Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
Taking Control of the Process
Tunneling, Crypto and VPNs
Defense in depth is dead; Long live defense in depth!

Clickjacking, Cursorjacking & Filejacking

Interview: Morey Haber, VP of Technology at BeyondTrust

Why Do We Need Software Escrow?
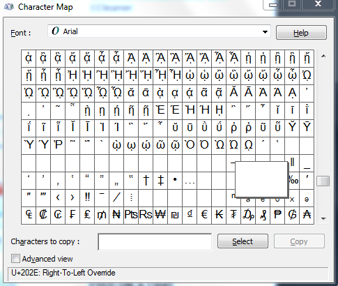
Spoof using right to left override (RTLO) technique

iOS Application Security Part 41 - Debugging applications using LLDB
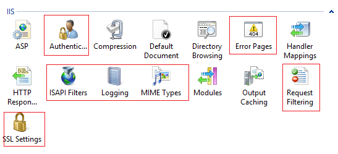
Hardening IIS security

Cracking NQ vault step by step
Anonymizing Activities in the Digital World using TOR

PoS Malware is More Effective and Dangerous

Solutions to net-force cryptography CTF challenges

iOS Application Security Part 40 - Testing apps on your Mac

Bypassing In Safari

IT Security Awareness Programs
Solutions to Net-Force steganography CTF challenges

Security Policy Template for Web Applications

DNA cryptography and information security

Android Application hacking with Insecure Bank Part 4

Bypassing same origin policy (SOP)
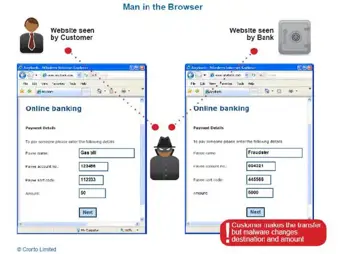
Are Browsers the Weakest Link of the Security Chain?
Security attacks via malicious QR codes

Encryption Solutions for the New World