Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Building and Testing Your Own VPN

Launching Shellcode from Cat Pictures
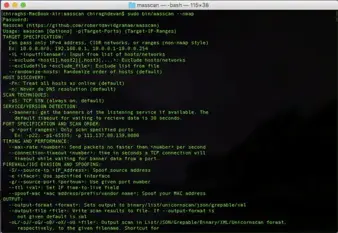
MASSCAN – Scan the internet in minutes

Mobile, Smartphone & BYOD
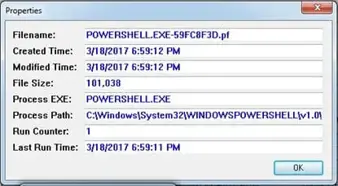
More PowerShell Remoting Artifacts
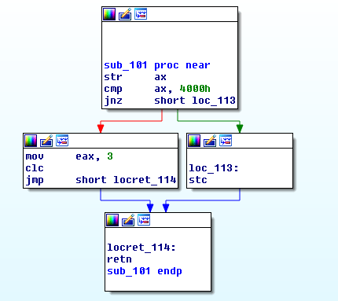
Avatar Rootkit: Deeper Dropper Analysis
Advanced Technical Review of VPN Infrastructure Impacts
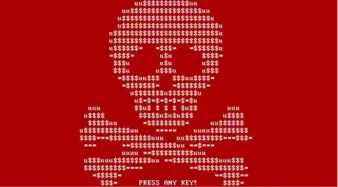
RanRan and PetrWrap Threats: Political and Criminal Abuses in the Ransomware Landscape

RIPS – Finding vulnerabilities in PHP application
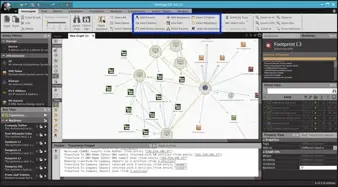
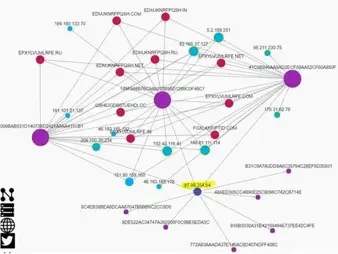
Maltego: Making sense of data
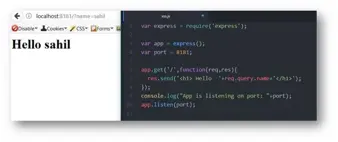
Code Review of Node.Js Applications: Uncommon Flaws
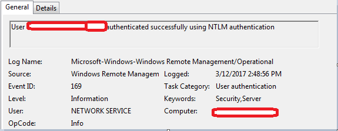
PowerShell remoting artifacts: An introduction
Ursnif Malware

WikiLeaks Vault 7 Data Leak: Another Earthquake in the Intelligence Community
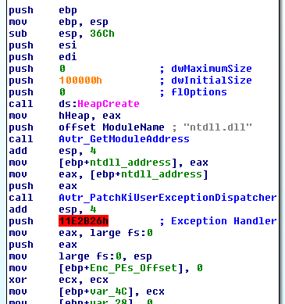
Avatar Rootkit: Dropper Analysis
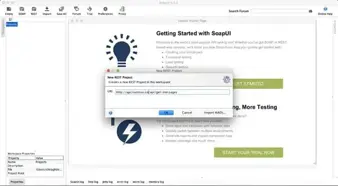
SoapUI: Security Testing
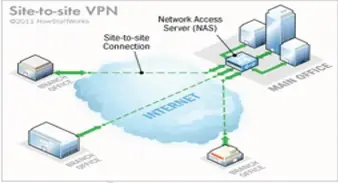
The Security Policy and Network Requirements of a Virtual Private Network
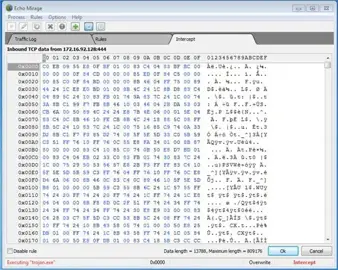
Echo Mirage: Walkthrough
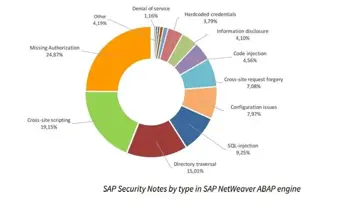
SAP ABAP Platform Security

Exclusive – A Close Look at the Largest Credential Harvesting Campaign Via an IoT Botnet

Top Firewall for Differently Populated Enterprises
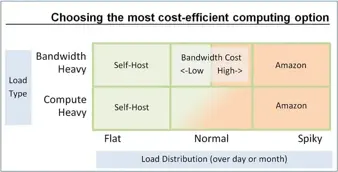
How to Conduct a Cost-Benefit Analysis and Implement a Virtual Private Network

Creating Effective Phishing Landing Pages

An Insight into Virtual Private Networks and IP Tunneling