Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
Running Metasploitable2 on virtualBox

Botnets, how do they work? Architectures and case studies – Part 2

Snort Rule Writing for the IT Professional: Part 3

Software Patent Law: EU, New Zealand, and the US compared

Massive Vulnerability CVE-2013-0027 Owns/Strikes Internet Explorer 6 to 10
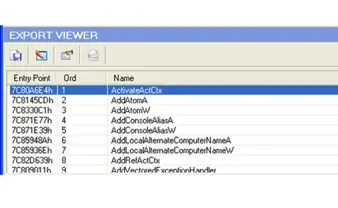
The export directory

Phishing and social engineering techniques

Android Forensics

.NET Framework CLR: Common Language Runtime

Risks of using a shared hosting server

An Introduction to Returned-Oriented Programming (Linux)

Embedding Security in Procurement Process & Vendor Contracts – Part 2

DDoS Attack on Spamhaus – An insight

Code Access Security (CAS)

Loading the Windows Kernel Driver
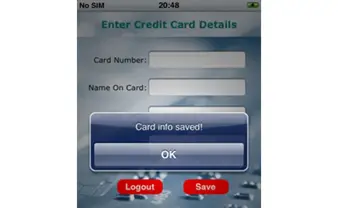
Penetration testing for iPhone applications – Part 4

Compiling the Windows Kernel Driver

Writing a Windows Kernel Driver
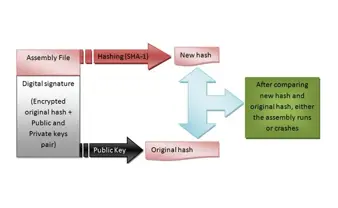
Dot NET Assemblies and Strong Name Signature

Windows Building Environment for Kernel Driver Development

Botnets and cybercrime - Introduction

Machine Learning Part 3: Ranking

Windows booting process

Linux Booting Process