Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Insurance Against Ransomware Threats
Patching by Reversing Binary

SAP Risks - Fraud

Past and Present Iran-linked Cyber-Espionage Operations

How Security Awareness Training Can Prevent a Ransomware Situation
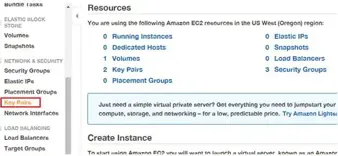
Configuring Kali Linux on AWS for FREE to get the Public IP

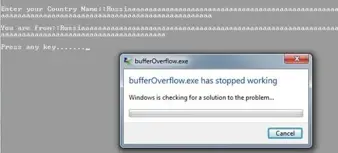
Malware Analysis with OllyDbg

How to prevent access control attacks
Static Analysis

Network security policy
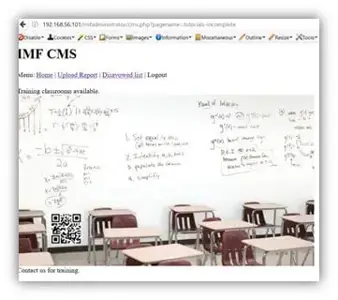
Hacking IMF – CTFh

SAP Risks: Sabotage

Breaking into Fortress DC416 – CTFha

Freedom Hosting II Hacked: 10,613 .onion Sites are Down

Mathematical algorithms of asymmetric cryptography and an introduction to public key infrastructure

Security Awareness

How Healthy is Security Across Healthcare?
Shamoon Reloaded: the Mysterious Return of the Dreaded Wiper
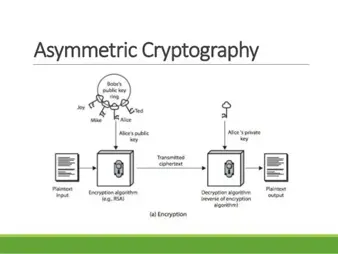
A Review of Asymmetric Cryptography
Code Analysis

Which Cloud Certifications are Important for 2018?

Penetration Testing from Amazon Cloud

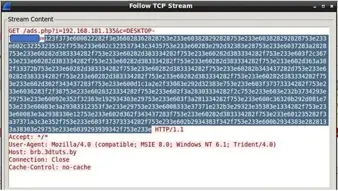
Process: gaining and elevating access
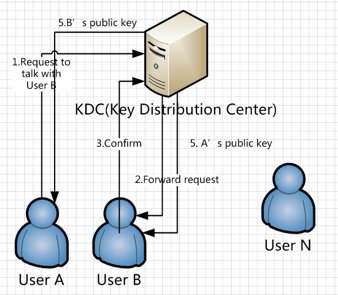
An introduction to the key distribution center, mathematical algorithms, and the hashing function