Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

CompTIA Cloud+ Certification: An Overview [updated 2021]
NASEF1: LOCATING TARGET VulnHub CTF Walkthrough

Operation technology sees rise in targeted remote access Trojans and ransomware

How to learn Linux: Bring your passion, Jasmine Jackson will do the rest

How gamification boosts security awareness training effectiveness

Average Project Manager Salary in 2021

Vehicle hacking: A history of connected car vulnerabilities and exploits

REvil ransomware: Lessons learned from a major supply chain attack

Cloud security engineer: Is it the career for you?

HACKSUDO: PROXIMACENTAURI VulnHub CTF Walkthrough, Part 2

FLoC delayed: what does this mean for security and privacy?

How to start learning cybersecurity? Take this free foundations course!
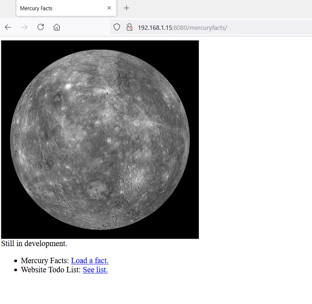
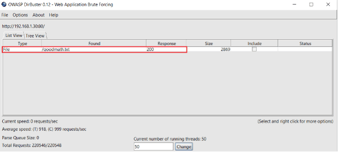
THE PLANETS: MERCURY VulnHub CTF Walkthrough

CertNexus CyberSec First Responder: Certification, exam and training details

CertNexus Certified IoT Security Practitioner: Certification, exam and training details
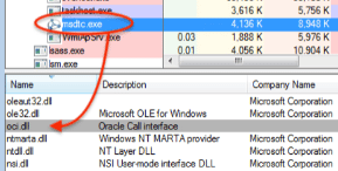
Pingback malware: How it works and how to prevent it
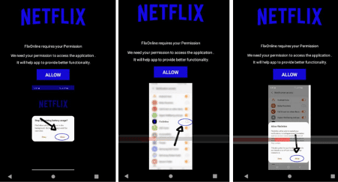
Android malware worm auto-spreads via WhatsApp messages

The state of BEC in 2021 (and beyond)

Data governance: Is it the career for you?

Stolen company credentials used within hours, study says

How to map MITRE ATT&CK against security controls
Malware analysis: Ragnarok ransomware

ISACA CDPSE domain 3: Data lifecycle
How to carry out a watering hole attack: Examples and video walkthrough