VoIP network recon: Footprinting, scanning, and enumeration
The traditional PSTN has been replaced by more advanced and efficient VoIP network. VoIP has quickly made its place in the corporate and home environment as well; there are many advantages of using VoIP network over PSTN. But, the security risk has also increased over the period; securing VoIP network in a corporate environment is the necessity that you can't ignore. VoIP uses the internet infrastructure to establish the connection for voices, data also travels on the same network; it seems a big advantage of VoIP, as there is no need to deploy a separate network for VoIP; but, at the same time VoIP is vulnerable to the common TCP/IP attacking vectors (because the network is same).
Information gathering is the foremost step of hacking & penetration testing; you need to find the detail picture of the network/server/system that you want to exploit, and the same step should be taken prior exploiting the VoIP network. This tutorial discusses the process, tools, and techniques to achieve this objective.

What should you learn next?
VoIP lab environment
Creating the lab environment is crucial to practice the attacking methodologies; you should create a VoIP network to practice the scanning and other attacking vectors. There are two types of phones:
- Hardware based
- Software based
Hardware based is the one that has the physical appearance, while the software based phone can be installed on your computer (Windows, Linux, MAC, Android, iOS, etc.). In this lab environment two software based phones from different vendors have been configured on two different machines:
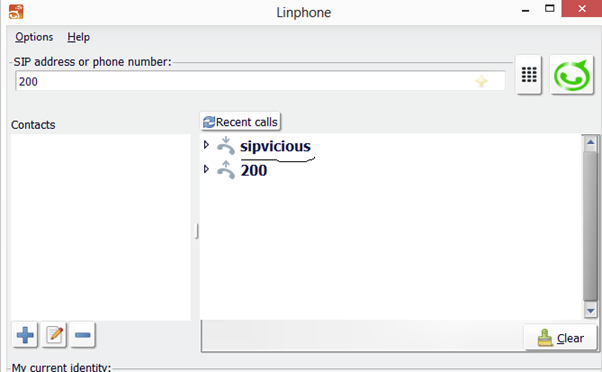
- Linphone configured on a Windows machine
- Zoiper configured on a Linux machine
Apart from the phone, VoIP server has also been installed and configured. Trixbox is a software PBX based on Asterisk is installed on a virtual machine, Digium (the parent company) no longer updating the community version of the software. However, the last release can be downloaded from the SourceForge.
Another software that you can use as a VoIP server is FreePBX. It is an open source project that provides the GUI of Asterisk PBX.
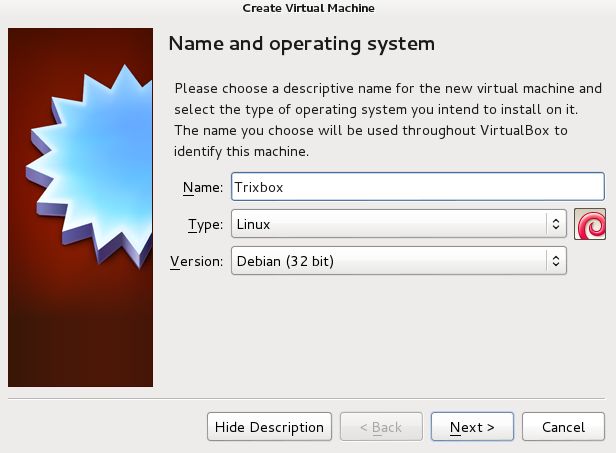
Create a new machine in the VirtualBox (you may use any other VM), put the name and select Linux as the machine type (since the PBX is based on Linux OS).
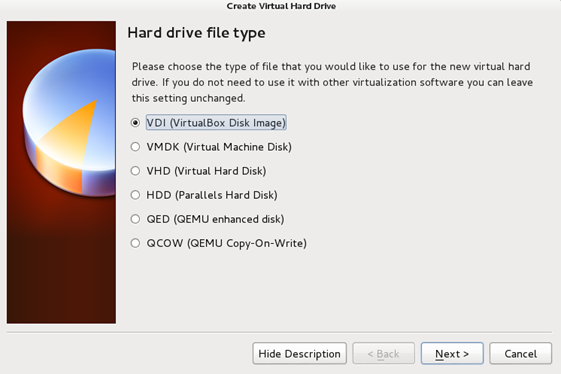
Assign the memory for the server; 512MB is good to start with. Create a new virtual hard drive, and select the VDI:
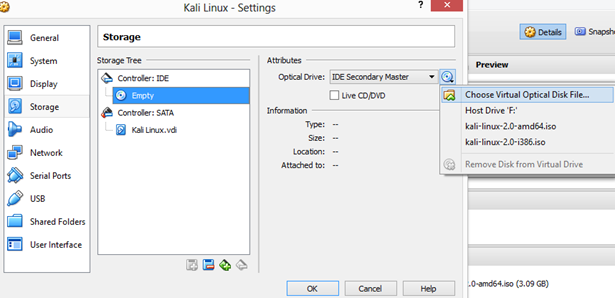
Dynamically allocate the drive space and finish the setup. Click on Settings → Storage → Empty → Choose a virtual CD/DVD file and select the download ISO image:
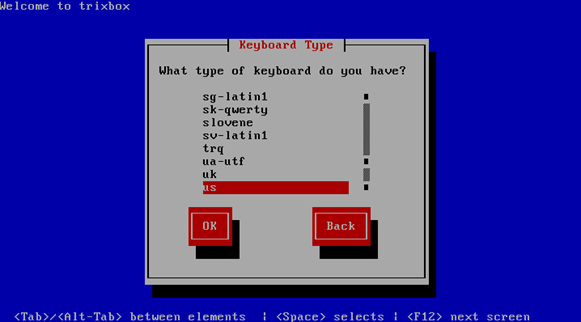
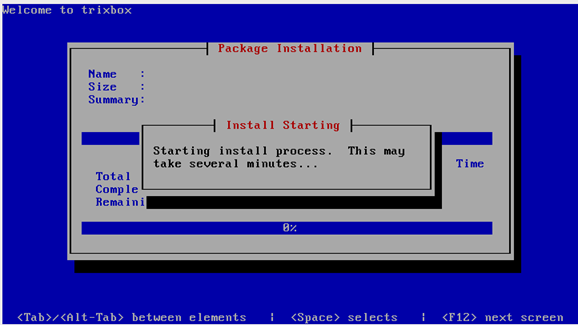
Start the machine and press enter to get in the installation process, select the keyboard layout:
Enter a strong password, make sure that the password is for the root account and this account will have all the authorities. The installation process will take some time:
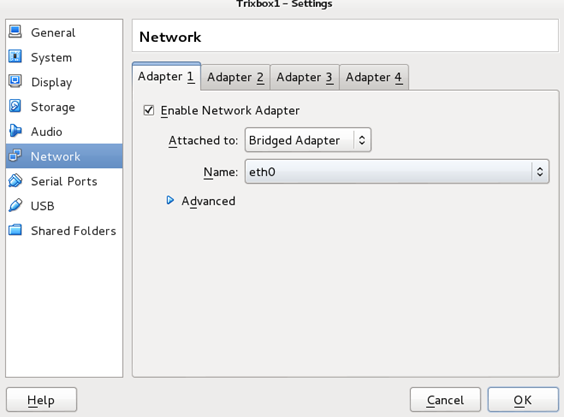
Remove the ISO image after installing the server. Select the bridge adapter under the Network setting to have this machine connected to the network:
Start the server.
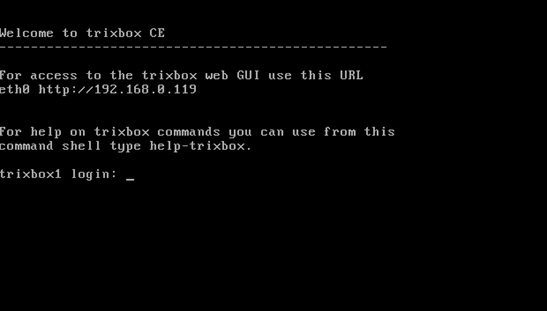
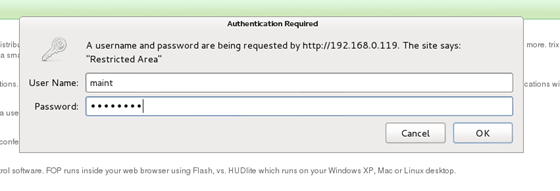
On your browser locate the given IP address, you will be redirected to the GUI of the server; switch the user to admin (from the right top), use the default credentials (username: maint | password: password):
The front page is the summary of the server; you can see the performance of the server. The core objective is to create the user extensions so that other machines can connect to the server. Click on PBX → PBX settings → Extensions (basic) → Add new Extension:
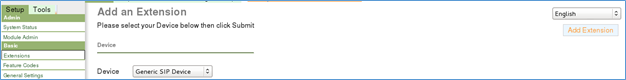
Select "Generic SIP Device" and click on submit. Enter the extension number (it depends on your dialing plan); display name is to have a memorable name appear on the screen. "Secret" is the password of any particular extension, make sure to enter a strong password:
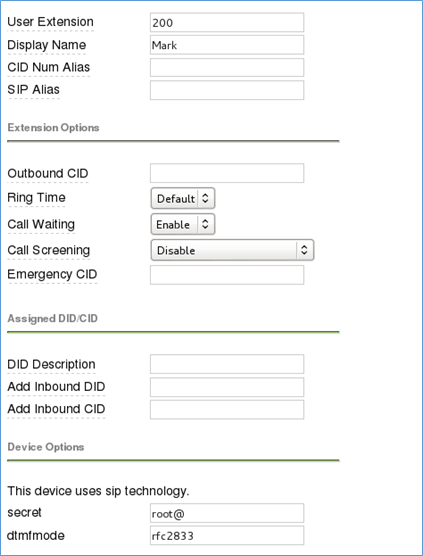
Click on submit to add the extension. "Apply configuration setting" to direct the server to apply the made changes.
Softphone configuration
Download and install any softphone from the internet, create a new account and select the SIP:
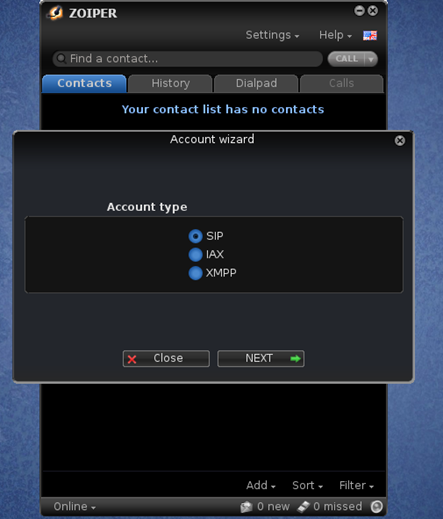
Username: extension@voipserver (200@192.168.0.100)
Password: Enter the password (secret)
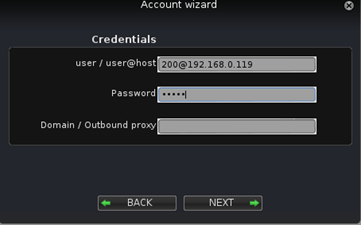
Click on next and the account is added. The newly configured softphone can communicate with the server, add another extension on the other softphone and configure it on any other machine.
Create a VoIP network; add different extensions using different dialing plan to practice the scanning and enumeration process.
Footprinting the VoIP environment
In footprinting, we utilize the publicly available data to acquire the intended information. Most of the organizations don't have any idea about the crucial data available on the internet that an attacker might get and use against them. VoIP server comes with a web interface, so there should a web server running with VoIP; in the meantime, the server is vulnerable to SQL-injection attack. Denial of service (DOS) attack can also be launched against the router of the server to make the resource unavailable to the intended users.
You should look for the following information during footprinting, scanning and enumeration process:
- The public IP of the server
- The VoIP network / infrastructure
- Devices connected to the VoIP network, their open ports, and running services
- Users information (extension, the device information, and logs)
- Information about the VoIP server (model, vendor, OS, ports, etc.)
Where to look and what is the process to get the listed information:
- Google search and Shodan to find the publicly available information
- Map the organizational structure, office locations, top management
- Job listing websites
- Nmap, Sipvicious, and other tools to map the internal VoIP network
Job portal websites reveal much important information:
Requirement:
SIP (OpenSIPS or FreeSWITCH) 3-5 years with VoIP 3-5 years supporting SIP G.711 in large…...
Experience in voice telecommunication infrastructure (TDM and VoIP) including Avaya 96xx phones, SIP phones, and accessories, Acme, Spiera, Audiocodes SBCs…….
Both the examples above reveal the information about the server and end-user devices that the organization is using. It also reveals the possible model or series that an organization might use or intended to use in future.
Google is a very good friend of hackers, utilize the Google dorks to find the VoIP network and device information:
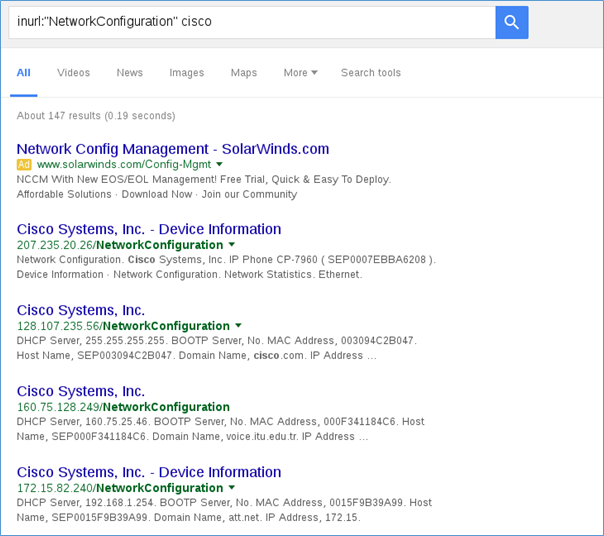
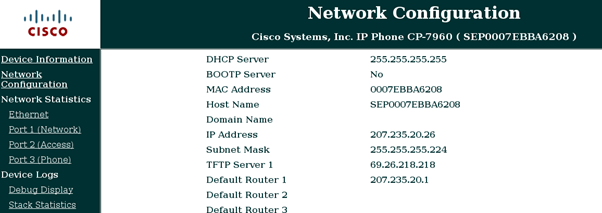
Here you can see the valuable information about the network is available for everyone to see:
A simple WHOIS search and DNS analysis also reveals much important information of the target organization. In the following example MALTEGO is used to analyze the DNS of the domain:
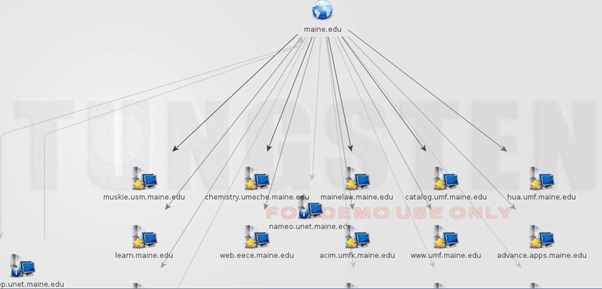
The objective is to find the DNS name such as voip.abc.com, callmanager.abc.com, etc. In the given example, the mail server, web server and Cisco CallManager have been found. These are the enough information to map the target network and to penetrate to the inside of the network.
A simple search on Shodan.io shows 33k servers running VoIP
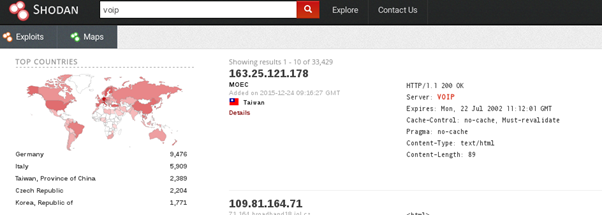
Create an account on shodan and search the network of any specific target. Let's analyze a server found via Shodan:
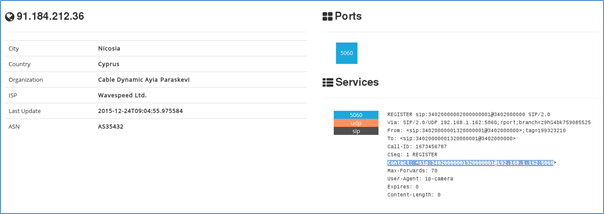
The UDP port number 5060 represents the SIP service (VoIP); the search information provides the external IP and the internal IP (highlighted) as well. Now an attacker has to scan the internal network to find further information.
Scanning & enumerating the VoIP environment
After the footprinting, you must have sufficient information to scan the internal environment. We will begin with the quick Nmap scan on the entire network (since we don't have any idea at the moment); once we get some information, then we will refine our search:
Make sure to focus on UDP/TCP ports 5050 and 5061 because SIP enables devices to use these ports, the Cisco phones usually response on UDP/TCP ports 2000 and 2001.
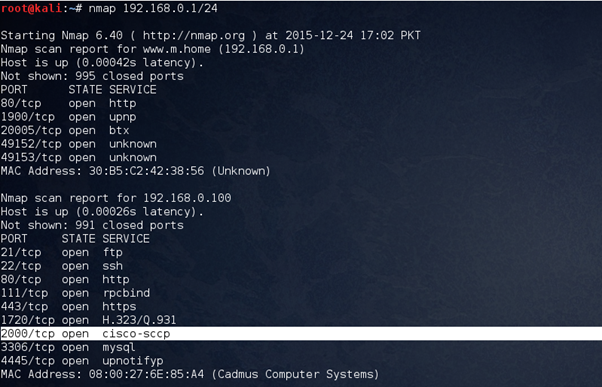
The result of the basic scan shows live systems, open port numbers and the services running on each port. The machine (192.168.0.100) seems interesting because the following services are running:
- Cisco-sccp
- H.323/Q.931
The other interesting result:
Nmap scan report for 192.168.0.118
Host is up (0.11s latency).
Not shown: 987 closed ports
PORT STATE SERVICE
135/tcpopen msrpc
139/tcpopen netbios-ssn
445/tcpopen microsoft-ds
554/tcpopen rtsp
2869/tcp openicslap
5060/tcp open sip
5357/tcp openwsdapi
10243/tcpopen unknown
49152/tcpopen unknown
49153/tcpopen unknown
49154/tcpopen unknown
49155/tcpopen unknown
49175/tcpopen unknown
MAC Address: 08:ED:B9:A8:4B:E1 (Hon Hai Precision Ind. Co.)
5060 is open, and it is SIP. So far we have identified the two machines running VoIP services. Note them down for further analysis:
192.168.0.100
192.168.0.118
Let's have another intense scan to identify the running operating systems and the services; the objective is to find the VoIP server.
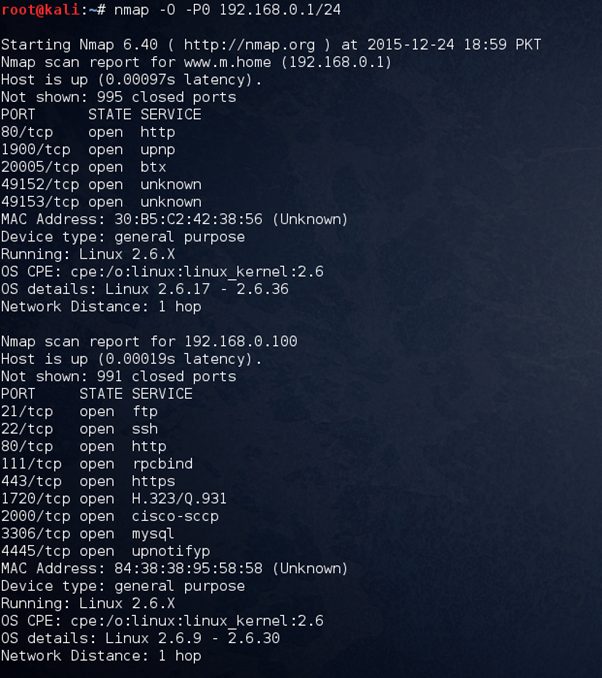
Nessus is the vulnerability scanner tool but it performs the footprinting and scanning to identify the target network, let's use Nessus to get the complete picture of the target network. Basic network scan using Nessus has been done and here is the result:
192.168.0.118 (nothing interesting related to VoIP found by Nessus)
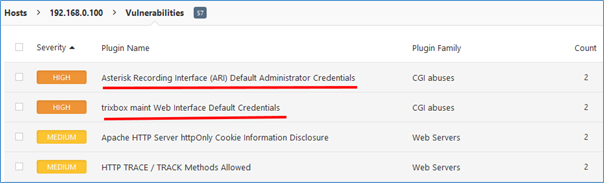
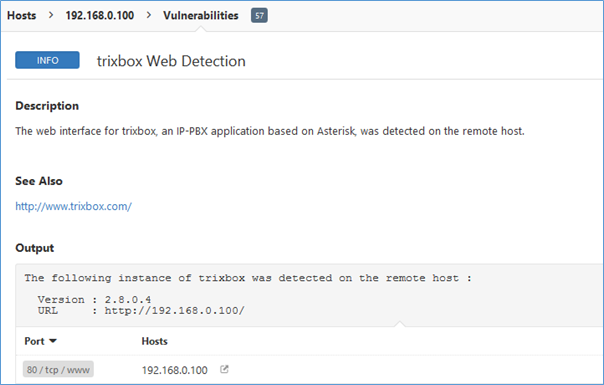
192.168.0.100 seems a VoIP server is running Asterisk based PBX (Trix box). Nessus has also detected the Trixbox web version.
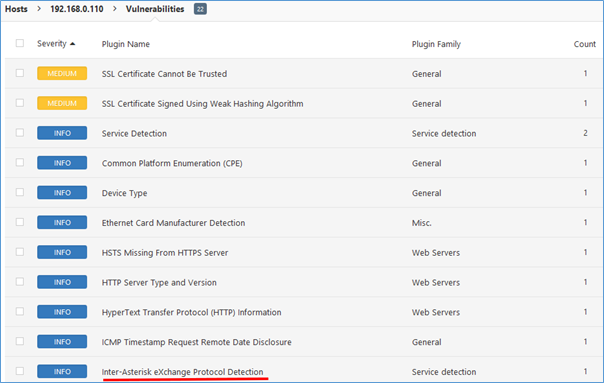
Another system (192.168.0.110) has been detected by Nessus. Inter-asterisk exchange protocol is running on the said system.
So far, three machines have been identified:
192.168.0.100 (server)
192.168.0.118 (may be client, need to confirm)
192.168.0.110 (probably client)
Software versions can also be detected using nmap (-sV) but Nessus has done most of the important part of scanning, and we are very much sure about the target network now.
Let's focus on enumeration; the objective is to get the information of the clients running VoIP client (software and hardware based phone).
Svmap is the common tool to enumerate the VoIP server and clients, it is available on Kali Linux, you can simply open the terminal on your machine and scan the entire network.

It is confirmed that the said IP is running the VoIP server; the server version has successfully been enumerated. Use the Metasploit module for more confirmation to check whether any other devices using VoIP or not. The following module used to the situation:
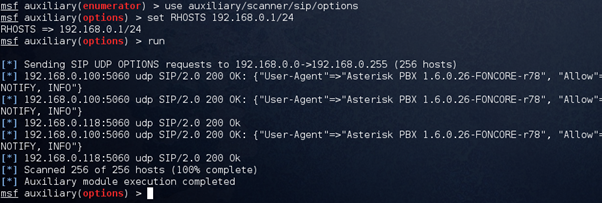
[*] 192.168.0.100:5060 udp SIP/2.0 200 OK: {"User-Agent"=>"Asterisk PBX 1.6.0.26-FONCORE-r78", "Allow"=>"INVITE, ACK, CANCEL, OPTIONS, BYE, REFER, SUBSCRIBE, NOTIFY, INFO"}
[*] 192.168.0.118:5060 udp SIP/2.0 200 Ok
[*] 192.168.0.100:5060 udp SIP/2.0 200 OK: {"User-Agent"=>"Asterisk PBX 1.6.0.26-FONCORE-r78", "Allow"=>"INVITE, ACK, CANCEL, OPTIONS, BYE, REFER, SUBSCRIBE, NOTIFY, INFO"}
Metasploit is also confirming the results. Svmap allows both INVITE and OPTIONS methods; the invite method generates the ring at the client side; it is not recommended because the user might get alerted after receiving an awkward call. This is an advanced test used to get the client's software details. The following test has been run to check the specific ports (5050-5062) only, and the method is INVITE:
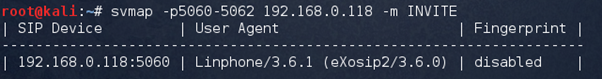
Now we have the information of the running software, its vendor, and version. The impact of this test can be seen on the client side:
So far the confirmation of two IP's (192.168.0.100 | 192.168.0.118) has received, one is the server while the other is a client. Another suspicious machine was discovered in the previous step, but it has not been confirmed yet. Let's send the INVITE packet to the machine:
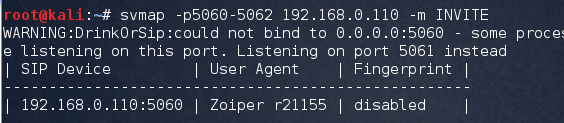
Another confirmation is here; the suspicious machine is the VoIP client running Zoiper (softphone).
192.168.0.100 (VoIP server)
192.168.0.110 (Client,zoiper)
192.168.0.118 (Client, Linphone)
The scanning and enumerating of the VoIP network is done, the vendor, version, operating system and other related information have been acquired. But, what about the user extensions? What extension or dialing plan this network has?
Username enumeration is crucial while attacking VoIP network, you should know the username mapped on every individual client, it helps while attacking the network, and as a pentester, you should be aware of this vulnerability. For username enumeration, sniff the traffic using Wireshark and then analyze the packets to get the user extensions.
Open Wireshark → capture → interfaces (select your interface, eht0 for wired connection and wlan0 for WiFi) → capture → start (this will start the sniffing; you will see the incoming and outgoing packets on the screen).
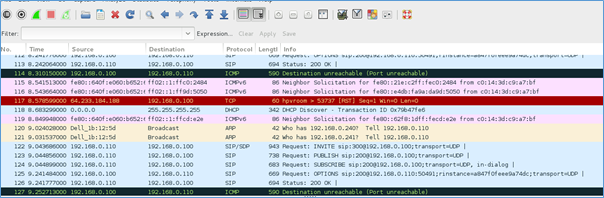
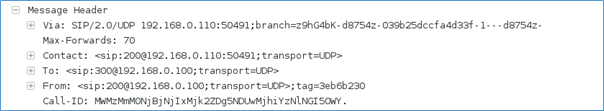
Analyze the SIP packets:
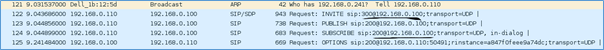
The header of each packet shows the sender and receiver extensions, by analyzing the header, two extensions have been identified:
- 200
- 300

What should you learn next?
Conclusion
The advantages of using VoIP in the corporate environment are tremendous. It is cost effective; the economy of scale can be achieved and provides better sound quality. But, the risk is there, a security engineer should check the security of the VoIP server, its open ports before making the server live. Hack your network and defend it before a hacker scan and exploit it.







