Process: gaining and elevating access
Gaining and elevating access and its relation to penetration testing
Background
Penetration Testing is a process that typically consists of the following phases.

Cybersecurity interview guide
- Information Gathering
- Scanning and Enumeration
- Gaining Access
- Maintaining Access
- Clearing Tracks
Though Information Gathering, scanning and enumeration phases are crucial in any pen test, the ultimate goal of an attacker or pentester spending time in those early phases is to reach Gaining Access phase. Gaining Access is the phase where an attacker obtains control over the target. Be it a network or a web application, "Gaining Access" is only the beginning. Maintaining Access and post exploitation (elevating access and pivoting) are usually performed for lateral movement.
This article discusses the process of gaining access and elevating it to proceed further using some simple examples.
Gaining access
As mentioned earlier, gaining access is the ultimate goal of a penetration tester during any assessment. However, most of the times this requires a great deal of time to be spent on theInformation gathering and scanning phases. In a few cases, gaining access could be as easy as accessing an exposed private URL.
The following figure shows that a Jboss server is running the target machine and JMX-console is exposed with no authentication.

In this case, an attacker can simply use this exposed JMX-console to deploy a shell on the server and maintain access to it.
However, gaining access will not be as easy as accessing an exposed URL all the times. Sometimes, it may be required to run exploits against the target to gain access. This is where the penetration tester should be careful. He has to run exploits only when there is no shadow of doubt about the vulnerability existing on the target system. This rule must be followed at least when we are performing assessments on production systems. In most of the cases, penetration testers are not allowed to run exploits on production systems especially when they are critical and should have no downtime at all.
Java Deserialization in popular application servers such as WebLogic and WebSphere is a classic example of exploiting remote systems using an exploit rather than simply accessing URLs.
You may read more about this here if you are interested.
How are exploits classified?
As we go through the discussion about using exploits to gain access to the target machines, let us see some basics about software exploits.
What is an exploit?
In the context of software, an exploit can be defined as a piece of code that takes advantage of a vulnerability to cause unintended behavior in the software.
When we discuss exploits during an assessment, we should be aware of the following.
- Researchers usually release exploits (or) proof of concepts online, and they are made available to the public.
- Some organizations develop exploits and provide them only through their commercial products.
- Some exploits will be sold on the black market, and we do not know who is using them.
Now, our area of focus here is mostly on the first category, where the exploits are publicly available.
www.exploit-db.com is a good resource for various exploits.

We can find various categories of exploits here.
Types of exploits
Exploits are broadly classified into two types based on how they contact the target system/software.
Remote exploits
Remote exploits are more valuable than any other type of exploits. Remote exploits are like guns loaded with bullets. We can hit the remote system using this kind of exploits typically over a network and gain access to it.
Example: Java Deserialization vulnerability in WebLogic Application Server and MS08-067 in Windows XP and Server 2003. The vulnerabilities mentioned above are remotely exploitable, and working exploits are publicly available.
Local exploits
Local exploits are used to exploit the vulnerabilities locally. These are mostly used to elevate the privileges of a user on a machine. This means a user who has physical access/shell access with low privileges can attempt to gain higher privileges by using local exploits. Though remotely exploitable vulnerabilities are more valuable, local exploits are useful in exploiting vulnerabilities when elevating access is required. A remotely exploitable vulnerability that gives a low privileged shell when combined with privilege escalation vulnerability with an available local exploit can lead to complete network compromise.
Example: 'Dirty COW' Race Condition Privilege Escalation. This vulnerability is a classic example to demonstrate local exploits. A working proof of concept exploit is available at the following link.
https://www.exploit-db.com/exploits/40611/
Client Side Exploits
Another category of exploits we did not discuss is client side exploits. To use this category of exploits, an attacker/pentester relies most of the time on Social Engineering techniques. In a typical client-side exploitation scenario, an attacker will send a malicious file that can exploit a vulnerable software (Example: Internet Explorer, Adobe Reader, etc.) on the victim's machine. Once successfully exploited, the attacker will gain access to the victim's machine remotely -- typically over a reverse shell.
Elevating access
Elevating Access is an important step in a penetration test when we get access to the target with some limitations. Though gaining access is good news, we require a shell with administrative access to perform most of the interesting tasks on the target machine. This is where attackers look for options that let them elevate the access on the target machine. As mentioned earlier, using local exploits on a vulnerable machine is one of the options to elevate the access, but this may not work every time especially with a fully updated and patched machine. This is when we need to look for other options such as misconfigurations, and insecure file system permissions, etc.
Elevating access from a low privilege to higher privilege is one form of Privilege Escalation.
Privilege Escalation is broadly categorized into two types.
- Horizontal Privilege Escalation
- Vertical Privilege Escalation
Horizontal privilege escalation
When a user with low privileges can obtain the resources or data of other users with same privileges, it is called as horizontal privilege escalation.
Vertical privilege escalation
When a user with low privileges can obtain higher privileges than what is intended by the system administrator, it is known as Vertical Privilege Escalation.
Let us discuss some examples associated with both Vertical and Horizontal Privilege Escalation.
We typically seeHorizontal Privilege Escalation in web applications, where one user will be able to access the resources of another user.
With the evolution of REST APIs, this is also commonly seen in mobile applications these days due to the statelessness nature of REST API design and of course the mistakes made by the developers.
Assume that a user has performed a transaction online, and he was given a transaction ID to verify his transaction details at a later point in time. The URL looks as shown below.
https://bank.com/transactions/tr_id/2344544443
Now, the user can change this ID to something else, and he can view the transaction details associated with that ID if the application is vulnerable.
https://bank.com/transactions/tr_id/2344544444
This is a typical example of Horizontal Privilege Escalation.
During a penetration testing, if we get access to a box with low privileges, what we are interested in is Vertical Privilege Escalation. Let us see an example.
Assume that we have gained access to a Server running Ubuntu 12.04. Searching online for a root exploit associated with this version of Ubuntu Server, landed us on the following exploit from www.exploit-db.com.
https://www.exploit-db.com/exploits/33589/
Running this exploit on the target machine gives us a shell with elevated privileges as shown in the figure below.
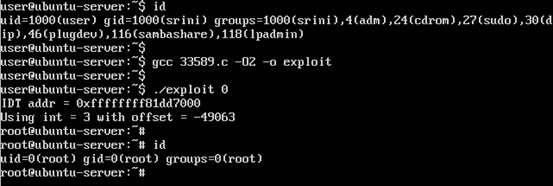
What have we just done in the above figure?
- The output of the first command "id" shows that we got access to a server with normal user privileges.
- Next, we have compiled the exploit taken from www.exploit-db.com
- Then, we ran it with the required argument as mentioned in the source.
- Finally, we ran the "id" command to verify if we got root access.
As mentioned earlier in the article, it may not always be possible to gain root access by running exploits if the machine is properly patched to fix the latest vulnerabilities. So, as a penetration tester we should also be aware of other options such as misconfigurations, and insecure file system permissions, etc. to elevate the privileges on a target machine when required.
Pivoting
Pivoting is a technique used to compromise other machines on a network by using a compromised machine as a pivot point.
This is useful especially when an attacker compromised a machine behind a firewall, and then he wants to scan and gain access to other machines on the internal network. SSH Tunneling is often used in this case, but the Metasploit framework also has useful modules to achieve this.
If you are using a Metasploit framework, typing portfwd –h command on the meterpreter shell will give you an idea about how Metasploit can be used in pivoting.

Learn Python for Pentesting
Conclusion
In this article, we have discussed the process of gaining access and maintaining access. We also briefly discussed exploits and their types followed by elevating access and use of pivoting during a penetration test.








