Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
Pentester’s Guide to IoT Penetration Testing

GCIH certification overview
Video Tutorial - Paraben E3 Platform and Mobile Phone Forensics

Security+: Deploying Mobile Devices Securely - 5 Top Tips [DECOMMISSIONED ARTICLE]

Security+: Technologies and Tools - SIEM [DECOMMISSIONED ARTICLE]

Security+: technologies and tools - Access point [DECOMMISSIONED ARTICLE]

Security+: Technologies and Tools - Load Balancer [DECOMMISSIONED ARTICLE]

Security+: Technologies and Tools - Proxy [DECOMMISSIONED ARTICLE]

Security vulnerabilities of cryptocurrency exchanges

PowerShell For Pentesters Part 2: The Essentials of PowerShell

What Does Compliance With OWASP Really Mean for Financial Institutions?
Kioptrix VMs challenge walkthrough
USV: 2017 Part 1 CTF Walkthrough
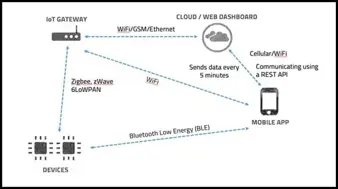
Beginner’s guide to Pentesting IoT Architecture/Network and Setting up IoT Pentesting Lab - Part 2
Beginner’s Guide to Pentesting IoT Architecture/Network and Setting Up IoT Pentesting Lab - Part 1

Gmail Phishing Scams You Need to Know About

Mirai botnet evolution since its source code is available online

The top 15 must-have books in InfoSec

Top threats to online voting from a cybersecurity perspective

And Again, About Storing Passwords
Gaining Shell Access via UART Interface Part 3
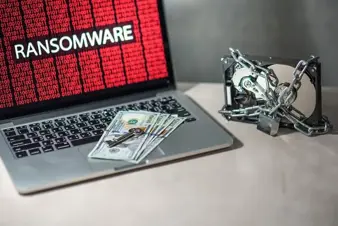
The Decline of Ransomware and the Rise of Cryptocurrency Mining Malware

Mechanics Behind Ransomware-as-a-Service
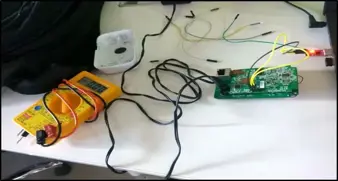
Gaining Shell Access via UART Interface Part 2