Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Cybersecurity Weekly: REvil decryptor, AT&T loses millions, OMIGOD flaw

ISACA CDPSE domain 1: Privacy governance

Cybersecurity Weekly: Cobalt Strike beacon, REvil is back, IT training pitfalls
The real dangers of vulnerable IoT devices
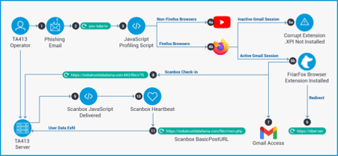
How criminals leverage a Firefox fake extension to target Gmail accounts

What to expect during your CMMC assessment

How cross-site scripting attacks work: Examples and video walkthrough

Python for active defense: Monitoring

ISC2 CSSLP job titles and career outlook
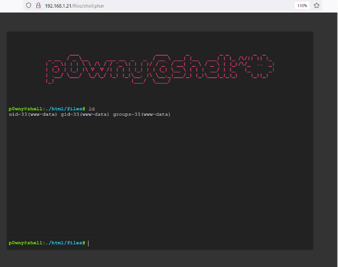
HACKSUDO: PROXIMACENTAURI VulnHub CTF Walkthrough, Part 1

Red teaming: Is it the career for you?

Python for active defense: Network
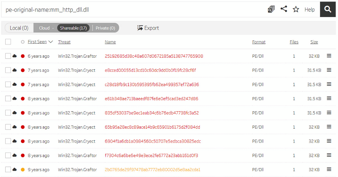
Taidoor malware: what it is, how it works and how to prevent it | malware spotlight

ISC2 CSSLP exam details and process

Cybersecurity Weekly: Fake NFT scam, Atlassian flaw, security analyst interview questions

iOS forensics

Python for active defense: Decoys

Tutorial: How to exfiltrate or execute files in compromised machines with DNS

Cyber risks of digitizing legacy systems in healthcare environments
VULNCMS: 1 VulnHub CTF walkthrough part 2

ISC2 CSSLP domain 8: Secure software supply chain

Incident responder careers: What’s it like to work in incident response?

Cybersecurity Weekly: Phishing attacks using redirects, intermittent file encryption, Ragnarok shuts doors
SUNBURST backdoor malware: What it is, how it works, and how to prevent it | Malware spotlight