Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

What Is an IdM and how to discover if you need one
Gaining Shell Access via UART Interface Part 1
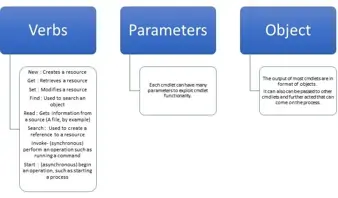
PowerShell for pentesters part 1: Introduction to PowerShell and Cmdlets

The International Association of Privacy Professionals CIPP/E Certification

The International Association of Privacy Professionals CIPM Certification

GIAC penetration tester (GPEN) certification

What is the GCFE?

How to Identify and Detect a Phishing Email – 10 Tips

What is the difference between the surface web, the deep web, and the dark web?

Security+ Domain #6: Cryptography and PKI [DECOMMISSIONED ARTICLE]

10 Tips to Increase IoT Cameras Protection

Android Penetration Tools Walkthrough Series: AppMon

User and Entity Behavioral Analytics (UEBA) Overview

Finding and exploiting XXE - XML external entities injection

Android penetration tools walkthrough series: Drozer
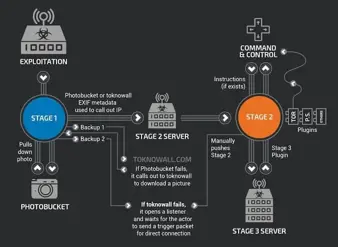
The VPNFilter: A Powerful Botnet of More Than 500k Devices Ready to Attack
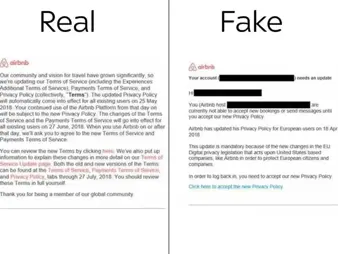
GDPR Provides Scammers with a New Golden Opportunity

Why Military Veterans Make Good Cybersecurity Professionals

Minorities in Cybersecurity: The Importance of a Diverse Security Workforce

GIAC Certifications Overview

A brief guide to GDPR compliance

10 things employers need to know about workplace privacy laws
5 Security Awareness Tips for HIPAA Compliance

Android penetration tools walkthrough series: AndroBugs framework