Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

PCI-DSS and PA-DSS

Android Application hacking with Insecure Bank - Part 3
Browser-based vulnerabilities in web applications

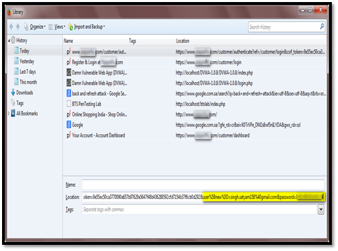
Buying personal information in the deep web

Digital Dark Age: Information Explosion and Data Risks

Ethical Hacking Dual Certification

Cracking a Wi-Fi WPA2 Password, Thanks to Amazon

Wi-Fi Security: Securing Yourself against Practical Wireless Attacks

Understanding iOS Security: Part 1

Introduction to GSM security
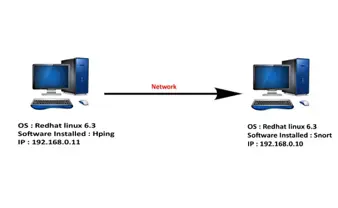
Packet crafting: a serious crime!

iOS Application Security Part 39 - Sensitive information in memory
Cyber Security Risks in Supply Chain Management – Part 2

The FREAK Vulnerability: From Discovery to Mitigation

Cyber Security Risk in Supply Chain Management: Part 1

Understanding Web Caching
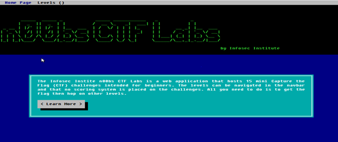
n00bs CTF Labs - Solutions!

Digital footprints and privacy concerns
DDoS on UPNP Devices

n00bs CTF Labs by Infosec Institute

Equation Group APT and TAO NSA: Two Hacking Arsenals Too Similar

HTML5 Security: Cross Domain Messaging

Biometrics: Today’s Choice for the Future of Authentication
OWASP ProActive Controls: Part 2 of 2