Threat Intelligence

Threat Intelligence
The demand for dark web hacking tools has reached all-time highs across the cybercriminal ecosystem during the COVID-19 pandemic.

August 3, 2021
Dan Virgillito
Threat Intelligence
Public packages can be exploited and replaced with malicious ones at even the largest companies like Apple and more.

June 3, 2021
Pedro Tavares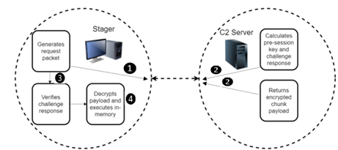
Threat Intelligence
BendyBear malware has proven to be one of the most dangerous, and a threat to countries across the world.

June 2, 2021
Pedro Tavares
Threat Intelligence
The age of cyber spying Targeted malware is often an issue for officials such as diplomats and telecom operators. In rare cases, industries become a target,

March 18, 2021
Greg Belding
Threat Intelligence
What do cybercrime, fake news, the Middle East/South Asia and a dragon from the Final Fantasy or the Dungeons & Dragons series all have in common? The an

March 9, 2021
Greg Belding
Threat Intelligence
2020 was a busy year for cybercriminals, with new opportunities brought on by the COVID-19 lockdowns and digital transformation initiatives. According to McA

February 8, 2021
Dan Virgillito
Threat Intelligence
Introduction If you are a malware researcher, you’ve probably heard of KashmirBlack, a botnet that has been in the wild since 2019. If you are not a malware

February 4, 2021
Greg Belding
Threat Intelligence
Introduction In October 2020, the BlackBerry Research Operations team released a comprehensive report highlighting the reach, tradecraft and sophisticated t

January 21, 2021
Patrick Mallory
Threat Intelligence
Introduction Think your Linux system is immune to malware? Well, think again. Advanced attack groups have sophisticated PHP rootkits, web shells, exploit co

January 18, 2021
Dan Virgillito
Threat Intelligence
Ransomware remains the number one security risk to businesses and users, even though attacks have slowed down — or have they? Key findings from the 2020 Veri

December 10, 2020
Daniel Brecht- 12 pre-built training plans
- Employer-requested skills
- Personalized, hands-on training
In this series
- Dark Web hacking tools: Phishing kits, exploits, DDoS for hire and more
- Dependency confusion: Compromising the supply chain
- BendyBear: A shellcode attack used for cyberespionage
- ATP group MontysThree uses MT3 toolset in industrial cyberespionage
- BlackBerry exposes threat actor group BAHAMUT: Cyberespionage, phishing and other APTs
- Top 9 cybercrime tactics, techniques and trends in 2020: A recap
- KashmirBlack botnet targets WordPress, Joomla and other popular CMS platforms
- BAHAMUT: Uncovering a massive hack-for-hire cyberespionage group
- Linux security and APTs: Identifying threats and reducing risk
- Top 6 ransomware strains to watch out for in 2020
- 2020 Verizon data breach investigations report: Summary and key findings for security professionals
- How hackers use CAPTCHA to evade automated detection
- The State of Ransomware 2020: Key findings from Sophos & Malwarebytes
- Dark web fraud: How-to guides make cybercrime too easy
- Top 6 malware strains to watch out for in 2020
- Top Cybersecurity Predictions for 2020
- Malware spotlight: What is click fraud?
- What does dark web monitoring really do?
- ThreatMetrix Cybercrime Report: An interview
- Are dark web monitoring services worth it?
- Cybercrime and the underground market [Updated 2019]
- Verizon DBIR 2019 analysis
- Common causes of large breaches (Q1 2019)
- The Magecart Cybercrime Group Is Threatening E-Commerce Websites Worldwide
- Russian Cyberspies Target 2018 U.S. Midterm Elections
- The Increasing Threat of Banking Trojans and Cryptojacking
- Leaders’ Meetings: A Privileged Target for Hackers
- Fraud as a Service (FaaS): Everything You Need to Know
- All about SamSam Ransomware
- The Decline of Ransomware and the Rise of Cryptocurrency Mining Malware
- Mechanics Behind Ransomware-as-a-Service
- The Art of Fileless Malware
- ZLAB MALWARE ANALYSIS REPORT: RANSOMWARE-AS-A-SERVICE PLATFORMS
- Which Are the Most Exploited Flaws by Cybercriminal Organizations?
- 5 New Threats Every Organization Should be Prepared for in 2018
- Memcrashed: The Dangerous Trend Behind the Biggest DDoS Attack Ever
- Open source threat intelligence tools & techniques
- Global Cost of Cybercrime on the Rise
- An Enterprise Guide to Using Threat Intelligence for Cyber Defense
- The Five Largest Ransomware Attacks of 2017
- Intellectual Property Crimes in the Dark Web
- Top 5 Smartest Malware Programs
- Is Russian Intelligence Using Tainted Software to Access Corporate and Government Networks?
- Vault 7 Leaks: Inside the CIA's Secret Kingdom (July-August 07)
- DragonFly 2.0: The Alleged Nation-State Actor Hits the Energy Sector Again
- Russian APT Groups Continue Their Stealthy Operations
- Massive Petya Attack: Cybercrime or Information Warfare?
- SAP SECURITY FOR CISO: SAP Attacks and Incidents
- Role of Threat Intelligence in Business World
- WikiLeaks Vault 7 Data Leak: Another Earthquake in the Intelligence Community
- Reduce security events
- Reinforce cyber secure behaviors
- Strengthen cybersecurity culture at your organization