Penetration testing: maintaining access
Once a pentester manages to gain access to the target system, he should work hard to keep his boat afloat, metaphorically speaking. He can choose either to use the hijacked system as a launching-pad (i.e., to be part of a botnet for DDoS attacks or spam campaigns), at this moment attack, scan and exploit other systems, or keep on exploiting the current system in stealth mode. Both actions can entail a great deal of damage.

Learn Python for Pentesting
For example, the pentester could set up a sniffer to intercept all inbound/outbound network traffic, including an FTP (file transfer protocol) and telnet sessions with other systems, so that he will later transmit that data wherever he wants.
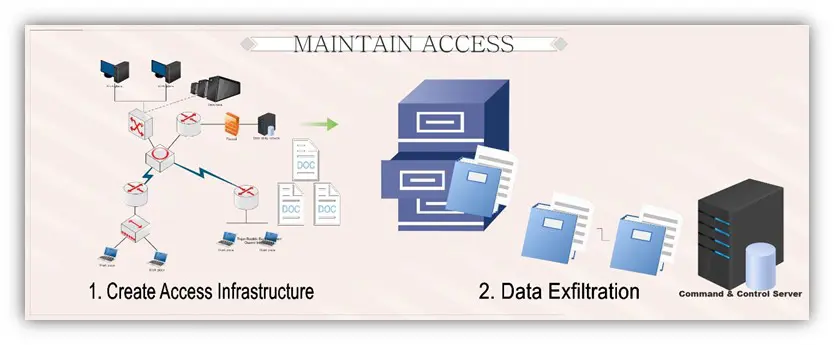
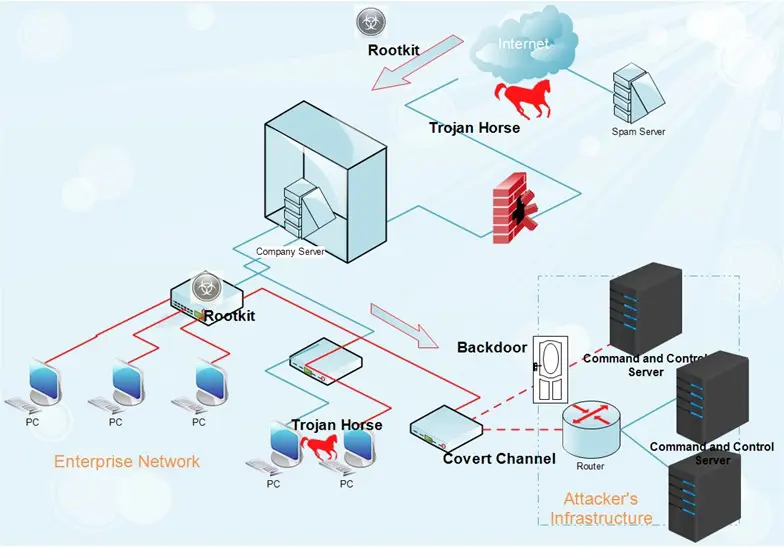
For those who want to remain undetected, it will be imperative to undertake further steps to secure their presence. There are different ways through which that can happen, but typically through the installation of hidden infrastructure for repeated and unfettered access based on backdoors, Trojan horses, rootkits, and covert channels (section 1). When this infrastructure is all set to go, the pentester can then proceed to exfiltrate whatever data he considers being valuable (section 2).
Tools and methods for maintaining access
A backdoor or a Trojan is a convenient tool for establishing easy access into the already breached system. A Trojan horse provides access at the application level, but to gain it, the user needs to install the piece of malware locally. In Windows-run systems, the majority of Trojans proceed to install themselves as a service and then run as a local system, having administrative access. Furthermore, the pentester can mount Trojans to sneak out passwords, credentials, and any other sensitive information stored on the system.
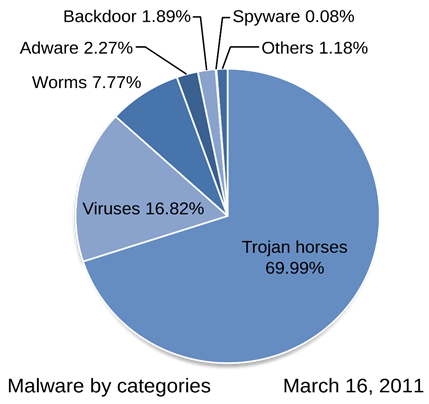
Source: Wikipedia by Kizar
Much like remote access Trojans (RATs), backdoors are installed in target systems and come with built-in upload/download functionality. They upload gathered files of interest and then rely on ports like port 53 (for DNS) and 80 and 443 (for HTTP and HTTPS, respectively) to cover up their traffic. TrendMicro reports cyber incidents connected to attackers bypassing "the connection restriction whenever they use HTTP to transmit data and to bypass detection. Based on [TrendMicro's] investigation, there are instances when attackers manually download the .ZIP file containing all collected data."
A covert channel
A covert channel is when data is being sent through secret communication tunnels. VoIP, DNS tunnels, ICMP tunnels, and HTTP tunnels are such paths for data extraction from the inside of a network. All of these covert channels can transport encrypted data as well.
Although detecting covert channels is not impossible, it may require considerable efforts on the part of the victim. Network signatures, flow data analysis and protocol analysis are some of the indicators of anomalies in the outbound traffic which a pentester wielding the right tools can come across. On top of that, despite that protocol- or application-specific tools do not yield easily to security purposes, they could show better results in comparison to their security-specific counterparts.
To detect a covert tunnel is one thing, but to block it is a completely different matter. Pentester can:
block ICMP outbound at the corporate information border;
block DNS requests to servers outside the corporate network but not to such to internal DNS servers;
leverage Web proxies to dispose of the HTTP tunnels;
delay delivery for a voicemail in cases of VoIP RTR exfiltration tunneling so that he can send to an audio processor, which will examine every packet for encoded data in a voicemail (in a similar fashion as antispam software works).
Rootkit
A rootkit is a type of malware highly adept at hiding itself from a computer system. Hence, what distinguish rootkits from other types of malware is their heightened ability to conceal themselves to bypass the computer security measures. In effect, that is the main idea behind their creation.

Source: Cristiaan Colen
Rootkits are usually loaded with the help of Trojan horses, starting on the targeted platform with "user" level access. Once getting an initial foothold into the system under attack, they spy on passwords and other similar login details to gain "administrator" level access. This process is called privilege escalation. Nevertheless, the rootkits' real "specialty" is maintaining access.
Unlike the ordinary viruses which attempt to inflict as much damage as possible for a short period, rootkits tend to lurk in the targeted system, progressively and slowly undermining it. Prima facie the emphasis is on the word 'secrecy'. For example, rootkit keyloggers are designed to record the words the victim types without his knowledge. It has plenty of time to steal sensitive information given the fact that this malware may remain undetected, which will, in turn, increase the probability of identity theft.
In this regard, rootkits are somehow reminiscent of some forms of parasites, which enter the body but may remain dormant for years until they muster up enough strength to overcome the immune system from within the body.
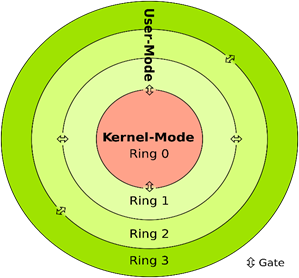
Source: Wikipedia by User:Sven and User:Cljk
If we split a computer system into three basic layers, we end up with hardware, kernel, and operating system level. In essence, the kernel is the core of the operating systems. Often user-level rootkits use low-priority processes to subvert security software. Kernel-level rootkits are far stealthier and dangerous than their other levels counterparts because of the following reasons:
- they have the ability to camouflage their presence when they add their code to portions of the operating system's kernel;
- they run earlier than the operating system does;
- they can circumvent encryption and create secret channels for unrestricted access to the penetrated system;
- It has been proven that to remove kernel-level and boot-level rootkits often is not that simple;
- Rootkits residing in the kernel memory normally leave no trace on the hard disk. Also, they may modify files, parts of the disk, and even alter the kernel so that they can resist reboots.
Rootkits installed at the kernel level gain full administrator access to the systems in the gunsight of the potential attacker. Unlike Trojan horses, rootkits pave an access path (with "good intentions) right to the operating system level.
Some advice on how to remove rootkits
Classical security measures such as antivirus software alone usually cannot cope with the danger the rootkits represent. As an alternative approach, you can pick one of the purpose-built programs designed to eradicate rootkits: Malwarebytes Anti-rootkit, GMER, Sophos Anti-Rootkit, TDSSKiller, etc. (See here).
Nonetheless, sometimes such measures may prove to be ineffective, since they will succeed to alleviate only some of the negative influence that the rootkit disseminates all over your system, without any guarantees that these programs will be able to remove it for good. Besides anti-rootkit software, one may initiate the "clean slate" procedure – that is, to backup the most important files and re-install the operating system completely. Under normal circumstances, an act of this magnitude would extirpate the rootkit. But even then there is no 100% guarantee because a very rare sort of rootkits, BIOS-level rootkits, can survive the re-install.
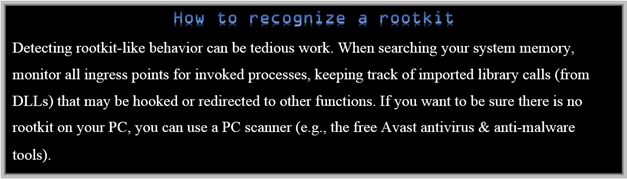
Source: https://www.avast.com/c-rootkit
No matter how hard a rootkit tries to be invisible, however, there are always signs, at least in theory (if it is any consolation to you), because the purpose of the rootkit is to maintain an ingress path for the outsider.
Data exfiltration
Data exfiltration is an unauthorized transfer of data from a computer system or IT servers to an external system or device. It can be carried out manually (similar to a 'copy-paste' command) or automatically via malware spread across a network.
A 2015 McAfee report points out that 60% of all reported data exfiltration cases occurred via direct electronic means, whereas the rest 40% involved physical media, such as downloading data to a USB drive or stealing a laptop. A considerable part of that 40% share involved mobile phones, which is perhaps due to the ubiquitous acceptance of bring-your-own-device policy in many corporations. Personally, identifiable information (PII) and personal health information (PHI) were the top content categories, followed by intellectual property and financial data.
When the data is exfiltrated electronically, it is usually through different kinds of web protocols, tunneling protocols, email or file transfers. While the file transfer protocol (FTP) is regarded as a standard network protocol whose purpose is to transfer files, it may also be used to facilitate data exfiltration campaigns. Other protocols and techniques are applicable as well, for instance, routing control packets, secure shell, peer-to-peer, instant messaging, Windows Management Instrumentation, hiding data within video or images, and VoIP. Webcams, microphones, and similar peripheral devices may be rigged to monitor the target's activities. Pentester can also make use of HTTP file transfers or the Tor anonymity network as a means to mask location and traffic.
Sometimes before the exfiltration takes place, the pentester would want to process the data to transfer it easier outside the exploited system. Typical activities with relation to this point are compression, encryption and password protection. Then the processed data will be uploaded from within the target network to a server somewhere outside. Common traffic channels are a preferable route for smuggling data out of the targeted system since the extraction will blend in with the noise of the network.
The FrameworkPOS malware is an excellent illustration of how data exfiltration works – it leverages memory scraping techniques to dig out credit card information stored somewhere in processes running on the endpoint. Upon finding the relevant data, the malicious software performs DNS tunneling to connect to a command and control server to pull out the data. Furthermore, the FrameworkPOS encodes via XOR the credit card information, hostname and IP address, and adds the encoded package to an HTTP request to export data from the environment. This trick effectively obfuscates a firewall- and proxy-based inspection.
Undetected data exfiltration is what wrongdoers are looking for in many cases, as the real-life cyberattacks against Target and Home Depot demonstrate. This is so because some of the information they steal is secret, and it is more valuable or only valuable when it stays secret.
Early detection is crucial when it comes to Advance Persistent Threats (APTs) and stopping malicious actors from exfiltrating your data. Every organization should have an effective threat intelligence procedure in place which will help determine all the suspicious activities that can be considered as related to data exfiltration. The real-time local threat intelligence system should be complemented by connecting to a global threat intelligence network to keep abreast with the latest security trends.
According to Splunk Enterprise Security some notable indicators of data exfiltration are a good starting point for a full-blown investigation. Those indicators are:
- Unapproved port activity
- High-volume email activity to non-corporate domains
- Host sending excessive email
- Excessive DNS queries
- Web uploads to non-corporate sites by users
In essence, an effective method for prevention of data exfiltration is every method or tool enumerated so far concerning detection and removal of basic data exfiltration elements, i.e., Trojan horses, backdoors, rootkits and covert channels.
Conclusion
"Maintaining Access" is a phase of the pentest cycle which has a very concrete purpose – to allow the pentester to linger in the targeted systems until he acquires what information he considers to be valuable and then manages to extract it successfully from the system. However, as is often the case, it is easier said than done. Let's compare it to being in someone else's house without his permission – it is one thing to enter his home and walk around for a while, but it is another matter when you want to settle in for a little longer without attracting the owner's attention. While such a Houdini-like trick may be a tad easier in the cyber world, it remains challenging. Challenging but not impossible.

Learn Threat Modeling
Sources
- The 5 Phases of Hacking: Maintaining Access
- Data Exfiltration, Part 4: How Does the Data Leave Your Four Walls?
- Advanced Methods to Detect Advanced Cyber Attacks: HTTP(S) Exfiltration
- Stealth Viruses and Rootkits
- The Virus Lab – What is a Rootkit?
- What Are Rootkits and Why They Are Dangerous?
- How a Rootkit Works
- What is Data Exfiltration?
- Detecting covert channels to prevent enterprise data exfiltration
- Stop Data Exfiltration
- How to Create a Nearly Undetectable Covert Channel with Tunnelshell
- Exfiltration Through Obscurity – Detecting Attackers Tactics For Stealing Your Data
- Detect and Stop Data Exfiltration
- Data Exfiltration: How Do Threat Actors Steal Your Data?
- Phase 4 - Maintaining Access
- CIS 450 – Network Security Chapter 15 – Preserving Access."— Presentation transcript
- What is a rootkit








