credentials sold on the dark web. Some of these credentials were then used by fraudsters to take over the accounts of Amazon sellers. The problem is that many people tend to use the same password, or variations on it, for multiple sites, so, after identifying people affiliated with Amazon in their lists of stolen Yahoo user data, criminals could sometimes strike lucky and use the Yahoo password they had stolen to access the user’s Amazon account.
Spot the difference
Some of the ways you can spot a fraudulent Amazon email:
- Links to fake sites, for instance account-amazon.com. Amazon will also never send emails with links to an IP address like: “http://113.540.022.453/amazon.co.uk/”.
- Emails containing typos.
- Requests for you to reveal confidential information. If you are asked to do so, go directly to the official Amazon website and never click on a link (hovering over links will reveal the real destination.)
- Requests to update payment and account information.
- An order confirmation for an item you didn't purchase or an attachment to confirm an order.
You can make all changes to your Amazon account by going to your account on the official website; never by clicking on email links or downloading attachments.
Psychological warfare
A Sendlane blog on marketing tactics and human psychology makes for interesting reading if you substitute “marketing “with “social engineering.” With no due disrespect to Sendlane, their “Magnificent Seven Triggers for Email Marketers” could be re-titled: “Magnificent Seven Triggers for Email Phishers.”
Some marketing tactics from Sendlane and some illustrative fake email examples for different psychological triggers:
- Urgency (Fear) - By building a sense of urgency, it becomes infinitely more difficult for your prospects to simply walk away from your messages – “Your Amazon account has been compromised! Please click the link to reset your password immediately.”
- Exclusivity (Pride) - Exclusivity is a powerful trigger that essentially gives your reader the impression they they’re getting special access – “Amazon has partnered with Google to bring you, our most valued customer, an EXCLUSIVE special deal. Please log in with your Gmail account to claim before stocks run out.”
- Social proof (Authority) - Provide evidence that you’re the real deal versus a disposable company – “Amazon has posted record results this quarter. We appreciate your input to help make our service even better. Please click on the link to provide us with your valuable feedback.”
- Storytelling (Trust) – Be honest and “real” with your readers - “You may have heard some deplorable news stories about recent Amazon scams in which valued customers have been duped into buying nonexistent goods. We are sad and angry for the victims. At Amazon we will always refund your money if you are not completely satisfied with our service. Please download our Guarantee Policy (attached).”
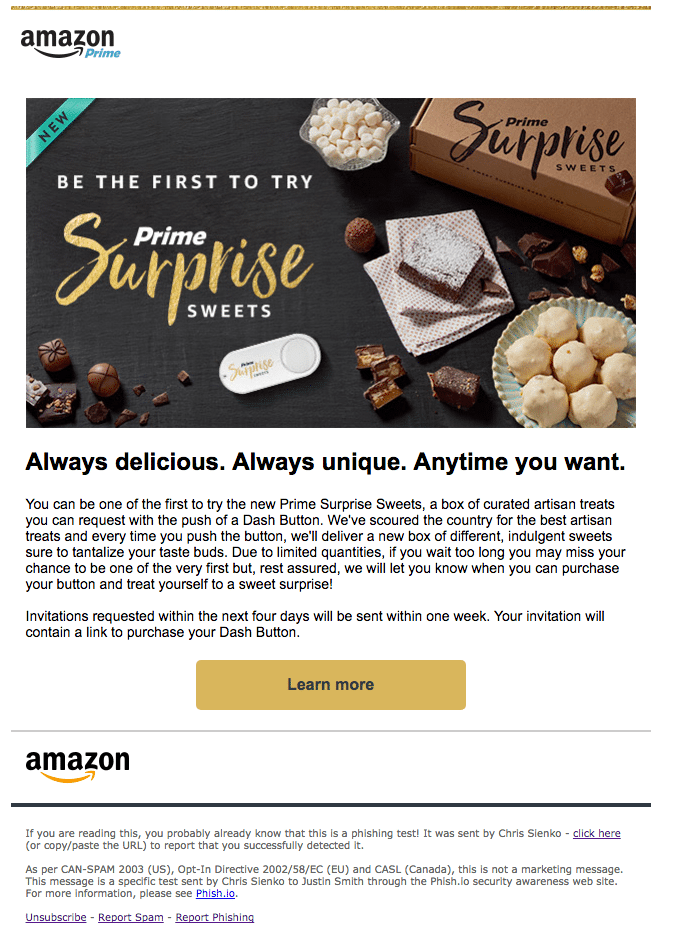
- Newness (Curiosity) - Presenting readers with the inside scoop will almost always grab their attention – “As one of our most valued customers, we’re offering you the exclusive opportunity to be the first to hear our news and take advantage of the most incredible Closing Down Sale you’ll ever attend. Click the link for details.”
- Bargain (Greed) - Nobody can resist a steep deal – “It’s the season to be silly! The new iPhone will be shipping in three weeks. Until then, purchase ANY of the earlier models at HALF the recommended retail price. While stocks last. Please click here to get your new phone NOW!”
- Simplicity (Exhaustion) - Chances are, your readers are already feeling bogged down by their inboxes – “Click hear to stop receiving marketing messages from Amazon.”

Learn Python for Cybersecurity
Security awareness training can help people understand the psychological triggers behind phishing scams: that phishing is not a scary geek concept; that it is not too difficult to learn how to avoid becoming another casualty of cyber crime; and that the psychology behind phishing is not too different from that behind legitimate marketing and sales techniques. A great way to learn is using InfoSec Institute’s PhishSim, an amusing phishing simulation tool you can safely use to learn more about phishing, and educate your friends, family and colleagues.