Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
Arrays: A Brief Tutorial

GFI LanGuard – Network Security Scanner
Reversing Loops
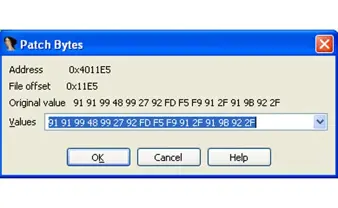
IDA program patching

Implementing Secure SDLC – Part 4

Snort Rule Writing for the IT Professional

Android: WhatsApp chat forensic analysis

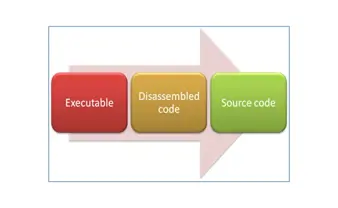
Linear sweep vs recursive disassembling algorithm
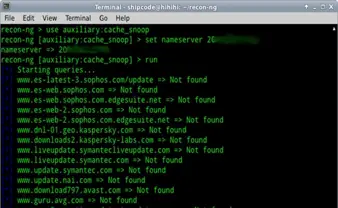
Awesome modules of Recon-ng used for Web Recon testing

Application security testing of thick client applications

Which Weapon Should I Choose for Web Penetration Testing? 2.0

Identity Management Solutions

Anatomy of a Risk Assessment

Anti-debugging: Detecting system debugger
Unpacking, reversing, patching
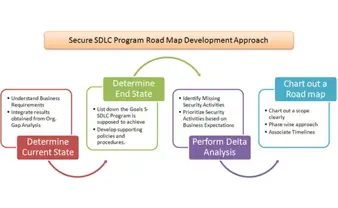
Implementing Secure Software Development Program – Part 3
Object Oriented Programming in C#.net
Cyber-espionage: The greatest transfer of wealth in history
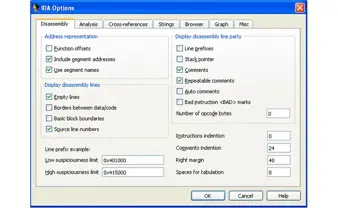
IDA Pro Configuration Options

Cryptography 101 with SSL

IDA Pro: IDC, SDK and Remote Debugging Overview

Facebook malware: How do they work, how to protect yourself against them and what to do if you get infected

Implementing Secure Software Development Program

Secure code review: A practical approach