Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Web application testing with Arachni

Creepy, the geolocation information aggregator

IT auditing and controls – Auditing organizations, frameworks and standards

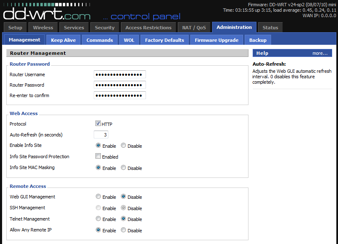
The Case of the Great Router Robbery

IT auditing and controls - An introduction
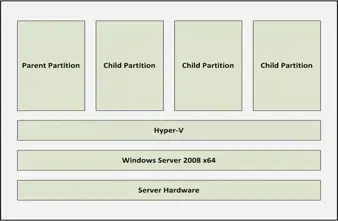
Microsoft Virtual Server Security: 10 Tips and Settings

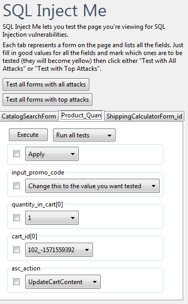
SQL Injection – Another hacking how-to

Grep Essentials
OWASP Top 10 Deeper Dive – A5: Cross-Site Request Forgery (CSRF)

Computer Forensics: Snort Logs Analysis
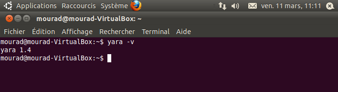
Malware Analysis: Classifying with ClamAV and YARA

CISA Domain 5 – Protection of Information Assets

How to Learn the IT Skills of a Security Professional

CISA Domain 2 – Governance and Management of IT
OWASP top 10 tools and tactics

Standards for Penetration Testing

CISSP Domain - Business Continuity and Disaster Recovery
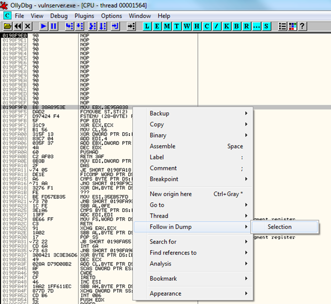
Stack Based Buffer Overflow Tutorial, part 3 - Adding shellcode
Stack Based Buffer Overflow Tutorial, part 2 - Exploiting the stack overflow
Stack based buffer overflow tutorial, part 1 - Introduction

CISSP Domain - Information Security Governance and Risk Management

An introduction to fuzzing: using fuzzers (SPIKE) to find vulnerabilities

Security Incident Response Testing To Meet Audit Requirements

The Device Driver Process Injection Rootkit