Spam vs. phishing: Definitions, overview & examples
Spam is usually defined as unsolicited commercial e-mail, often from someone trying to sell something. Spammers are not generally trying to get sensitive information from you, although they may try to elicit personal information to add to their database for future spam attempts. According to Statista, spam messages account for 48.16 percent of email traffic worldwide. The most common types of spam email analyzed in 2017 were healthcare and dating spam. The estimate from Talos Intelligence is even more grim: 85 percent of email volume in May 2018 was spam.
Phishing is not limited to email. Other types of phishing include voice phishing, tabnabbing, SMS phishing, Evil Twins, link manipulation on websites and other social engineering techniques. In this article, we will focus on email phishing. This is most assuredly a malicious attack with the intent of luring a victim into disclosing personal (preferably financial) information, with a view to stealing their identity (e.g. passwords and user identification details), and their money.

Learn Python for Pentesting
As reported by Dark Reading, PhishMe found that 91 percent of cyberattacks start with a phish. A study by Symantec confirmed this, stating that 95 percent of all attacks on enterprise networks are the result of successful spearphishing.
We shall see these definitions are not quite as clear-cut as they seem, nor universally agreed on. In this article, we will examine both definitions and provide examples of each.
But, first let’s take a look at junk mail, spam and phishing, and what to know about each of them.
Also see: The Best Techniques to Avoid Phishing Scams
Junk mail
Definition
Definitions of junk mail from Business Dictionary, Market Business News and Merriam-Webster all agree that junk mail is unsolicited, of a commercial nature, usually sent in bulk, and can be either sent by snail or electronic mail. But is it?
Core characteristics
- Usually unintentionally solicited
- Commercial
- Not usually malicious
- Often routed to an email application’s spam folder
- Usually sent in bulk via electronic or snail mail
Variations
- Unsolicited mail sent out usually by direct marketing or direct mail firms. Used mainly for introducing new products, books and magazines, investment opportunities, merchandise catalogs and similar items. Junk mail is big business in industrialized countries. Unsolicited email is called spam
- Third-class mail, such as advertisements, mailed indiscriminately in large quantities
These latter definitions, particularly the characteristic of being unsolicited, blurs the distinction between spam and junk email. To explain the difference more clearly, the concept of graymail is more enlightening.
According to the University of Indianapolis, spam and phishing emails (graymail) should not be confused with junk mail, although junk they are. Junk mail includes promotional emails to which you have (sometimes inadvertently or by omission) subscribed. That little check box at the bottom of the page when you subscribed to Acme Clothing Bazaar’s mailing list? Unless you ticked it opting out of future email correspondence with their business partners, Acme understood it to mean you wanted to receive junk email from their partners too.
And the junk mail you receive from people you know? Even though it goes into the spam folder, it is not actually spam. It’s more likely that when they entered a competition to win a holiday, they were invited to share the opportunity with all their friends. So while junk mail can be annoying, it’s rarely intended to cause actual harm.
Spam
Definition
According to Indiana University, the terms junk mail and spam have evolved to become somewhat interchangeable: “The term ‘spam’ is Internet slang that refers to unsolicited commercial email (UCE) or unsolicited bulk email (UBE). Some people refer to this kind of communication as junk email to equate it with the paper junk mail that comes through the U.S.” Like the definition from the University of Indianapolis, this definition sharpens the distinction between junk email and spam.
Core characteristics
- Unsolicited
- Commercial
- Not usually malicious but can be vicious
- Often routed to an email application’s spam folder
- Sent via electronic mail, text, in an instant message, or in comments on websites, e.g. forums and Usenet groups
- Sometimes attempts to elicit personal details for non-nefarious purposes, or to beg for donations to questionable causes
- A form of junk mail
- Often sent in bulk
- Recipient addresses harvested from publicly accessible sources or by dictionary guessing email addresses, e.g. John1@aol.com, John2@aol.com and so on
Additional characteristics
- Irrelevant or unsolicited messages sent over the Internet, typically to a large number of users, for the purposes of advertising, phishing, spreading malware, etc. (Oxford Dictionaries)
- Spam is electronic junk mail or junk newsgroup postings. Some people define spam even more generally as any unsolicited email. However, if a long-lost brother finds your email address and sends you a message, this could hardly be called spam, even though it is unsolicited. Real spam is generally email advertising for some product sent to a mailing list or newsgroup. (Webopedia)
Why is it bad?
- May promote products with little real value, get-rich-quick schemes, quasi-medical products, dicey legal services and potentially illegal offers and products
- Often unethical, dishonest, and fraudulent. For instance, in 2001, Spam Abuse reported that spammers were soliciting donations for relatives of the victims of the 9/11/2001 terrorist attacks on the U.S. “We at spam.abuse.net do not believe that any of these relatives will see any of that money.”
- Is a threat to Usenet and mailing groups which often receive barrages of spam, comprising the integrity of a group’s content
- Being of dubious origin, spam is often sent from computers infected by computer viruses
- May hijack real users’ identities to send spam to other users
Why do they do it?
- If just a fraction of people who receive a spam email buy the advertised product or subscribe to a service, spammers can make a lot of money. A spam business can be set up for very little and can be very lucrative. Speaking to Wired Magazine, Gmail spam czar Brad Taylor says "It costs $3,000 to rent a botnet and send out 100 million messages. It takes only 30 Viagra orders to pay for that."
- Spammers can sell mailing lists (which is a good reason not to reply to spam, even to give them a piece of your mind. Knowing your email address is valid makes it even more valuable)
- If a spammer send out one million messages and gets a .01 percent response, it equates to 100 buyers — great business for ten minutes’ work
Examples
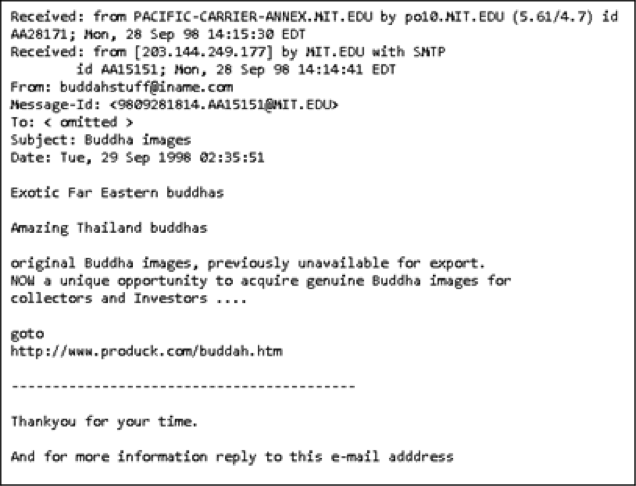
From the Massachusetts Institute of Technology (MIT) come hosts of examples: for instance, this unsolicited advertisement for “Eastern buddhas.” If you go to the website, you will find it does not exist. Spammers tend to create short-lived websites that are removed almost as fast as they spring up:
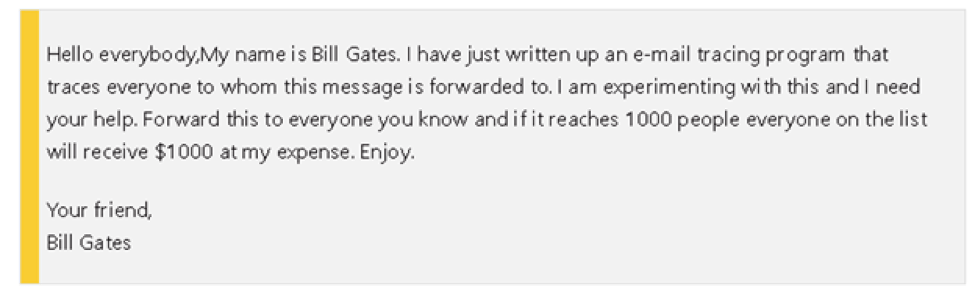
A classic reproduced by Snopes that continues to do the rounds on regular occasions:
You should always check what you suspect may be a spam email with a reputable site like Hoax Slayer. Remember, if it sounds too good to be true, it probably is. Bill Gates will not pay you to forward emails to your contacts. Ever.
Phishing
Definition
According to Webopedia, phishing is the act of sending an email to a user while falsely claiming to be an established legitimate enterprise, all in an attempt to scam the user into surrendering private information that will be used for identity theft. The email will typically direct the user to visit a website where they are asked to update personal information, such as a password, credit card, social security number or bank account numbers. The website, however, is bogus and will capture and steal any information the user enters on the page.
Core characteristics
- Unsolicited
- Commercial
- Always malicious
- Seldom routed to an email application’s spam folder as it usually appears to come from a legitimate source
- Always attempts to elicit personal details for nefarious purposes, or to beg for donations to questionable causes
- May be sent in bulk
- Includes link to phony website
- Recipient addresses harvested from publicly accessible sources, by dictionary guessing email addresses, e.g. John1@aol.com, John2@aol.com, etc., by utilizing the contacts of previously stolen identities, and from personal information sold on the Dark Web
- Utilizes emotional social engineering techniques like intimidation, a sense of urgency, authority, trust, and so on
Additional characteristics
- A scam by which an Internet user is duped (as by a deceptive email message) into revealing personal or confidential information which the scammer can use illicitly. (Merriam-Webster)
Why it is bad?
- Potential identity theft
- Embarrassment, ruined reputations and harassment
- Disrupted operations of accounts
- Compromise of brand integrity for businesses and loss of data
- Any number of financial consequences, including the loss of savings, vehicle repossession and even the loss of employment
- Spread of malware
- Theft of intellectual property
Why do they do it?
According to Wikipedia, “Phishing is the attempt to obtain sensitive information such as usernames, passwords, and credit card details (and money), often for malicious reasons, by disguising as a trustworthy entity in an electronic communication.” Did you spot the word “often?” The website continues: “Phishing is an example of social engineering techniques used to deceive users, and exploits weaknesses in current web security.”
The fact is that while phishing can be described as always malicious, the aim is not always direct financial gain. Some phishers may seek to discredit political parties or other organizations by hijacking the credentials of workers from whom they can steal and compromise sensitive information. Others may hijack a user’s identity and then cyberbully or harass their contacts – for “fun.”
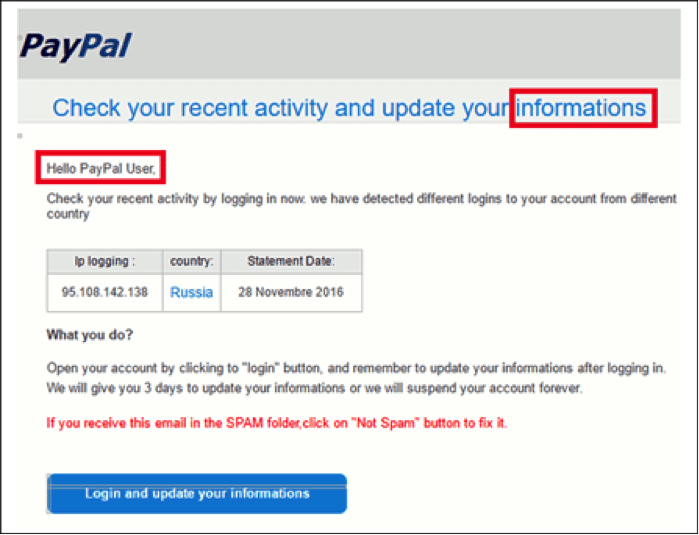
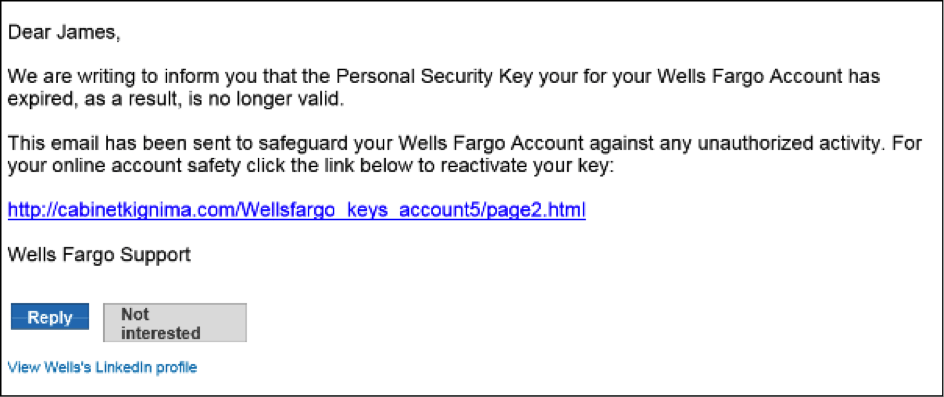
- By impersonating major brands like PayPal, Apple, major banking institutions and government organizations, phishers are assured that a large percentage of potential victims are likely to subscribe to or have an account with the legitimate organization that is being spoofed
- Phishers can use the identities they have stolen to make illegal purchases, or commit other types of fraud
- Make money selling personal information on the Dark Web. For instance, a credit card number may sell for as much as $5
Example
From Raw Info Pages, a typical example of bad spelling or grammar, and generic salutation:
From Phishing.org, you can see that the domain name of the link address is not related to the purported sender:
Related terms
- Email scam. A form of email fraud which includes both spamming and phishing techniques
- Website spoofing. Fraudulent websites that masquerade as legitimate sites by copying the design of the website as well as in some cases utilizing a URL similar to the real site
- Brand spoofing. Where the identities of legitimate organizations are used to create fake websites or to phish victims
- Malware – Closely related to phishing, the main difference is that not all malware is delivered via email
Where to next?
Phishing scams are evolving. According to AWG, at the end of 2016 less than five percent of phishing sites were found on HTTPS infrastructure. By the fourth quarter of 2017, however, nearly a third of phishing attacks were hosted on Web sites that had HTTPS and SSL certificates. The best defense against phishing and spamming is security awareness.
Protect your family and employees with Infosec IQ security-awareness training or test your organization's phishing susceptibility with a free Phishing Risk Test.
Sources
- About spam, Indiana University
- Spammers do more than spam, Spam Abuse
- Why do Spammers Spam?, MCP Mag
- Recent examples of spam that’s been sent to addresses at MIT, MIT
- FACT CHECK: Free Company Giveaways, Snopes
- Phishing for Influence: When Hackers Meddle in Politics, FraudWatch International
- Don’t be fooled by these fake PayPal emails, learn to spot phishing, Raw Computing
-

Learn Vulnerability Assessments
Seven courses build the skills needed to perform a custom vulnerability assessment for any computer system, application or network. - Phishing examples, Phishing.org